This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Code Review and the SDLC"
(New page: ==Introduction== Integration of secure code review into the system development life cycle should yield dramatic results to the overall quality of the code developed. Secure code review is ...) |
|||
| Line 13: | Line 13: | ||
So on with the code review. | So on with the code review. | ||
| + | |||
| + | |||
| + | |||
| + | [[Image:Code_Review_-_SDLC.jpg]] | ||
Revision as of 15:14, 2 July 2008
Introduction
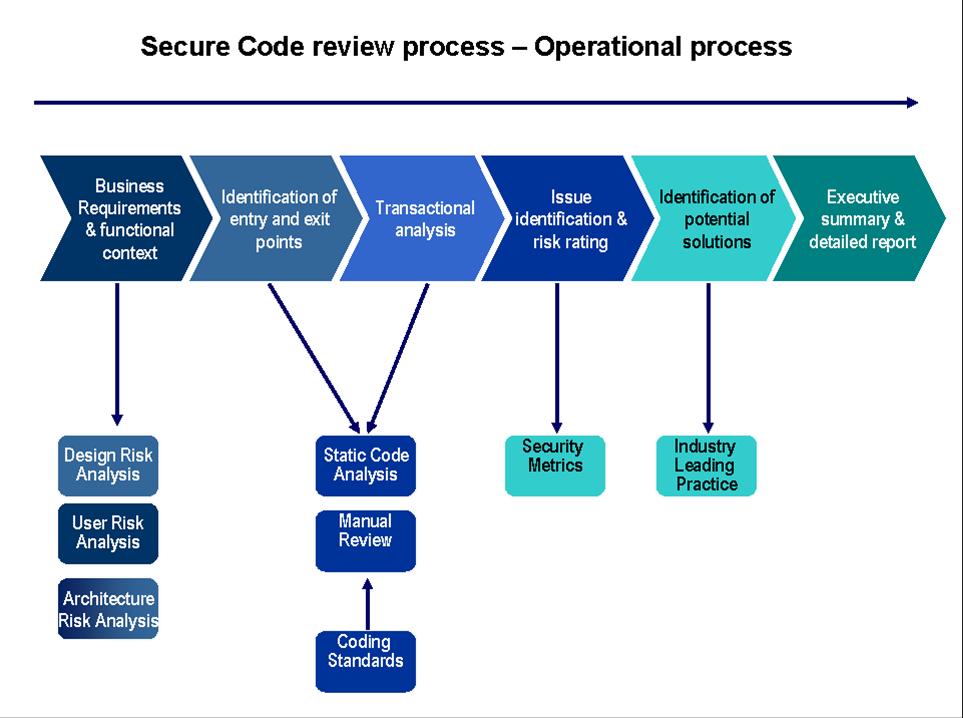
Integration of secure code review into the system development life cycle should yield dramatic results to the overall quality of the code developed. Secure code review is not a silver bullet but is part of a healthy application development diet. Consider it as one of they layers in a defence in depth approach to application security. Secure code review is also a cornerstone of the approach to developing secure software. The idea of integrating a phase into your SLDC may sound daunting, yet another layer of complexity or an additional cost but in the long term and in today’s cyber landscape it is cost effective, reputation building and in the best interest of any business to do so.
Where to start
To be honest, secure code review is not simply about reviewing code. If all that was required was to review code for correctness any automated grep tool could perform this. Code review is about establishing some context in the business sense around the code. At the end of the day we are not securing code for the codes sake but for what the code or application is protecting, the money, the business intelligence, the good stuff that gives business an edge or the data which equates to financial and capital assets.
So the context wherein an application is used is of key importance. An application is going to be attacked by professional criminals only if there is something within the application worth stealing.
In the case of code review prior to reviewing code we need to establish the risk profile of the application to be reviewed. The attack surface needs to be established and probability and impact of individual threat agent’s successfully executing an exploit.
Internal corporate policies and standards would also dictate the requirements for various categories of web application be it internal, external public, external B2B etc.
So on with the code review.