|
|
| Line 1: |
Line 1: |
| | __NOTOC__ | | __NOTOC__ |
| − | {|
| |
| − | |-
| |
| − | ! width="700" align="center" | <br>
| |
| − | ! width="500" align="center" | <br>
| |
| − | |-
| |
| − | | align="center" | [[Image:OWASPLatam_Banner_Screenshot.JPG|1100px]]
| |
| − | | align="center" |
| |
| − |
| |
| − | |}
| |
| | | | |
| | = Welcome = | | = Welcome = |
| Line 18: |
Line 9: |
| | | style="width: 95%; color: rgb(0, 0, 0);" | | | | style="width: 95%; color: rgb(0, 0, 0);" | |
| | <font size=2pt> | | <font size=2pt> |
| − | We are pleased to announce that the [http://www.owasp.org/index.php/Uruguay OWASP Uruguay chapter] will host the OWASP AppSec Latam 2012 conference in Montevideo, Uruguay at ANTEL National Telco Company. The event will be composed of 2 days of training (November 18-19), followed by 2 days of conference talks (November 20-21). | + | We are pleased to announce that the [http://www.owasp.org/index.php/Uruguay OWASP Uruguay chapter] will host the OWASP AppSec Rio de la Plata 2015 conference in Montevideo, Uruguay at ANTEL National Telco Company. The event will be composed of 2 days of training (November 31- December 1st), followed by 2 days of conference talks (December 2-3). |
| | | | |
| | | | |
| − | The Global AppSec Latin America 2012 Conference will be a reunion of Information Security latin american leaders, and will present cutting-edge ideas. OWASP events attract a worldwide audience interested in “what’s next”. The conference is expected to draw 200-250 technologists from Government, Financial Services, Media, Pharmaceuticals, Healthcare, Technology, and many other verticals.<br><br> | + | The AppSec Rio de la Plata 2015 Conference will be a reunion of Information Security latin american leaders, and will present cutting-edge ideas. OWASP events attract a worldwide audience interested in “what’s next”. The conference is expected to draw 300-400 technologists from Government, Financial Services, Media, Pharmaceuticals, Healthcare, Technology, and many other verticals.<br><br> |
| | | | |
| − | <br> If you have any questions, please email the conference committee: [ mailto: [email protected] AppSecLatam2012@owasp.org]<br><br> | + | <br> You can check all the updates and news in the website: [http://appsecriodelaplata.org/2015/ AppSec Rio de la Plata 2015 Website]<br><br> |
| | | | |
| − | <br> '''Who Should Attend Global AppSec Latin América 2012:''' | + | <br> '''Who Should Attend Global AppSec Rio de la Plata 2015:''' |
| | | | |
| | *Application Developers | | *Application Developers |
| Line 43: |
Line 34: |
| | | | |
| | |} | | |} |
| − |
| |
| − | <!-- Twitter Box -->
| |
| − |
| |
| − | | style="border: 0px solid rgb(204, 204, 204); width: 100%; font-size: 95%; color: rgb(0, 0, 0);" | <!-- DON'T REMOVE ME, I'M STRUCTURAL -->
| |
| − | <!-- There be dragons here -->
| |
| − | [[Image:OWASPL_Latam2012_Logo.JPG|300px]]
| |
| − |
| |
| − | {|
| |
| − | |-
| |
| − | | style="border: 1px solid rgb(204, 204, 204); width: 100%; font-size: 95%; color: rgb(0, 0, 0); background-color: rgb(236, 236, 236);" |
| |
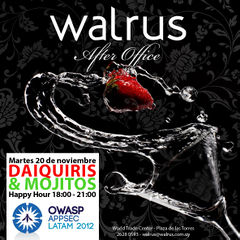
| − | Use the '''[http://search.twitter.com/search?q=%23AppSecLatam #AppSecLatam]''' hashtag for your tweets for AppSec Latin America 2012 (What are [http://hashtags.org/ hashtags]?)
