This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Internet of Things Project"
Aaron.guzman (talk | contribs) (→Medical Device Testing) (Tag: Visual edit) |
Aaron.guzman (talk | contribs) (FSTM) (Tag: Visual edit) |
||
| Line 1,079: | Line 1,079: | ||
* [https://github.com/scriptingxss/IoTGoat OWASP IoTGoat] | * [https://github.com/scriptingxss/IoTGoat OWASP IoTGoat] | ||
|- | |- | ||
| + | | | ||
| + | |}{{Social Media Links}} | ||
| + | |||
| + | | style="padding-left:25px;width:300px;border-right: 1px dotted gray;padding-right:25px;" valign="top" | | ||
| + | |||
| + | == What is the Firmware Analysis Project? == | ||
| + | |||
| + | The Firmware Analysis Project provides: | ||
| + | |||
| + | * Security testing guidance for vulnerabilities in the "Device Firmware" attack surface | ||
| + | * Steps for extracting file systems from various firmware files | ||
| + | * Guidance on searching a file systems for sensitive of interesting data | ||
| + | * Information on static analysis of firmware contents | ||
| + | * Information on dynamic analysis of emulated services (e.g. web admin interface) | ||
| + | * Testing tool links | ||
| + | * A site for pulling together existing information on firmware analysis | ||
| + | |||
| + | == Project Leaders == | ||
| + | |||
| + | * Craig Smith | ||
| + | |||
| + | == Related Projects == | ||
| + | |||
| + | * [[OWASP_Mobile_Security_Project|OWASP Mobile Security]] | ||
| + | * [[OWASP_Top_Ten_Project|OWASP Web Top 10]] | ||
| + | * [https://www.owasp.org/index.php/OWASP_Embedded_Application_Security OWASP Embedded Application Security Project] | ||
| + | |||
| + | == Collaboration == | ||
| + | [https://owasp-iot-security.slack.com The Slack Channel] | ||
| + | |||
| + | == Resources == | ||
| + | * [https://www.owasp.org/index.php/IoT_Firmware_Analysis IoT Firmware Analysis Primer] | ||
| + | * [https://otalliance.org/initiatives/internet-things Online Trust Alliance - Internet of Things] | ||
| + | * [https://people.debian.org/~aurel32/qemu/ Pre-compiled QEMU images] | ||
| + | * [https://code.google.com/archive/p/firmware-mod-kit/ Firmware Modification Kit] | ||
| + | * [https://craigsmith.net/episode-11-1-firmware-extraction/ Short Firmware Extraction Video] | ||
| + | * [https://craigsmith.net/episode-12-1-firmware-emulation-with-qemu/ Firmware Emulation with QEMU] | ||
| + | * [https://craigsmith.net/episode-18-1-file-extraction-from-network-capture/ File Extraction from Network Capture] | ||
| + | |||
| + | == News and Events == | ||
| + | * Coming Soon | ||
| + | |||
|} | |} | ||
= Firmware Security Testing Methodology = | = Firmware Security Testing Methodology = | ||
[[File:OWASP_Project_Header.jpg|link=]] | [[File:OWASP_Project_Header.jpg|link=]] | ||
| + | |||
| + | {| style="padding: 0;margin:0;margin-top:10px;text-align:left;" |- | ||
| + | | style="border-right: 1px dotted gray;padding-right:25px;" valign="top" | | ||
== Firmware Security Testing Methodology == | == Firmware Security Testing Methodology == | ||
| + | |||
The Firmware Security Testing Methodology (FSTM) is composed of nine stages tailored to enable security researchers, software developers, consultants, hobbyists, and Information Security professionals with conducting firmware security assessments. | The Firmware Security Testing Methodology (FSTM) is composed of nine stages tailored to enable security researchers, software developers, consultants, hobbyists, and Information Security professionals with conducting firmware security assessments. | ||
| Line 1,095: | Line 1,141: | ||
|- | |- | ||
|2. Obtaining firmware | |2. Obtaining firmware | ||
| − | |Attain | + | |Attain firmware using one or more of the proposed methods listed |
|- | |- | ||
|3. Analyzing firmware | |3. Analyzing firmware | ||
| Line 1,101: | Line 1,147: | ||
|- | |- | ||
|4. Extracting the filesystem | |4. Extracting the filesystem | ||
| − | |Carve | + | |Carve filesystem contents from the target firmware |
|- | |- | ||
|5. Analyzing filesystem contents | |5. Analyzing filesystem contents | ||
| Line 1,107: | Line 1,153: | ||
|- | |- | ||
|6. Emulating firmware | |6. Emulating firmware | ||
| − | |Emulate | + | |Emulate firmware files and components |
|- | |- | ||
|7. Dynamic analysis | |7. Dynamic analysis | ||
| Line 1,113: | Line 1,159: | ||
|- | |- | ||
|8. Runtime analysis | |8. Runtime analysis | ||
| − | |Analyze | + | |Analyze compiled binaries during device runtime |
|- | |- | ||
|9. Binary Exploitation | |9. Binary Exploitation | ||
