See below how the Secure code assurance tool integrates security into software development phases
- Sprint planning phase
Objective: Ensures security requirements are understood
- Developers use the Identify risks screen to
- Select the critical function to developing/changing
- Identify the technologies used
- Automatically generate the security requirements and tests
See how to use the tools and its internal mapping to generate security requirements
- Product owners use the Secure code requirements screen to
- Create an audit trail to store evidence of secure development
- Create Jira tickets for requirements and tests to manage work
- Development phase
Objective: Ensure correct implementation of security requirements
- Secure code review phase
Objective: Ensure correct implementation of security requirements
- Testing phase
Objective: Ensure valid security testing
- Approval phase
Objective: Streamline the approval and audit process
- Risk management
Objective: Enable risk managers to prioritise, plan and monitor mitigation efforts
- Risk managers use the Application risk exposure screen to
- View each application critical function and the associated risks
- Identify where mitigation effort is required by viewing which risks require security requirements
- Identify where development effort is required by viewing which security requirements need secure code blocks
- Identify where extra testing effort is required by viewing which risks require security test plans
See how the Application landscape overview screen informs risk based decision making
Preparation phase
When developing secure software we need to consider both standard secure code and client specific architectural requirements
Standard secure code requirements
- SCAT comes out the box with a standard OWASP secure code requirements map. This mapping need to be modified to the specific organisation requirements
- Information security and development team use the Internal mapping screen to
- Map the security requirements to OWASP risks
- Map organisation approved secure code blocks to security requirements
- Map security test plans to OWASP risks
See how to setup the SCAT's internal mapping
Client specific architectural requirements
- To generate these requirements we perform a risk assessment on client application landscape and identify
- Critical applications and functions
- Risk associated with each critical application function
- Architectural security requirements to secure each critical application functions
- Client specific secure code blocks to implement security requirements
- Secure test plans to verify risk has been mitigated
- Tool administrators use the Internal mapping screen to
- Create json files of the organisation specific risks, security requirements, secure code blocks and tests
- Import these into the SCAT
See how to import organisations specific risks, security requirements, secure code blocks and tests
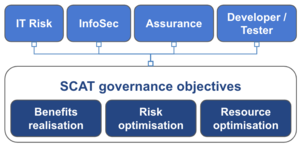
Governance, first line of defence and SCAT
SCAT has the following governance objectives implemented by the following “first line of defense” functions
Benefits realisation: Enabling development teams to deliver at speed
- Promoting compliance to security requirements
- Minimising the impact of audit and assurance
Risk optimisation: Minimise the negative and maximise the positive consequences
- Informing risk based decision making
Resource optimisation: Predictable, repeatable and consistent level of security across all teams
- Integrating security into the software development process
Promoting compliance to security requirements
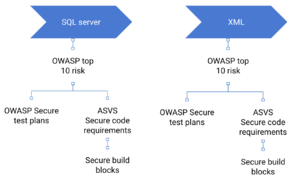
- Understand the security requirement: The tool maintains the following internal mapping allowing organisations to translate complex security requirements into code level and testing guidance
- Risks mapped to technologies and secure code requirements
- Secure code requirements (OWASP ASVS) mapped to secure code building block
- Secure test plans (OWASP testing guide) mapped to risks
- The second mapping is lifted from OWASP secure knowledge framework and duplicated in the SCAT. I hope to link with the SKF and remove the duplicate functionality from the SCAT tool
- Verify understanding: The tool also makes use of OWASP ZAP basic scan to scan localhost for vulnerabilities, confirming the correct implementation of security requirements
Minimising the impact of audit and assurance
- In the testing and approval phase SCAT allows testers to stores testing evidence against the critical application function and its associated risk. Providing traceability through requirements and centrally storing and publishing test evidence
Informing risk based decision making
- For each application critical function, SCAT shows
- The risks that impact that application critical function
- Security requirements and secure code block to protect against the risk
- Test evidence proving risk has been mitigated to within tolerance
- Allowing risk teams see levels of exposure, easily compare it to tolerance levels. And prioritise and coordinate mitigation activities across teams and the whole application landscape
Integrating security into the software development process
- SCAT wraps security theory, best practices and requirements into set of single purpose security screens. Then plots each of those screens to a specific software development phase
- Plotting security screens to specific software development phases provides development teams with concise information when and how they need it
Licensing
This program is free software: you can redistribute it and/or modify it under the terms of the link GNU Affero General Public License 3.0 as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version.
Project Resources
[Installation Package]
[Source Code]
Project Leader
Michael Bergman
Classifications