This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "LatamTour2017"
m (→03 de Abril) |
m (small update to the Costa Rica agenda) |
||
| Line 550: | Line 550: | ||
This talk will assume that a basic understanding of data flow diagramming, pen testing, security architecture, and threat analytics is understood by the audience. This talk also centers around the idea of modeling threats for applications based upon a higher propensity of threat intelligence, how to harvest and correlate threat patterns to your threat model and also how to correlate a threat model to defining preemptive controls and countermeasures to include in the overall design. | This talk will assume that a basic understanding of data flow diagramming, pen testing, security architecture, and threat analytics is understood by the audience. This talk also centers around the idea of modeling threats for applications based upon a higher propensity of threat intelligence, how to harvest and correlate threat patterns to your threat model and also how to correlate a threat model to defining preemptive controls and countermeasures to include in the overall design. | ||
| − | This talk will focus on walking attendees through the PASTA threat modeling methodology over 3 different deployment models for technology: IoT, E-Commerce, and Mobile. The talk will place specific emphasis on phases II (Technology Enumeration), phase III (Application Decomposition), and phase IV (threat analysis). Although all 7 phases of the PASTA threat modeling methodology will be exemplified, discussions around what tools and techniques around phases II, III, and IV will be discussed in detail since many industry professionals find it challenging to know the various application components that make up the various tiers of an application model. I will be exemplifying some tools to enumerate technical components across various application levels (ex: fingerprinting service PIDs on different apps or systems across IoT, Mobile, eCommerce) as each of these types of system environments are different. Another emphasis on the talk will be around defining trust boundaries while data flow diagramming and identifying what possible countermeasures to introduce from an architectural level. We'll review security architectural best practices from SABSA and TOGAF and how it can fortify secure design patterns. Stage/ Phase IV (Threat Analysis) will also be a key focus as we speak on practical ways in which threat data can be harvested as well as collected from external threat sources. We'll be integrating STIX and TAXII considerations on how to have infrastructure that can feed relevant data points to your threat model. The actual threat modeling methodology can be found here: www.versprite.com/PASTA-abstract.pdf | + | This talk will focus on walking attendees through the PASTA threat modeling methodology over 3 different deployment models for technology: IoT, E-Commerce, and Mobile. The talk will place specific emphasis on phases II (Technology Enumeration), phase III (Application Decomposition), and phase IV (threat analysis). Although all 7 phases of the PASTA threat modeling methodology will be exemplified, discussions around what tools and techniques around phases II, III, and IV will be discussed in detail since many industry professionals find it challenging to know the various application components that make up the various tiers of an application model. I will be exemplifying some tools to enumerate technical components across various application levels (ex: fingerprinting service PIDs on different apps or systems across IoT, Mobile, eCommerce) as each of these types of system environments are different. Another emphasis on the talk will be around defining trust boundaries while data flow diagramming and identifying what possible countermeasures to introduce from an architectural level. We'll review security architectural best practices from SABSA and TOGAF and how it can fortify secure design patterns. Stage/ Phase IV (Threat Analysis) will also be a key focus as we speak on practical ways in which threat data can be harvested as well as collected from external threat sources. We'll be integrating STIX and TAXII considerations on how to have infrastructure that can feed relevant data points to your threat model. The actual threat modeling methodology can be found here: https://www.versprite.com/PASTA-abstract.pdf |
| Salón #1 | | Salón #1 | ||
|- | |- | ||
| Line 562: | Line 562: | ||
|- | |- | ||
| 9:20 - 10:15 | | 9:20 - 10:15 | ||
| − | | | + | | DevOps: Primeros Pasos |
| Martin Flores González Costa Rica | | Martin Flores González Costa Rica | ||
| Bugs are the main source of vulnerabilities in software; being able to quickly and seamlessly deploy fixes all the way to production should be one of the main goals of any development team; practices allowing towards that goal; by means of removing silos and barriers, need to be embraced by organizations of all sizes. DevOps movement has gain momentum, learning about its spirit, main practices and the overall journey; could enable software development organizations to find what is needed so they could start their journey too. Join us for this presentation were we will cover some of the history of DevOps, its practices and process and finally a short demo of an application embracing these practices. | | Bugs are the main source of vulnerabilities in software; being able to quickly and seamlessly deploy fixes all the way to production should be one of the main goals of any development team; practices allowing towards that goal; by means of removing silos and barriers, need to be embraced by organizations of all sizes. DevOps movement has gain momentum, learning about its spirit, main practices and the overall journey; could enable software development organizations to find what is needed so they could start their journey too. Join us for this presentation were we will cover some of the history of DevOps, its practices and process and finally a short demo of an application embracing these practices. | ||
Revision as of 02:25, 4 April 2017
- WELCOME
- CALL FOR PAPERS & TRAININGS
- BOLIVIA
- CORDOBA
- URUGUAY
- BUENOS AIRES
- COSTA RICA
- PATAGONIA
- ECUADOR
- RIVIERA MAYA
- MANIZALES
- PERU
- BOGOTÁ
- EL SALVADOR
- CHILE
- SÃO PAULO
- VENEZUELA
- REPUBLICA DOMINICANA
- SPONSORS
- TEAM
Agenda
- April, 3: Manizales, Colombia
- April, 3: Bogotá, Colombia - REGISTRATE AQUÍ
- April, 5-6: Montevideo, Uruguay - REGISTRATE AQUÍ
- April, 6-7: República Dominicana - REGÍSTRATE AQUÍ
- April, 8: Quito, Ecuador -REGISTRARSE AQUI
- April, 19: Córdoba, Argentina
- April, 21: Patagonia, Argentina - REGISTRARSE AQUI
- April, 21: San José, Costa Rica
- April, 21: Lima, Perú
- April, 21-22: Santa Cruz, Bolivia -REGISTRARSE AQUI
- April, 22: Cancun, Mexico
- April, 22: São Paulo, Brazil
- April, 25: San Salvador, El Salvador - Registrarse aquí
- April, 26-27: Santiago de Chile
- April, 27: Caracas, Venezuela -REGISTRARSE AQUI
- April, 28: Buenos Aires, Argentina - REGISTRARSE AQUI
Latam Tour Objective
The OWASP Latam Tour objective is to raise awareness about application security in the Latin America region, so that people and organizations can make informed decisions about true application security risks. Everyone is free to participate in OWASP and all of our materials are available under a free and open software license.
We are proposing a chapters conference driven model in which the sessions are free for everybody and the costs are supported by a mix of funding i.e. OWASP Foundation, local chapter budget, external sponsorship, etc. 1-day training sessions are also offered in some tour stops. These sessions’ fees are $ 200USD for OWASP members and $ 250 USD for non-members (group discounts may apply).
Who Should Attend the Latam Tour?
