This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "CISO AppSec Guide: Quick Reference to OWASP Guides & Projects"
From OWASP
(→Appendix I-D: Quick Reference to OWASP Guides & Projects: Added content to table) |
m (→Appendix I-D: Quick Reference to OWASP Guides & Projects: Bullets updated) |
||
| Line 19: | Line 19: | ||
| Standards and Policies | | Standards and Policies | ||
| Part I - Section 4.2 "Application Security Standards, Policies and Compliance" | | Part I - Section 4.2 "Application Security Standards, Policies and Compliance" | ||
| − | | *Development Guide - Policy Frameworks | + | | |
| + | * Development Guide - Policy Frameworks | ||
* CLASP - Identify Global Security Policy | * CLASP - Identify Global Security Policy | ||
* SAMM - Policy & Compliance | * SAMM - Policy & Compliance | ||
| Line 27: | Line 28: | ||
| Governance | | Governance | ||
| Part III - Section 6.2.1 "Application Security Governance, Risk and Compliance" | | Part III - Section 6.2.1 "Application Security Governance, Risk and Compliance" | ||
| − | |* SAMM - Governance | + | | |
| + | * SAMM - Governance | ||
|- | |- | ||
| Develop and implement software security development and security testing processes | | Develop and implement software security development and security testing processes | ||
| Line 34: | Line 36: | ||
Part III - Section 6.4 "How to Choose the Right OWASP projects and Tools for Your Organization" | Part III - Section 6.4 "How to Choose the Right OWASP projects and Tools for Your Organization" | ||
| − | | * Development Guide | + | | |
| + | * Development Guide | ||
* Code Review Guide | * Code Review Guide | ||
* Secure Coding Practices Checklist | * Secure Coding Practices Checklist | ||
| Line 46: | Line 49: | ||
| Risk Strategy | | Risk Strategy | ||
| Part I - Section 4.3 "Risk Assessment and Measurement" | | Part I - Section 4.3 "Risk Assessment and Measurement" | ||
| − | | * SAMM - Strategy & Metrics | + | | |
| + | * SAMM - Strategy & Metrics | ||
|- | |- | ||
| Work with executive management, business managers and internal audit and legal counsel to define application security requirements that can be verified and audited | | Work with executive management, business managers and internal audit and legal counsel to define application security requirements that can be verified and audited | ||
| Line 53: | Line 57: | ||
Part III - Section 6.2 "Addressing CISO's Application Security Functions" | Part III - Section 6.2 "Addressing CISO's Application Security Functions" | ||
| − | | * Application Security Verification Standards - All | + | | |
| + | * Application Security Verification Standards - All | ||
* CLASP - Document Security-Relevant Requirements | * CLASP - Document Security-Relevant Requirements | ||
* SAMM - Security Requirements | * SAMM - Security Requirements | ||
| Line 63: | Line 68: | ||
| Risk Metrics & Monitoring | | Risk Metrics & Monitoring | ||
| Part IV - Section 7 "Selection of Metrics for Managing Risks & Application Security Investments" | | Part IV - Section 7 "Selection of Metrics for Managing Risks & Application Security Investments" | ||
| − | | * Applications Security Metrics - All | + | | |
| + | * Applications Security Metrics - All | ||
* CLASP - Define and Monitor Metrics | * CLASP - Define and Monitor Metrics | ||
|- | |- | ||
| Line 73: | Line 79: | ||
Part III Section 6 "Selection of Application Security Processes" | Part III Section 6 "Selection of Application Security Processes" | ||
| − | | OWASP Top Ten Risks | + | | |
| + | * OWASP Top Ten Risks | ||
* Testing Guide - Threat Modelling | * Testing Guide - Threat Modelling | ||
* Development Guide - Threat Risk Modelling | * Development Guide - Threat Risk Modelling | ||
| Line 82: | Line 89: | ||
|Procurement | |Procurement | ||
| Part III - Section 6.3.2 "Integrating Risk Management as part of the SDLC" | | Part III - Section 6.3.2 "Integrating Risk Management as part of the SDLC" | ||
| − | | * Legal - Secure Software Contract Annex | + | | |
