This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
EUTour2013
| |
OWASP EUROPE TOUR 2013 Tour Home Page |
- Welcome
- Full schedule
- Cambridge
- Midlands
- London
- Czech
- Bucharest
- Belgium
- Netherlands
- Denmark
- Barcelona
- Finland
- Lisbon
- Dublin
- Rome
- Training
- CTF Competition
- Sponsors
- Team
|
|
Current Tour Schedule (edit)
- Cambrige - 13th May (Monday)
- Midlands - 15th May (Wednesday)
- London - 3rd June (Monday)
- Czech - 4th June (Tuesday)
- Bucharest - 5th June (Wednesday
- Belgium - 6th June (Thursday)
- Denmark - 10th of June (Monday)
- Barcelona - 13th, 14th June (Thursday, Friday)
- Finland - 17th June (Monday)
- Netherlands - June 20th (Thursday)
- Lisbon - 21st June (Friday)
- France - 24th June (Monday)
- Geneva - 25th June (Tuesday)
- Dublin - 25th, 26th June (Tuesday, Wednesday)
- Rome - 27,28th June (Thursday, Friday)
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - Cambridge 2013Monday 13th May (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Monday 13th May) | |
| Fecha | Lugar |
| Monday 13th May | Venue Location: Anglia Ruskin University (Cambridge) - Lord Ashcroft Building - Room LAB002 Venue Address: East Road, Cambridge, CB1 1PT |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour: OWASP Cambridge Chapter Registration
| |
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 11:00 (0 mins) |
Registration | ||||
| 11:45 (0 mins) |
Introduction & Welcome | Adrian Winckles - OWASP Cambridge Chapter Leader & Senior Lecturer | Introduction to OWASP & Anglia Ruskin University
Schedule for the Day | ||
| 12:00 (45 mins) |
Real Costs of Cybercrime | Ross Anderson (Cambridge University) | Following a systematic study of the costs of cybercrime, in response to a request from the UK Ministry of Defence following scepticism that previous studies had hyped the problem, each of the main categories of cybercrime we set out what is and is not known of the direct costs, indirect costs and defence costs { both to the UK and to the world as a whole. We distinguish carefully between traditional crimes that are now `cyber' because they are conducted online (such as tax and welfare fraud); transitional crimes whose modus operandi has changed substantially as a result of the move online (such as credit card fraud); new crimes that owe their existence to the Internet; and what we might call platform crimes such as the provision of botnets which facilitate other crimes rather than being used to extract money from victims
directly. | ||
| 12:45 (45 mins) |
Three Legged Cybercrime Investigation and its Implications | DI Stewart Garrick (Metropolitan Police ECrime Unit) | DI Stewart Garrick has over 27 years experience in the Metropolitan Police Service, 22 years as a detective and 10 years as a Detective Inspector. His career has been spent primarily on major crime units engaged on both proactive and reactive investigations, including 5 years investigating murders, 3 years on the Homicide Task Force (a proactive unit targeting those who would commit murder) and 5 years managing covert operations against organised crime. In March 2011 he joined Scotland Yard's Police Central eCrime Unit. He has witnessed the PCeU's growth from 40 officers to over 100 and has managed several high profile investigations. He has recently taken charge of the unit's cadre of police and civilian forensic examiners who are integrated into the unit's dynamic investigative model. He has this year completed an MSc in Countering Organised Crime and Terrorism at UCL, with a dissertation examining the emergence of radicalising settings based on Situational Action Theory. | ||
| 13:30 (45 mins) |
OWASP Mobile Top 10 | Justin Clarke - London OWASP Chapter Leader | The OWASP Mobile Security Project is a centralized resource intended to give developers and security teams the resources they need to build and maintain secure mobile applications. Through the project, our goal is to classify mobile security risks and provide developmental controls to reduce their impact or likelihood of exploitation.
As part of the overall Mobile Project , the Top 10 Mobile Risks include M1: Insecure Data Storage M2: Weak Server Side Controls M3: Insufficient Transport Layer Protection M4: Client Side Injection M5: Poor Authorization and Authentication M6: Improper Session Handling M7: Security Decisions Via Untrusted Inputs M8: Side Channel Data Leakage M9: Broken Cryptography M10: Sensitive Information Disclosure | ||
| 14:15 (45 mins) |
Refreshments & Networking | LAB107 | |||
| 15:00 (45 mins) |
Everything We Know is Wrong | Eoin Keary - OWASP Global Committee | The premise behind this talk is to challenge both the technical controls we recommend to developers and also out actual approach to testing. This talk is sure to challenge the status quo of web security today.
"Insanity is doing the same thing over and over and expecting different results." - Albert Einstein We continue to rely on a “pentest” to secure our applications. Why do we think it is acceptable to perform a time-limited test of an application to help ensure security when a determined attacker may spend 10-100 times longer attempting to find a suitable vulnerability? Our testing methodologies are non-consistent and rely on the individual and the tools they use. Currently we treat vulnerabilities like XSS and SQLI as different issues but the root causes it the same. – it’s all code injection theory!! Why do we do this and make security bugs over complex? Why are we still happy with “Testing security out” rather than the more superior “building security in”? | ||
| 15:45 (45 mins) |
Tricolour Alphanumercial Spaghetti | Colin Watson - OWASP Project Leader | Do you know your "A, B, Cs" from your "1, 2, 3s"?
Is "red" much worse than "orange", and why is "yellow" used instead of "green"? Just what is a "critical" vulnerability? Is "critical" the same as "very high"? How do PCI DSS "level 4 and 5" security scanning vulnerabilities relate to application weaknesses? Does a "tick" mean you passed? Are you using CWE and CVSS? Is a "medium" network vulnerability as dangerous as a "medium" application vulnerability? Can CWSS help? What is FIPS PUB 199? Does risk ranking equate to prioritisation? What is "one" vulnerability? Are you drowning in a mess of unrelated, classifications, terminology and abbreviations? If you are a security verifier and want to know more about ranking your findings more meaningfully, or receive test reports and want to better understand the results, or are just new to ranking weaknesses/vulnerabilities and want an overview, come along to this presentation. It will also explain why the unranked information-only ("grey" or "blue"?) findings might contain some of the best value information. | ||
| 16:30 (45 mins) |
Secure Coding, some simple steps help. | Steven van der Baan - OWASP Cambridge | Secure coding is often perceived as difficult and complex.
While it is true that 'good security' should be embedded into the design, there are a couple of steps a developer can take which lead to a more secure application. In this presentation we will go to the basics of secure application development and demonstrate these principles which help you build security into your application. | ||
| REGIONAL MEETING | |
OWASP Europe Tour - Leicester 2013Wednesday 15th May (Regional Meeting) | |
| DESCRIPTION | |
| OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license. | |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
Wednesday 15th May | |
| When | Where |
| Wednesday 15th May | Venue Location: De Montfort University, Leicester Venue Address: Hugh Aston Building, De Montfort University, Leicester |