- Application Developers
- Application Testers and Quality Assurance
- Application Project Management and Staff
- Chief Information Officers, Chief Information Security Officers, Chief Technology Officers, Deputies, Associates and Staff
- Chief Financial Officers, Auditors, and Staff Responsible for IT Security Oversight and Compliance
- Security Managers and Staff
- Executives, Managers, and Staff Responsible for IT Security Governance
- IT Professionals Interesting in Improving IT Security
- Anyone interested in learning about or promoting Web Application Security
Special offer - Become an OWASP Member
As part of the OWASP Latam Tour, you could become an OWASP Member by paying 20 U$D. Show your support and become an OWASP member today!
QUESTIONS
- If you have any questions about the Latam Tour, please send an email to [email protected]
#Latamtour hashtag for your tweets for Latam Tour (What are hashtags?)
@AppSecLatam Twitter Feed (follow us on Twitter!) <twitter>34534108</twitter>
Do you want to give a talk or a training session in Latin America?
Please send your proposals to the corresponding chapter leader before March 1st 2017:
- Argentina (Buenos Aires): Submit your talk here
- Argentina (Patagonia): Submit your talk here or send it to Gaston Toth [[email protected]]
- Argentina (Córdoba): send it to Eduardo Casanovas [[email protected]]
- Mexico (Riviera Maya): Submit your talk here or send it to Paulino Calderon [[email protected]]
- Bolivia: Elvin Mollinedo [[email protected]]
- Chile: Carlos Allendes [[email protected]]
- Colombia (Bogotá): Submit your talk here or send it to Giovanni Cruz Forero [[email protected]]
- Costa Rica: Michael Hidalgo [[email protected]]
- Ecuador (Quito): Submit your talk here or send it to Fernando Vela [[email protected]]
- Guatemala: Pablo Barrera [[email protected]]
- Peru (Lima) : John Vargas [[email protected]]
- Honduras : Gustavo Solano [[email protected]]
- Rep.Dominicana : Jonathan Correa [[email protected]]
- São Paulo: Magno Logan Submit your talk here
- Uruguay (Montevideo): Submit your talk here
- Venezuela (Caracas): Edgar Salazar [[email protected]]
By your submission you agree to the Speaker Agreement, Invited Speaker Agreement or Instructor Agreement.
BOLIVIA: 21-22 de Abril de 2017 (Conferencia de Seguridad Gratuita)
El evento más importante de la región llega nuevamente a Bolivia, OWASP Latam tour 2017!.
Expositores internacionales estarán presentando conferencias sobre los temas más importantes en Seguridad en Aplicaciones.
REGISTRO
La entrada a las conferencias es gratuita. Los asistentes únicamente deberán registrarse en la lista de asistencia.
Registro a OWASP LATAM Tour 2017 Bolivia
UBICACION

Dirección: Av. Beni y 3er. Anillo Externo Santa Cruz, Bolivia.
AGENDA
21 de abril
| Hora | Expositor | Conferencia | País |
|---|---|---|---|
| 08:00 - 08:30 | Registro - Acreditación | ||
| 08:30 - 09:00 | Proyecto OWASP | ||
| 09:00 - 09:45 | Saul Mamani M. | Seguridad Perimetral de Aplicaciones, una buena alternativa | Oruro, Bolivia |
| 09:45 - 10:30 | Marcelo Evangelista | Red Team: Why you need the Red? | Brasil |
| 10:30 - 11:00 | Pausa para café | ||
| 11:00 - 11:45 | Camilo Quenta | Ransomware en las alturas - enjaulando a linux | La Paz, Bolivia |
| 11:45 - 12:30 | Carlos Vidaurre | "BLUE" attacks | Santa Cruz, Bolivia |
| 12:30 - 14:00 | Horario de Almuerzo | ||
| 14:00 - 14:45 | Jaime Ivan Mendoza | IoT internet | Santa Cruz, Bolivia |
| 14:45 - 15:30 | Herman Brule | DDOS y bot a larga escala | Francia |
| 15:30 - 16:00 | Pausa para café | ||
| 16:00 - 16:45 | Juan Alberto Fajardo Canaza | Paseando en el anonimato | Potosi, Bolivia |
| 16:45 - 17:30 | Ricardo Supo Picón | Érase una vez cuando hackearon un NIC | Peru |
22 de abril
| Hora | Expositor | Conferencia | País |
|---|---|---|---|
| 08:00 - 08:30 | Registro - Acreditación | ||
| 08:30 - 09:00 | Proyecto OWASP | ||
| 09:00 - 09:45 | Juampa Rodríguez | 0037: Con Licencia para F*ckear! | La Paz, Bolivia |
| 09:45 - 10:30 | Jorge Santillán | Kit de robótica economico | Sucre, Bolivia |
| 10:30 - 11:00 | Pausa para café | ||
| 11:00 - 11:45 | Israel Aràoz | El salto del León ( win32 Exploiting ) | Santa Cruz, Bolivia |
| 11:45 - 12:30 | Elvin Mollinedo | Biotecnología | Santa Cruz, Bolivia |
| 12:30 - 14:00 | Horario de Almuerzo | ||
| 14:00 - 14:45 | Richard Villca | Desarrollo de Exploits | Oruro, Bolivia |
| 14:45 - 15:30 | Pablo Videla | Ingeniería (Anti) Social | Chile |
| 15:30 - 16:00 | Pausa para café | ||
| 16:00 - 16:45 | Boris Murillo | "MAFIA inc. How bad guys own our money ...and data" | La Paz, Bolivia |
| 16:45 - 17:30 | Diego Bruno | DevOps - Del Salar de Uyuni a Skynet | Argentina |
TALLERES

|
Top 10 OWASP al Cumplimiento de PCI-DSS v3.2 |
| Detalle del training...
Costo para Miembros OWASP: 200 Dolares Americanos
| |
| Ing. Ricardo Supo Picon
Co-lider del Capítulo Peruano de OWASP, CTO & Founder de INZAFE S.A. (Brasil - Chile - Perú), Ingeniero de Sistemas por la Universidad de Lima y Postgrado en Seguridad Informática por la UOC España. Reconocido por el gobierno peruano por su apoyo a combatir el Cybercrimen. Dispone de más de 10 años de experiencia en el sector bancario latinoamericano especializándose en los temas de ethical hacking, análisis forense, pentesting web, programación segura, ingeniería reversa, análisis de malware, optimización, revisión de código, criptografía y fraude bancario. |

|
Desarrollo de Exploit y Herramientas de Seguridad con Python
Costo para Miembros OWASP: 200 Dolares Americanos
|
| Detalle del training... | |
| Ing. Israel Aráoz S.
CTO & Founder DEFENET (Defense Network) con más de 10 años de experiencia en seguridad informática, Implementación de normas ISO 27001 y ISO 22301, Miembro del Capitulo Owasp Bolivia, Docente de pre-grado y posgrado en Criptografia, Auditoria Informatica ,Ejecución de Pruebas de Intrusión en Guatemala, Bolivia , Chile, Honduras , Instructor en Análisis Forense Digital, Exploiting, Ingeniera Inversa , Certificación en Certified Ethical Hacker & Computer Hacking Forensic Investigator, Exploiting & Reversing sobre Windows & Linux, Scripting Python. |
ORGANIZA: OWASP Chapter Bolivia
Te invitamos a ser parte del capítulo OWASP Bolivia.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP BOLIVIA
Redes Sociales
CORDOBA: 19 de Abril de 2017 (Conferencia de Seguridad Gratuita)
El evento más importante de la región llega a Códroba, OWASP Latam tour 2017!.
