This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Rochester"
Dawnaitken (talk | contribs) |
(Updating now that the Juice Shop event has passed) |
||
| Line 6: | Line 6: | ||
== Upcoming Meetings & Events == | == Upcoming Meetings & Events == | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | + | No events currently scheduled | |
| − | |||
| − | |||
| − | |||
| − | |||
== Participation == | == Participation == | ||
| Line 55: | Line 39: | ||
== Past Events == | == Past Events == | ||
| + | ; '''OWASP Juice Shop Workshop''' | ||
| + | ; '''July 18th, 2018''' | ||
| + | ; '''5:30 pm - 8:00 pm''' | ||
| + | ; '''44 Celebration Drive, Conference Rooms 2007a and 2007b''' | ||
| + | |||
| + | We're looking for chapter members who are familiar with basic application security and the OWASP Top 10 who are interested in learning OWASP Juice Shop. The goal is to help plan and facilitate a larger capture-the-flag event at a future meeting. Please bring a Laptop with a WiFi network connection and a modern web browser. You will be installing OWASP Juice Shop on your laptop. | ||
| + | |||
| + | ; '''What is OWASP Juice Shop?''' | ||
| + | |||
| + | OWASP Juice Shop is an intentionally insecure web app for security trainings written entirely in JavaScript which encompasses the entire OWASP Top Ten and other severe security flaws. Juice Shop is written in Node.js, Express and AngularJS. https://www.owasp.org/index.php/OWASP_Juice_Shop_Project | ||
| + | |||
| + | ; '''What will the workshop cover?''' | ||
| + | |||
| + | Jim Keeler will lead the workshop. Attendees will learn about the OWASP Juice Shop project, installation and setup, how to exploit common web application vulnerabilities, jeopardy style capture-the-flag (CTF) events, and CTF scoreboards. At the end of the workshop we will be looking for volunteers to help us host a future CTF event! Pizza will be provided. '''Please RSVP to Ralph Durkee, <[email protected]> so that we may expect you.''' | ||
| + | |||
| + | ; '''Directions''' | ||
| + | |||
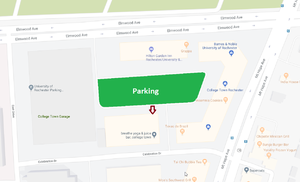
| + | [[File:UofRMC Map.png|thumb]] | ||
| + | Park anywhere in the green area. You can enter from Elmwood Ave going eastbound only or from Celebration Drive. Parking is free in the labeled surface lot. Enter the building by the arrow. Take the stairs or elevator to the 2nd floor. Take a right off the elevator and you should be able to easily find room 2007. | ||
| + | |||
| + | |||
| + | |||
; '''OWASP Rochester Social Event''' | ; '''OWASP Rochester Social Event''' | ||
Please join the Rochester OWASP chapter for a social event Wednesday, April 25th at MacGregors' in Henrietta. | Please join the Rochester OWASP chapter for a social event Wednesday, April 25th at MacGregors' in Henrietta. | ||
Revision as of 22:15, 1 August 2018
Welcome to the OWASP Rochester Local Chapter
Welcome to the local Rochester chapter homepage. The chapter leaders are Ralph Durkee and John King
Upcoming Meetings & Events
No events currently scheduled
Participation
OWASP chapter meetings are free and open to anyone interested in application security. We encourage members to give presentations on specific topics and to contribute to the local chapter by sharing their knowledge with others.
Mailing Lists:
Prior to participating with OWASP please review the Chapter Rules.
Local Officers
- President: Vacant
- Vice President: Ralph Durkee
- Treasurer: Ralph Durkee
- Secretary: Appointed by Event Coordinator at each meeting.
- Event Coordinator: Vacant
- Communications and Chapter OWASP Evangelist: Vacant
- Webmaster: John King
- Mail List Administrator: John King
Meeting Dates & Location
Dates: Meetings are announced via the announcement mailing list and on the website. Meetings reminders are sent to the OWASP Rochester Announcement distribution list at least one week prior to a meeting.
If you or your organization is interested in sponsoring a meeting or hosting a meeting please contact one of the local officers listed above.
Past Events
- OWASP Juice Shop Workshop
- July 18th, 2018
- 5:30 pm - 8:00 pm
- 44 Celebration Drive, Conference Rooms 2007a and 2007b
We're looking for chapter members who are familiar with basic application security and the OWASP Top 10 who are interested in learning OWASP Juice Shop. The goal is to help plan and facilitate a larger capture-the-flag event at a future meeting. Please bring a Laptop with a WiFi network connection and a modern web browser. You will be installing OWASP Juice Shop on your laptop.