| Price and registration | |
This event is FREE Due to limited space, registration is required for this event: Book your free place now!
| |
| Meeting Details | |||||
| Time | Title | Speaker | Description | ||
| 18:00 (10 mins) |
Arrival and Welcome | ||||
| 18:10 (45 mins) |
Me, a camera and a bucket! | Robin Wood (@digininja) | |||
| 19:00 (45 mins) |
Time for a better gun! | Arron "Finux" Finnon (@f1nux): | |||
| 19:50 (45 mins) |
All Your Files Are Belong to Us! | David Lodge | |||
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - London 2013Monday 3rd June | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
London EUTour2013 Conference Day (Monday 3rd June) | |
| Date | Location |
| Monday 3rd June | Venue Location: Lion Court Conference Centre Venue Address: 25 Procter Street, Holborn, London, WC1V 6NY |
| Price and registration | |
This event is FREE and open to allRegistration Link to the Europe Tour: REGISTER HERE!
| |
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 09:00 am (45 mins) |
Registration and Tea/Coffee | ||||
| 9:45 am (15 mins) |
Introduction & Welcome Video |
Justin Clarke - London OWASP Chapter Leader | Introduction to OWASP & London Event Schedule for the Day | ||
| 10:00AM (45 mins) |
Managing Web & Application Security with OWASP – bringing it all together Video | Presentation |
Tobias Gondrom - OWASP Project Leader | Setting up, managing and improving your global information security organisation using mature OWASP projects and tools. Achieving cost-effective application security and bringing it all together on the management level. A journey through different organisational stages and how OWASP tools help organisations moving forward improving their web and application security. This talk will discuss a number of quick wins and how to effectively manage global security initiatives and use OWASP tools inside your organisation. | ||
| 10:45AM (45 mins) |
Using the O2 Platform, Zap and AppSensor to protect and test applications Video |
Dinis Cruz - OWASP O2 Platform Project Leader | This presentation will show how these 3 OWASP tools can be used to find and mitigate security vulnerabilities in applications. The O2 Platform will be used to analyse the target application source code, and automate the use of both Zap and AppSensor's capabilities | ||
| 11:30AM (45 mins) |
PCI for Developers No Video | Presentation to follow |
Fabio Cerullo, OWASP Ireland | The PCI-DSS and PA DSS standards are well known to security professionals and auditors, but how are these interpreted by software development teams? Usually is not clear whether all requirements are necessary and most importantly, how these should be implemented. This talk aims to help developers understanding the key points of these standards in a simple and fast approach and be able to implement them during the software development cycle. | ||
| 12:15PM (60 mins) |
Lunch | ||||
| 1:15PM (45 mins) |
Teaching an Old Dog New Tricks: Securing Development with PMD Video | Presentation |
Justin Clarke - London OWASP Chapter Leader | Using static analysis to identify software bugs is not a new paradigm. For years, developers have used static analysis tools to identifying code quality issues. While these tools may not be specifically designed for identifying security bugs. This presentation will discuss how custom security rules can be added to existing code quality tools to identify potential software security bugs. Writing custom software security rules for the popular Java code scanning tool PMD will be the focus of the presentation. | ||
| 2:00PM (45 mins) |
Your framework will fail you Video | Presentation |
Rory McCune - OWASP Scotland | A lot of reliance for Web Application Security is put in the framework that’s used. But here’s the bad news … it will fail you. There’s no such thing as perfect code, and web application frameworks are no exception. So how do you avoid the panic upgrades when a security alert hits your e-mail Inbox? This talk aims to give you some ideas about what you can do reduce reliance on individual security mechanisms and allow you to sleep more easily at night. | ||
| 2:45PM (30 mins) |
Tea/Coffee Break and Networking | ||||
| 3:15PM (45 mins) |
OWASP Cornucopia Project Video | Presentation |
Colin Watson - OWASP Project Leader | Microsoft's Elevation of Privilege (EoP) threat modelling card game has been refreshed into a new version more suitable for typical web applications, and aligned with OWASP advice and guides. "OWASP Cornucopia - Ecommerce Web Application Edition" will be presented and used to demonstrate how it can help developers identify security requirements from the OWASP Secure Coding Practices - Quick Reference Guide. The project is now referenced by a PCIDSS information supplement. | ||
| 4:00PM (45 mins) |
Secure Coding, some simple steps help Video | Presentation |
Steven van der Baan - OWASP Cambridge | Secure coding is often perceived as difficult and complex.
While it is true that 'good security' should be embedded into the design, there are a couple of steps a developer can take which lead to a more secure application. In this presentation we will go to the basics of secure application development and demonstrate these principles which help you build security into your application. | ||
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - Czech 2013I have to inform you this meeting was postponed because of serious floods in Prague. New date to be announced. (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Monday 13th May) | |
| Fecha | Lugar |
| Tuesday 4th June | Venue Location: MFF UK - room K1 Venue Address: Sokolovská 49/83 186 00 Praha-Praha 8, Česká republika |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour - Czech: http://owasp-czech.eventbrite.com/
| |
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 6:00 pm (30 mins) |
Registration | ||||
| 6:30 pm (10 mins) |
Introduction | Jan Kopecky | |||
| 6:40 pm (30 mins) |
OWASP introduction | Sebastien Deleersnyder | Detailed information about OWASP. | ||
| 7:10 pm (45 mins) |
OWASP TOP 10 | Jan Kopecky | During this presentation we will go through TOP 10 security issues with live demonstrations. | ||
| 7:55 pm (45 mins) |
Integrating security into the software development lifecycle | Sebastien Deleersnyder | Using the OWASP Software Assurance Maturity Model (OpenSAMM) as a framework, this talk covers the major application security controls of a secure development lifecycle program as provided by OWASP. Featured OWASP open source material include: OWASP guidelines and tools such as ESAPI, Zed Attack Proxy (ZAP), as well as educational resources. | ||
| 8:40 pm (30-45 mins) |
Discussion | All attendees | This will be free discussion where people can talk to each other about any topic. | ||
| CONFERENCE | |
OWASP Europe Tour - Bucharest 2013Wednesday 5th June (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Wednesday 5th of June) | |
| Date | Location |
| Wednesday 5th of June | Venue Location: University "Politehnica" of Bucharest Venue Address: Splaiul Independentei nr. 313, sector 6, Bucuresti, ROMANIA; Rectorship Building, Senate Hall |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour:
| |
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 02:30 pm (30 mins) |
Introduction & Welcome | Ionel Chirita, Claudiu Constantinescu | Introduction to OWASP | ||
| 03:15 pm (45 mins) |
Penetration Testing - a way for improving our cyber security | Adrian Furtună | The talk presents a comparison between two internal penetration tests made in consecutive years at the same client. We will see the successful attack scenarios and the techniques used to take control over the network. Furthermore, we will see how and why the security posture of the client improved as a result of the penetration tests. | ||
