This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Category:OWASP WebGoat Project"
(→Future Development) |
(→Future Development) |
||
| Line 63: | Line 63: | ||
'''New Features in 5.x''' | '''New Features in 5.x''' | ||
| − | * XSS phishing lesson is available via the source code project at Google. Using a standard search feature, your mission is create a "login" form on the page, steal the user credentials, and post the credentials to the WebGoat Catcher servlet. | + | * XSS phishing lesson is available via the source code project at Google. Using a standard search feature, your mission is to create a "login" form on the page, steal the user credentials, and post the credentials to the WebGoat Catcher servlet. |
* Catcher servlet. Want to prove your attack works? You can now write lessons where the attack can send sensitive information to the Catcher servlet. The Catcher servlet will write the posted values into the originating lesson's properties file. | * Catcher servlet. Want to prove your attack works? You can now write lessons where the attack can send sensitive information to the Catcher servlet. The Catcher servlet will write the posted values into the originating lesson's properties file. | ||
Revision as of 13:01, 26 March 2007
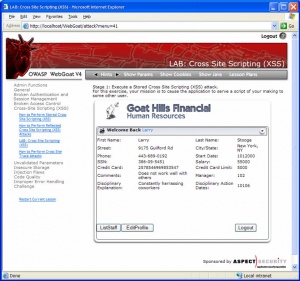
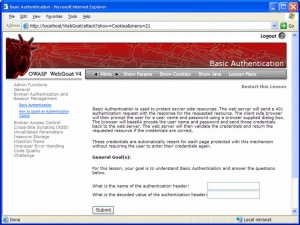
WebGoat is a deliberately insecure J2EE web application maintained by OWASP designed to teach web application security lessons. In each lesson, users must demonstrate their understanding of a security issue by exploiting a real vulnerability in the WebGoat application. For example, in one of the lessons the user must use SQL injection to steal fake credit card numbers. The application is a realistic teaching environment, providing users with hints and code to further explain the lesson.
Why the name "WebGoat"? Developers should not feel bad about not knowing security. Even the best programmers make security errors. What they need is a scapegoat, right? Just blame it on the 'Goat!
To get started, read the WebGoat User and Install Guide
Goals
Web application security is difficult to learn and practice. Not many people have full blown web applications like online book stores or online banks that can be used to scan for vulnerabilities. In addition, security professionals frequently need to test tools against a platform known to be vulnerable to ensure that they perform as advertised. All of this needs to happen in a safe and legal environment. Even if your intentions are good, we believe you should never attempt to find vulnerabilities without permission.
The primary goal of the WebGoat project is simple: create a de-facto interactive teaching environment for web application security. In the future, the project team hopes to extend WebGoat into becoming a security benchmarking platform and a Java-based Web site Honeypot.
Check out the project roadmap and find some tasks that you can help with right away.
Download
You can download WebGoat from the OWASP Source Code Center at Sourceforge. There are versions with and without Java, and installation only requires unzipping the download and running a start script. For convenience, a ready-to-deploy WAR file is also made available to drop right into your J2EE application server.
You can download the WebGoat source code from Google code.
The WebGoat distributions are now available at Google code downloads. The Windows WebGoat release (unzip, click, and run) is only available at Sourceforge due to file size limits.
Overview
WebGoat is written in Java and therefore installs on any platform with a Java virtual machine. There are installation programs for Linux, OS X Tiger and Windows. Once deployed, the user can go through the lessons and track their progress with the scorecard. There are currently over 30 lessons, including those dealing with the following issues:
|
|
For more details, please see the WebGoat User and Install Guide.
Newest Release
WebGoat 5.0
WebGoat 5.0 has been released. Special thanks to the many people who have sent comments and suggestions and those who have put in the effort to contribute their time to this release.
The 5.0 release would not have been possible without the efforts of Sherif Koussa and OWASP Autumn of Code 2006.
Please send all comments to webgoat AT g2-inc DOT com regarding this release candidate. A final release is scheduled for the end of January
Future Development
WebGoat 5.x - Estimated release date: Summer 2007
If you would like to become a member of the WebGoat source code project hosted at Google Code contact Bruce Mayhew at bruce DOT mayhew AT g2-inc.com.
New Features in 5.x
- XSS phishing lesson is available via the source code project at Google. Using a standard search feature, your mission is to create a "login" form on the page, steal the user credentials, and post the credentials to the WebGoat Catcher servlet.
- Catcher servlet. Want to prove your attack works? You can now write lessons where the attack can send sensitive information to the Catcher servlet. The Catcher servlet will write the posted values into the originating lesson's properties file.
- Documentation. A draft version of how to solve the WebGoat Labs is available at WebGoat Google Code Downloads
Project Contributors
The WebGoat project is run by Bruce Mayhew of G2. He can be contacted at bruce DOT mayhew AT g2-inc.com. WebGoat distributions are currently maintained on [SourceForge]. The WebGoat framework makes it extremely easy to add additional lessons. We are actively seeking developers to add new lessons as new web technologies emerge. If you are interested in volunteering for the project, or have a comment, question, or suggestion, please join the WebGoat [mailing list].
Project Sponsors
The WebGoat project is sponsored by

Pages in category "OWASP WebGoat Project"
The following 17 pages are in this category, out of 17 total.