- What is OWASP Juice Shop?
OWASP Juice Shop is an intentionally insecure web app for security trainings written entirely in JavaScript which encompasses the entire OWASP Top Ten and other severe security flaws. Juice Shop is written in Node.js, Express and AngularJS. https://www.owasp.org/index.php/OWASP_Juice_Shop_Project
- What will the workshop cover?
Jim Keeler will lead the workshop. Attendees will learn about the OWASP Juice Shop project, installation and setup, how to exploit common web application vulnerabilities, jeopardy style capture-the-flag (CTF) events, and CTF scoreboards. At the end of the workshop we will be looking for volunteers to help us host a future CTF event! Pizza will be provided. Please RSVP to Ralph Durkee, <[email protected]> so that we may expect you.
- Directions
Park anywhere in the green area. You can enter from Elmwood Ave going eastbound only or from Celebration Drive. Parking is free in the labeled surface lot. Enter the building by the arrow. Take the stairs or elevator to the 2nd floor. Take a right off the elevator and you should be able to easily find room 2007.
- OWASP Rochester Social Event
Please join the Rochester OWASP chapter for a social event Wednesday, April 25th at MacGregors' in Henrietta.
Appetizers will be provided.
When: Wednesday, April 25 at 5:30pm
Where: MacGregors' Grill and Tap Room (300 Jefferson Rd, Rochester, NY)
- OWASP Rochester Social Event
Please join the Rochester OWASP chapter for a social event Wednesday, December 6th at MacGregors' in Henrietta.
Appetizers will be provided.
When: Wednesday, December 6 at 5:30pm
Where: MacGregors' Grill and Tap Room (300 Jefferson Rd, Rochester, NY)
- Rochester Security Summit
Date: Oct 19-20, 2017
OWASP Track (day 2):
- Keynote: David Kennedy
- Beyond the Top 10 (John N. King, Mary Beth King)
- How Billion Dollar Enterprises Manage Application Security at Scale (Altaz Valani)
- Almost Intractable Application Security Problems… and Solutions (Danny Harris)
Joint OWASP-ISSA Rochester Chapter Meeting
July 13, 2017
6:00pm
Nixon Peabody
1300 Clinton Square, 14th Floor
How Billion Dollar Enterprises Manage Application Security at Scale
Security Compass recently completed a research study by surveying companies across multiple industries with the goal of discovering how large, complex organizations address application security at scale. The majority of respondents surveyed were multinational organizations who reported annual earnings greater than $1 billion USD. Through this new research study, we have gleamed novel insights on how large organizations manage application security at scale. Through this presentation, we will reveal aggregated insights, industry trends, and best practices that illuminate how organizations are addressing application security at scale, so that you may apply and compare these learnings to the state of application security at your own organization.
Speaker: Altaz Valani
Altaz Valani is a Research Director at Security Compass responsible for managing the overall research vision and team. Prior to joining Security Compass, Altaz was a Senior Research Director in the Application Development Practice at Info-Tech Research Group providing IT managers, directors, and senior managers with guidance and analysis around application development – including Agile, Cloud, Mobile, and the overall SDLC. His other past positions include Senior Manager at KPMG, and various entrepreneurial and intrapreneurial positions where he worked side by side with senior-level stakeholders at blue chip clients to drive business value through software development.
Altaz enjoys coding, teaching, and the challenge of learning. He received his BEng in Computer Engineering from McMaster University, and his MBA from the University of Western Ontario. AltazMAS!
Parking
Free parking is available underneath the building. Please bring your ticket with you for validation.
Entrance for parking: https://www.google.com/maps/dir/43.1558628,-77.605952/@43.1556506,-77.6077177,17.12z
OWASP Rochester Chapter Event
March 1, 2017
6:00pm to 7:15pm
Nixon Peabody
1300 Clinton Square, 13th Floor
Introduction to Application Security and OWASP Top 10 Risks (part 2 of 2)
Want to learn more about the security challenges developers face? This session will provide easy to understand, demo-driven examples of four common application vulnerabilities. You’ll see the attack in action, learn how the attack works, learn how it can be prevented, and watch a successful defensive counter.
This session will be covering the following components of the OWASP Top 10:
- A1 – Injection
- A3 – Cross-Site Scripting (XSS)
- A8 – Cross-Site Request Forgery (CSRF)
- A10 – Unvalidated Redirects and Forwards
The source code used in the demo is freely available and uses a Java/JEE stack.