| 04:15 pm (45 mins) |
Android reverse engineering: understanding third-party applications | Vicente Aguilera | It will present the objectives of the software reverse engineering and the techniques and tools to execute this process in Android applications. It will present, from a security analyst point of view and in a practical manner, the process of analyzing an existing application at Google Play Store. | ||
| 05:15 pm (45 mins) |
The Trouble with Passwords | Mark Goodwin | Many developers still seem unsure of how to deal with passwords and password data. This presentation covers some common mistakes made when storing credentials and introduces some good ways of tackling them. | ||
| 06:15 pm (45 mins) |
Hacking the ViewState in ASP.NET | Ovidiu Diaconescu | The view state is a necessary evil of ASP.NET Web Forms. Without having the proper protection mechanisms in place, it is trivial to exploit. This session will teach you how to take advantage of unsecured web applications and how to tighten-up your own | ||
| 07:15 pm (45 mins) |
Do you "GRANT ALL PRIVILEGES ..." in MySQL/MariaDB/Percona Server? | Gabriel Preda | We discuss (at least) elementary security procedures for MySQL and it's forks. Dive through short information about MySQL forks, replication options and their security implications. Finally some notes on what changes about security when you scale MySQL. | ||
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - Belgium 2013Thursday 6th June (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Monday 13th May) | |
| Fecha | Lugar |
| Thursday 6th June | Venue Location: University of Leuven Venue Address: Department of Computer Science |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour - Belgium: REGISTER HERE!
| |
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 17:30 (45 mins) |
Welcome & sandwiches | ||||
| 18:15 (15 mins) |
OWASP Update | Sebastien Deleersnyder | |||
| 18:30 (45 mins) |
Needles in haystacks, we we are not solving the appsec problem & html hacking the browser, CSP is dead. | Eoin Keary, CTO and founder of BCC Risk Advisory Ltd. | TBD | ||
| 19:30 (45 mins) |
Teaching an Old Dog New Tricks: Securing Development with PMD | Justin Clarke, Director and Co-Founder of Gotham Digital Science | Using static analysis to identify software bugs is not a new paradigm. For years, developers have used static analysis tools to identifying code quality issues. While these tools may not be specifically designed for identifying security bugs. This presentation will discuss how custom security rules can be added to existing code quality tools to identify potential software security bugs. Writing custom software security rules for the popular Java code scanning tool PMD will be the focus of the presentation.
Justin Clarke is a Director and Co-Founder of Gotham Digital Science. He is the lead author/technical editor of "SQL Injection Attacks and Defense" (Syngress), co-author of "Network Security Tools" (O'Reilly), contributor to "Network Security Assessment, 2nd Edition" (O'Reilly), as well as a speaker at numerous security conferences and events such as Black Hat, EuSecWest, ISACA, BruCON, OWASP AppSec, OSCON, RSA and SANS. Justin is the Chapter Leader for the OWASP London chapter in the United Kingdom. | ||
| 20:30 (45 mins) |
Vulnerability Prediction in Android Applications | Aram Hovsepyan, Ph. D. | We present an approach to predict which components of a software system contain security vulnerabilities. Prediction models are a key instrument to identify the weak spots that deserve special scrutiny. Our approach is based on text mining the source code of an application. We have explored the potential of the bag-of-words representation and discovered that a dependable prediction model can be built by means of machine learning techniques. In a validation with 10 Android applications we have obtained performance results that often outclass state-of-the-art approaches. | ||
Bio
- Dr. Aram Hovsepyan received both his Master's Degree in Informatics and PhD Degree in Engineering from KU Leuven. Since July 2011, he has been working as a senior researcher in the iMinds-DistriNet research group at KU Leuven where he collaborates with Dr. Riccardo Scandariato and Prof. Wouter Joosen. Dr. Hovsepyan's main research interests lie in the area of model-driven software development and empirical software engineering with a particular focus on security vulnerability prediction techniques.
\
| CONFERENCE | |
OWASP Europe Tour - The Netherlands 2013'Thursday, June 20th (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Thursday, June 20th) | ||
| Date | Venue | PR material |
| Thursday, June 20th | Hogeschool van Amstedam Venue Address: Duivendrechtsekade 36-38, 1096 AH Amsterdam
|
Flyer (pdf A4 format) Poster(pdf A3 format) |
| Price and registration | ||
This event is FREE Registration Link to the Europe Tour: Click here
| ||
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 05:45 PM (30 mins) |
Registration - Sandwiches and drinks provided | ||||
| 06:15 PM (15 mins) |
Opening | Ferdinand Vroom & Martin Knobloch | Welcome and OWASP News | ||
| 6:30 PM (45 mins) |
The OWASP Zed Attack Proxy (ZAP) | Simon Bennetts has been developing web applications since 1997, and strongly believes that you cannot build secure web applications without knowing how to attack them.
He now works for Mozilla as part of their security team, is the OWASP ZAP project lead and has contributed to many other open source security projects. |
The OWASP Zed Attack Proxy (ZAP) is an easy to use integrated penetration testing tool for finding vulnerabilities in web applications.
It is designed to be used by people with a wide range of security experience and as such is ideal for developers and functional testers who are new to penetration testing as well as being a useful addition to an experienced pen testers toolbox. It is also community project, being maintained by a worldwide group of volunteers and is completely free, open source and cross platform. Since its release in 2010 ZAP has gone from strength to strength and is now a flagship OWASP project. | ||
| 07:15 PM (15 mins) |
Break | ||||
| 07:30 PM (45 mins) |
Needles in haystacks, we we are not solving the appsec problem & html hacking the browser, CSP is dead | Eoin Keary, CTO and founder of BCC Risk Advisory Ltd. | "Insanity is doing the same thing over and over and expecting different results." - Albert Einstein We continue to rely on a “pentest” to secure our applications. Why do we think it is acceptable to perform a time-limited test of an application to help ensure security when a determined attacker may spend 10-100 times longer attempting to find a suitable vulnerability? Our testing methodologies are non-consistent and rely on the individual and the tools they use. Currently we treat vulnerabilities like XSS and SQLI as different issues but the root causes it the same. – it’s all code injection theory!! Why do we do this and make security bugs over complex? | ||
| 08:15 PM (45 mins) |
Secure Coding, some simple steps help | Steven van der Baan is a passionate Security Consultant and Software Architect, with a broad history in software development and architecture. Steven has a varied background in developing complex systems, mainly in Java. He has the capability to analyse problems and provide sound advise on possible solutions. He can also design a solution that fits the wishes of the client. Steven is determined, steadfast and critical, likes to work in teams, but is capable to work on his own. He is always willing to share his knowledge and help his colleagues. Steven follows the latest developments in the security field to keep his knowledge up to date. | Secure coding is often perceived as difficult and complex.