| |
| − |
| |
| − | '''@AppSecLatAm Twitter Feed ([http://twitter.com/AppSecLatam follow us on Twitter!])''' <twitter>262394051</twitter>
| |
| − |
| |
| − | | style="width: 110px; font-size: 95%; color: rgb(0, 0, 0);" |
| |
| − | |}
| |
| − |
| |
| − | | style="width: 110px; font-size: 95%; color: rgb(0, 0, 0);" |
| |
| − | |}
| |
| − | <!-- End Banner -->
| |
| | | | |
| | | | |
| Line 69: |
Line 40: |
| | | | |
| | | | |
| − | The trainings will be held November 18th and 19th, 2012 (Sunday and Monday) and will run from 8:30 AM to 5:30 PM each day. | + | The trainings will be held November 31th and 1st December, 2015 and will run from 8:30 AM to 5:30 PM each day. |
| | | | |
| | | | |
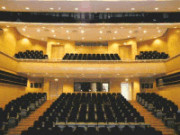
| − | AppSec Latam 2012 will be held in downtown Montevideo, Uruguay at the [http://www.antel.com.uy/antel/institucional/nuestra-empresa/complejo-torre Antel National Telco Company]. Directions are available through: [https://maps.google.com/maps?q=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&hl=es-419&ll=-34.899448,-56.179104&spn=0.098412,0.181789&geocode=FaOW6_0dt4qm_A&hnear=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&t=m&z=13 Google Maps] | + | AppSec Rio de la Plata 2015 will be held in downtown Montevideo, Uruguay at the [http://www.antel.com.uy/antel/institucional/nuestra-empresa/complejo-torre Antel National Telco Company]. Directions are available through: [https://maps.google.com/maps?q=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&hl=es-419&ll=-34.899448,-56.179104&spn=0.098412,0.181789&geocode=FaOW6_0dt4qm_A&hnear=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&t=m&z=13 Google Maps] |
| | <br> | | <br> |
| | <br> | | <br> |
| Line 80: |
Line 51: |
| | | | |
| | | | |
| − | == Developing Secure Java Applications with ESAPI == | + | == Training 1: (Call for papers Open!)== |
| − | '''Instructor:''' Fabio Cerullo | + | '''Instructor:''' TBDD |
| − | [[Image:Cerullof.jpg|150 px|right]]
| |
| − | | |
| − | Fabio helps customers around the globe by assessing the security of applications developed in-house or by third parties, defining policies and standards, implementing risk management initiatives, as well as providing training on the subject to developers, auditors, executives and security professionals.
| |
| − | | |
| − | As a member of the OWASP Fundation, Fabio is part of the Global Education Committee whose mission is to provide training and educational services to businesses, governments and educational institutions on application security, and has been appointed OWASP Ireland Chapter Leader since early 2010.
| |
| − | | |
| − | He holds a Msc in Computer Engineering from UCA and has been granted the CISSP & CSSLP certificates by (ISC)2.
| |
| | | | |
| | ===Course Language=== | | ===Course Language=== |
| Line 98: |
Line 62: |
| | Required Skill Level: Intermediate<br> | | Required Skill Level: Intermediate<br> |
| | | | |
| − | This course aims to provide the knowledge and resources required to improve the security of Java applications using the OWASP Enterprise Security API (ESAPI) Libraries. These libraries are designed to make it easier for developers to retrofit security into existing applications, and also serve as a solid foundation for new development.
| |
| − |
| |
| − | ===Course Contents===
| |
| − |
| |
| − | The participants, through theory and labs, will be able to identify critical vulnerabilities in web applications and implement the necessary corrective measures using the ESAPI libraries.
| |
| − |
| |
| − | Topics Include:<br>
| |
| − | <br>
| |
| − | - Introduction to ESAPI Architecture<br>
| |
| − | - Security Controls Overview<br>
| |
| − | - Authentication<br>
| |
| − | - Session Management<br>
| |
| − | - Access control<br>
| |
| − | - Input validation<br>
| |
| − | - Output encoding/escaping<br>
| |
| − | - Cryptography<br>
| |
| − | - Error handling and logging<br>
| |
| − | - Data Protection<br>
| |
| − | - HTTP security<br>
| |
| − |
| |
| − | The class is hands-on and will include labs. Attendees should have a laptop capable of running VMs. We will provide a VM at the beginning of the class.