|Exploit identified vulnerabilities discovered in previous stages to attain root and/or code execution | |Exploit identified vulnerabilities discovered in previous stages to attain root and/or code execution | ||
| − | |} | + | |}The full methodology release can be downloaded via the following TBD. |
| − | The full{{Social Media Links}} | + | |
| + | {{Social Media Links}} | ||
| style="padding-left:25px;width:300px;border-right: 1px dotted gray;padding-right:25px;" valign="top" | | | style="padding-left:25px;width:300px;border-right: 1px dotted gray;padding-right:25px;" valign="top" | | ||
| − | == What is the Firmware | + | == What is the Firmware Security Testing Methodology == |
| − | The Firmware | + | The Firmware Security Testing Methodology Project provides: |
| − | * | + | *Attack walkthroughs |
| − | * | + | *Tool usage examples |
| − | * | + | *Screenshots |
| − | * | + | *Companion virtual machine preloaded with tools (EmbedOS) - <nowiki>https://github.com/scriptingxss/EmbedOS</nowiki> |
| − | |||
| − | |||
| − | |||
== Project Leaders == | == Project Leaders == | ||
| − | * | + | * Aaron Guzman |
| − | |||
| − | |||
| − | + | == Quick Download == | |
| − | + | * TBD | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | == | ||
| − | * | ||
|} | |} | ||
Revision as of 14:49, 31 October 2019
- Main
- IoT Top 10
- OWASP IoT Top 10 2018 Mapping Project
- IoTGoat
- ByteSweep
- IoT Attack Surface Areas
- IoT Vulnerabilities
- Medical Devices
- Firmware Analysis
- Firmware Security Testing Methodology
- IoT Event Logging Project
- ICS/SCADA
- Community
- Project About
OWASP Internet of Things (IoT) ProjectOxford defines the Internet of Things as: “A proposed development of the Internet in which everyday objects have network connectivity, allowing them to send and receive data.” The OWASP Internet of Things Project is designed to help manufacturers, developers, and consumers better understand the security issues associated with the Internet of Things, and to enable users in any context to make better security decisions when building, deploying, or assessing IoT technologies. The project looks to define a structure for various IoT sub-projects such as Attack Surface Areas, Testing Guides, Tools, and Top Vulnerabilities. Updated!The OWASP IoT Project for 2018 has been released!PhilosophyThe OWASP Internet of Things Project was started in 2014 as a way help Developers, Manufacturers, Enterprises, and Consumers to make better decisions regarding the creation and use of IoT systems. This continues today with the 2018 release of the OWASP IoT Top 10, which represents the top ten things to avoid when building, deploying, or managing IoT systems. The primary theme for the 2018 OWASP Internet of Things Top 10 is simplicity. Rather than having separate lists for risks vs. threats vs. vulnerabilities—or for developers vs. enterprises vs. consumers—the project team elected to have a single, unified list that captures the top things to avoid when dealing with IoT Security. The team recognized that there are now dozens of organizations releasing elaborate guidance on IoT Security—all of which are designed for slightly different audiences and industry verticals. We thought the most useful resource we could create is a single list that addresses the highest priority issues for manufacturers, enterprises, and consumers at the same time. The result is the 2018 OWASP IoT Top 10. MethodologyThe project team is a collection of volunteer professionals from within the security industry, with experience spanning multiple areas of expertise, including: manufacturers, consulting, security testers, developers, and many more. The project was conducted in the following phases:
The Future of the OWASP IoT Top 10The team has a number of activities planned to continue improving on the project going forward. Some of the items being discussed include:
Participation in the OWASP IoT Project is open to the community. We take input from all participants — whether you’re a developer, a manufacturer, a penetration tester, or someone just trying to implement IoT securely. You can find the team meeting every other Friday in the the #iot-security room of the OWASP Slack Channel. The OWASP IoT Security Team, 2018 LicensingThe OWASP Internet of Things Project is free to use. It is licensed under the http://creativecommons.org/licenses/by-sa/3.0/ Creative Commons Attribution-ShareAlike 3.0 license], so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one.
