|
Instructions are in RED text and should be removed from your document by deleting the text with the span tags. This document is intended to serve as an example of what is required of an OWASP project wiki page. The text in red serves as instructions, while the text in black serves as an example. Text in black is expected to be replaced entirely with information specific to your OWASP project.
Project About
PROJECT INFO
What does this OWASP project offer you?
|
RELEASE(S) INFO
What releases are available for this project?
|
| what
|
is this project?
|
| Name: Secure code assurance tool (SCAT)
|
| Purpose: N/A
|
| License: N/A
|
| who
|
is working on this project?
|
| Project Leader(s):
|
| how
|
can you learn more?
|
| Project Pamphlet: Not Yet Created
|
| Project Presentation:
|
| Mailing list: N/A
|
| Project Roadmap: Not Yet Created
|
| Key Contacts
|
|
- Contact Michael Bergman @ to contribute to this project
- Contact Michael Bergman @ to review or sponsor this project
|
|
|
What is the Secure code assurance tool (SCAT)
Information security, risk assurance and compliance define the strategic direction of the organisation in security policies and requirements
Software development teams need to implement the strategic direction in code
Secure code assurance tool (SCAT) translates the strategic security direction into code level and testing guidance helping development teams correctly and consistently implement strategic security direction
- SCAT is a secure code assurance tool for both inhouse and third party development teams
- SCAT is designed to perform a “first line of defense” function for the software development teams
- SCAT ensures development teams understand security requirements, correctly implements these, have the testing evidence proving correct implementation and provides insight into development and test.ing efforts
Problems this project addresses
- Low levels of compliance as developers and testers don’t understand the complex security requirements and don’t know how to write code to implement it or test it
- Development teams see approvers as a blocker. Approvers and assurance delay release while development teams do a blind scramble for evidence to prove they have met the security requirements
- Risk managers struggle to answer basic questions like what is the highest priority risk across our application landscape, and therefore cannot prioritise or coordinate mitigation efforts. Resulting in duplication of effort and inconsistent implementation across teams
How does the Secure code assurance tool (SCAT) help
Promoting compliance to security requirements
- SCAT allows organisations to translate complex security requirements into code level and testing guidance for development teams. Enabling development teams to correctly and consistently implement these.
Integrating security
- SCAT wraps security theory, best practices and requirements into set of single purpose security screens. Then maps those screens to a specific SDLC phase. This mapping informs developers of the security requirements for that SDLC phase and gives them the tools to meet those requirements.
Minimising the impact of audit and assurance
- SCAT allows testers stores testing evidence against the critical application function and its associated risk. Providing traceability through requirements and centrally storing and publishing test evidence.
Informing risk based decision making
- SCAT shows, for each application critical function, how many test plans have test evidence and how many security requirements have secure code blocks. Allowing risk teams see which application critical functions need more testing effort and how that testing effort can best be coordinated and prioritized across the appalachian landscape
SCAT is a simple 5 screen MVC, C# web application with a small footprint that can be deployed to third party and inhouse development teams without further complicating development environment.
How to use the Secure code assurance tool
See below how the Security code assurance tool integrates security into the phases of software development
- Sprint planning phase
- Developers use the Identify risks screen
- To Select the application critical function they are developing/changing
- To identify the technologies they are using to develop/change the application critical function
- The Secure code assurance tools uses its internal mapping to automatically generate the security requirements associated with using this technology
See how to use the tools and its internal mapping to generate security requirements
- Development phase
- Developers use the Secure development screen
- To see and understand how to attack and prevent the risks associated with the critical function
- To see the secure code requirements to protect against exploitation
- To see the secure code block to guide developers to implement security requirement
- After development run a ZAP basic scan to verify security requirements have been correctly implemented
See how the tool helps developers understand security requirements and write secure code
- Testing phase
- Testers use the Secure testing screen
- To see the OWASP test plans required to test the risk mitigation efforts
- To attach testing result to the test plan as control assurance evidence proving the risk has been mitigated
- The Secure code assurance tool does not integrate with any testing tools other than OWASP ZAP. Testing results generated outside of the secure code assurance tool is manually uploaded and stored
See how the tool helps testers test risk mitigation efforts and strore testing evidence
- Approval phase
- Risk management
- Risk managers use the Application risk exposure screen
- To see each application critical function and the associated risks
- To see the number of security requirements for each risk, and which of those requirements have secure code block. Allowing risk team to define where mitigation effort is required and monitors the progress of mitigation efforts
- To see the number of security tests for each risk. Allowing risk team to determine where extra testing effort is required and monitor test coverage and quality
See how the Application landscape overview screen informs risk based decision making
How does the Secure code assurance tool (SCAT) work
Promoting compliance to security requirements
- Firstly, understand the security requirement: The tool maintains the following internal mapping allowing organisations to translate complex security requirements into code level and testing guidance the development teams understand.
