This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Abuse Case Cheat Sheet"
(Creation of the Abuse Case CS) |
(Minor changes from the start up to the "Proposition" section. Added QA/Functional tester to team.) |
||
| Line 18: | Line 18: | ||
These security requirements are too generic and useless for a development team... | These security requirements are too generic and useless for a development team... | ||
| − | To build a secure application, from an pragmatic point of view, it is important to identify the attacks | + | To build a secure application, from an pragmatic point of view, it is important to identify the attacks which the application must defend against according to its business and technical context. |
= Objective = | = Objective = | ||
| − | The objective of this cheat sheet is to provide a explanation about what | + | The objective of this cheat sheet is to provide a explanation about what an '''Abuse Case''' is, why abuse cases are important when considering the security of an application and, finally, to provide a proposal for a pragmatic approach to built a list of abuse cases and track them for every feature planned to be implemented as part of an application whatever project mode used (waterfall or agile). |
'''Important note about this Cheat Sheet:''' | '''Important note about this Cheat Sheet:''' | ||
<pre> | <pre> | ||
| − | The main objective is to provide a pragmatic approach in order to allow a company or a project team to start building and handling the list of abuse cases and then customize the elements proposed to | + | The main objective is to provide a pragmatic approach in order to allow a company or a project team to start building and handling the list of abuse cases and then customize the elements proposed to its context/culture in order to, finally, build its own method. |
This cheat sheet can be seen like a getting started tutorial.</pre> | This cheat sheet can be seen like a getting started tutorial.</pre> | ||
| Line 32: | Line 32: | ||
= Context & approach = | = Context & approach = | ||
| − | == Why identify | + | == Why clearly identify the attacks? == |
| − | + | Clearly identifying the attacks against which the application must defend is essential in order to enable the following steps in a project or sprint: | |
* Evaluate the business risk for each of the identified attacks in order perform a selection according to the business risk and the project/sprint budget. | * Evaluate the business risk for each of the identified attacks in order perform a selection according to the business risk and the project/sprint budget. | ||
| − | * | + | * Derive security requirements and add them into the project specification or sprint's user stories acceptance criteria. |
| − | * Estimate the overhead to provision in the | + | * Estimate the overhead to provision in the initial project/sprint charge that will be necessary to implement the countermeasures. |
| − | * About | + | * About countermeasures: Allow the project team to define them and in which location they are appropriate (network, infrastructure, code...) to be positioned. |
| + | |||
== Notion of Abuse Case == | == Notion of Abuse Case == | ||
| − | In order to help | + | In order to help build the list of attacks, the notion of '''Abuse Case''' exists. |
An '''Abuse Case''' can be defined as: | An '''Abuse Case''' can be defined as: | ||
| − | <pre>A way to use a feature | + | <pre>A way to use a feature that was not expected by the implementer, allowing an attacker to influence the feature or outcome of use of the feature based on the attacker action (or input).</pre> |
Synopsys define an '''Abuse Case'' like this: | Synopsys define an '''Abuse Case'' like this: | ||
| Line 60: | Line 61: | ||
== How to define the list of Abuse Cases? == | == How to define the list of Abuse Cases? == | ||
| − | + | There are many different ways to define the list of abuse cases for a feature (that can be mapped to a user story in agile mode). | |
| − | The project [[OWASP_SAMM_Project|OWASP Open SAMM]] | + | The project [[OWASP_SAMM_Project|OWASP Open SAMM]] proposes the following approach in the ''Activity A'' of the Security Practice ''Threat Assessment'' for the Maturity level 2: |
<pre> | <pre> | ||
| Line 76: | Line 77: | ||
Open SAMM source: [[SAMM_-_Threat_Assessment_-_2|Threat Assessment Level 2 Actvity A]] | Open SAMM source: [[SAMM_-_Threat_Assessment_-_2|Threat Assessment Level 2 Actvity A]] | ||
| − | |||
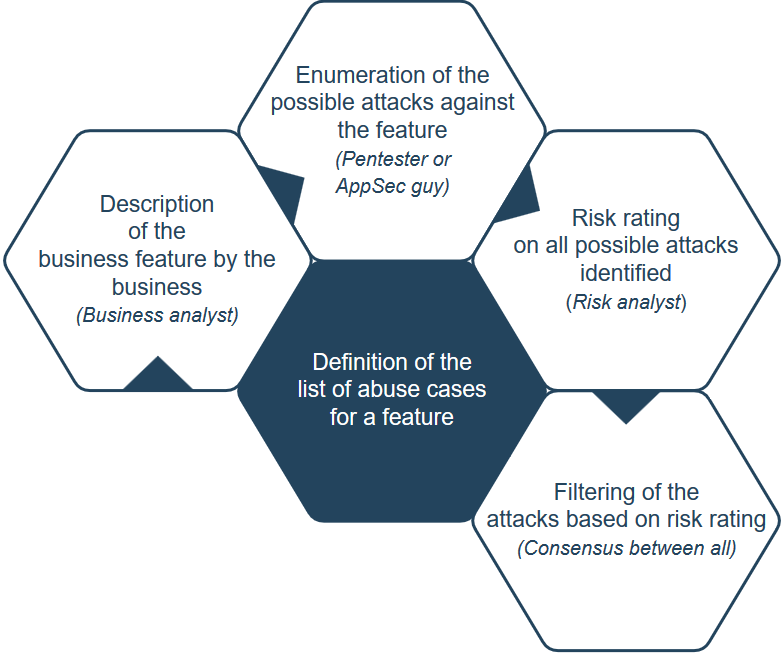
Another way to achieve the building of the list can be the following (more ground and collaborative oriented): | Another way to achieve the building of the list can be the following (more ground and collaborative oriented): | ||
| − | + | Make a workshop that includes people with the following profiles: | |
* '''Business analyst''': Will be the business key people that will describe each feature from a business point of view. | * '''Business analyst''': Will be the business key people that will describe each feature from a business point of view. | ||
| − | * '''Risk analyst''': Will be the company risk | + | * '''Risk analyst''': Will be the company's risk personnel that will evaluate the business risk from a proposed attack (sometimes it is the '''Business analyst''' depending on the company). |