Slides: http://www.johnnking.com/slides/owasp2017/
Source code: https://github.com/JohnNKing/appsecdemo
Speaker: John King
John is an experienced developer with a special focus on application security, enterprise software, and Agile product development. He’s a Senior Web Programmer / Analyst for RIT, an Officer of the Rochester Chapters of ISSA and OWASP, and has been a contributor to the Rochester Security Summit for the past four years.
OWASP Rochester Chapter Event
November 18, 2016
Noon to 1:15pm
RIT, GCCIS
GOL-2130 (Air Gap Lab)
Introduction to Application Security and OWASP Top 10 Risks (part 1 of 2)
Application Security is really hot and very much in demand. Find out why it’s so hot and get an in-depth introduction to application security and 6 of the OWASP Top 10 Application Risks. Ralph will discuss the how-to of the exploits and defenses for:
- A2 – Broken Authentication and Session Management
- A4 – Insecure Direct Object References
- A5 – Security Misconfiguration
- A6 – Sensitive Data Exposure
- A7 – Missing Function Level Access Control
- A9 – Using Components with Known Vulnerabilities
Speaker: Ralph Durkee
Ralph is the principal security consultant and owner of Durkee Consulting, Inc since 1996. Ralph started the OWASP Rochester, NY chapter in 2004 and served as founding officer and president for the Rochester ISSA chapter and the annual Rochester Security Summit. He routinely performs network and application penetration tests, software security assessments and secure software development consultations for clients. His expertise in advanced penetration testing, incident handling, secure software development and secure Internet and web applications is based on over 30 years of hands-on technical experience. He has developed and taught a wide variety of professional security seminars including custom web application security training, and SANS SEC401 & SEC504 – Hacker Techniques and Incident Handling and CISSP bootcamp courses since 2004. Ralph also regularly consults on the development and implementation of a wide variety of security standards such as web application security, database encryption, Windows, and Linux security. Ralph also has done security consulting for compliance with the Payment Card Industry Data Security Standard, and holds the following certifications CISSP, C|EH, CRISC, GSEC, GCIH, GSNA, GCIA, GPEN and GXPN.
- Rochester Security Summit
Date: Oct 5-6, 2016
OWASP Track (day 2):
- Keynote: Jeremiah Grossman
- Introduction to Application Security and OWASP Top 10 Risks (Ralph Durkee & John King)
- Common Developer Crypto Mistakes (Kevin W. Wall)
- #DevOpsSec – Killing the Buzz? (Jason Ross)
- Web Application Firewall Evaluation with DevOps, SDLC and the New OWASP Core Rule Set (Chaim Sanders)
- OWASP Rochester Social Event (8/11/16, MacGregors')
Please join the Rochester OWASP chapter for a social event August 11th at MacGregors' in Henrietta.
Come out and discuss your favorite topics in application security! Appetizers will be provided.
When: Thursday, August 11 at 5:30pm
Where: MacGregors' Grill and Tap Room (300 Jefferson Rd, Rochester, NY)
- Understanding and Preventing Cross-Site Request Forgery Attacks
Date: Feb 10th, 12 Noon - 1:30pm Location: Univ of Rochester College Town – Building 3
- Speaker
- John King
- Slides http://www.johnnking.com/slides/csrf/
Ranked #8 on the OWASP Top 10, “Cross-Site Request Forgery (CSRF) is an attack that forces an end user to execute unwanted actions on a web application in which they're currently authenticated.” (OWASP Wiki)
CSRF vulnerabilities are commonplace and easily missed by developers who are unfamiliar with this class of attack. Unlike injection vulnerabilities, they do not become apparent during testing unless you know exactly what to look for. This session will provide an introduction to CSRF vulnerabilities, and will include an attack demonstration and practical examples that prevent this type of vulnerability.
John is a web application developer with 10+ years of experience, with a focus on product management, user-experience, and application security. He has recently joined RIT ITS as a Senior Web Programmer / Analyst. He also serves as an officer of the Rochester chapters of OWASP and ISSA, and helps plan the annual Rochester Security Summit.
- NodeJS Security
Date: Nov 6th 12 noon - 1:30pm Location: Univ of Rochester College Town – Building 3
- Speaker
- Jason Ross
NodeJS has become an industry standard for deploying agile web applications. This talk provides an introduction to NodeJS – what it is, what it isn’t, how to get it running, and common elements that get deployed with Node (such as Grunt and Bower). With a firm understanding of the platform, we'll then examine common problems and security risks associated with NodeJS applications, as well as what options are currently available to secure and audit NodeJS projects.
