This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
IOS Application Security Testing Cheat Sheet
From OWASP
Revision as of 10:48, 3 August 2014 by Jason Haddix (talk | contribs)
[hide]
DRAFT CHEAT SHEET - WORK IN PROGRESS
Introduction
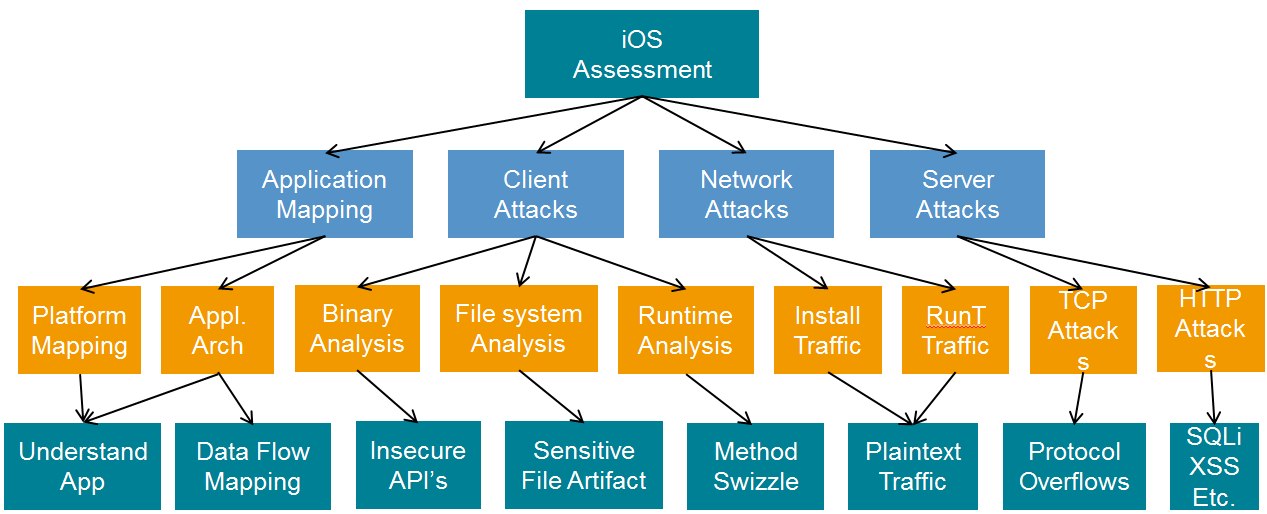
This cheat sheet provides a checklist of tasks to be performed when testing an iOS application.
When assessing a mobile application several areas should be taken into account: client software, the communication channel and the server side infrastructure.
Testing an iOS application usually requires a jailbroken device. (A device that not pose any restrictions on the software that can be installed on it.)
Information gathering
- Observe application behavior
- Determine the application’s data states (at rest, in transit or on display) and sensitivity
- Identify access methods
- Identify what frameworks are in use
- Identify server side APIs that are in use
- Identify what protocols are in use
- Identify other applications or services with which the application interacts
- Decrypt Appstore binaries: the .ipa will be decrypted at runtime by the kernel’s mach loader. Cydia has several applications available: Crackulous, AppCrack and Clutch. Also, you can use GDB. The “cryptid” field of the LC_ENCRYPTION_INFO identifies if the application is encrypted or not. Use otool –l <app name> | grep –A 4 LC_ENCRYPTION_INFO
- Determine the architecture the application was compiled for: otool –f <app name> or lipo -info <app>.
- Get information about what functions, classes and methods are referenced in the application and in the dynamically loaded libraries. Use nm <app name>
- List the dynamic dependencies. Use otool –L <app name>
- Dump the load commands for the application. Use otool –l <app name>
- Dump the runtime information from the compiled application. Identify each class compiled into the program and its associated methods, instance variables and properties. Use class-dump-z <app name>. That can be put that into a .h file which can be used later to create hooks for method swizzling or to simply make the methods of the app easier to read.
- Dump the keychain using dump_keychain to reveal application specific credentials and passwords if stored in the keychain.
Determine the security features in place:
- Locate the PIE (Position Independent Executable) - an app compiled without PIE (using the “–fPIE –pie” flag) will load the executable at a fixed address. Check this using the command: otool –hv <app name>
- Stack smashing protection - specify the –fstack-protector-all compiler flag. A “canary” is placed on the stack to protect the saved base pointer, saved instruction pointer and function arguments. It will be verified upon the function return to see if it has been overwritten. Check this using: otool –I –v <app name> | grep stack . If the application was compiled with the stack smashing protection two undefined symbols will be present: “___stack_chk_fail” and “___stack_chk_guard”.
Application traffic analysis
- Analyze error messages
- Analyze cacheable information
- Transport layer security (TLS version; NSURLRequest object )
- Attack XML processors
- SQL injection
- Privacy issues (sensitive information disclosure)
- Improper session handling
- Decisions via untrusted inputs
- Broken cryptography
- Unmanaged code
- URL Schemes
- Push notifications
- Authentication
- Authorization
- Session management
- Data storage
- Data validation (input, output)
- Transport Layer protection – are the certificates validated, does the application implement Certificate Pinning
- Denial of service
- Business logic
- UDID or MAC ID usage (privacy concerns)
Runtime analysis
- Disassemble the application (gdb)
- Analyze file system interaction
- Use the .h file generated with class-dump-z to create a method swizzling hook of some interesting methods to either examine the data as it flow through or create a "stealer" app.
- Analyze the application with a debugger (gdb): inspecting objects in memory and calling functions and methods; replacing variables and methods at runtime.
- Investigate CFStream and NSStream
- Investigate protocol handlers (application: openURL - validates the source application that instantiated the URL request) for example: try to reconfigure the default landing page for the application using a malicious iframe.