| − | * '''Offsensive guy (Pentester or Application Security guy with offensive mindset)''': Will be the ''attacker'' that will propose all attacks that he can perform on the business feature that | + | * '''Offsensive guy (Pentester or Application Security guy with offensive mindset)''': Will be the ''attacker'' that will propose all attacks that he can perform on the business feature that will be presented to him. If the company does not have this profile then it is possible to ask an intervention of an external specialist (Pentester or AppSec consultant from a security firm). If possible, include 2 offensives guys (ex: 1 Pentester + 1 AppSec) in order to increase the number of possible attacks that will be identified and considered. |
| − | * '''Technical leaders of the projects''': Will be the project technical | + | * '''Technical leaders of the projects''': Will be the project technical people and will allow technical exchange about attacks and countermeasures identified during the workshop. |
| + | * '''Quality assurance analyst or functional tester''': Personnel that may have a good sense of how the application/functionality is intended to work (positive testing) and what things cause it to fail (failure cases). | ||
| − | During this workshop (duration depend on the size of the list | + | During this workshop (duration will depend on the size of the feature list, but 4 hours is a good start) all business features that will be part of the project or the sprint will be processed. The output of the workshop will be a list of attacks (abuse cases) for all business features. All abuse cases will have a risk rating that will allow for filtering and prioritization. |
It is important to take in account '''Technical''' and '''Business''' kind of abuse cases and mark them accordingly. | It is important to take in account '''Technical''' and '''Business''' kind of abuse cases and mark them accordingly. | ||
| Line 103: | Line 104: | ||
| − | Whatever the mode of project used (agile or waterfall), the | + | Whatever the mode of project used (agile or waterfall), the abuse cases selected to be addressed must become security requirements in each feature specification section (waterfall) or User Story acceptance criteria (agile) in order to allow additional cost/effort evaluation, identification and implementation of the countermeasures. |
| − | Each abuse case must have a unique identifier in order to allow tracking of | + | Each abuse case must have a unique identifier in order to allow tracking of its handling in the whole project/sprint, details about this point will be given in the proposal section. |
An example of unique ID can be '''ABUSE_CASE_001'''. | An example of unique ID can be '''ABUSE_CASE_001'''. | ||
| − | The following schema provide an overview of the chaining of the | + | The following schema provide an overview of the chaining of the different steps involved (from left to right): |
[[File:ABUSE_CASE_CS_CHAINING_SCHEMA.png|center]] | [[File:ABUSE_CASE_CS_CHAINING_SCHEMA.png|center]] | ||
Revision as of 18:14, 25 September 2018
|
Last revision (mm/dd/yy): 09/25/2018 IntroductionOften when the security level of an application is mentioned in requirements, the following expressions are meet:
These security requirements are too generic and useless for a development team... To build a secure application, from an pragmatic point of view, it is important to identify the attacks which the application must defend against according to its business and technical context. ObjectiveThe objective of this cheat sheet is to provide a explanation about what an Abuse Case is, why abuse cases are important when considering the security of an application and, finally, to provide a proposal for a pragmatic approach to built a list of abuse cases and track them for every feature planned to be implemented as part of an application whatever project mode used (waterfall or agile). Important note about this Cheat Sheet: The main objective is to provide a pragmatic approach in order to allow a company or a project team to start building and handling the list of abuse cases and then customize the elements proposed to its context/culture in order to, finally, build its own method. This cheat sheet can be seen like a getting started tutorial. Context & approachWhy clearly identify the attacks?Clearly identifying the attacks against which the application must defend is essential in order to enable the following steps in a project or sprint:
Notion of Abuse CaseIn order to help build the list of attacks, the notion of Abuse Case exists. An Abuse Case can be defined as: A way to use a feature that was not expected by the implementer, allowing an attacker to influence the feature or outcome of use of the feature based on the attacker action (or input). Synopsys define an 'Abuse Case like this: Misuse and abuse cases describe how users misuse or exploit the weaknesses of controls in software features to attack an application. This can lead to tangible business impact when a direct attack against business functionalities, which may bring in revenue or provide positive user experience, are attacked. Abuse cases can also be an effective way to drive security requirements that lead to proper protection of these critical business use cases. Synopsys source: https://www.synopsys.com/blogs/software-security/abuse-cases-can-drive-security-requirements/ Another definition of Abuse Case by Cigital: https://cigital.com/papers/download/misuse-bp.pdf How to define the list of Abuse Cases?There are many different ways to define the list of abuse cases for a feature (that can be mapped to a user story in agile mode).