Jason Ross is a Senior Consultant specializing in web application testing, Android application and device testing, and incident response management. He has provided network and application vulnerability assessment & penetration testing to a wide range of clients, including US Government agencies and Fortune 100 companies. He has also developed and delivered training tools and programs to major clients on topics such as advanced mobile penetration testing and forensic techniques.
Jason has a background in network incident response, forensic analysis and Unix & Windows platform engineering. He is an independent security researcher, and has spoken at numerous security conferences, including BlackHat DC, BSides Las Vegas, DEF CON Skytalks, and various regional conferences. Jason is also an active participant in the anti-malware community, and works with several highly vetted trust groups to track, monitor, and mitigate malicious Internet activity.
- Introduction to OWASP Application Security – Building and Breaking Applications
Date: Sept 18th 12 noon - 1:30pm
- Speaker
- Ralph Durkee, Principal Security Consultant, CISSP, C|EH, GSEC, GCIH, GSNA, GCIA, GPEN
Application Security continues to be the most challenging and demanding area for securing our information. Even large organizations like Google and Microsoft that are well funded and have a strong commitment to security, have difficulty developing secure software. Too often, when a vulnerability is found and a software patch is provided, the initial patch is soon found to be lacking and is still vulnerable. The initial patch for the recent Android StageFright vulnerability is a prime example. So yes, writing secure software is a serious challenge, but it can be done. Knowing how to build secure software and how to break insecure software can be both fun and profitable. There is and will continue to be a growing demand for developers and application penetration testers that “get it”. We'll discuss specific examples from the OWASP Top 10 and the OWASP secure coding principles about how things can go very wrong, and what we can do to keep the bad guys out.
- OWASP Top 10 - https://www.owasp.org/index.php/Top10#OWASP_Top_10_for_2013
- OWASP Secure Coding Principles - https://www.owasp.org/index.php/Secure_Coding_Principles
Presentation Slides: https://www.owasp.org/images/e/ec/Durkee_OWASP_2015_09_AppSec.pdf
- Application Security for Agile and Continuous Delivery
Date: May 12th, 2015 6pm
- Speaker
- Douglass Wilson, IBM Distinguished Engineer
- CTO for Vulnerability, Risk and Compliance Products IBM Security Systems IBU
- Free food and drink, provide by our meeting Sponsor, IBM
- Location
- Mulconry's Irish Pub, 17 Liftbridge Lane East, Fairport, NY 14450
- Hands-on Ethical Hacking
- Preventing and Exploiting Stack Overflow Vulnerabilities
Date: Apr 15, 2015 5:30pm
- Speaker
- Ralph Durkee
- We'll have a hands-on Ethical Hacking training session on preventing and exploiting stack overflow vulnerabilities.
- In the session we'll discuss how to find a buffer overflow vulnerability and then develop a customized exploit for a stack based buffer overflow.
- We'll also discuss and test mitigating techniques such as address randomization, stack protections mechanisms, non-executable stacks and of course secure programming to prevent buffer overflows.
- Rochester Security Summit
Date: Oct 7-8, 2014 8am - 4:30pm Topics:
- Top Ten Web Defenses (Jim Manico)
- Ethical Hacking: Preventing and Writing Exploits for Buffer Overflows (Ralph Durkee)
- Docker and Linux Containers for Infosec Professionals (Matt Kaar)
- Building a Software Security Program (Kuai Hinojosa)
Location: Hyatt Regency, Rochester, NY 14604
- June 20 2014 Meeting
Topic: Security Development Lifecycle Speaker: Larry Kovnat (CISSP, CISM) Location: Nixon Peabody, 1300 Clinton Square, Rochester, NY 14604 Speaker: Larry Kovnat (CISSP, CISM) Location: Nixon Peabody, 1300 Clinton Square, Rochester, NY 14604
- April Meeting 2013
Topic: Ethical Hacking as a Professional Penetration Testing Technique
Speaker: Ralph Durkee, Durkee Consulting
https://www.owasp.org/images/f/fc/Ralph_Durkee_Pen_Test_v24L_handout.pdf
- May 2012
Mercury Networks Security Summit
Tpoic: Mozilla's Content Security Policy
Speaker: Lou Leone
https://www.owasp.org/images/9/95/2012_CSP.pptx
- May 2011 Meeting
Michael Coates webinar on Attack-Aware Applications.