While it is true that 'good security' should be embedded into the design, there are a couple of steps a developer can take which lead to a more secure application. In this presentation we will go to the basics of secure application development and demonstrate these principles which help you build security into your application. | ||
| 09:00 PM to 09:30 PM | Networking | ||||
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - Denmark 2013Monday 10th of June 2013 from 1700 - 2115 | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
Monday 10th of June | |
| Fecha | Lugar |
| Monday 10th June | Venue Location: Technical University of Denmark, DTU Compute, Institut for Matematik og Computer Science (former DTU Informatik) Venue Address: DTU Compute, Building 324 (between building 322 and 325), entrance from Elektrovej or Matematiktorvet, 2800 Kgs Lyngby, Denmark |
| Price and registration | |
| This event is FREE | |
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 16:30 (45 mins) |
Arriving and Networking | ||||
| 17:15 (15 mins) |
Welcome and OWASP | Ulf Munkedal | What is OWASP? Why this event? How can you learn more and/or contribute? Thank you to our venue and food sponsor DTU Compute and the EU Tour 2013 sponsors. | ||
| 17:30 (15 mins) |
Information security at DTU Compute | Christian W. Probst, Associate Professor | A brief overview of what is going on at DTU Compute when it comes to information security related projects, e.g. the TREsPASS. | ||
| 17:45 (45 mins) |
OWASP Tools and resources | Fabio Cerullo | Fabio will give an overview of the many tools and resources that OWASP makes available and explain how you can use them. Including the OWASP ESAPI - Enterprise Security API and how you can use it to write lower-risk applications. | ||
| 18:30 (30 mins) |
Dinner break and networking | Sandwiches and soft drinks | Thanks to DTU Compute | ||
| 19:00 (60 mins) |
Android Security and App Testing | Alexandru Gherman | Practical examples of the risks from OWASP Mobile Top 10 with proof-of-concepts and practical reverse engineering and testing of a downloaded app. | ||
| 20:00 (15 mins) |
Coffee break and networking | Coffee, the and possibly a cake :) | Thanks to DTU Compute | ||
| 20:15 (45 mins) |
The Building Security in Maturity Model (BSIMM) | Ellen Moar | How do you know what security activities belong in your software lifecycle? How do you measure what you're doing? Begun in 2009, the BSIMM, is an observation-based scientific model directly describing the collective software security activities of more than sixty software security initiatives. Used as a measuring tool, BSIMM helps an organisation understand and plan their software security initiative. It covers the full framework of software development from requirements, architecture, code and test, to release management, governance, and training. This talk will introduce the measurements, explain what is measured, how it is measured, and how the measurement can be used to create or improve a software security initiative. | ||
| 21:00 (15 min) |
Rounding up | Ulf Munkedal | Conclusions and last questions before splitting up after a great evening :) | ||
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - Barcelona 2013Friday 14th June (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Friday 14th June) | |
| Date | Location |
| Friday 14th June | Universitat Ramon Llull, La Salle - URL Sant Joan de La Salle, 42 |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour:
| |
| Conference Details | |||||
| Time | Speaker | Title / Description | |||
| 09:15-10:00 | Registration | ||||
| 10:00-10:05 | 
|
Josep Maria Ribes. Director d'Enginyeria de La Salle Campus Barcelona. |
Bienvenida. | ||
| 10:05-10:15 | 
|
Vicente Aguilera Díaz. OWASP Spain Chapter Leader. Socio y Director Dpto. Auditoría en Internet Security Auditors. |
Introducción a la jornada. | ||
| 10:15-11:15 | 
|
Selva María Orejón Lozano. Directora ejecutiva de onbranding. Co-fundadora AERCO-PSM. Fundadora y Directora del Congreso Brand Care. |
Seguridad en redes sociales. Ya estamos todos conectados Online, incluso hiperconectados, hiperexpuestos con nuestros contactos. Saben qué hacemos, dónde estamos, con quién, qué compramos, qué consumimos ... pero ¿y nuestra seguridad? ¿Ya sabemos quién ve qué? ¿Nos interesa comunicar todo lo que hacemos? ¿Tener tanta visibilidad? Y como empresa ¿ya controlamos a quien lleva nuestra comunicación? ¿Y si se va de la empresa? ¿Tenemos acceso real y completo en nuestra comunidad?. | ||
| 11:15-12:15 | 
|
Fabio Cerullo. CEO & Founder Cycubix Limited. OWASP Ireland Chapter Leader. |
PCI Para Desarrolladores. Los estandares PCI-DSS y PCI-PA DSS son bien conocidos por los profesionales de seguridad y auditoria informatica, pero como son interpretados por los equipos de desarrollo de software? Muchas veces no es claro si todos los requerimientos son necesarios y mas importante, como tienen que ser implementados. Esta charla tiene como objetivo ayudar a los desarrolladores a interpretar de manera rapida y sencilla cuales son los puntos criticos de estos estandares a tener en cuenta y poder implementarlos durante el ciclo de desarrollo de software. | ||
| 12:15-13:15 | 
|
Chema Alonso. CEO en Telefónica Digital Identity & Privacy. |
Why cyberspies always win. Todos los días sitios webs pertenecientes a grandes empresas son vulneradas. Muchas de esas empresas pasan revisiones constantes de seguridad, y sin embargo, siguen apareciendo en las noticias las contraseñas de usuarios, los datos de los clientes o información sensible de la empresa. ¿Por qué? En esta sesión se presentarán algunas ideas al respecto sobre este tema... de forma muy maligna. | ||
| 13:15-15:15 | Lunch & Networking | ||||
| 15:15-16:15 | 
|
Albert López Fernández. Analista de Seguridad en Internet Security Auditors. |
Low Level Miseries when Exploiting Linux Heap. Se explicarán varias vulnerabilidades que afectan a la implementación del heap en sistemas GNU/Linux. Se realizará un repaso del estado del arte, y cómo aprovecharse de las vulnerabilidades presentes en el código encargado de gestionar la memoria dinámica en Linux y se detallará cuál ha sido la problemática al desarrollar los payloads necesarios para explotar dichas vulnerabilidades. Asimismo, se repasará a alto nivel cómo funciona la gestión de memoria dinámica en Linux para luego destripar su funcionamiento a bajo nivel. | ||
| 16:15-17:15 | 
|
Marc Rivero López. Security researcher en Barcelona Digital. |
Internet tactical fraud evolution. Antes de entrar en materia y a modo de contexto histórico se expondrá la evolución del fraude en Internet en la última década. Desde las brechas de seguridad provocadas con el afán de conocimiento, hasta los ataques industrializados en los que se roban a usuario de manera masiva. Se hará especial hincapíe a las medidas de seguridad adoptadas durantes los últimos años en el sector de la banca electrónica y las técnicas empleadas por los delincuentes para conseguir saltárselas.Del mismo modo, se expondrá la capacidad del código malicioso actual para conseguir, ya no solamente la información de cuentas bancarias, sino del contexto en el que se ejecutan (sandbox laboratorios de malware con el fin de recopilar información que pueda ser convertida en inteligencia que servirá para optimizar las tácticas empleadas). | ||