| |
| − |
| |
| − | <br>
| |
| − |
| |
| − | == Advanced Vulnerability Research and Exploit Development ==
| |
| − | <span style="color:red">UPDATE: THIS TRAINING HAS BEEN CANCELLED DUE TO LOW REGISTRATION NUMBERS </span>
| |
| − |
| |
| − | '''Instructor: '''Gianni Gnesa, [http://www.ptrace-security.com Ptrace Security]<br>
| |
| − | [[Image:Owasp_training.jpg|frame|alt=Gianni Gnesa|right]]
| |
| − | Gianni Gnesa, BCS, MSCS, CEH, OSCP, OSEE, Network+, Linux+, is a security researcher and professional trainer at Ptrace Security, a Swiss-based company that offers specialized IT security services to customers worldwide. With several years of experience in vulnerability research, exploit development, and penetration testing, Gianni is an expert in exposing the vulnerabilities of complex commercial products and modern network infrastructures. In his spare time, Gianni conducts independent security research on kernel exploitation and rootkit detection.
| |
| − |
| |
| − |
| |
| − |
| |
| − |
| |
| − | ==Hands on Web Application Testing: Assessing Web Apps the OWASP way==
| |
| − | Instructor: Matt Tesauro
| |
| − | [[Image:Matt-Tesauro.png|frame|alt=Matt Tesauro|right|Matt Tesauro]]
| |
| − |
| |
| − |
| |
| − | Matt Tesauro has worked in web application development and security since 2000. He has worn many different hats, from developer to DBA to System Administrator to Penetration Tester. Matt also taught graduate and undergraduate classes on web application development and XML at Texas A&M University. Currently, he's focused on application security risk assessments at Praetorian. Outside work, he is the project lead for the OWASP Live CD / WTE, a member of the OWASP Foundation board, and part of the Austin OWASP chapter leadership. Matt Tesauro has a B.S. in Economics and a M.S in Management Information Systems from Texas A&M University. He is also has the CISSP, CEH (Certified Ethical Hacker), RHCE (Red Hat Certified Engineer), and Linux+ certifications.
| |
| − |
| |
| − |
| |
| − |
| |
| − | ===Course Abstract===
| |
| − | The goal of the training session is to teach students how to identify, test, and exploit web application vulnerabilities. The creator and project lead of the OWASP Live CD, now recoined OWASP WTE, will be the instructor for this course and WTE will be a major component of the class. Through lecture, demonstrations, and hands on labs, the session will cover the critical areas of web application security testing using the OWASP Testing Guide v3 as the framework and a custom version of OWASP WTE as the platform. Students will be introduced to a number of open source web security testing tools and provided with hands on labs to sharpen their skills and reinforce what they’ve learned. Students will also receive a complementary DVD containing the custom WTE training lab, a copy of the OWASP Testing Guide, handouts and cheat-sheets to use while testing plus several additional OWASP references. Demonstrations and labs will cover both common and esoteric web vulnerabilities and includes topics such as Cross-Site Scripting (XSS), SQL injection, CSRF and Ajax vulnerabilities. Students are encouraged to continue to use and share the custom WTE lab after the class to further hone their testing skills.
| |
| − |
| |
| − |
| |
| − | '''More details''' about this class including a detailed outline, are available '''[https://www.owasp.org/index.php/AppSecLatam2012/Training/Hands_On_Web_Application_Testing HERE]'''
| |
| − |
| |
| − | = Conference Schedule =
| |
| − | <font size=2pt>
| |
| − | {{:AppSecLatam2012/Schedule_Tuesday_Nov_20,_2012}}
| |
| − |
| |
| − |
| |
| − | {{:AppSecLatam2012/Schedule_Wednesday_Nov_21,_2012}}
| |
| − |
| |
| − | = Keynotes =
| |
| − | <font size=2pt>
| |
| − | == Jerry Hoff ==
| |
| − |
| |
| − | {| style="background-color: transparent"
| |
| − | |-
| |
| − | ! width="200" align="center" | <br>
| |
| − | ! width="1000" align="center" | <br>
| |
| − | |-
| |
| − | | align="center" | [[Image:Jerry.png|100px]]
| |
| − | | align="justify" | '''Building Security Into Frameworks: Who is doing it right'''. In this talk, Jerry Hoff, VP of the Static Code Analysis Division at WhiteHat Security, will discuss the importance of security controls in mobile and web frameworks. The talk features a tour through a spectrum of languages and frameworks. A tip of the hat will be given to frameworks and security controls that demonstrably mitigate vulnerabilities, resulting in more secure code. A wag of the finger will be given to frameworks that either lack essential security controls, or implement them improperly.