Reconocidos expositores estarán presentando conferencias sobre los temas más importantes en Seguridad en Aplicaciones.
REGISTRO
TBD
UBICACION
Instituto Universitarío Aeronáutico, Av Fuerza Aérea 6500 de la Ciudad de Córdoba
Córdoba, Argentinac
AGENDA
Se encuentra abierto el llamado a conferencistas!! (Call for papers is open!)
ORGANIZA: OWASP Chapter Córdoba
| TALLER Y CONFERENCIAS - OWASP LATAM TOUR 2017 | |
|
Miércoles 5 de Abril (Talleres - A definir) | |
| Descripcion y Objetivo | |
|
El evento más importante de la región llega nuevamente a Uruguay, OWASP Latam tour 2017!. |
| TALLER: Miércoles 5 de Abril | |
| Taller: Owasp top 10 hands on training | |
| Durante todo el OWASP Latam Tour se estarán realizando talleres de capacitación dictados por destacados profesionales en la materia. En Uruguay, se llevará a cabo el siguiente taller: Owasp top 10 hands on training el día miércoles 5 de abril de 2017 en el Hotel IBIS - Montevideo, Uruguay. | |
| Owasp top 10 hands on trainings
Este entrenamiento ayuda a los desarrolladores a conocer sobre seguridad en el desarrollo web de forma adecuada. Orientado a desarrolladores y personas relacionados con el ciclo de vida del desarrollo de software o sus pruebas de seguridad. Nivel: Básico-Intermedio Objetivos: - Conocer OWASP Top 10 - Aprender cómo comprobar cada vulnerabilidad desde el punto de vista del Desarrollador
El grupo de OWASP Uruguay brindará un taller con sus mejores exponentes.
Precio: U$S 250 REGISTRO TRAINING - USD 250 | |
| Fecha | Lugar |
| TALLER: Miércoles 5 de Abril | Hotel IBIS |
| Precio y Registro | |
El ingreso al entrenamiento es PAGO con un costo de USD 250 - El proceso de registro lo podrá ubicar en el siguiente link Link de Registro al Training en el OWASP LATAM TOUR 2017: REGISTRO TRAINING - USD 250 | |
| CONFERENCIA: Jueves 6 de Abril | ||
| Fecha | Lugar | |
| Miércoles 6 de Abril | Auditorio Massera - Universidad de la RepúblicaPasaje Landoni y J.Herrera y Reissig, Montevideo, Uruguay - www.fing.edu.uy | |
| Precio y Registro | ||
El ingreso al evento es GRATUITO - El proceso de registro lo podrá ubicar en el siguiente link Link de Registro al OWASP LATAM TOUR 2017: Registro Gratuito al OWASP LATAM TOUR 2017 - URUGUAY | ||
| DETALLES DE LA JORNADA | |||||
| Horario | Modulo | Ponente | Detalles | ||
| 9:00-9:30 | Acreditación | Acreditación | Acreditación | ||
| 9:30 - 10:30 | Bienvenida | Mateo Martínez (OWASP Uruguay) | Presentación de OWASP y Proyectos | ||
| 10:30 - 11:30 | Esoteric Web Application Vulnerabilities | Andrés Riancho | Una interesante charla que muestra casos practicos de vulnerabilidades complejas (que no se ven todos los dias). | ||
| 11:30 - 12:30 | OWASP Security Knowledge Framework | Edgar Salazar | OWASP SKF pretende ser una herramienta que se utiliza como guía para construir y verificar software seguro. También se puede utilizar para entrenar a los desarrolladores sobre la seguridad de las aplicaciones. La educación es el primer paso en el ciclo de vida de desarrollo de software seguro. | ||
| 12:30 - 14:00 | Corte | Almuerzo | Almuerzo | ||
| 14:00 - 14:45 | Hacking con ZAP | Santiago Vazquez (Paraguay) | Presentaremos diversas técnicas para hacer hacking de apliaciones usando ZAP | ||
| 14:45 - 15:30 | Hacking and Bitcoins (not hacking BITCOINS) | Alberto Hill | Presentaremos los problemas de seguridad mas importantes en la historia de cryptomonedas, en particular bitcoins, evaluacion de la seguridad en bitcoins, y resumen donde los problemas son basicamente los mismos de hace 15 años en portales web, y no en el diseño de blockchain/bitcoins, donde la seguridad fue contempleada desde el diseño. Se termina con un mapeo del owasp top 10 2013 y los incidentes mencionados asi como un caso real de hacke de sitio administrador de bitcoins. | ||
| 15:30 - 16:00 | Break | Break | Break | ||
| 16:00 - 16:45 | (fr)Agile Security Testing | Felipe Zipitria | Descripcion | ||
| 16:45 - 17:30 | OWASP ASVS - Cómo me puede servir | Gerardo Canedo | Charla de Difusión del OWASP ASVS, Entry level. Contaré nuestra experiencia de utilizarlo como requerimientos de seguridad. | ||
ORGANIZA: OWASP Chapter Uruguay
Te invitamos a ser parte del capítulo OWASP Uruguay.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP URUGUAY
OWASP Latam Tour en Buenos Aires, Argentina
Invitamos a estudiantes, desarrolladores, expertos en seguridad informática y curiosos en general a compartir con la comunidad de OWASP un nuevo evento en Buenos Aires! Será una jornada de charlas técnicas, en un ambiente relajado e ideal para conocer otras personas interesadas en la seguridad en aplicaciones.
Inscripcion
TDB
Fecha y lugar
28 Abril 2017 - 9am (puntual!)
DigitalHouse | Coding School (Monroe 860)
Charlas
Se encuentra abierto el llamado a conferencistas!! (Call for papers is open!)
| Hora | Titulo | Orador |
| 9:10 | Introducción a OWASP | Martín Tartarelli / Andrés Riancho |
ORGANIZA: OWASP Chapter Argentina
Te invitamos a ser parte del capítulo OWASP Argentina.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP Argentina
Costa Rica: 21 de Abril de 2017 (Conferencia de Seguridad Gratuita)
El evento más importante de la región llega a San José, Costa Rica, OWASP Latam tour 2017!.
Expositores nacionales e internacionales estarán presentando conferencias sobre los temas más importantes en Seguridad en Aplicaciones.
REGISTRO
https://www.eventbrite.com/e/owasp-latam-tour-2017-costa-rica-tickets-32740071435
UBICACION
La conferencia se llevará a cabo en las instalaciones del Centro Nacional de Alta Tecnología(CENAT). Edificio Dr. Franklin Chang Diaz, 1.3 km. Norte de la Embajada de EE.UU. Pavas, San José, Costa Rica.