|
Dani Creus. Lead Consultant RISK Team EMEA - Verizon. | ||||
| 17:15-18:00 | Mesa de debate | ||||
| 18:00-18:15 | Closure | ||||
| CONFERENCE | |
OWASP Europe Tour - Finland 2013Monday 17th June (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Monday 17th June) | |
| When | Where |
| Monday 17th June | Venue Location: HTC Keilaniemi Venue Address: Keilaranta 15 |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour - Finland: Regonline
| |
| Conference Details | |||||
| Time | Title | Speaker | Description | ||
| 16:00 (15 mins) |
Registration & coffee | ||||
| 16:15 (15 mins) |
Welcome | Petteri Arola | OWASP in Finland | ||
| 16:30 (15 mins) |
Word from our sponsor | ||||
| 16:45 (30 mins followed by 15 min break) |
Nokia responsible disclosure program | Omar Benbouazza-Villa | Nokia has launched responsible disclosure program recently. Omar will talk about experiences starting and running such a program as a part of enterprise application security program. Common errors, solutions and best practices will be explained to help other companies to improve their security with this type of programs. | ||
| 17:30 (1 hour 30 mins) |
Social engineering | Gavin Ewan | Jac0byterebel is not your typical social engineering presenter. Out goes the snake oil sale of analysing the minutia of pop psychology and trying to squeeze out real answers to the questions asked during a real social engineering attack. In comes hard hitting accounts of social engineering attacks drawn from real sources but anonymised to protect the pwned. | ||
| 19:00 (15 min) |
Rounding up | Petteri Arola | Conclusions and last questions. Discussion continues over food & drinks at same location | ||
Abstract
Omar's presentation:
Nokia has launched responsible disclosure program recently. Omar will talk about experiences starting and running such a program as a part of enterprise application security program. Common errors, solutions and best practices will be explained to help other companies to improve their security with this type of programs.
Gavin's presentation:
Jac0byterebel is not your typical social engineering presenter. Out goes the snake oil sale of analysing the minutia of pop psychology and trying to squeeze out real answers to the questions asked during a real social engineering attack. In comes hard hitting accounts of social engineering attacks drawn from real sources but anonymised to protect the pwned.
Deano, our ‘hypothetical’ bad-guy, could hack and social engineer his way to cash in his pocket and no cash in your pocket. Easy, boring, predictable. But what if Deano, a criminal social engineer, really upped his game?
This talk will see Deano up the stakes and deliver the kind of aggressive attack you have all lived in fear of. No longer a phone call to get your credentials, or a rogue e-mail to direct you to a fake website, this time its personal and Deano is looking to do you REAL damage.
Drawing on real data from anonymised sources, from the account given of this attack, attendees of the talk will see that a real social engineer doesn’t once pick up a psychology textbook. Deano will instead pose you a question -
“What if Deano could destroy my business without anyone realising it had been attacked?”
Live in fear of Hactivism? You won’t sleep at night after meeting Deano.
If you want an hour and a half of being told that ‘looking to the right makes you easier to social engineer’, go to another talk. If you want to see how the real bad guy operates, and talk about how to defend against him, then I look forward to seeing you there..
Bio
Omar
Omar Benbouazza is a spanish hacker working in the Nokia Incident Response Team, as a Senior Security Analyst. He has been working in Security Information the last 8 years and has big experience in international companies such as Telefonica, Ernst&Young, Santander Bank and now Nokia. He is also organizer of the most important security conference in Spain, RootedCON.
Gavin Ewan
Gavin 'Jac0byterebel' Ewan is a ranty, shouty, sweary Scottish hacker. After selling lots of things to lots of people, he decided to get firmly into the field of information security, always having been a geek at heart. Having taken his education and training in psychology, particularly sales psychology into the field of social engineering, he is now re-writing the social engineering rulebook and chasing out the snake-oil salesmen. Already a successful speaker, Gavin has delivered talks on social engineering worldwide to various audiences.
| CONFERENCE | |
OWASP Europe Tour - Lisbon 2013Friday 21st June (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Friday 21st June) | |
| Date | Location |
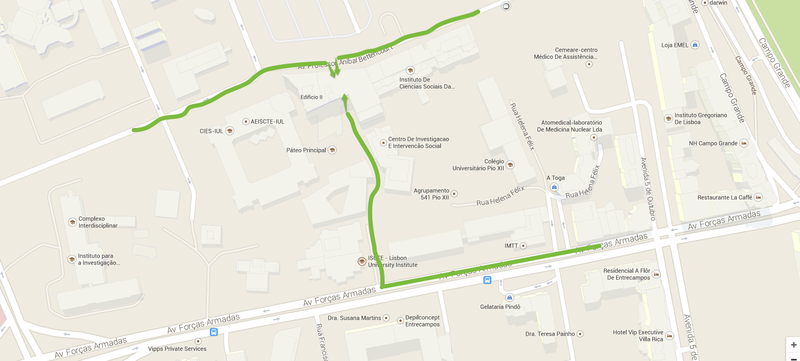
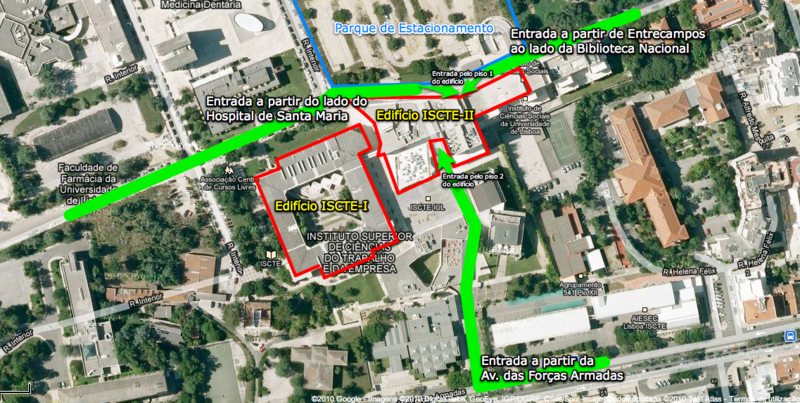
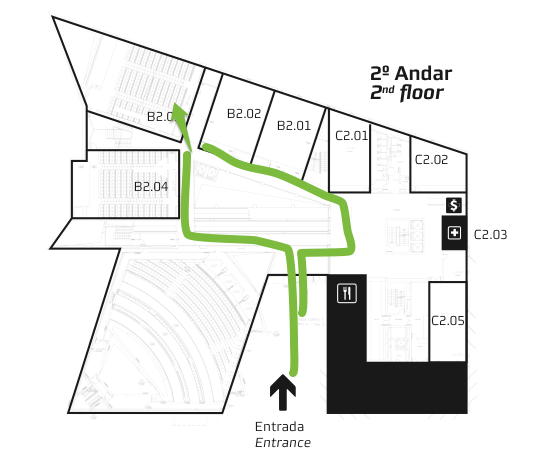
| Friday 21st June | Venue Location: ISCTE-IUL University Institute of Lisbon, Aud. B2.03 Venue Address: Avª das Forças Armadas, 1649-026 Lisboa |
| Pictures | Set 1 Set 2 |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour (Lisboa): Registration
| |
| Conference Details | |||||
| Time | Speaker | Title / Description | |||
| 14:00 | Opening | ||||
| 14:15 - 15:15 | 
|
Lieven Desmet DistriNet Research Group, Katholieke Universiteit Leuven, OWASP Benelux. |
Sandboxing JavaScript. - Discussing the problem of remote script inclusion based on an analysis of the Top 10.000 websites; - Overview of JavaScript sandboxing techniques, with particular focus on JSand (ie. a prototype we have developed at KU Leuven). | ||
| 15:15 - 16:00 | 
|
Pedro Fortuna CTO, Auditmark. |
Protecting JavaScript source code – Facts and Fiction. The goal of code obfuscation is to delay the understanding of a program does. It can be used, for example, in scenarios where the code contains Intellectual Property (algorithms) or when the owner wants to prevent a competitor for stealing and reusing the code. To achieve it, an obfuscation transformation translates easy to understand code into a much harder to understand form. But in order to be resilient, obfuscation transformations need also to resist automatic reversal performed using static or dynamic code analysis techniques. This presentation focuses on the specific case of JavaScript source obfuscation, main usage cases, presents some obfuscation examples and their value in providing real protection against reverse-engineering. Slides | ||
| 16:00 - 16:45 | 
|
Ricardo Melo CTO, DRI. |
PHP and Application Security. To which level can PHP and application security cohexist? The presentation will provide information about the most security critical aspects while developing a PHP web application. Slides | ||
| 16:45 - 17:30 | 
|
Tiago Henriques Founder and Team Leader of PTCoreSec. |
Software - vulnerabilities and needs. In this talk he will discuss some of the most common ways attackers can use to compromise your computers, understand the details of how some of the tools can be used to achieve this and even how when we are sending our taxes online (IRS) we put ourselves in danger. How can a simple link or opening a simple PDF file give and attacker remote access to your computer systems. | ||
| 17:30 - 18:15 | 
|
Dinis Cruz OWASP OWASP O2 Platform project |
Scripting Application Security Pentesting at the speed of Scripting (using O2 Platform) - This presentation will show how the OWASP O2 Platform scripting capabilities can be used to 'codify' an pen-testers mind/action and perform advanced analysis, fuzzing and exploitation of both Web and desktop-based Applications. | ||
| 18:30 | Closure | ||||
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - Dublin 2013Tuesday 25th June (Training. Info about the training session) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
Training (Wednesday 25th June) | |
| When | Where |
