This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Attack Surface Detector Project"
(resources12) |
(→ASD Plugin for OWASP ZAP:) (Tag: Visual edit) |
||
| Line 3: | Line 3: | ||
{| style="padding: 0;margin:0;margin-top:10px;text-align:left;" |- | {| style="padding: 0;margin:0;margin-top:10px;text-align:left;" |- | ||
| style="border-right: 1px dotted gray;padding-right:25px;" valign="top" | | | style="border-right: 1px dotted gray;padding-right:25px;" valign="top" | | ||
| − | <span style="color:#ff0000"> | + | <span style="color:#ff0000"></span> |
| − | </span> | ||
==Introduction== | ==Introduction== | ||
<span style="color:#000000"> | <span style="color:#000000"> | ||
| Line 14: | Line 13: | ||
<span style="color:#000000"> | <span style="color:#000000"> | ||
This tool is the Attack Surface Detector, a plugin for OWASP ZAP and PortSwigger Burp Suite. This tool figures out the endpoints of a web application, the parameters these endpoints accept, and the data type of those parameters. This includes the unlinked endpoints a spider won't find in client-side code, or optional parameters totally unused in client-side code. The plugin then imports this data into ZAP or Burp so you view the results, or work with the detected endpoints and parameters from the target site map.<br> | This tool is the Attack Surface Detector, a plugin for OWASP ZAP and PortSwigger Burp Suite. This tool figures out the endpoints of a web application, the parameters these endpoints accept, and the data type of those parameters. This includes the unlinked endpoints a spider won't find in client-side code, or optional parameters totally unused in client-side code. The plugin then imports this data into ZAP or Burp so you view the results, or work with the detected endpoints and parameters from the target site map.<br> | ||
| − | </span> | + | </span>[[File:ASD-Endpoint-Screens.png|center|thumb|628x628px]] |
| − | |||
| − | [[File:ASD- | ||
==== Attack Surface Detector Command Line Interface==== | ==== Attack Surface Detector Command Line Interface==== | ||
| Line 49: | Line 46: | ||
| style="padding-left:25px;width:200px;border-right: 1px dotted gray;padding-right:25px;" valign="top" | | | style="padding-left:25px;width:200px;border-right: 1px dotted gray;padding-right:25px;" valign="top" | | ||
| − | |||
== Project Resources == | == Project Resources == | ||
| − | <span style="color:#ff0000"> | + | <span style="color:#ff0000"></span> |
| − | </span> | ||
====ASD Plugin for OWASP ZAP:==== | ====ASD Plugin for OWASP ZAP:==== | ||
[https://github.com/secdec/attack-surface-detector-zap/ ASD ZAP Home Page] | [https://github.com/secdec/attack-surface-detector-zap/ ASD ZAP Home Page] | ||
| Line 109: | Line 104: | ||
* [https://github.com/secdec/attack-surface-detector-zap/issues Create an issue] | * [https://github.com/secdec/attack-surface-detector-zap/issues Create an issue] | ||
* [https://lists.owasp.org/mailman/listinfo/owasp_attack_surface_detector_project OWASP project email List] | * [https://lists.owasp.org/mailman/listinfo/owasp_attack_surface_detector_project OWASP project email List] | ||
| − | |||
| − | |||
== Related Projects == | == Related Projects == | ||
| − | <span style="color:#000000"> | + | <span style="color:#000000"></span> |
| − | </span> | ||
* [[OWASP Zed Attack Proxy Project]] | * [[OWASP Zed Attack Proxy Project]] | ||
* [[OWASP Code Pulse Project]] | * [[OWASP Code Pulse Project]] | ||
| Line 122: | Line 114: | ||
{| width="200" cellpadding="2" | {| width="200" cellpadding="2" | ||
|- | |- | ||
| − | | rowspan="2" | + | | rowspan="2" width="50%" valign="top" align="center" | [[File:New projects.png|100px|link=https://www.owasp.org/index.php/OWASP_Project_Stages#tab=Incubator_Projects]] |
| − | | | + | | width="50%" valign="top" align="center" | [[File:Owasp-breakers-small.png|link=]] |
|- | |- | ||
| − | | | + | | width="50%" valign="top" align="center" | [[File:Owasp-defenders-small.png|link=]] |
|- | |- | ||
| colspan="2" align="center" | [[File:Project_Type_Files_TOOL.jpg|link=]] | | colspan="2" align="center" | [[File:Project_Type_Files_TOOL.jpg|link=]] | ||
| Line 131: | Line 123: | ||
|} | |} | ||
| − | |||
__NOTOC__ <headertabs /> | __NOTOC__ <headertabs /> | ||
Revision as of 16:13, 16 August 2018
|
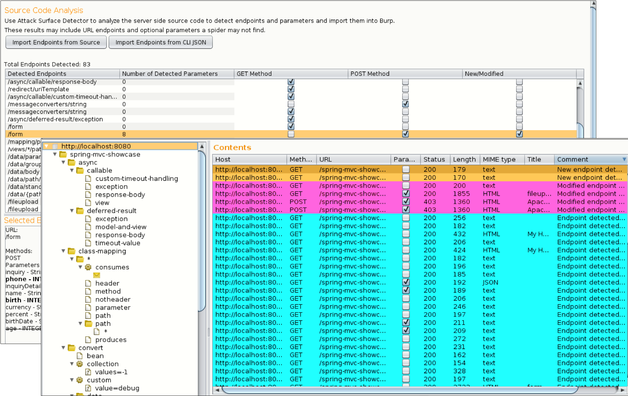
IntroductionDuring web application penetration testing, it is important to enumerate your application's attack surface. While Dynamic Application Security Testing (DAST) tools (such as Burp Suite and ZAP) are good at spidering to identify application attack surfaces, they will often fail to identify unlinked endpoints and optional parameters. These endpoints and parameters not found often go untested, which can leave your application open to an attacker. What is the Attack Surface Detector?Attack Surface Detector ZAP and Burp Plugins
This tool is the Attack Surface Detector, a plugin for OWASP ZAP and PortSwigger Burp Suite. This tool figures out the endpoints of a web application, the parameters these endpoints accept, and the data type of those parameters. This includes the unlinked endpoints a spider won't find in client-side code, or optional parameters totally unused in client-side code. The plugin then imports this data into ZAP or Burp so you view the results, or work with the detected endpoints and parameters from the target site map. Attack Surface Detector Command Line Interface The attack-surface-detector-cli program is a command-line tool that takes in a folder location and outputs the set of endpoints detected within that codebase. It uses the ASTAM Correlator's threadfix-ham module to generate these endpoints. The endpoints are output to the console by default, and can save a JSON version of those endpoints through the -output-file and -json flags. How it WorksThe Attack Surface Detector uses static code analyses to identify web app endpoints by parsing routes and identifying parameters (with supported languages and frameworks). Supported Frameworks
LicensingThe Attack Surface Detector plugin is free to use. It is licensed under the link Mozilla Public License 2.0. Getting InvolvedContributions to the Attack Surface Detector project are encouraged and welcome. Additions of new features and enhancements can be provided through GitHub. We encourage users to assess the technology through individual evaluations, pilots and/or case studies. |
Project Resources
ASD Plugin for OWASP ZAP:Install Attack Surface Detector ASD Plugin for PortSwigger Burp:Install Attack Surface Detector ASD command-line tool:Project LeaderKen Prole Email: [email protected] Related Projects
Classifications
| |||||