AGENDA
| OWASP LATAM TOUR 2017 - SAN JOSE, COSTA RICA | ||||||
|---|---|---|---|---|---|---|
| Hora | Nombre de la Conferencia | Expositor / Speaker | Detalles | Ubicación | ||
| 7:00 - 8:00 | Recepción y Registro | |||||
| 8:00 -8:15 | Bienvenida | Michael Hidalgo (OWASP Costa Rica) | Presentación de OWASP y Proyectos | Salón #1 | ||
| 8:15 -9:15 | Keynote:Threat Modeling w/ PASTA - Risk Centric Application Threat Modeling Case Studies | Tony UcedaVelez Atlanta, Georgia | Developers needs prescriptive guidance on preemptive design and coding techniques. This can be done blindly or in alignment to both application use cases and the context of abuse cases or threats. This talk will speak to case studies in risk centric threat modeling using the PASTA (Process for Attack Simulation & Threat Analysis) methodology and provide 3 use cases of IoT, E-Commerce, and Mobile Applications.
This talk will assume that a basic understanding of data flow diagramming, pen testing, security architecture, and threat analytics is understood by the audience. This talk also centers around the idea of modeling threats for applications based upon a higher propensity of threat intelligence, how to harvest and correlate threat patterns to your threat model and also how to correlate a threat model to defining preemptive controls and countermeasures to include in the overall design. This talk will focus on walking attendees through the PASTA threat modeling methodology over 3 different deployment models for technology: IoT, E-Commerce, and Mobile. The talk will place specific emphasis on phases II (Technology Enumeration), phase III (Application Decomposition), and phase IV (threat analysis). Although all 7 phases of the PASTA threat modeling methodology will be exemplified, discussions around what tools and techniques around phases II, III, and IV will be discussed in detail since many industry professionals find it challenging to know the various application components that make up the various tiers of an application model. I will be exemplifying some tools to enumerate technical components across various application levels (ex: fingerprinting service PIDs on different apps or systems across IoT, Mobile, eCommerce) as each of these types of system environments are different. Another emphasis on the talk will be around defining trust boundaries while data flow diagramming and identifying what possible countermeasures to introduce from an architectural level. We'll review security architectural best practices from SABSA and TOGAF and how it can fortify secure design patterns. Stage/ Phase IV (Threat Analysis) will also be a key focus as we speak on practical ways in which threat data can be harvested as well as collected from external threat sources. We'll be integrating STIX and TAXII considerations on how to have infrastructure that can feed relevant data points to your threat model. The actual threat modeling methodology can be found here: https://www.versprite.com/PASTA-abstract.pdf |
Salón #1 | ||
| 9:20 - 10:15 | Identity and Access Management the fundamentals | Karina Quiros Rapso Costa Rica | Identity and Access Management es un conjunto de procesos y tecnologías para permitir la administración de identidades y control de los accesos que estas necesitan para utilizar recursos tecnológicos en la compañía. En términos de gestión de accesos, este aspecto de seguridad ha sido manejado por cada una de las aplicaciones, por consiguiente, la información se encuentra en múltiples repositorios, con diferentes políticas y procesos.
Implementaciones de este tipo, dificulta la visibilidad de los accesos que tiene cierta persona en un momento determinado e incrementa los riesgos de seguridad cuando una persona se retira de la empresa y se debe proceder con la eliminación de todas las autorizaciones a los sistemas que haya utilizado. El conocer cuáles son los procesos básicos requeridos para implementar un manejo adecuado de esta información, permite evaluar el nivel de madurez de la organización en esta área y brinda una visión para definir un plan de acción, conociendo los beneficios y retos que cada etapa conlleva. |
Salón #1 | ||
| 9:20 - 10:15 | DevOps: Primeros Pasos | Martin Flores González Costa Rica | Bugs are the main source of vulnerabilities in software; being able to quickly and seamlessly deploy fixes all the way to production should be one of the main goals of any development team; practices allowing towards that goal; by means of removing silos and barriers, need to be embraced by organizations of all sizes. DevOps movement has gain momentum, learning about its spirit, main practices and the overall journey; could enable software development organizations to find what is needed so they could start their journey too. Join us for this presentation were we will cover some of the history of DevOps, its practices and process and finally a short demo of an application embracing these practices. | Salón #2 | ||
| 10:15-10:30 | Coffee Break | Coffee Break | Coffee Break | Coffee Break | ||
| 10:30-11:30 | Signed JSON Web Token for ensuring data integrity and authenticity of REST Messages | Allan R. Cascante Valverde | When passing on a request through different RESTful services there is always the risk of a forged request attack. To avoid such risk a mechanism to persist authentication across the multiple REST services is required, a signed JSON Web Tokens (JWT) could be a viable solution to prevent this attack. Json Web Tokens allows for claims to be transferred between two systems. These claims form the payload of the JWT which is URL safe base64 encoded. The token can then take a digital signature, of which the private key owner would be the service that was able to authenticate the request initially, so that the request would be authenticated for all others in the chain; as long as the digital signature is still valid. Ensuring data integrity and security across multiple services and components can be a challenge solved by the use of JWT Tokens. | Salón #1 | ||
| 11:30-12:30 | Protecting your web sites and applications through the cloud | Luis Diego Raga Costa Rica | Every day we see more and more companies adopting cloud technologies to protect their web sites and applications from external threats such a DDoS and application layer attacks. There are several benefits of using a cloud solution to augment your security controls and security perimeter, but the main one is that you can drop malicious traffic on the cloud, saving you from processing and inspecting this traffic. In this talk we will cover some of the technologies that can be applied using cloud technologies to protect your websites and Internet facing applications | Salón #1 | ||
| 12:30-1:30 | Lunch | Lunch | Lunch | Lunch | ||
| 1:30-2:30 | Keynote:Hassle Free Security Automation with Free and Open Source tools | Anderson Dadario Sao Paulo, Brazil | Security personnel headcount is always behind IT departments, thus security automation is mandatory to maximize the efficiency of the information security department. However automation is tricky, time-consuming and hard to maintain. Especially if the information security team is small. That said, I'd like to present how to tackle the most important points with the least effort using free and/or open source technologies like Docker, Intelligence Gathering scripts, Slack, Mozilla tools, OWASP tools and others to maximize the security investment. On the other hand the security industry has some limitation when it comes to security software focused on security automation, hence I'll also discuss those limitations to show opportunities. And last but not least, I will release some public code on GitHub related with automation as well. [ Disclaimer: I work for Gauntlet, a service related to this talk, but although there is a free service on there, I won't discuss it in the talk. I'm willing to share my knowledge only and keep it vendor agnostic. If you have any doubts, just ask me or check my past slides in my website and you'll see that there are no slides covering Gauntlet in the middle of the talk expect on 'Who I am' slides. Thank you. | Salón #1 | ||
| 2:30-3:30 | Challenges of Securing 3rd party Cloud Infrastructure | Oscar Monge Espana Costa Rica | La conferencia habla de los problemas que se pueden encontrar en empresas medianas y coporaciones al intentar asegurar IaaS en proveedores externos de servicios de nube. Abarca componentes de Logging & Monitoring, Automation Scripts. | Salón #1 | ||
| 2:30-3:30 | Análisis de uso malware Mirai en PSI DyN DNS | Kenneth Monge Quirós | El tema central va a ser el ataque masivo del cual fue víctima el proveedor de servicios de Internet llamado Dyn Managed DNS, que bajo un DDoS vió interrumpido sus servicio a clientes de mucha importancia. | Salón #2 | ||
| 3:45-4:00 + | Cierre | Cierre | Cierre | Salón #1 | ||
ORGANIZA: OWASP Chapter Costa Rica
Te invitamos a ser parte del capítulo OWASP Costa Rica.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP Costa Rica
OWASP Latam Tour en la Patagonia, Argentina
Invitamos a estudiantes, desarrolladores, expertos en seguridad informática y curiosos en general a compartir con la comunidad de OWASP un nuevo evento en la Patagonia! Será una jornada de charlas técnicas, en un ambiente relajado e ideal para conocer otras personas interesadas en la seguridad en aplicaciones.
