This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
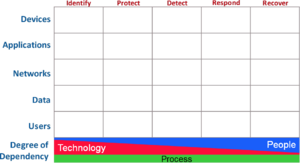
OWASP Cyber Defense Matrix
IntroductionImagine going into a grocery store to shop for Thanksgiving dinner, but instead of seeing nice, orderly aisles, you see a massive pile of food in the middle of the store. Finding the ingredients that you need to make dinner is going to be extremely hard because there’s no organizational system helping you understand where things are or if you already have something. The disorganization makes it very difficult to find what you need. The cybersecurity vendor marketplace is like this disorganized grocery store. A proof of this assertion can be seen by looking at the vendor hall at any major security conference. The cacophony of sounds from vendors hawking their wares, the confusing language of the vendor’s marketecture, and the lack of any semblance of organization (aside from biggest to smallest) does not help buyers understand what they need or where to find it. Because the cybersecurity community does not use consistent terminology to describe what we need, there is much confusion about what many vendor products actually do. Instead of a clear articulation of a product's capabilities, vendors bombard us with overused, trendy jargon that usually leaves buyers wondering if the product can really solve any of our woes. Some organizations even organize themselves according to the jargon. We need to stop letting marketing pitches dictate our terminology and not lose sight of the more bland descriptors that actually tell us what something does. The Cyber Defense Matrix helps us understand what we need organized through a logical construct so that when we go into the security vendor marketplace, we can quickly discern what products solve what problems and be informed on what is the core function of a given product. In addition, the Cyber Defense Matrix provides a mechanism to ensure that we have capabilities across the entire spectrum of options to help secure our environments. Although the Cyber Defense Matrix was initially created to help organize security technologies, many other use cases have been discovered to help build, manage, and operate a security program. This project intends to capture these use cases and their implementations to help security practitioners mature their security programs. DescriptionThe basic construct of the Cyber Defense Matrix starts with two dimensions. The first dimension captures the five operational functions of the NIST Cybersecurity Framework:
The second dimension captures five assets classes that we try to secure:
There is one more important piece of this matrix. At bottom of the grid, we show a continuum that characterizes the degree of dependency on technology, people, and process as we progress through the five operational functions of the NIST Cybersecurity Framework. TECHNOLOGY plays a much greater role in IDENTIFY and PROTECT. As we move to DETECT, RESPOND, and RECOVER, our dependency on TECHNOLOGY diminishes and our dependency on PEOPLE grows. Throughout all five operational functions, there's a consistent level of dependency on PROCESS. This continuum helps us understand where we might have imbalances in our reliance on PEOPLE, PROCESS, and TECHNOLOGY when trying to tackle our cybersecurity challenges. We believe that this matrix is a realistic model describes a broad range of cybersecurity practices. In this website, you will find several insights on the Cyber Defense Matrix and examples of how to leverage it to address the challenges that we face in cybersecurity. If you discover a new use of the Cyber Defense Matrix, we would love to hear about it. Likewise, if you find a problem with the matrix in that it doesn't seem to properly describe something that we do in cybersecurity, please point that out, and we'll either adjust the matrix or clarify how that problem can be address through the matrix. LicensingThe Cyber Defense Matrix, originally created by Sounil Yu, is licensed under the http://creativecommons.org/licenses/by-sa/4.0/ Creative Commons Attribution-ShareAlike 4.0 license, so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one. |
What is OWASP Security Principles Project?The end goal is to identify, cite, and document the fundamental principles of information security. Once this is well organised, I think it would be great to publish this through the OWASP Press. Of course, it will always remain freely available, and any money collected will go directly into the project to absorb costs with any remaining funds going to the OWASP Foundation. This document should serve as a guide to technical architects and designers outlining the fundamental principles of security. PresentationProject LeaderMailing List: [email protected]Related ProjectsOpenhub |
MAILING LISTNews and Events
Classifications
| |||||||||||||||||
Coming Soon..
How can I participate in your project?
Join the mailing list, say hello!
If I am not a programmer can I participate in your project?
Yes, you can certainly participate in the project if you are not a programmer or technical. The project needs different skills and expertise and different times during its development. Currently, we are looking for researchers, writers, graphic designers, and a project administrator.
Contributors
Everyone is invited to collaborate on this project.
April 5th 2017 project announced publicly at the OWASP NYC Chapter Meeting call for DATA is OPEN
June 2017 - Project Submitted and Approved by OWASP Foundation, page online
July 2017 - Planning for BlackHat/Defcon Face to Face Meet-Up
Aug 2017 - <Summer Hiatus>
Sept 2017 - AppSecUSA Project Summit
Come back soon..... working on that one ;:)