| |
| − |
| |
| − | Many of the OWASP Top 10 vulnerabilities and their corresponding security controls will be discussed. Participants will walk away with a better understanding of the security libraries available across a wide array of popular web technologies.
| |
| − |
| |
| − |
| |
| − | Jerry Hoff is the VP of the Static Code Analysis Division at WhiteHat Security. Prior to joining WhiteHat, he was a co-founder and managing partner at Infrared Security. Jerry has worked at a number of fortune ten financial firms, along with years of hands-on security consulting, where he specialized in manual code review, web application penetration testing, and architecture reviews. Jerry also has years of development and teaching experience. He taught for over seven years at Washington University's CAIT program, and the microcomputer program at University of Missouri in St. Louis. Jerry is the writer/producer of the popular OWASP Appsec Tutorial Series and the lead developer for the WebGoat.NET project.
| |
| − | |}
| |
| − | <br>
| |
| − |
| |
| − |
| |
| − | == Juliano Rizzo ==
| |
| − |
| |
| − | {| style="background-color: transparent"
| |
| − | |-
| |
| − | ! width="200" align="center" | <br>
| |
| − | ! width="1000" align="center" | <br>
| |
| − | |-
| |
| − | | align="center" |http://www.ekoparty.org//images/foto-juliano-rizzo.jpg
| |
| − | | align="justify" | '''From FUN to CRIME'''. In this talk, Juliano Rizzo will share his experience researching and implementing new practical
| |
| − | cryptographic attacks against web applications and protocols.
| |
| − |
| |
| − |
| |
| − | Juliano Rizzo has been involved in computer security for more than 12 years, working on vulnerability research, reverse engineering, source code review and development of high quality exploits for bugs of all classes. As a researcher he has published papers, security advisories and tools. His recent work includes the ASP.NET padding oracle exploit and the BEAST and CRIME attacks against the SSL/TLS protocol. Twitter: @julianor
| |
| − |
| |
| − | |}
| |
| − | <br>
| |
| − |
| |
| − | ==Cristian Borghello==
| |
| − | {| style="background-color: transparent"
| |
| − | |-
| |
| − | ! width="200" align="center" | <br>
| |
| − | ! width="1000" align="center" | <br>
| |
| − | |-
| |
| − | | align="center" | [[Image:Cristian-borghello-P.jpg|100px]]
| |
| − | | align="justify" | '''Tainted variables to find Potentially Vulnerable Functions (PVF)'''. We will study different ways to statically analyze the source code and
| |
| − | find vulnerabilities through input variables and functions that can
| |
| − | add potential vulnerabilities in web applications. Cristian F. Borghello, holds a degree in Information System,
| |
| − | developer, Certified Information Systems Security Professional (CISSP)
| |
| − | and Microsoft Security MVP (Most Valuable Professional).
| |
| − |
| |
| − | Currently Director of Segu-Info and independent consultant in
| |
| − | Information Security. He writes for various specialized media and
| |
| − | research independently on Computer Security and Information. Interest
| |
| − | in Computer Security and its research has led him to keep this site:
| |
| − | http://www.segu-info.com.ar/
| |
| − | Cristian is member of OWASP (Open Web Application Security Project)
| |
| − | Buenos Aires Chapter, ISSA (Information Systems Security Association),
| |
| − | CSA (Cloud Security Alliance) Argentina Chapter and ISC2 Argentina
| |
| − | Chapter.