| Tuesday 25th June | Venue Location: TCube Venue Address: 32 - 34 Castle Street, Dublin 2, Ireland |
| DEFENSIVE PROGRAMMING – JAVASCRIPT AND HTML5 HTML5 is the fifth revision of the HTML standard. HTML5, and its integration with JavaScript, introduces new
security risks that we need to carefully consider when writing web front-end code. Modern web-based software, including
mobile web front-end applications, makes heavy use of innovative JavaScript and HTML5 browser support to deliver
advanced user experiences. Front-end developers focus their efforts on creating this experience and are generally not aware
of the security implications of the technologies they use. The Defensive Programming – JavaScript/HTML5 course helps web front-end developers understand the risks involved with
manipulating the HTML Document Object Model (DOM) and using the advanced features of JavaScript and HTML 5 such as
cross-domain requests and local storage. The course reinforces some important security aspects of modern browser
architecture and presents the student with defensive programming techniques that can be immediately applied to prevent common vulnerabilities from being introduced. Additionally, the course provides a detailed description of typical JavaScript sources and sinks and explains how they can be used to detect problems in code. For more information about the training please see Further training information
| |
| Price and registration | |
| Price: 350€ Non members / 300€ OWASP members. Duration: 8 hours (09:00h - 18:00h)
Registration Link to the Europe Tour training: Register Here
| |
|
CONFERENCE (Wednesday 26th June) | |
| When | Where |
| Wednesday 26th June | Venue Location: TCube Venue Address: 32 - 34 Castle Street, Dublin 2, Ireland |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour: Register Here
| |
| Conference Details - Times are subject to change | |||||
| Time | Title | Speaker | Description | ||
| 09:30 (30 mins) |
Registration | ||||
| 10:00 (15 mins) |
Introduction | ||||
| 10:15 (15 mins) |
Interactive Workshop - Ultimate Fighting Championship: Bugs vs Flaws | Paco Hope | Abstract
We see a lot of defects in software and they fall broadly into two categories: bugs or flaws. How well we understand the defects and our correct categorisation influences how successful we will be fixing them. If we mistake a flaw for a bug and offer a point solution, we'll be back in the same situation as before, only with more broken code. If we mistake a bug for a flaw, we condemn ourselves to reengineering hunks of our system when a localised patch would do. Spend time with Paco Hope analysing defects from real systems. Create rules that distinguish bugs from flaws and cast your vote. Argue about what to do with them. Climb into the ring with that defect and pin it to the mat! Learning Objectives
Pre-Requisites All security and software developers should be prepared for this. Prior experience in mixed martial arts is not necessary. :) | ||
| 11:15 (15 mins) |
Coffee Break | ||||
| 11:30 (60 mins) |
Using the browser as a platform for security tools | Mark Goodwin | |||
| 12:30 (60 mins) |
Lunch | ||||
| 13:30 (60 mins) |
Lesson learned from the trenches of targeted attack | Robert McArdle | Targeted attacks are now a major worry for organisations. In this talk we will describe real life case studies of some of the largest and more sophisticated targeted attacks, including how we infiltrated and mapped criminal networks, and live demos of some such mapping in action.
In this talk we will discuss some of the major ongoing and previous targeted attack campaigns that have been uncovered by Trend Micro in the last year or so, such as Luckycat, Tinba and others. We will discuss in-depth the modus operandi of the criminals in these so called APT attacks, show how we mapped and infiltrated their infrastructure, and demo some of the tools and techniques that we use when carrying out these type of investigations. All of this presentation will focus on real technical details from real cases studies, and this presentation will also include live demos. KEY QUESTIONS
1) What is the reality (not the hype) of a modern targeted attack | ||
| 14:30 (15 mins) |
Coffee Break | ||||
| 14:45 (60 mins) |
The Building Security In Maturity Model (BSIMM) | Paco Hope | How do you know what security activities belong in your software lifecycle? How do you measure what you're doing? Begun in 2009, the BSIMM, is an observation-based scientific model directly describing the collective software security activities of more than sixty software security initiatives. Used as a measuring tool, BSIMM helps an organisation understand and plan their software security initiative. It covers the full framework of software development from requirements, architecture, code and test, to release management, governance, and training. This talk will introduce the measurements, explain what is measured, how it is measured, and how the measurement can be used to create or improve a software security initiative.
Paco Hope is a Principal Consultant at Cigital, helping Fortune 500 companies secure their software for over 10 years in a variety of industries like online gaming, financial services, retail, and embedded systems. He is the author of two books on security, the most recent being the Web Security Testing Cookbook and a frequent conference speaker. As and a member of (ISC)²'s Application Security Advisory Board, he helps create and advise on the direction of the CSSLP certification. His passion is empowering everyone in the software lifecycle—developers, testers, analysts—to make meaningful contributions to the securing of software. | ||
| 15:45 (60 mins) |
Needles in haystacks, why we are not solving the appsec problem & html hacking the | Eoin Keary | We continue to rely on a “pentest” to secure our applications. Why do we think it is acceptable to perform a time-limited test of an application to help ensure security when a determined attacker may spend 10-100 times longer attempting to find a suitable vulnerability? Our testing methodologies are non-consistent and rely on the individual and the tools they use. Currently we treat vulnerabilities like XSS and SQLI as different issues but the root causes it the same. – it’s all code injection theory!! | ||
| 16:45 (15 mins) |
Close | ||||
| CONFERENCE AND TRAINING | |
OWASP Europe Tour - Rome 2013Thursday 27th June (Conference) | |
| DESCRIPTION | |
OWASP Europe TOUR, is an event across the European region that promotes awareness about application security, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
| |
| OWASP MEMBERSHIP | |
| During the OWASP Europe Tour you could become a member and support our mission. |
|
CONFERENCE (Thursday 27th June) | |
| When | Where |
| Thursday 27th June the Conference, Friday 28th June for the Training | Venue Location: Università Degli Studi Roma Tre Venue Address: Via vito Volterra, 62, 00182 Roma, Italy |
| Price and registration | |
This event is FREE Registration Link to the Europe Tour:| Conference
Registration Link to the Europe Tour:| Training
| |
| Conference Details | |||||
| Time | Title | Speaker | Description | Presentation | |
| 09:00 am (30 mins) |
Registration | ||||
| 9:30 am (15 mins) |
Introduction by the Academic Authorities to the event OWASP European Tour 2013 - Rome | Università Degli Studi Roma Tre | |||
| 9:45 am (45 mins) |
OWASP Shepherd project | Mark Denhian, David Ryan and Paul McCann | Competing in CTF events can be difficult for some and winning them can even be strenuous. Behind the curtains creating a fun and resilient CTF to be played with in the first place is the near impossible challenge. The Honeyn3t Ireland team have spent the last better part of a year working on providing CTFs. This talk will chronicle how to run a successful CTF by highlighting the common mistakes made and by utilising existing OWASP projects | Slides | |