| + | * Legal - Secure Software Contract Annex | ||
* Tools projects | * Tools projects | ||
|- | |- | ||
| Line 90: | Line 98: | ||
Part IV Section 6.3.4 "Software Assurance Maturity Models" | Part IV Section 6.3.4 "Software Assurance Maturity Models" | ||
| − | | * Education | + | | |
| + | * Education | ||
* Training Modules / Conference Videos | * Training Modules / Conference Videos | ||
* Application Security FAQ | * Application Security FAQ | ||
| Line 103: | Line 112: | ||
| Incident Response | | Incident Response | ||
| Part IV Section 6.2 "Addressing CISO's Application Security Functions" | | Part IV Section 6.2 "Addressing CISO's Application Security Functions" | ||
| − | | * .HET Incident Response | + | | |
| + | * .HET Incident Response | ||
* CLASP - Manage Security Issue Disclosure Process | * CLASP - Manage Security Issue Disclosure Process | ||
|} | |} | ||
Revision as of 20:58, 29 September 2013
< Back to the Application Security Guide For CISOs
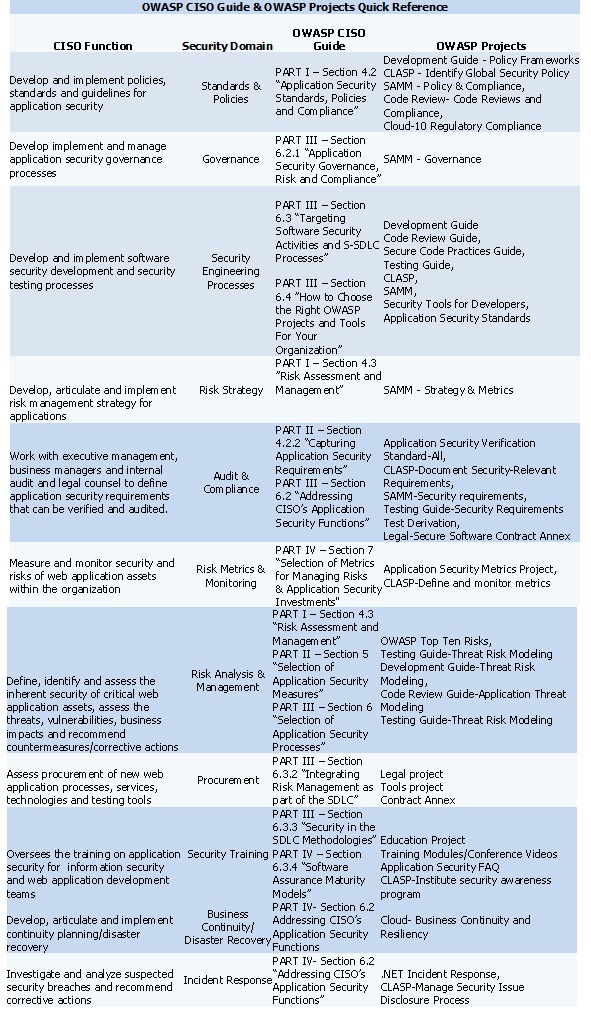
Appendix I-D: Quick Reference to OWASP Guides & Projects
This quick reference maps typical CISO's functions and information security domains to different sections of the OWASP' CISO Guide and relevant OWASP projects.
To do:
- Check cross-references back to other parts of guie and add links/anchors
- Check for other OWASP projects
| CISO Function | Security Domain | OWASP CISO Guide | OWASP Projects |
|---|---|---|---|
| Develop and implement policies, standards and guidelines for application security | Standards and Policies | Part I - Section 4.2 "Application Security Standards, Policies and Compliance" |
|
| Develop, implement and manage application security governance | Governance | Part III - Section 6.2.1 "Application Security Governance, Risk and Compliance" |
|
| Develop and implement software security development and security testing processes | Security Engineering Processes | Part III - Section 6.3 "Targeting Software Security Activities and S-SDLC processes"
Part III - Section 6.4 "How to Choose the Right OWASP projects and Tools for Your Organization" |
|
| Develop, articulate and implement a risk management strategy for applications | Risk Strategy | Part I - Section 4.3 "Risk Assessment and Measurement" |
|
| Work with executive management, business managers and internal audit and legal counsel to define application security requirements that can be verified and audited | Audit & Compliance | Part II - Section 4.2.2 "Capturing Application Security Requirements"
Part III - Section 6.2 "Addressing CISO's Application Security Functions" |
|
| Measure and monitor security and risks of application assets within the organization | Risk Metrics & Monitoring | Part IV - Section 7 "Selection of Metrics for Managing Risks & Application Security Investments" |
|
| Define, identify and assess the inherent security of critical application assets, assess the threats, vulnerabilities, business impacts and recommend countermeasurers/corrective actions | Risk Analysis & Management | Part I - Section 4.3 "Risk Assessment and Management"
Part II Section 5 "Selection of Application Security Measures" Part III Section 6 "Selection of Application Security Processes" |
|
| Assess procurement of new application processes, services, technologies and security tools | Procurement | Part III - Section 6.3.2 "Integrating Risk Management as part of the SDLC" |
|
| Oversee the training on application security for development, operational and information security teams | Security Training | Part III Section 6.3.3 "Security in SDLC Methodologies"
Part IV Section 6.3.4 "Software Assurance Maturity Models" |
|
| Develop, articulate and implement continuity planning/disaster recovery | Business Continuity / Disaster Recovery | Part IV Section 6.2 "Addressing CISO's Application Security Functions" | |
| Investigate and analyse suspected and actual application security incidents and recommend corrective actions | Incident Response | Part IV Section 6.2 "Addressing CISO's Application Security Functions" |
|