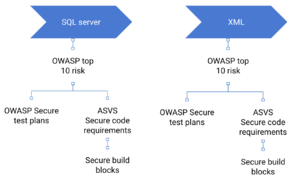
Technologies used in the organisation to secure code requirements
- Secure code requirements (OWASP ASVS) to secure code building block
- Secure test plans to OWASP top 10 risks (OWASP testing guide)
- The first and second mapping lifted from SKF and duplicated in the SCAT. I hope to link with the SKF and remove the duplicate functionality from the SCAT tool.
- Secondly, verify understanding: The tool also makes use of OWASP ZAP basic scan and simple risk training sandboxes to validate understanding and correct implementation
Integrating security
- In the sprint planning phase SCAT implements “shift left” and uses its internal mapping to generate security requirements before development begins
- In the Development phase SCAT implements “best practices” that explain security requirements, provides code level and testing guidance to correctly implement them and basic automatic security tooling to verify understanding and correct implementation
- In the Testing phase SCAT implements “traceability through requirements” and links security test evidence to the critical application function it tests
Tool setup
- Information security and development team can also
- Define new organisation specific risks and security requirements
- Link additional scanning tools
Security integration system
There are 3 domains to consider when securing software development.
- The secure software development process: Involves securing the way an organisation develops software. So any development change dropped into the process comes out secure on the other end.
- Developing secure code: Helping the development team produce secure code. By supporting the development team at each phase of the software development process
- Continuous improvement:..........
This OWASP project focuses on the Developing secure code domain and details the why and how behind the Secure code assurance tool.
I've detailed the other domains in an article that will be published in the Nov/Dec issue of the ISC2 magazine, I will add a link here after publication.
Do not review past this point
There are 3 domains to consider when securing software development.
- The secure software development process: Involves securing the way an organisation develops software. So any development change dropped into the process comes out secure on the other end.
- Developing secure code: Helping the development team produce secure code. By supporting the development team at each phase of the software development process
- Continuous improvement:..........
This OWASP project focuses on the Developing secure code domain and details the why and how behind the Secure code assurance tool.
I've detailed the other domains in an article that will be published in the Nov/Dec issue of the ISC2 magazine, I will add a link here after publication.
Why the Secure code assurance tool
Producing secure software requires the input of a number of teams
- Information security: Needs to understand the technology behind the functional requirement and its associated risks. Then generate a list of security requirements to protect the technology against exploitation
- Development teams: Need to implement the technology, test it and record evidence proving the security requirements are met and
- Approvers: Need to review testing evidence against the organisations risk tolerance levels. Then accept the risk associate with the functional requirement by approving the release
- Compliance and Assurance: Need to review the testing evidence collected by the development teams and verify its consistency, traceability and quality
- IT risk: Needs to manage and monitor risk mitigation efforts
Why is producing secure software so hard and how does the Secure code assurance tool help?