| 10:30 am (30 mins) |
PCI for Developers | Fabio Cerullo, OWASP Dublin Chapter, CEO & Founder of Cycubix | The PCI-DSS and PA DSS standards are well known to security professionals and auditors, but how are these interpreted by software development teams? Usually is not clear whether all requirements are necessary and most importantly, how these should be implemented. This talk aims to help developers understanding the key points of these standards in a simple and fast approach and be able to implement them during the software development cycle | Slides | |
| 11:00AM (30 mins) |
Scripting Application Security | Dinis Cruz, OWASP O2 Platform project leader | Pentesting at the speed of Scripting (using O2 Platform)
This presentation will show how the OWASP O2 Platform scripting capabilities can be used to 'codify' an pen-testers mind/action and perform advanced analysis, fuzzing and exploitation of both Web and desktop-based Applications. |
- | |
| 11:30 am (30 mins) |
Client-Side Security in the modern Web | Mauro Gentile, Software Security Consultant of Minded Security | The web is evolving day by day: interactive and effective web applications are progressively adopted in the Internet thanks to innovative solutions implemented in modern web browsers. These latters offer sensational capabilities for running complex applications since client-side scripting languages ensure flexibility and varied functionalities. As the complexity of the web moves on the client-side, web security needs to shift its focus on this part too; indeed, enriching browsers capabilities may pave the way to new possible threats and attack surfaces. In this talk, we analyse how the adoption of HTML5 impacted the Web in terms of security and we dissect how attackers might exploit such introduction in order to realize successful attacks. By touching novel XSS attack vectors, clickjacking techniques, CSRF exploits, and cross domain communication approaches, we present interesting and real attack methodologies, and at the same we report robust defenses, such as CSP, against these today's threats by trying to understand the hindrances which could slaken their adoption. Eventually, practical examples are provided for each discussion point and the behaviors of the parties, which are involved in the attack, are considered in order to understand how attackers move, how victims are cheated and how developers should act. | Slides | |
| 12:00 am (30 mins) |
Android Apps permissions model (in)security | Davide Danelon, Software Security Consultant of Minded Security | Android devices, as well as applications developed for them, are growing exponentially and, as result, the personal data that users retain on such devices are increasing. Android has made of the "permissions model", a flag of the security of the operating system. How this model turns out to be really secure? Can an application, that do not require any permission, access to sensitive data and send them to a remote handler? We will focus on the security management of Android and how this model can be, in part, bypassed independently from the version in use. In the example shown, an application, seemingly harmless, is able to steal the data stored on a device updated to the latest version, currently available, of Android. | Slides | |
| OWASP EU TOUR 2013 | |||
| == TRAINING SESSIONS == | |||
| SPAIN - Barcelona | |||
| Date | Location | ||
| Jueves, 13 de junio de 2013 09:00h - 18:00h |
Universitat Ramon Llull, La Salle - URL Sant Joan de La Salle, 42 E-08022 Barcelona, Spain Aula: MFS.03 | ||
 Fabio Cerullo |
Taller: Desarrollo Seguro usando OWASP ESAPI Este curso tiene como objetivo proporcionar los conocimientos y recursos necesarios para mejorar la seguridad de las aplicaciones Java utilizando las librerias OWASP Enterprise Security API (ESAPI). Estas librerias se han diseñado para que sea más fácil para los desarrolladores mejorar la seguridad en aplicaciones existentes, como asi tambien utilizarlas como base para el desarrollo de nuevas aplicaciones. Los principios generales aprendidos en el curso se puede aplicar en el contexto de otros lenguajes de programación.
Perfil del instructor Fabio Cerullo, CEO y fundador de Cycubix, ayuda a clientes de todo el mundo a mejorar la seguridad de aplicaciones desarrolladas internamente o por terceros, mediante la definición de políticas y normas, implementando iniciativas de desarrollo seguro y gestión de riesgos, así como brindando capacitación sobre el tema a desarrolladores, auditores, ejecutivos y profesionales. Duracion: 8 horas (09:00h - 18:00h)
Precio: 250€ No miembros / 200€ Miembros OWASP. Existen tambien descuentos para grupos y miembros de ATI.
Regístrese a este taller: HAGA CLIC AQUI! | ||
| Date | Location | ||
| Jueves, 13 de junio de 2013 14:00h - 18:00h |
Universitat Ramon Llull, La Salle - URL Sant Joan de La Salle, 42 E-08022 Barcelona, Spain Aula: MFS.04 | ||
 Simón Roses |
Taller: OSINT + Python = Custom Hacking Workshop Taller práctico que combina el arte de OSINT (Open Source Inteligence) mediante el desarrollo de scripts en Python utilizando diversas API y librerías disponibles. A lo largo del taller se realizarán ejercicios prácticos con el objetivo de asimilar los conceptos por parte del alumno. Para entrar en materia se recomienda la lectura del siguiente artículo: Perfil del instructor Simón Roses eslicenciado en Informática por Suffolk University (Boston), Postgrado en E-Commerce, Harvard University (Boston) y Executive MBA, Instituto de Empresa (Madrid). En la actualidad es el CEO de VULNEX. Anteriormente formó parte de Microsoft, PriceWaterhouseCoopers y @Stake. Creador y colaborador en varios proyectos de código abierto de seguridad como OWASP Pantera y LibExploit, además de publicar avisos en seguridad de conocidos productos. Ponente habitual en eventos del sector de seguridad incluyendo BlackHat, RSA, OWASP, DeepSec, Source y Technets de seguridad de Microsoft. CISSP, CEH y CSSLP. Duracion: 4 horas (14:00h - 18:00h)
Precio: 125€ No miembros / 100€ Miembros OWASP. Existen tambien descuentos para grupos y miembros de ATI.
Regístrese a este taller: HAGA CLIC AQUI!. | ||
| Date | Location | ||
| Jueves, 13 de junio de 2013 09:00h - 13:00h |
Universitat Ramon Llull, La Salle - URL Sant Joan de La Salle, 42 E-08022 Barcelona, Spain Aula: MFS.04 | ||
 Matias Katz |
Taller: OWASP Top 5 Esta formación incorporará las técnicas de ataque a plataformas Web más importantes en la actualidad, estandarizadas mediante la norma OWASP Top 5. El curso presentará al alumno la forma de realizar estos ataques, y las contramedidas necesarias para mitigar su riesgo en sus desarrollos. La clase contará con contenido teórico y demostraciones prácticas e interactivas de laboratorio. Esta formación está orientada a desarrolladores, administradores de bases de datos, analistas de sistemas, auditores de seguridad, jefes de proyecto, así como cualquier otro interesado en las principales técnicas de ataque y defensa en aplicaciones Web.