| |
| − |
| |
| − | |}
| |
| − | <br>
| |
| − |
| |
| − | ==Hernán M. Racciatti==
| |
| − | {| style="background-color: transparent"
| |
| − | |-
| |
| − | ! width="200" align="center" | <br>
| |
| − | ! width="1000" align="center" | <br>
| |
| − | |-
| |
| − | | align="center" | [[Image:Photo_Hernan_Racciatti.jpg|100px]]
| |
| − | | align="justify" | '''The security of your company will be compromised'''. Hernan M. Racciatti has 20 years of experience in Information Technology, having dedicated most of his careers in areas related to Information Security.
| |
| − |
| |
| − | Currently serves as Director of Security at SIClabs, advising private companies and public agencies, leading Penetration Test, Security Application Assessment, Code Source Review, pursuing researches about information security, teaching and offering seminars and technical lectures at conferences of national and international level related to his field.
| |
| − |
| |
| − | Among his contributions to the community, should be noted: active participation as a collaborator in some ISECOM´s project (OSSTMM-Open Source Security Testing Methodology Manual and Hacker High School), OISSG (ISSAF – Information Systems Security Assessment Framework), the development of small tools designed to secure information systems and several papers, articles and technical documents written for digital and print publications whit national and international circulation.
| |
| − |
| |
| − | During last year, he found and reported vulnerability in major commercial products.
| |
| − |
| |
| − | Hernan Marcelo Racciatti is member of the Core Team at ISECOM (Institute for Security and Open Methodologies), ISSAF Key Contributor at OISSG (Open Information System Security Group), President of CSA (Cloud Security Alliance) Argentina Chapter, Executive Committee Member of the ONG Argentina Cibersegura, ISSA (Information Systems Security Association) and OWASP (Open Web Application Security Project) Buenos Aires Chapter Member.
| |
| − |
| |
| − | Learn more about Hernan at [http://www.hernanracciatti.com.ar/ http://www.hernanracciatti.com.ar/]
| |
| − | |}
| |
| − | <br>
| |
| − |
| |
| − | = Speakers =
| |
| − | <font size=2pt>
| |
| − |
| |
| − | These are the selected presentations and are subject to confirmation from presenters.
| |
| − |
| |
| − | {| style="background-color: transparent"
| |
| − | |-
| |
| − | | width="300" align="center" | '''Name & Title'''
| |
| − | | width="1000" align="justify" | '''Bio'''
| |
| − | |-
| |
| − | |- <br/> || <br/>
| |
| − | |-
| |
| − | |'''Assessing Application Security Risk''', ''Alex Bauert'' || Application Security Manager, Cargill. 20+ years in IT; localized software, sysadm, and app sec among some other roles. I have worked with application security at a software company, a large bank and currently Cargill. I am also active in the Minnesota OWASP chapter. In my free time I am a youth soccer coach.
| |
| − | |-
| |
| − | |'''Malware en dispositivos móviles''', ''Sebastian Bortnik'' || Sebastián Bortnik es CISM y el Gerente de Educación y Servicios de ESET para Latinoamérica.
| |
| − | |-
| |
| − | |'''Password Security Policies - Lessons learned from recent password leaks''', ''Flavio de Cristofaro'' || Flavio is the VP of Engineering for Professional Products at Core Securiry. His primary focus is on building and evolving CORE Impact Pro as well as introducing new professional products into the marketplace.
| |
| − | He has over 10 years of experience in penetration testing and IT security, having led onsite and remote penetration testing engagements for several clients worldwide. Prior to joining the Engineering team, he led the CORE Security Consulting Services practice where he coordinated leading-edge penetration testing services for multiple global organizations. Prior to joining CORE, he worked at Deloitte leading one of the global penetration testing centers located in Argentina. He also taught at ITBA University in Argentina until 2004.