Registro
El registro a las charlas es libre y gratuito. - REGISTRARSE AQUI
Viernes 21 de abril, Neuquén. De 9:00hs a 18:00hs -> Imperdible!
Agenda
| Hora | Conferencia | Expositor | Pais |
|---|---|---|---|
| Presentación | Gaston Toth | Patagonia, Argentina | |
| Donde está mi Dinero!! - Casos reales en cyber crimen de ATM’s | Camilo Fernandez | Guatemala | |
| Hacking a NFC/RFID | Nahuel Grisolia | Buenos Aires, Argentina | |
| Sysadmin Fails - El despertar de root | Ramon Arias | Santiago, Chile | |
| Remote wars phantom menace | Pablo Torres | Buenos Aires, Argentina | |
| Seguridad Informatica en las Universidades | Jorge Sznek | Neuquen, Argentina | |
| Internet de las cosas, Botnet y Seguridad | Natalia Toranzo | Neuquen, Argentina | |
| Mobile pentesting | Juan Urbano Stordeur | Buenos Aires, Argentina | |
| Es posible hackear un pais? | Camilo Fernandez | Guatemala |
¿Dónde?
Viernes 21
Universidad Nacional del Comahue, Buenos Aires 1400, Neuquén
ECUADOR: 8 de Abril de 2017 (Conferencia de Seguridad Gratuita)
El evento más importante de la región llega nuevamente a Ecuador, OWASP Latam tour 2017!.
Expositores internacionales estarán presentando conferencias sobre los temas más importantes en Seguridad en Aplicaciones web y mas.
REGISTRO
El registro a las charlas es gratuito. REGISTRESE AQUI
Sábado 8 de abril, Quito-Ecuador. De 9:00hs a 17:00hs -> No te lo pierdas!
UBICACION
Ladrón De Guevara E11-253- Universidad "Escuela Politécnica Nacional"
PO•Box: 17-01-2759
Quito, Ecuador
AGENDA
Este evento solo se puede llevar a cabo gracias a la inmensa generosidad y apoyo de nuestros patrocinadores:
- Escuela Politecnica Nacional
- Kaspersky Lab
- Krakensec
¿Te gustaría apoyar a nuestro evento? Contactanos.
ORGANIZA: OWASP ECUADOR
Te invitamos a ser parte del capítulo OWASP ECUADOR.
CHARLAS
El acceso a las conferencias es gratuito.
| Hora | Título | Conferencista | Pais |
| 09:00 | Introducción al capítulo OWASP Ecuador | Fernando Vela & Roberto Andrade | Ecuador |
| 10:00 | Hackeando WebServices | Alejandro Quiroz | Ecuador |
| 10:45 | Virtualizacion Segura | Victor Chisava | Colombia |
| 11:45 | Hackeando Apache | Jorge Torres | Colombia |
| 13:00 | Break | ||
| 14:00 | Érase una vez cuando hackearon un NIC | Ricardo Supo Picon | Peru |
| 14:45 | Comunicaciones Seguras VOIP | Cristian Palacios | Ecuador |
| 15:45 | Ransomware: Amenaza despiadada | Nahum Davila | Colombia |
ORGANIZA: OWASP Chapter Ecuador
Te invitamos a ser parte del capítulo OWASP Ecuador.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP Ecuador
Riviera Maya: 21 y 22 de Abril de 2017 en Cancun, Quintana Roo, Mexico
Para la edición 2017 estamos muy emocionados de que México se una al OWASP LATAM Tour. Por primera vez nos reuniremos en Cancun, Quintana Roo para un día de conferencias impartidas por expertos en la industria en donde discutiremos las últimas tecnologías, técnicas de ataque/protección y muchos otros temas relacionados con la seguridad informática.
OWASP LATAM Tour es un evento realizado en todo América Latina que promueve la seguridad de software con el objetivo de crear conciencia sobre los riesgos a los que nos enfrentamos actualmente. Está enfocado a instituciones como universidades, organismos gubernamentales, empresas de TI y entidades financieras.
¿Quieres tener presencia en el evento? Call For Sponsors
¿Tienes una plática o taller que compartir? Call For Papers
REGISTRO
La entrada a las conferencias es gratuita. Los asistentes únicamente deberán registrarse en la lista de asistencia.
Registro a OWASP LATAM Tour 2017 Riviera Maya
FECHA Y UBICACION
El 21 y 22 de abril en Tech Garage en Cancun, Quintana Roo, Mexico.
¿Necesitas viajar a Cancun? A partir del 22 de marzo podrás utilizar el código 'OWASP' para obtener un 10% en tu vuelo con Interjet.
AGENDA
CONFERENCIAS (Sábado 22 de abril)
El acceso a las conferencias es gratuito con previo registro.
| Hora | Título | Conferencista |
| 9:30 | Introducción a evento | OWASP Riviera Maya |
| 09:45 | Mis vulnerabilidades favoritas del 2016 en Google | Eduardo Vela (@sirdarckcat) |
| 10:45 | Vulnerabilidades web esotéricas | Andres Riancho (w3af) |
| 11:45 | BREAK/NETWORKING | |
| 12:15 | Comprometiendo el Internet Industrial de las Cosas (IIOT) | Rafael Bucio (@bucio) |
| 13:15 | Shields up and go to red alert! | Edgar Baldemar (edgarbaldemarmx) |
| 14:15 | Atacando el atacante, crónica de un sysadmin | Jacobo Tibaquirá Murillo (jjtibaquira) |
| 15:00 | BREAK/NETWORKING | |
| 16:30 | Un lobo disfrazado de oveja | Roberto Salgado (@lightos) Paulino Calderón (@calderpwn) |
| 17:30 | Timing attacks | Andres Riancho (w3af) |
| 18:30 | Aventuras y desventuras de un pentester | Jaime Andrés Restrepo (@dragonjar) |
TALLERES (Viernes 21 de abril)
El costo de los talleres es de 250 usd por persona. Registrate aquí. Estos son los talleres confirmados hasta el momento pero la agenda final se publicará la primera semana de abril. Recuerden que tienen hasta el 1 de marzo para mandar su propuesta de taller.