- Complex environments: Development, security, risk, compliance and assurance teams need to combine their GDPR, ISO, risk tolerances level, OWASP ASVS, security testing, JAVA and .Net knowledge, filter it, and generate security requirements for each critical application function. The process of aligning the knowledge and efforts of these teams is time consuming and slows down the development process
How does the tool help
- Centrally stores security requirements and links these to the technologies used in the organisation environment. Allowing developers to select the technology used to implement their functional requirement and automatically get a list of relevant security requirements
- Benefit: Developers can generate the security requirements themselves, without waiting on the security, risk, compliance and assurance teams. This will speed up the requirements generation process make it consistent and repeatable across all teams
- Huge number of complex security requirements: Development teams do not understand the complicated security requirements therefore cannot correctly implement or test them. Also, the flexibility of development languages almost guarantee that every developer will implement the security requirement differently
How does the tool help
- Stores a language specific and approved secure code building block against each security requirement. These guide developers towards constantly implementing the security requirements
- Stores a set of OWASP tests against each risk. Guiding the testing team on how to correctly validate the security requirement has been met
- Allows developers to run an "on demand" OWASP ZAP basic scan on their code. Enabling an immediate feedback loop to verify they have correctly implemented the security requirements
- Allows developers to open an "on demand" risk training sandbox environment. Training developers how to exploit and defend against the risk
- Compliance: Approvers review testing evidence to make sure development teams have complied to the ever increasing security and regulatory requirements. But finding the relevant testing evidence generated by testers or in CI\CD pipelines is a lengthy process that blocks the release
How does the tool help
- Centrally stores testing evidence alongside the risk and application critical function. Allowing approvers to quickly see if the critical application function has been tested and mitigated according to risk tolerance
- Risk management of the application landscape: Risk managers cannot
- see which security requirements do not have secure code blocks</il>
- see which risks need test plans or have not been tested
- see how a single security test can be re-used to test a different application risk
- see where mitigation efforts will have the most impact
How does the tool help
- Provides a dashboard view of application landscape giving risk managers the information they need to prioritise and manage risk efforts
Description
This is where you need to add your more robust project description. A project description should outline the purpose of the project, how it is used, and the value it provides to application security. Ideally, project descriptions should be written in such a way that there is no question what value the project provides to the software security community. This section will be seen and used in various places within the Projects Portal. Poorly written project descriptions therefore detract from a project’s visibility, so project leaders should ensure that the description is meaningful.
For a more detailed look at the inner workings of the tool and a brief instructional video please take a look at my linkedIn article
Secure coding tool
Licensing
A project must be licensed under a community friendly or open source license. For more information on OWASP recommended licenses, please see OWASP Licenses. While OWASP does not promote any particular license over another, the vast majority of projects have chosen a Creative Commons license variant for documentation projects, or a GNU General Public License variant for tools and code projects. This example assumes that you want to use the AGPL 3.0 license.
This program is free software: you can redistribute it and/or modify it under the terms of the link GNU Affero General Public License 3.0 as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version. OWASP XXX and any contributions are Copyright © by {the Project Leader(s) or OWASP} {Year(s)}.
Roadmap
As of November, 2013, the highest priorities for the next 6 months are:
- Complete the first draft of the Tool Project Template
- Get other people to review the Tool Project Template and provide feedback
- Incorporate feedback into changes in the Tool Project Template
- Finalize the Tool Project template and have it reviewed to be promoted from an Incubator Project to a Lab Project
Subsequent Releases will add
- Internationalization Support
- Additional Unit Tests
- Automated Regression tests
Getting Involved
Involvement in the development and promotion of Tool Project Template is actively encouraged!
You do not have to be a security expert or a programmer to contribute.
Some of the ways you can help are as follows:
|
Project Resources
This is where you can link to the key locations for project files, including setup programs, the source code repository, online documentation, a Wiki Home Page, threaded discussions about the project, and Issue Tracking system, etc.
Installation Package
Source Code
What's New (Revision History)
Documentation
Wiki Home Page
Issue Tracker
Slide Presentation
Video
Project Leader
A project leader is the individual who decides to lead the project throughout its lifecycle. The project leader is responsible for communicating the project’s progress to the OWASP Foundation, and he/she is ultimately responsible for the project’s deliverables. The project leader must provide OWASP with his/her real name and contact e-mail address for his/her project application to be accepted, as OWASP prides itself on the openness of its products, operations, and members.
Michael Bergman
Related Projects
This is where you can link to other OWASP Projects that are similar to yours.
Classifications
|