Further considering the threats to the organization, conduct a more formal analysis to determine potential misuse or abuse of functionality. Typically, this process begins with identification of normal usage scenarios, e.g. use-case diagrams if available. If a formal abuse-case technique isn’t used, generate a set of abuse-cases for each scenario by starting with a statement of normal usage and brainstorming ways in which the statement might be negated, in whole or in part. The simplest way to get started is to insert the word “no” or “not” into the usage statement in as many ways as possible, typically around nouns and verbs. Each usage scenario should generate several possible abuse-case statements. Further elaborate the abuse-case statements to include any application-specific concerns based on the business function of the software. The ultimate goal is for the completed set of abuse statements to form a model for usage patterns that should be disallowed by the software. If desired, these abuse cases can be combined with existing threat models. After initial creation, abuse-case models should be updated for active projects during the design phase. For existing projects, new requirements should be analyzed for potential abuse, and existing projects should opportunistically build abuse-cases for established functionality where practical. Open SAMM source: Threat Assessment Level 2 Actvity A Another way to achieve the building of the list can be the following (more ground and collaborative oriented): Make a workshop that includes people with the following profiles:
It is important to take in account Technical and Business kind of abuse cases and mark them accordingly. Example:
When to define the list of Abuse Cases?On agile project, the definition workshop must be made after the meeting in which User Stories are associated to a Sprint. On waterfall project, the definition workshop must be made when business feature to implements are identified and known by the business.
An example of unique ID can be ABUSE_CASE_001.
PropositionThe proposal will use the workshop explained in previous section and will focus on the output of the workshop. Step 1: Preparation of the workshopFirst, even if it is obvious, the business key people must be sure to know, understand and be able to explain the business features that will be processed during the workshop. Secondly, create a new Microsoft Excel file (you can also use Google Sheet or any other similar software) with the following sheets:
FEATURES sheet:
Step 2: During the workshopUse the Excel file to review all the features. For each feature, follow this flow:
With the time and accross projects, you will obtains your own dictionary of attacks and countermeasures that are applicable to the kind of application of your business domain. This dictionary will speed up the further workshops in a significant way. To promote the creation of this dictionary, you can, at the end of the project/sprint, gather the list of attacks and countermeasures identified in a central location (wiki, database, file...) that will be used during the next workshop in combination with the input of the offensive guys. Step 3: After the workshopThe Excel file contain, at this stage, the list of all abuse cases that must be handled and, potentially how, depending on the capacity to found countermeasures. Now, there 2 remaining task:
Step 4: During implementation - Abuse cases handling trackingIn order to track the handling of all the abuse cases keep in the selection, the following approach can be used: If one or several abuse cases are handled at:
Using this way, it become possible (via some minor scripting) to identify where the the abuse cases are addressed. Step 5: During implementation - Abuse cases handling validationAs abuse cases are defined, it is possible to put in place automated or manual validations to ensure that:
Add automated tests allow also to track that countermeasures against the abuse cases are still effective/in place during maintenance or bug fixing phase of a project (prevent accidental removal/disabling). It is also usefull when Continuous Delivery approach is used (https://continuousdelivery.com/) in to ensure that all abuse cases protections are in place before to open expected access to the application. Sources of the schemasAll schemas has been created using https://www.draw.io/ site and exported, as PNG image, for being integrated into this article. All XML descriptors files for each schema are available below (using XML description, modification of the schema is possible using DRAW.IO site): Authors and Primary EditorsDominique Righetto - [email protected] Other Cheatsheets |