| Hora | Título | Instructor |
| 12:00-18:00 | OWASP TOP 10 Web - Desde descubrimiento a explotación | Edgar Baldemar Ramos (edgarbaldemarmx) |
| 10:00-18:00 | OWASP TOP 10 Móvil - Desde descubrimiento a explotación | Victor Hugo Ramos Alvarez (vhramosa) |
| 10:00-14:00 | Metasploit 101 (TALLER GRATUITO) | Jacobo Tibaquira (jjtibaquira) |
PATROCINADORES
Este evento solo se puede llevar a cabo gracias a la inmensa generosidad y apoyo de nuestros patrocinadores. Una vez más le agradecemos por ayudar a mejorar la seguridad de software en México a:
- Bugcon Security Conferences
- Consultora Ohkasis
- CyberOPSEC México
- DragonJAR
- FMCancun
- ITCenter Solutions
- ITSEC
- Papa Johns Cancun
- Pricetravel
- Protektnet
- Purple Security
- The Home Depot MX
- Tech Garage Cancun
- Tropicode
- UniversIT
- Websec México
¿Te gustaría apoyar a nuestro evento? Hay muchas formas de hacerlo.
ORGANIZA: OWASP Chapter Riviera Maya
Te invitamos a ser parte del capítulo OWASP Riviera Maya.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP Riviera Maya
Manizales: 3 de Abril de 2017
OWASP LATAM Tour es un evento realizado en todo América Latina que promueve la seguridad de software con el objetivo de crear conciencia sobre los riesgos a los que nos enfrentamos actualmente. Está enfocado a instituciones como universidades, organismos gubernamentales, empresas de TI y entidades financieras.
REGISTRO
La entrada a las conferencias es gratuita. Los asistentes únicamente deberán registrarse en la lista de asistencia.
FECHA Y UBICACION
El 3 de abril en el auditorio 323 - Universidad de Manizales.
AGENDA
CHARLAS
El acceso a las conferencias es gratuito.
| Hora | Título | Conferencista |
| 09:00 | Introducción al capítulo OWASP Manizales | Jaime Restrepo |
| 10:00 | Hackeando APIs REST | Juan Castro |
| 11:00 | BREAK | |
| 11:30 | Ingenieria Social enfocada en Seguridad Web | Hugo Bayona |
| 12:30 | ALMUERZO LIBRE | |
| 14:00 | Seguridad en redes Smartgrid | Diego Gonzales |
| 15:00 | Nsearch, lo que le faltaba a nmap | Jacobo Tibaquira |
| 16:00 | BREAK | |
| 16:30 | Sorpresas de la seguridad informatica | Santiago Bernal |
| 17:30 | Web Application Security Testing the OWASP Style | John Vargas |
PATROCINADORES
Este evento solo se puede llevar a cabo gracias a la inmensa generosidad y apoyo de nuestros patrocinadores:
¿Te gustaría apoyar a nuestro evento? Contactanos.
ORGANIZA: OWASP Manizales
Te invitamos a ser parte del capítulo OWASP Manizales.
Lima, Perú: 22 de Abril de 2017 (Conferencia de Seguridad Gratuita)
El evento más importante de la región llega a Lima, Perú, OWASP Latam Tour 2017!.
Expositores internacionales estarán presentando conferencias sobre los temas más importantes en Seguridad en Aplicaciones.
REGISTRO
TBD
UBICACIÓN
TBD
AGENDA
Se encuentra abierto el llamado a conferencistas!! (Call for papers is open!) Presente aqui su charla
ORGANIZA: OWASP Chapter Perú
Te invitamos a ser parte del capítulo OWASP Perú.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP Perú
Bogotá: 3 de Abril del 2017 en Bogotá, Colombia
En 2017 volvemos al Latam Tour, con la idea de tener un día para compartir todos los proyectos que tiene OWASP, discutir como los usamos, que hemos aprendido de ellos, la forma en que podemos seguir fortaleciendo nuestra seguridad digital con dichos proyectos en un ambiente de aprendizaje, junto a los miembros del Capítulo Bogotá y todos los asistentes que quieran aprender y compartir en este evento.
OWASP LATAM Tour es un evento realizado en todo América Latina que promueve la seguridad de software con el objetivo de crear conciencia sobre los riesgos a los que nos enfrentamos actualmente. Está enfocado a instituciones como universidades, organismos gubernamentales, empresas de TI y entidades financieras.
Tu puedes ser uno de nuestros Patrocinadores, si estas interesado escribe a [email protected] o cualquier miembro del capítulo OWASP Bogotá para más información.
El llamado a charlas ya se ha cerrado, gracias a todos los que nos enviaron sus propuestas.
REGISTRO
La entrada al evento es totalmente gratuita, pero para términos de logística necesitamos que todos los asistentes se encuentre registrados en la lista de asistencia del evento.
Registro a OWASP LATAM Tour 2017 Bogotá
FECHA Y UBICACION
El 3 de Abril en el Auditorio Principal de la Universidad Piloto de Colombia, ubicada en la Carrera 9 No. 45A - 44 en Bogotá, Colombia.
AGENDA
03 de Abril
| Hora | Expositor | Conferencia | País |
|---|---|---|---|
| 07:50 - 08:25 | Registro - Acreditación | ||
| 08:25 - 08:40 | Giovanni Cruz Forero | Esto es OWASP | Colombia |
| 08:40 - 10:40 | Ricardo Supo Picón | Del Top 10 OWASP al Cumplimiento de PCI-DSS v 3.2 - Workshop | Perú |
| 10:40 - 11:05 | Jeffrey Steve Borbón Sanabria | ¿Y cómo editamos sistemas legados que nadie sabe como sirven? | Colombia |
| 11:05 - 11:30 | Break | ||
| 11:30 - 12:00 | Juan Pablo Arévalo - Andrés Vega | OWASP Mobile Project and Internet of Things | Colombia |
| 12:00 - 12:40 | Hugo Alvarez - Maria Alejandra Blanco | Offensive Web Testing Framework (OWTF) | Colombia |
| 12:40 - 13:40 | Almuerzo | ||
| 13:45 - 14:30 | Edgar Felipe Duarte Porras | Malware: Burlando los antivirus con JavaScripts | Colombia |
| 14:30 - 14:55 | Tatiana Higuera - Nicolas Moreno | OWASP SeraphimDroid Project | Colombia |
| 14:55 - 15:40 | Oscar Mondragon | Antidefacement Web | Colombia |
| 15:40 - 16:10 | Break | ||
| 16:10 - 16:45 | David Useche – Maria Paula Bueno | The OWASP Enterprise Security API (ESAPI): Security Control Library | Colombia |
| 16:45 - 17:30 | Jonathan Maderos | Hackeando una Elección | Venezuela |
| 17:30 - 17:45 | CIERRE | ||
PATROCINADORES
Este año el OWASP LATAM Tour en Bogotá es posible gracias a nuestros patrocinadores:
Tu puedes ser uno de nuestros patrocinadores, no dudes en comunicarte con cualquier miembro del Capítulo Bogotá.