| |
| − | |-
| |
| − | |'''OWASP Mobile Top 10''', ''Mauro Flores'' || Mauro Flores tiene más de 15 años de experiencia en Seguridad de la Información. Ha participado en proyectos de diseño, especificación y desarrollo de aplicaciones de seguridad para diferentes empresas de Uruguay y el exterior, incluyendo trabajos de reserarch & Develop en seguridad para empresas de UK y USA. Ha realizado más de 30 test de penetración , diversos trabajos de análisis forense y apoyado a diferentes organizaciones privadas y públicas a la mejora de la seguridad de sus sistemas así como a la mejora de la gestión de la seguridad alineado a las normativas internacionales (SGSI, PCI, etc).
| |
| − |
| |
| − | Actualmente se desempeña como Gerente de la línea de Seguridad de la Información de Deloitte Uruguay. Además, es el Chapter Leader del capitulo Uruguay del OWASP y miembro del Global Industry Committee de esta organización. También es miembro activo del Anti-Phishing Working Group (APWG).
| |
| − | |-
| |
| − | |'''Resource Certification: Implementation Challenges''', ''Dario Gomez'' || Dario Gomez was formed in 2010 in computer sciences at the University ORT Uruguay. Currently he's working for 4 years as a software developer at Internet Address Registry for Latin America and the Caribbean - LACNIC, where one of main responsibilities is the development of the resources certification system of organization (http://lacnic.net/en/rpki/).
| |
| − | Previously, he worked at the help desk and maintenance of servers and networks in the British Hospital of Uruguay.
| |
| − | |-
| |
| − | |'''Presentation Of The OWASP ODZ Multi CMS Scanner''', ''Mennouchi Islam'' || Mennouchi Islam Azeddine CEO and security consultant at Way4Com Owasp Algeria chapter leader and OWASP ODZ Multi CMS Scanner project leader.
| |
| − | |-
| |
| − | |'''A real ZAP story''', ''Mateo Martínez'' || With more than 10 years of experience in IT & Security strategy, Business Continuity Management,ISO 27001, CobIT and ITIL he has developed Security Projects based in Dubai, Chicago, Montevideo and Buenos Aires.
| |
| − | Information Security Manager in global companies and currently working at McAfee Argentina in a presales role. CISSP, ITIL & MCP certified.
| |
| − |
| |
| − | |-
| |
| − | |'''Critérios para Institucionalizar Segurança em Processos de Desenvolvimento de Software''', ''Francisco Nunes'' || Graduated in Computer Science at Universidade Estadual do Ceará (2001), with a graduation study period in Informatique de Gestion at Université du Québec à Chicoutimi (1999). He has a Master's in Computer Science from Universidade de Fortaleza (2007). He has experience in Information Security and Software Engineering, acting on the following subjects: information and software security, business continuity, security engineering, and software life cycle process improvement. He is CISM and CSSLP certified.
| |
| − | |-
| |
| − | |'''Understanding HTML5 security''', ''Andres Riancho'' || Andrés Riancho is an application security expert that currently leads the community driven, Open Source, w3af project and provides in-depth Web Application Penetration Testing services to companies around the world.
| |
| − |
| |
| − | In the research field, he discovered critical vulnerabilities in IPS appliances from 3com and ISS; and contributed with SAP research performed at his former employer.
| |
| − |
| |
| − | His main focus has always been the Web Application Security field, in which he developed w3af, a Web Application Attack and Audit Framework used extensively by penetration testers and security consultants. Andrés has spoken and hold trainings at many security conferences around the globe, like PHDays (Moscow), SecTor (Toronto), OWASP (Poland), CONFidence (Poland), OWASP World C0n (USA), CanSecWest (Canada), T2 (Finland) and ekoparty (Buenos Aires).
| |
| − |
| |
| − | Andrés founded Bonsai in 2009 in order to further research into automated Web Application Vulnerability detection and exploitation.
| |
| − |
| |
| − | Specialties: Web Application Security, Python, IPS device evasion, Networking, Information security research in general, Software development, Agile, Scrum, Product Owner.