|
What is the OWASP Internet of Things Project?The OWASP Internet of Things Project provides information on:
Project Leaders
Contributors
IoT Top 2018 Contributors
Related Projects |
CollaborationHint: If you're new to Slack, join OWASP's slack channel first, then join #iot-security within OWASP's channel. Quick DownloadIoT Attack Surface Mapping DEFCON 23 News and Events
Classifications
| |||||||
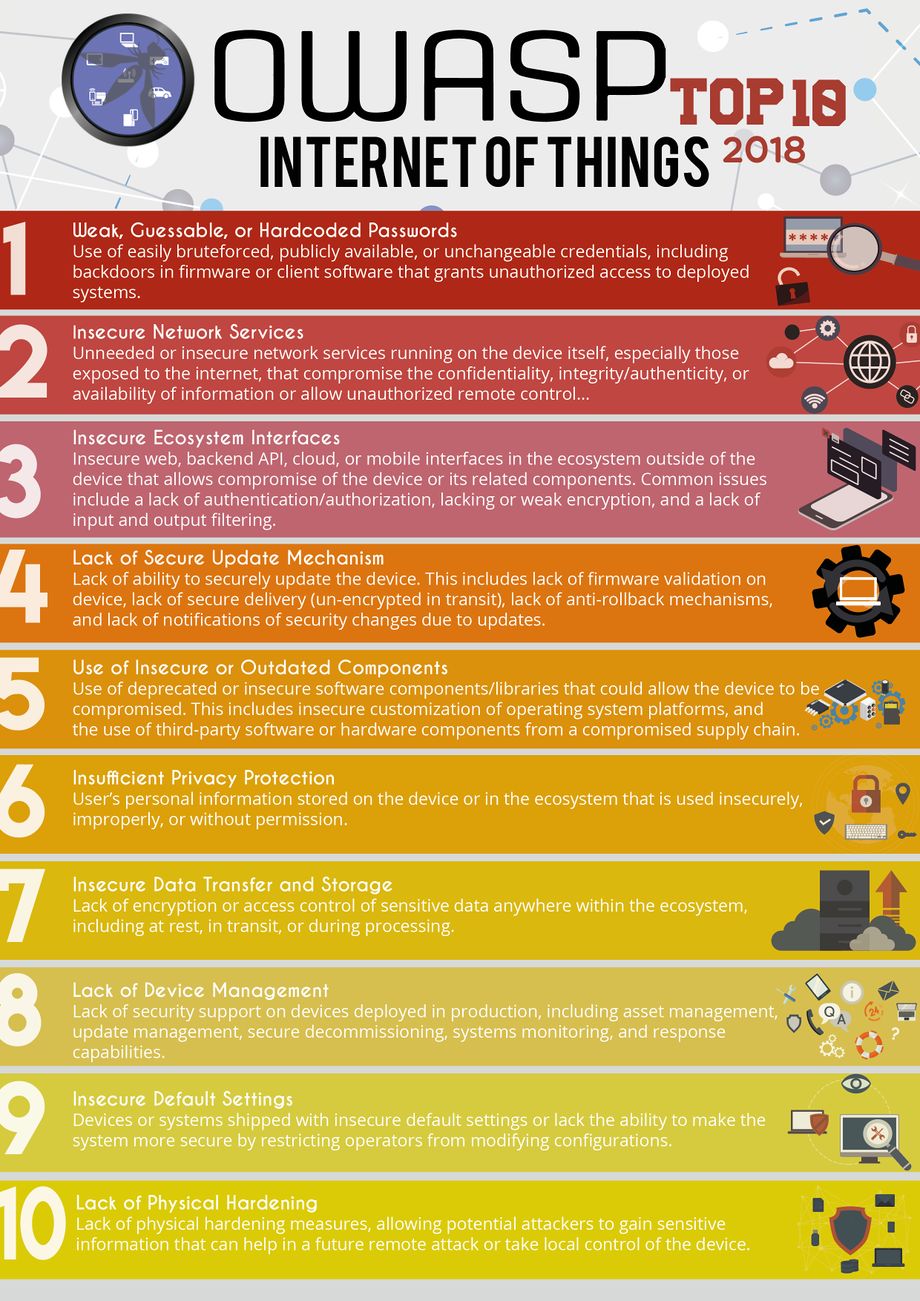
Internet of Things (IoT) Top 10 2018
The OWASP IoT Top 10 - 2018 is now available.