ORGANIZA: OWASP Chapter Bogotá
Te invitamos a ser parte del capítulo OWASP Bogotá.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP Bogotá
El Salvador: Martes 25 de Abril de 2017 (Conferencia de Seguridad Gratuita)
El evento más importante de la región llega a San Salvador, El Salvador, OWASP Latam tour 2017!.
Expositores internacionales presentando conferencias sobre los temas más importantes en Seguridad en Aplicaciones WEB.
REGISTRO
Evento Completamente Gratuito, a profesionales y estudiantes
Registrarse Aquí
UBICACION
Universidad Don Bosco, Campus Soyapango
AGENDA
| Hora | Agenda | Tematica | Expositor |
|---|---|---|---|
| 8:00 - 8:15 | Registro | ||
| 8:15 - 9:00 | Presentación del Capitulo OWASP El Salvador | Objetivos del Capitulo | |
| 9:05 - 10:00 | |||
| 10:00 - 10:15 | Coffe Break | ||
| 10:20 - 12:00 | OWASP Top 10 como mecanismo de protección
ante la Ciber Delincuencia. |
Como utilizar OWASP Top 10
como marco de referencia y Ley de Delitos Informaticos de El Salvador |
Lic. Nelson Chacon Reyes
Lider Capitulo OWASP El Salvador |
| 12:00 - 14:00 | Almuerzo | ||
| 14:00 - 15:00 | Evadiendo los 20 Controles Criticos
de Seguridad |
Técnicas comúnmente usadas para
Evadir los controles de Seguridad |
Walter Cuestas, PERU |
| 15:00 - 15:15 | Coffe Break | ||
| 15:15 - 17:00 | |||
| 17:00 - 18:00 | Cierre - Rifas |
Se encuentra abierto el llamado a conferencistas!! (Call for papers is open!)
Patrocinadores
Universidad Don Bosco, El Salvador. [ http://www.udb.edu.sv/udb/ ]
Instituto Superior de Tecnología Aplicada [ http://www.insteconline.com/ ]
TigerSecurity [ https://www.facebook.com/TigerSecSV/ ]
WebCommService [ http://www.webcommservice.com ]
ORGANIZA: OWASP Chapter El Salvador
Te invitamos a ser parte del capítulo OWASP El Salvador.
Toda la información del capítulo se encuentra en: Link al Sitio Web de OWASP El Salvador
OWASP CHILE invita a estudiantes y profesionales interesados en Seguridad de la Información, a nuestro evento OWASP LatamTour.

Charlas miércoles 26 abril 2017 [Inscribete aquí]
| Nro | Hora | Expositor | Título | Descripción | |
|---|---|---|---|---|---|
| 1 | 08:30 a 09:00 | Acreditación de asistentes | |||
| 2 | 09:00 a 09:05 | DUOC-UC y OWASP | Palabras de Bienvenida | ||
| 3 | 09:05 a 10:45 | Carlos Allendes | Hacker o Empresario? | La seguridad TI enfrenta el riesgo creciente del "hacking as a service". El cibercrimen ya derivó en un "modelo de negocio", que usa estrategias de mercado y define su "cadena de valor", similar a una empresa legítima: maximiza beneficios, innova y gestiona RRHH). Esta realidad llevará a nuevos niveles los riesgos tecnológicos y la necesidad de inversión en seguridad. | |
| 4 | 10:45 a 11:35 | TBD | TBD | TBD | |
| 5 | 11:35 a 11:50 | Coffee Break | |||
| 6 | 11:50 a 12:35 | Claudio Salazar | "Detectem" un proyecto open-source para seguridad | Las herramientas de pentesting (al igual que cualquier software) requieren mejoras y nuevas funcionalidades. Pero a menudo los proyectos open-source no usan buenas prácticas de desarrollo. Esta charla analiza la necesidad de saber programar para un pentester y propone buenas prácticas de programación, basado en la experiencia al crear la herramienta chilena: Detectem. | |
| 7 | 12:35 a 13:20 | Sebastián Quevedo | Análisis de anatomías de ataque: Ransomware y sus contramedidas | Existe un gran impacto del Ransomware hacia las organizaciones y personas. Este tipo de malware tiene una alta tasa de propagación/infección. Las primeras generaciones usaban criptovirología (año 2008) hasta los actuales que son bloqueadores de sistemas. Esta charla evalúa los principales efectos/daños que provoca y propone una estrategia práctica/efectiva para enfrentar esta amenaza. | |
| 8 | 13:20 a 15:00 | Horario de Almuerzo | |||
| 9 | 15:00 a 15:45 | Gustavo Nieves Arreaza | Buenas prácticas del SDLC basado en OWASP | Muchas organizaciones y personas entienden a OWASP como un referente para identificar fallas en el software ya terminado, pero la seguridad es un ciclo continuo, que debe mantenerse en paralelo a las fases del desarrollo y programación del software. OWASP provee herramientas útiles para todas las fases del ciclo de vida "SDLC". | |
| 10 | 15:50 a 16:30 | Ricardo Supo | Érase una vez cuando hackearon un NIC | Un día regresando del trabajo te reportan un incidente de riesgo bajo pero al analizarlo el NIC de un país estaba comprometido. Se narrará la historia jamás contada de un incidente nacional y como se pudo reducir los riesgos rápidamente. Los incidentes sucedidos en el NIC, banca y gobierno. Así mismo como las metodologías de OWASP apoyan a reducir los riesgos. | |
| 11 | 16:45 a 17:20 | Sorteo y Premios |
São Paulo: 22 de Abril de 2017
O evento mais importante sobre Segurança de Aplicações da América Latina chega em São Paulo, OWASP Latam Tour 2017.
Profissionais nacionais e internacionais estão apresentando palestras sobre os temas mais importantes em Segurança de Aplicações.
Caracas: April, 27th 2017
Registro
El registro es totalmente gratis, nos complacería mucho que nos acompañaras este día.
Registrate Aquí
Te esperamos!!!
UBICACIÓN
Universidad Central de Venezuela
Facultad de Ciencias
Auditórium Tobías Lasser
Paseo Los Ilustres Urb. Valle Abajo.