| |
| − | |-
| |
| − | |'''Don't try to block out the sun with your fingers!: Information harvesting with Test-driven development tools and understanding how to avoid it''', ''Nicolas Rodriguez'' || I'm a Senior Security Consultant at Core Security (http://www.coresecurity.com). I have 22 years of programming experience (C/C++, Assembler, Pascal, Clipper, Visual Basic, C#, Visual Basic.NET, Lisp, Python, Ruby and Perl among others), 10 years as a Network Administrator (Linux, Unix and Windows physical and virtual servers) and for the last 6 years I've been working as a Security Consultant doing mostly Network and Applications Penetration Tests, Source Code Audits and Client-Side Penetration Tests.
| |
| − | |-
| |
| − | |'''Templates to Derive Security Metric based on Attack Patterns''', ''Raja Sekhar'' || Professor Department of Computer Science & Engineering KL University Andhra Pradesh, India. Working in the Academic field for the past 17 years. Interested to contribute in the area of security metrics and cryptography. Developed a security metric program based on Attack Patterns.
| |
| − | |-
| |
| − | |'''Reducing Web Application Attack Surface with a HMAC based protocol''', ''Breno Silva'' || Breno is a computer scientist with over 9 years experience in Information Security, experienced with a wide range of software development techniques and languages, security systems and network technologies. Breno brings a research history publishing articles in academic conferences like IEEE WIFS, IEEE ICMLC, IEEE INDIN, World Academy of Science, as well industry related conferences like OWASP AppSec Latam, OWASP AppSec Research and Ph-Neutral, involving areas as algorithm design for network anomaly detection mechanisms in high-speed networks, application security and malicious code detection. He was a member of Suricata IPS developer team (next-generation IPS funded by US-Homeland Security). Breno is currently a Security Researcher at Trustwave SpiderLabs Research team and maintainer of Apache ModSecurity.
| |
| − | |-
| |
| − | |'''Using PASTA as a core ingredient to web application threat modeling''', ''Tony UcedaVelez'' || Tony UcedaVelez, CRISC, CISM, CISA, GIAC has more than 14 years of hands-on security and technology experience across government, healthcare, financial, education, and utility sectors. Tony founded VerSprite with the premise of redefining security services to a point that it reflects a hybrid and balanced approach in understanding client needs. Tony has consulted for numerous Fortune 500 organizations as well as large government entities within the areas of application security, security risk management, network security, and governance. Before VerSprite, Tony was the Sr. Director of Policy and Risk Management for a major Fortune 50 information service bureau. Tony's background in IT operations and software development, coupled with security operations, allows him to lead VerSprite with the mission of providing tailored, strategic solutions to its client base. Tony is a frequent speaker/ writer at ISACA, OWASP, and other information security forums around the world and is currently managing the Atlanta OWASP Chapter. He is also currently co-writing a book on application threat modeling via Wiley Life Sciences and has co-developed a patent pending methodology for risk based threat models. Tony is a graduate from Cornell University.
| |
| − | |-
| |
| − | |'''How dynamic have been static checking?''', ''Felipe Zipitria'' || Felipe Zipitria has a Master Degree in Computer Science from PEDECIBA Informática and his thesis was in the Computer Security field. He is working as a Senior System Administrator and teaching since 1998 at the Computer Science department of the Faculty of Engineering - University of the Republic. From 2006 he joined the Computer Security Group, and has been doing research and teaching Computer Security foundations for pre-graduate students, and Application Security for professionals and as a post-graduate course. He has been using OWASP tools and documentation for its courses since the first course for pre-graduates. As a Senior System Administrator he has specialized in Web Security, using Web Application Firewalls, Apache Web Server and Apache Tomcat, Virtualization, and Clustering. He has made Security Analysis for local enterprises, and several Penetration Tests and Source Code Analysis.