- I1 Weak Guessable, or Hardcoded Passwords
- I2 Insecure Network Services
- I3 Insecure Ecosystem Interfaces
- I4 Lack of Secure Update Mechanism
- I5 Use of Insecure or Outdated Components
- I6 Insufficient Privacy Protection
- I7 Insecure Data Transfer and Storage
- I8 Lack of Device Management
- I9 Insecure Default Settings
- I10 Lack of Physical Hardening
Internet of Things (IoT) Top 10 2014
- I1 Insecure Web Interface
- I2 Insufficient Authentication/Authorization
- I3 Insecure Network Services
- I4 Lack of Transport Encryption
- I5 Privacy Concerns
- I6 Insecure Cloud Interface
- I7 Insecure Mobile Interface
- I8 Insufficient Security Configurability
- I9 Insecure Software/Firmware
- I10 Poor Physical Security
IoT Top 10 2018 Mapping ProjectThe OWASP IoT Mapping Project is intended to provide a mapping of the OWASP IoT Top 10 2018 to industry publications and sister projects. The goal is to provide resources that enable practical uses for the OWASP IoT Top 10 . As with all Top 10 lists, they should be used as a first step and expanded upon according to the applicable IoT ecosystem. Mappings are structured with control categories, tests, or recommendations in the left column, descriptions in the middle column, and their mapping to the OWASP IoT Top 10 2018 list in the right column. Each mapping may not have a 1 to 1 relation; however, similar recommendations and/or controls are listed. For mappings that are not applicable to the IoT Top 10 2018 list, an "N/A" is provided as the mapping. An example mapping of the IoT Top 10 2014 is provided below. For additional mappings, please visit the following link: https://scriptingxss.gitbook.io/owasp-iot-top-10-mapping-project/ |
What is the IoT Top 10 Mapping Project?The OWASP IoT Mapping Project is intended to provide a mapping of the OWASP IoT Top 10 2018 to industry publications and sister projects. The goal is to provide resources that enable practical uses for the OWASP IoT Top 10 . As with all Top 10 lists, they should be used as a first step and expanded upon according to the applicable IoT ecosystem. Mappings include the following:
and more... GitBookMappings are hosted on GitBook using the following link https://scriptingxss.gitbook.io/owasp-iot-top-10-mapping-project/ Project Leaders
Collaboration |
IoTGoat ProjectIoT Goat is a deliberately insecure firmware based on OpenWrt. The project’s goal is to teach users about the most common vulnerabilities typically found in IoT devices. The vulnerabilities will be based on the top 10 vulnerabilities as documented by OWASP: https://www.owasp.org/index.php/OWASP_Internet_of_Things_Project. IoTGoat is expected to be released by December 2019. To get more information on getting started or how to contribute, visit the project's Github: https://github.com/scriptingxss/IoTGoat
|
What is the IoTGoat Project?The IoTGoat Project is a deliberately insecure firmware based on OpenWrt. The project’s goal is to teach users about the most common vulnerabilities typically found in IoT devices. The vulnerabilities will be based on the IoT Top 10. GitHubhttps://github.com/scriptingxss/IoTGoat Project Leaders
Related Projects
CollaborationQuick DownloadNews and Events
|

ByteSweep ProjectByteSweep is a Free Software IoT security analysis platform. This platform will allow IoT device makers, large and small, to conduct fully automated security checks before they ship firmware. A Free Software IoT Firmware Security Analysis Platform ByteSweep Features:
|
What is the ByteSweep Project?A Free Software IoT Firmware Security Analysis Platform. GitLabhttps://gitlab.com/bytesweep/bytesweep Project Leaders
CollaborationQuick Download |
IoT Attack Surface Areas ProjectThe OWASP IoT Attack Surface Areas (DRAFT) are as follows:
|
What is the IoT Attack Surface Areas Project?The IoT Attack Surface Areas Project provides a list of attack surfaces that should be understood by manufacturers, developers, security researchers, and those looking to deploy or implement IoT technologies within their organizations. Project Leaders
Related ProjectsCollaborationQuick Download
News and Events
|
IoT Vulnerabilities Project
|
What is the IoT Vulnerabilities Project?The IoT Vulnerabilities Project provides:
Project Leaders
Related ProjectsCollaborationResourcesNews and Events
|
Medical Device TestingThe Medical Device Testing project is intended to provide some basic attack surface considerations that should be evaluated before shipping Medical Device equipment.