https://owasp.webex.com/owasp/ldr.php?AT=pb&SP=MC&rID=87764002&rKey=14191b8f8c73dabc
- May 5, 2011
MercuryFest Speakers: Ralph Durkee, Andrea Cogliati, Duane Peifer Topic: SSL Man-in-the-Middle and Spoofing Attacks
- March 2011 Meeting
Topic: Pastebin Scrapping
Speaker: Silas Cutler, Global Crossing, Security Architect
- January 2011 Meeting
Topic: State of OWASP and the State of Web Application Security
Speaker: Ralph Durkee, Durkee Consulting
- August Meeting 2010
Topic: Man in the Middle Attacks: SSL Spoofing
Speaker: Duane Peifer, UberGuard Information Security and Ralph Durkee, Durkee Consulting
- June Meeting 2010
Topic: Client Side Exploits 101
Speaker: JP Bourget, BS IT, RIT 2005; MS Computer Security and Information Assurance, RIT 2008; CISSP; MCSE, CSS
- May Meeting 2010
Topic: New Techniques in Application Intrusion Detection
Speaker: Al Huizenga, Director of Product Management, Mykonos Software, Inc.
- February Meeting 2010
Ralph Durkee presented a recap of the recent AppSec conference in DC.
Andrea Cogliati gave a talk on Identity Federation and Claim-based Security.
- Oct 29-30 2008 - Rochester Security Summit 2008
- The Rochester OWASP chapter in partnership with other Rochester institutions is organizing the third annual Rochester Security Summit Oct 29-30 during National Cyber Security Awareness Month. This year we'll have a full day dedicated to application security and we are are working to bring to Rochester the best national acclaimed speakers.
Visit Rochester Security Summit Site for details.
Past Presentations
Mercury Networks Security Symposium May 2012 I'll see your cross site scripting and raise you a Content Security Policy by Lou Leone Presentation - PPTX
January Meeting 2011 State of OWASP and the State of Web Application Security by Ralph Durkee PPT PDF
August Meeting 2010 Man in the Middle Attacks: SSL Spoofing by Duane Peifer PPT PDF
August Meeting 2010 Man in the Middle Attacks: SSL Spoofing by Ralph Durkee PPT PDF
May Meeting 2010 New Techniques in Application Intrusion Detection by Al Huizenga PPTX PDF
May Meeting 2010 Identity Federation and Claim-based Security by Andrea Cogliati PDF
February Meeting 2010 DC AppSec Conference Recap by Ralph Durkee PPT
October Hackerfest 2009 Introduction to OWASP Rochester by Ralph Durkee, Lou Leone PPT
September OWASP 2009 Securing Apache Web Servers with Mod Security & CIS Benchmark by Ralph Durkee PPT Open Office
May OWASP 2009 Key Management - One Perspective by Lou Leone PPT
May IEEE 2009 Introduction to OWASP, presented by Ralph Durkee and Andrea Cogliati PPT
January 2009 Paranoid Programming Practices, by Lou Leone and Aaron Witt PPT
May 2008 Database Encryption, by Ralf Durkee PPT
January 2008 SQL Injection and Dynamic SQL, by Andrea Cogliati ZIP
September 2007 2007 OWASP Top 10 Most Critical Web Application Security Vulnerabilities, by Ralph Durkee PowerPoint
October 2006 The first of the OWASP top ten: unvalidated input, by Steve Buck. PowerPoint
April 2006 PGP: Encryption for e-mail and web applications, by Ralph Durkee PDF
February 2006 Identity Theft, Phishing and Pharming, by Danny Allan PDF
February 2006 Secure e-mail, by Thomas Bullinger PDF
January 2006 PCI Compliance, by Pat Massey, Ralf Durkee, Maureen Baran PDF
September 2005 Two Factor Authentication for Java Applications with Client Certificates, by Ralf Durkee PDF Open Office
April 2005 Avoiding Backend Exploitation of Mail Forms, by Max Kessler PowerPoint Open Office
March 2005 Bringing Two-Factor Authentication to Web Applications, by Michael Starks PowerPoint Open Office
February 2005 Insecure Storage, by Chris Karr PowerPoint
January 2005 Access Control and Session Mgmnt, by Steve Buck PowerPoint Open Office
November 2004 Intro to OWASP by Ralf Durkee. Demonstration of SQL Injection attack and prevention, by Paul Cupo PowerPoint