Perfil del instructor Matias Katz is an IT architect and a security specialist. He's CISSP, CEH and MCSE certified, and has 10 years of experience in the field, focusing in the implementation of security audits, in infrastructures and critic applications for big organizations, both private and public. After working at IBM for several years, in 2008 Matias founded Mkit Argentina (link: http://www.mkit.com.ar), a company that specializes in performing security audits, vulnerability analysis and penetration tests to organizations, companies and the public sector. The company also gives training of a high technical level for companies, organizations and end-users. Matias also works as an external consultant for the computer crimes division of the federal police department in Argentina, where he collaborates in open cases through the acquirement of digital evidence and performing active investigations for the potential suspects. He is a professor in 3 universities in Argentina, both in engineering courses and information security post-graduate degree courses. He has presented at some of the most important security conferences, like BlackHat, Ekoparty, H2HC, Campus Party. He has dozens of published papers, and has created many tools used daily by security professionals world-wide, for their security audits.
Duracion: 4 horas (09:00h - 13:00h)
Precio: 125€ No miembros / 100€ Miembros OWASP. Existen tambien descuentos para grupos y miembros de ATI.
Regístrese a este taller: HAGA CLIC AQUI!.
| ||
| Ireland - Dublin | |||
| Date | Location | ||
| Tuesday, June 25th, 2013 09:00h - 18:00h |
TCube 32 - 34 Castle Street, Dublin 2, Ireland | ||
 Paco Hope |
DEFENSIVE PROGRAMMING – JAVASCRIPT AND HTML5 HTML5 is the fifth revision of the HTML standard. HTML5, and its integration with JavaScript, introduces new
security risks that we need to carefully consider when writing web front-end code. Modern web-based software, including
mobile web front-end applications, makes heavy use of innovative JavaScript and HTML5 browser support to deliver
advanced user experiences. Front-end developers focus their efforts on creating this experience and are generally not aware
of the security implications of the technologies they use. The Defensive Programming – JavaScript/HTML5 course helps web front-end developers understand the risks involved with
manipulating the HTML Document Object Model (DOM) and using the advanced features of JavaScript and HTML 5 such as
cross-domain requests and local storage. The course reinforces some important security aspects of modern browser
architecture and presents the student with defensive programming techniques that can be immediately applied to prevent common vulnerabilities from being introduced. Additionally, the course provides a detailed description of typical JavaScript sources and sinks and explains how they can be used to detect problems in code. Prerequisites: Students should be familiar with Web programming environments and technologies including JavaScript
and HTML. Completion of the Foundations of Software Security, Attack and Defense, or OWASP Top Ten + 2 courses is
highly recommended.
Instructor Profile Mr. Hope is a Principal Consultant for Cigital with over 12 years experience in the securing of software and systems. He sets the technical direction in Europe and leads consultants delivering static source code analysis, architectural risk assessments, vulnerability assessments, and penetration tests. His experience covers web applications, online gaming (gambling), embedded gaming devices, lotteries, and business-to-business transaction systems. He has assessed systems for small startups with thousands of lines of code, and massive enterprises with thousands of applications and millions of lines of code. He is a frequent conference speaker at such venues as OWASP, RSA (US and Europe), Security B-Sides, and SecAppDev. He speaks on issues like integrating security into the software development lifecycle (SDLC), securing web applications, and secure random number generation. Paco is also involved in the leadership of the London Chapter of (ISC)2. He also serves on (ISC)2's Application Security Advisory Board, helping to advise on the direction of the Certified Secure Software Lifecycle Professional (CSSLP) certification. He has held the CISSP for nearly 10 years and the CSSLP since shortly after its creation. Mr. Hope has co-authored two books on software security: the Web Security Testing Cookbook and Mastering FreeBSD and OpenBSD Security. He has also authored a chapter of Gary McGraw's Building Security In.
Duration: 8 hours (09:00h - 18:00h)
Price: 350€ Non members / 300€ OWASP members.
Registration link: Register here. | ||
| ITALY - Rome | |||
| Date | Location | ||
| Friday 28th June 09:00h - 13:00h |
Università Degli Studi Roma Tre | ||
 Giorgio Fedon |
Title: Mobile Application Security and Security Development Introduction Students will learn mobile hacking techniques and remediation strategies for Android and iPhone operating systems. They will understand platform security models, mobile application secure design, mobile application security errors, mobile application vulnerabilities related to in-house development. Exploiting techniques for operating system components are explained in the extent they may impact on a company SSDLC process for their mobile applications.
Instructor Profile
Giorgio Fedon is the COO and a cofounder of Minded Security, where he is responsible for running daily operations of the company and managing Professional Services. Prior to founding Minded Security, Giorgio was employed as senior security consultant and penetration tester at Emaze Networks S.p.a., delivered code auditing, Forensic and Log analysis, Malware Analysis and complex Penetration Testing services to some of the most important Companies as Banks and Public Agencies in Italy. He participated as speaker in many national and international events talking mainly about web security and malware obfuscation techniques. He was also employed at IBM System & Technology Group in Dublin (Ireland).
Language: English and Italian
Duration: 4 horas (09:00h - 13:00h)
Price: The prices are: 125 Euro for non members / 100 Euro for members.
Registration Link: Register Here.
| ||
The OWASP Europe 2013 CTF online competition is OFFLINE. To register and play visit the following URL: TBD
Background information
Ever wonder what a CTF is, or ever been curious to have a go - but have no idea where to start? OWASP Security Shepherd has been designed and implemented with the aim of fostering and improving security awareness among a varied skill-set demographic. This project enables users to learn or to improve upon existing manual penetration testing skills.
The guys from Honeyn3t Ireland have created a customised version of the OWASP Security Shepherd for the OWASP EU Tour 2013.
More info about this project here:
https://www.owasp.org/index.php/OWASP_Security_Shepherd
Competition Rules
- No Denial of Service Attacks.
- No automated Scans (you might get banned).
- Do not generate large amounts of traffic.
- No destructive attacks (don't delete stuff).
- Please confine your hacking on the tasks that are explicitly free to hack.
- If you find a cheat or trick to solve things more easily, please report it for Bonus Points.
- The organizers might change the rules throughout the challenge.
- Participants breaking these rules might be penalized or excluded from the competition.
Winner Prize
- 1st Prize: An admission ticket to OWASP AppSec EU Conference to be hosted in Hamburg, Germany this August 2013.
- 2nd Prize: An Amazon gift card worth U$50.
Winner Announcement
The winners will be announced TBD.
Sponsorship
You could find all available sponsorship options for the OWASP EU Tour clicking here
Europe Tour Team
Chapter Leaders
- Adrian Winckles (Cambridge Chapter)
- Simon Bennetts (Manchester Chapter)
- Justin Clarke (London Chapter)
- Colin Watson (London Chapter)
- Jamie Shaw (East Midlands Chapter)
- Mark Goodwin (East Midlands Chapter)
- Ludovic Petit (France Chapter)
- Sebastien Deleersnyder (Belgium Chapter)
- Fiona Walsh (Dublin Chapter)
- Eoin Keary (Dublin Chapter)
- Fabio Cerullo (Dublin Chapter)
- Matteo Meucci (Italian Chapter)
Operations
Gold Sponsors |
||

|

| |
Sponsors |
||

|
||
Event Supporters | ||

|

| |
Educational Supporters |
||
| |

|

|

|

|

|

|
| |
Community Supporters |
||

|

|

|

|

|

|

|

|