- Buffer overflows and memory corruption
- Client side injection
- Runtime injections
- Having access to sources, test the memory by using Xcode Schemes
Insecure data storage
- Investigate log files(plugging the device in and pulling down logs with Xcode Organizer)
- Insecure data storage in application folder (var/mobile/Applications), caches, in backups (iTunes)
- Investigate custom created files
- Analyze SQLlite database
- Investigate property list files
- Investigate file caching
- Insecure data storage in keyboard cache
- Investigate Cookies.binarycookies
- Analyze iOS keychain (/private/var/Keychains/keychain-2.db) – when it is accessible and what information it contains; data stored in the keychain can only be accessible if the attacker has physical access to the device.
- Check for sensitive information in snapshots
- Audit data protection of files and keychain entries (To determine when a keychain item should be readable by an application check the data protection accessibility constants)
Tools
| Tool | Link | Description |
|---|---|---|
| Mallory proxy | http://intrepidusgroup.com/insight/mallory/ | Proxy for Binary protocols |
| Charles/Burp proxy | http://www.charlesproxy.com/ ; | Proxy for HTTP and HTTPS |
| OpenSSH | http://www.openssh.com/ | Connect to the iPhone remotely over SSH |
| Sqlite3 | http://www.sqlite.org/ | Sqlite database client |
| GNU Debugger | http://www.gnu.org/software/gdb/ | For run time analysis & reverse engineering |
| Syslogd | https://developer.apple.com/library/mac/#documentation/Darwin/Reference/ManPages/man8/syslogd.8.html | View iPhone logs |
| Tcpdump | http://www.tcpdump.org/ | Capture network traffic on phone |
| Otool | http://developer.apple.com/library/mac/#documentation/Darwin/Reference/ManPages/man1/otool.1.html | Odcctools: otool – object file displaying tool |
| Cycript | http://www.cycript.org/ | A language designed to interact with Objective-C classes |
| SSL Kill switch | https://github.com/iSECPartners/ios-ssl-kill-switch | Blackbox tool to disable SSL certificate validation - including certificate pinning in NSURL |
| Plutil | http://scw.us/iPhone/plutil/ | To view Plist files |
| nm | Analysis tool to display the symbol table, which includes names of functions and methods, as well as their load addresses. | |
| sysctl | https://developer.apple.com/library/mac/#documentation/Darwin/Reference /ManPages/man8/sysctl.8.html | A utility to read and change kernel state variables |
| dump_keychain | https://github.com/emonti/iOS_app_re_tools | A utility to dump the keychain |
| Filemon | http://www.newosxbook.com/files/filemon.iOS | Monitor realtime iOS file system |
| FileDP | http://www.securitylearn.net/2012/10/18/extracting-data-protection-class-from-files-on-ios/ | Audits data protection of files |
| BinaryCookieReader | http://securitylearn.net/wp-content/uploads/tools/iOS/BinaryCookieReader.py | Read cookies.binarycookies files |
| lsof ARM Binary | https://github.com/u35tpus/iosrep/tree/master/lsof | list of all open files and the processes that opened them |
| lsock ARM Binary | http://www.newosxbook.com/index.php?page=downloads | monitor socket connections |
| PonyDebugger Injected | https://github.com/dtrukr/PonyDebuggerInjected | Injected via Cycript to enable remote debugging |
| Weak Class Dump | https://raw.github.com/limneos/weak_classdump/master/weak_classdump.cy | Injected via Cycript to do class-dump (for when you cant un-encrypt the binary) |
| TrustME | https://github.com/intrepidusgroup/trustme | Lower level tool to disable SSL certificate validation - including certificate pinning (for everything else but NSURL) |
| Mac Robber | http://www.sleuthkit.org/mac-robber/download.php | C code, forensic tool for imaging filesystems and producing a timeline |
| USBMux Proxy | https://github.com/st3fan/usbmux-proxy | command line tool to connect local TCP port sto ports on an iPhone or iPod Touch device over USB. |
| iFunBox | http://www.i-funbox.com/ | Filesystem access (no jailbreak needed), USBMux Tunneler, .ipa installer |
| iNalyzer | https://appsec-labs.com/iNalyzer/ | iOS Penetration testing framework |
| removePIE | https://github.com/peterfillmore/removePIE | Disables ASLR of an application |
| snoop-it | https://code.google.com/p/snoop-it/ | A tool to assist security assessments and dynamic analysis of iOS Apps, includes runtime views of obj-c classes and methods, and options to modify those values |
| idb | https://github.com/dmayer/idb | A GUI (and cmdline) tool to simplify some common tasks for iOS pentesting and research. |
| Damn Vulnerable iOS Application | http://damnvulnerableiosapp.com/ | A purposefully vulnerable iOS application for learning iOS application assessment skills. |
Related Articles
- http://www.slideshare.net/jasonhaddix/pentesting-ios-applications
- https://www.owasp.org/index.php/Projects/OWASP_Mobile_Security_Project_-_Security_Testing_Guide
- http://pen-testing.sans.org/blog/pen-testing/2011/10/13/mobile-application-assessments-attack-vectors-and-arsenal-inventory#
- http://www.securitylearn.net/2012/09/07/penetration-testing-of-iphone-applications-part-3/
- Jonathan Zdziarski “Hacking and securing iOS applications” (ch. 6,7,8)
- http://www.mdsec.co.uk/research/iOS_Application_Insecurity_wp_v1.0_final.pdf
Authors and Primary Editors
Oana Cornea - oanacornea123[at]gmail.com
Jason Haddix - jason.haddix[at]hp.com
Other Cheatsheets
OWASP Cheat Sheets Project Homepage