|
What is the Medical Attack Surfaces project?The Medical Attack Surfaces project provides:
Project Leaders
Related ProjectsCollaborationResources
News and Events
|
Firmware Analysis ProjectThe Firmware Analysis Project is intended to provide security testing guidance for the IoT Attack Surface "Device Firmware":
|
What is the Firmware Analysis Project?The Firmware Analysis Project provides:
Project Leaders
Related ProjectsCollaborationResources
News and Events
|

Firmware Security Testing MethodologyThe Firmware Security Testing Methodology (FSTM) is composed of nine stages tailored to enable security researchers, software developers, consultants, hobbyists, and Information Security professionals with conducting firmware security assessments.
|
What is the Firmware Security Testing MethodologyThe Firmware Security Testing Methodology Project provides:
Project Leaders
Quick Download
|
IoT Logging EventsThis is a working draft of the recommended minimum IoT Device logging events. This includes many different types of devices, including consumer IoT, enterprise IoT, and ICS/SCADA type devices.
|
What is the IoT Security Logging Project?The IoT Secure Logging Project provides a list of core events that should be logged in any IoT-related system. The project exists because IoT systems in general are not logging nearly enough events to constitute input for a solid detection and response program around IoT devices, and for companies that want to do this there are not many good resources for what should be logged. Project Leaders
Related ProjectsCollaborationQuick Download
News and Events
|
ICS/SCADA ProjectThe OWASP ICS/SCADA Top 10 software weaknesses are as follows:
|
What is the ICS/SCADA Project?The ICS/SCADA Project provides:
Project Leaders
Related ProjectsCollaborationQuick Download
News and Events
|
A global grassroots organization that is focused on issues where computer security intersects public safety and human life.
Their areas of focus include:
- Medical devices
- Automobiles
- Home Electronics
- Public Infrastructure
Formed as an informal industry working group in 2005, today OTA is an Internal Revenue Service (IRS) approved 501c3 charitable organization with the mission to enhance online trust and empower users, while promoting innovation and the vitality of the internet. OTA is global organization supported by over 100 organizations headquartered in Bellevue, Washington with offices in Washington DC.
Addressing the mounting concerns, in January 2015 the Online Trust Alliance, established the IoT Trustworthy Working Group (ITWG), a multi-stakeholder initiative. The group recognizes “security and privacy by design” must be a priority from the onset of product development and be addressed holistically. The framework focuses on privacy, security sustainability. The sustainability pillar is critical as it looks at the life-cycle issues related to long- term supportability and transfers of ownership of devices and the data collected.
The AllSeen Alliance is a Linux Foundation collaborative project. They're a cross-industry consortium dedicated to enabling the interoperability of billions of devices, services and apps that comprise the Internet of Things. The Alliance supports the AllJoyn Framework, an open source software framework that makes it easy for devices and apps to discover and communicate with each other. Developers can write applications for interoperability regardless of transport layer, manufacturer, and without the need for Internet access. The software has been and will continue to be openly available for developers to download, and runs on popular platforms such as Linux and Linux-based Android, iOS, and Windows, including many other lightweight real-time operating systems.
The Industrial Internet Consortium (IIC)
The Industrial Internet Consortium is the open membership, international not-for-profit consortium that is setting the architectural framework and direction for the Industrial Internet. Founded by AT&T, Cisco, GE, IBM and Intel in March 2014, the consortium’s mission is to coordinate vast ecosystem initiatives to connect and integrate objects with people, processes and data using common architectures, interoperability and open standards.
Securing Smart Cities is a not-for-profit global initiative that aims to solve the existing and future cybersecurity problems of smart cities through collaboration between companies, governments, media outlets, other not-for-profit initiatives and individuals across the world.
Talks
RSA Conference San Francisco
Securing the Internet of Things: Mapping IoT Attack Surface Areas with the OWASP IoT Top 10 Project
Daniel Miessler, Practice Principal
April 21, 2015
---
Defcon 23
IoT Attack Surface Mapping
Daniel Miessler
August 6-9, 2015
Podcasts
IoT Conferences
Conference Call for Papers
| PROJECT INFO What does this OWASP project offer you? |
RELEASE(S) INFO What releases are available for this project? | |||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
| |||||||||||||||||||||||||||||||||||||