1040 Caracas
LISTADO DE SPEAKERS
| Registro 8:30 am | |||
| 9:00 am | OWASP Venezuela & UCV | Palabras de Bienvenida | |
| 9:15-9:55 am | TBD | TBD | |
| 10:00-10:40 am | TBD | TBD | |
| 10:40-11:10am | Coffee Break | ||
| 11:15-11:50 am | TBD | TBD | |
| 12:00-1:30 pm | Almuerzo Libre | ||
| 1:35-2:10 pm | TBD | TBD | |
| 2:15-2:40 pm | TBD | TBD | |
| 2:45-3:20 pm | Coffee Break | ||
| 3:35-4:10 pm | TBD | TBD | |
| 4:15-4:40 pm | TBD | TBD | |
| 4:45-5:00 pm | Palabras de cierre | ||
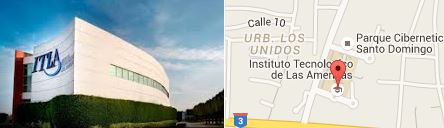
OWASP República Dominicana invita a estudiantes, profesionales e interesados en la Seguridad de la Información a nuestro segundo evento anual y gratuito de charlas OWASP, que realizaremos en el Instituto Tecnológico de Las Américas (ITLA) de la ciudad de Santo Domingo.
Charlas Jueves 6 abril [Registro Gratuito a Charlas]
| Nro | Expositor | Tema a Exponer | Descripción | |
|---|---|---|---|---|
| 1 | Willis Polanco [Dominicano] |
Palabras de Bienvenida | ||
| 2 | Jonathan Correa [Dominicano] |
Introducción al Capitulo de OWASP en República Dominicana (R.D) | Introducción a los objetivos de la comunidad internacional OWASP y expectativas a realizar en República Dominicana. | |
| 3 | Carlos Allendes [Chileno] |
Armar un Laboratorio de Hacking en 5 minutos. | Esta charla enseñará como armar un ambiente controlado de laboratorio, usando herramientas y recursos de OWASP, para practicar, auto-estudiar y entrenarse con aplicaciones web. | |
| 4 | Pausa de Café | |||
| 5 | Piero Alvigini [Dominicano] |
Corriendo un (C) SOC en el Caribe. | Se describe como opera SOC (Security Operations Center) en el caribe. El enfoque actual para el monitoreo continuo y respuesta ante incidentes frente a nuevas y emergentes amenazas de seguridad (APT). | |
| 6 | Ruddy Simons [Dominicano] |
Ransomware | El malware del tipo Ransomware se infiltra en la máquina de una víctima, bloquea su sistema y/o encripta los archivos del usuario (word, excel, ppt, fotografias), y así fuerzan a la víctima para obtener el pago de un rescate. | |
| 7 | Receso para Almorzar | |||
| 8 | Mario Orellana [Salvadoreño] |
Y cómo es que uno se convierte en hacker? | Mentalidad y perfil de un hacker y como iniciarse en la cyberseguridad. Demostración de las 5 fases de un ataque de hacking, y se entregará un breve análisis de las leyes informáticas de El Salvador y República Dominicana, para explicar bajo que condiciones podría ser considerado delito informático, una actividad no autorizada de intrusión. | |
| 9 | Ricardo Supo [Peruano] |
Érase una vez cuando hackearon un NIC | Un día regresando del trabajo te reportan un incidente de riesgo bajo pero al analizarlo el NIC de un país estaba comprometido. Se narrará la historia jamás contada de un incidente nacional y como se pudo reducir los riesgos rápidamente. Los incidentes sucedidos en el NIC, banca y gobierno y como no debió actuar el NIC. Así mismo como las metodologías de OWASP apoyan a reducir los riesgos. | |
| 10 | Luis Peralta [Dominicano] |
Palabras cierre |
Cursos/Taller[Registro de Asistentes]
| Nro | Expositor | Tema del Taller | Descripción |
|---|---|---|---|
| 1 | Ricardo Supo [Peruano] |
Del Top 10 OWASP al Cumplimiento de PCI-DSS v3.2 | PCI-DSS v3.2 en su Requisito 6, Desarrollar y mantener sistemas y aplicaciones seguros, exige seguir directrices seguras como las definidas por OWASP a las entidades bancarias emisoras de tarjetas de crédito.
En este taller se desarrollará de manera práctica el OWASP Top 10 tanto la detección y la explotación de cada una así como su corrección en código en ambientes de desarrollo bajo máquinas virtuales tanto para .Net como Java. |
Patrocinios
Le interesa participar con un stand en el evento y su logo en la página del Tour?
Pueden contactarnos en Oportunidades de patrocinio
Cualquier consulta puede canalizarla con el Presidente Owasp R.Dominicana: Jonathan Correa
¿Dónde y cuando?
Lugar: Instituto Tecnológico de Las Americas (ITLA) mapa
Parque Cibernético, República Dominicana
Fecha: Jueves 6 de Abril
Hacer click para ampliar mapa.
Redes Sociales

We are looking for Sponsors for the Latam Tour 2017
This is a truly unique opportunity to increase your brand recognition as a company dedicated to the highest standards of professional technology & security in the Latin-America region but also internationally throughout the world while supporting the continued activities conducted by OWASP worldwide.
- Sponsorship benefits for organizations specializing in IT & Security:
- Opportunity to use the latest technological trends for professional training / development
- Strengthen your company strategy by learning the latest trends in web software security
- Improve your business development strategy with leading information from the security industry
- Get networking and headhunting opportunities with world-class specialists and professionals
- Get the chance to interact with high-need discerning users to improve product development
- Increase your image as a professional company through this unique branding opportunity
- Sponsorship benefits for organizations utilizing the internet in their business:
- Opportunity to increase the international brand awareness and conduct business networking
- Strengthen your company strategy by learning the latest trends in web software security
- Improve your service development by understanding the latest trends in security issues & risks
- Contribute to information society as a company by developing safe and secure services
- Get the chance to interact with high-need discerning users to improve product development
- Opportunity to brand your company as one that focuses on the highest standards in technology
Make your company part of the conversation. Become a sponsor of the tour today!
SPONSOR OPPORTUNITIES OPORTUNIDADES DE PATROCINIO
Please contact [email protected] for further information
OWASP Latam Tour 2017 Team
Chapter Leaders
- Edgar Salazar (Venezuela)
- Elvin Mollinedo (Bolivia)
- Gaston Toth (Patagonia, Argentina)
- Diego Di Nardo (Patagonia, Argentina)
- John Vargas (Perú)
- Martin Tartarelli (Buenos Aires, Argentina)
- Magno_Logan (São Paulo, Brazil)
- Mateo Martinez (Uruguay)
- Mauro Flores (Uruguay)
- Felipe Zipitria (Uruguay)
- Fernando Vela (Ecuador)
- Ramiro Pulgar (Ecuador)
- Carlos Allendes (Chile)
- Gustavo Solano (Honduras)
- Jonathan Correa (Rep.Dominicana)
- Pablo Barrera (Guatemala)
- Paulino Calderon (Riviera Maya)
- Giovanni Cruz Forero (Bogotá)
- Nelson Chacon Reyes (El Salvador)
- Michael Hidalgo (Costa Rica)
OWASP Staff
- Alison Shrader (Finances)
- Kate Hartmann (Registration)
- Kelly Santalucia (Sponsorships)
- Laura Grau (Organization)



