| |
| − |
| |
| − | |}
| |
| | | | |
| | | | |
| Line 298: |
Line 67: |
| | = Venue = | | = Venue = |
| | <font size=2pt> | | <font size=2pt> |
| − | AppSec Latam 2012 will be held in downtown Montevideo, Uruguay at the [http://www.antel.com.uy/antel/institucional/nuestra-empresa/complejo-torre Antel National Telco Company]. Directions are available through: [https://maps.google.com/maps?q=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&hl=es-419&ll=-34.899448,-56.179104&spn=0.098412,0.181789&geocode=FaOW6_0dt4qm_A&hnear=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&t=m&z=13 Google Maps] | + | AppSec Rio de la Plata 2015 will be held in downtown Montevideo, Uruguay at the [http://www.antel.com.uy/antel/institucional/nuestra-empresa/complejo-torre Antel National Telco Company]. Directions are available through: [https://maps.google.com/maps?q=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&hl=es-419&ll=-34.899448,-56.179104&spn=0.098412,0.181789&geocode=FaOW6_0dt4qm_A&hnear=Auditorio+Torre+de+las+Telecomunicaciones,+Guatemala+1075,+Montevideo+11800,+Uruguay&t=m&z=13 Google Maps] |
| | <br> | | <br> |
| | <br> | | <br> |
| Line 315: |
Line 84: |
| | <br> | | <br> |
| | <br> | | <br> |
| − | <br> | + | <br>-- |
| | '''Inside the Auditorium (left) and Interactive Room (right):'''<br> | | '''Inside the Auditorium (left) and Interactive Room (right):'''<br> |
| | | | |
| Line 326: |
Line 95: |
| | == Online Registration == | | == Online Registration == |
| | | | |
| − | Registration is now closed. | + | Registration is now open! |
| | | | |
| | | | |
| Line 332: |
Line 101: |
| | '''Access to conference:''' | | '''Access to conference:''' |
| | | | |
| − | * Before October 15th: 3200.00 UYU (approx. 150.00 USD) | + | *Before del 30th september 100 USD |
| − | * Before Nov 5th: 4250.00 UYU (approx. 200.00 USD) | + | *Before 31st october 200 USD |
| − | * After Nov 5st: 5300.00 UYU (approx. 250.00 USD) | + | *After 1st november 300 USD |
| − | | |
| − | | |
| − | '''Training'''
| |
| − | | |
| − | * Two days: 17000.00 UYU (approx. 800.00 USD)
| |
| − | | |
| − | | |
| − | '''Discounts'''
| |
| | | | |
| − | * OWASP Member: 50.00 USD (Note: This discount is equal to the cost of becoming an OWASP paid Member.) | + | -- Discounts -- |
| − | * Student: 1600.00 UYU (approx. 75.00 USD). Note: student ID or other proof of current student status is required. | + | *OWASP Members 50.00 USD |
| − | * Students are eligible for 20% discount off training fees, making the total training cost for 2 days $640.00 USD. To take advantage of this offer, enter the discount code STUDENT_TRAINING at checkout.
| + | *Students: 75.00 USD Note: student ID or other proof of current student status is required |
| − | | |
| − |
| |
| | | | |
| | + | '''Trainings''' |
| | + | *1-Day 500.00 USD |
| | + | *2 Days 800.00 USD |
| | | | |
| | | | |
| Line 355: |
Line 117: |
| | = Sponsoring = | | = Sponsoring = |
| | <font size=2pt> | | <font size=2pt> |
| − | We are looking for sponsors for 2012 edition of Global AppSec Latin America. | + | We are looking for sponsors for 2015 edition of AppSec Rio de la Plata |
| | | | |
| | | | |
| − | If you are interested to sponsor Global AppSec Latin America 2012, please contact the conference team: [mailto:appseclatam2012@owasp.org appseclatam2012@owasp.org] | + | If you are interested to sponsor AppSec Rio de la Plata 2015, please contact [kelly.santalucia@owasp.org Kelly Santalucia] |
| | | | |
| | | | |
| − | To find out more about the different sponsorship opportunities please check the document below: <br> [https://www.owasp.org/images/3/37/AppSec_LATAM_2012_Sponsorship.pdf OWASP AppSec Latam 2012 Sponsorship Options - English] | + | To find out more about the different sponsorship opportunities please check the document below: <br> [http://appsecriodelaplata.org/2015/wp-content/uploads/2014/11/OWASPAppSecRiodelaPlata2015-Sponsorship.pdf OWASP AppSec Rio de la Plata Sonsorship Options - English] |
| | | | |
| | | | |