This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Security Integration System"
MB netblue4 (talk | contribs) (→Process integrity and point in time in the SDLC) |
MB netblue4 (talk | contribs) (→What is the Secure code assurance tool (SCAT)) |
||
| (41 intermediate revisions by the same user not shown) | |||
| Line 6: | Line 6: | ||
==What is the Secure code assurance tool (SCAT)== | ==What is the Secure code assurance tool (SCAT)== | ||
<h1><b>What is the SCAT</b></h1> | <h1><b>What is the SCAT</b></h1> | ||
| + | |||
| + | [https://www.linkedin.com/pulse/secure-code-assurance-tool-scat-version-20-michael-bergman/ For more information on the <b>why</b> behind the SCAT, read my linkedIn Article here] | ||
==What is the SCAT== | ==What is the SCAT== | ||
| Line 27: | Line 29: | ||
</ul> | </ul> | ||
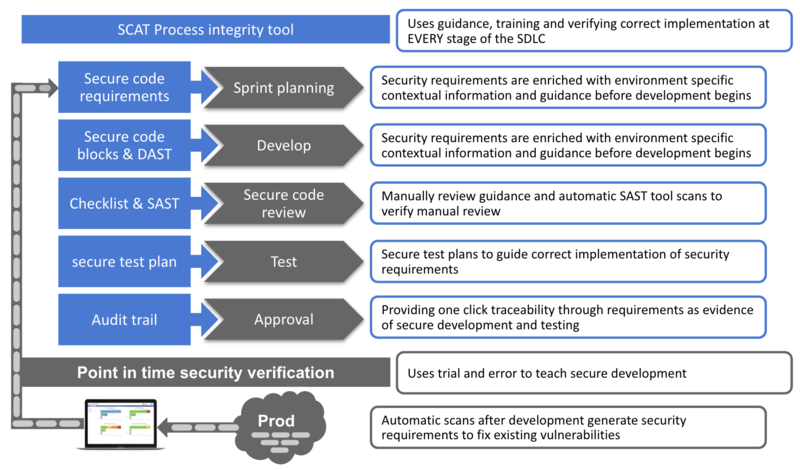
| − | ==Process integrity and point in time in the SDLC== | + | ==Process integrity and point in time tools: How they work in the SDLC== |
[[File:Process integrity VS point in time without check.png|800px|center|Process integrity VS point in time without check]] | [[File:Process integrity VS point in time without check.png|800px|center|Process integrity VS point in time without check]] | ||
| − | <h1><b> | + | <h1><b>Technical Description</b></h1> |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | + | ==Without further complicating development environment== | |
| − | |||
| − | |||
| − | |||
| − | == | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
<ul> | <ul> | ||
| − | <li> | + | <li>SCAT is a simple 5 screen MVC, C# web application with a small footprint that can be deployed without further complicating development environment |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| + | <li>Integrates with Jira and runs ZAP and SonarQube in docker containers | ||
| − | < | + | <li>SCAT is part of three domains to consider when securing software development. <em>I've detailed the other domains in an article that will be published in the Nov/Dec issue of the ISC2 magazine, I will add a link here after publication.</em> |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
<h1><b>See how developers use SCAT</b></h1> | <h1><b>See how developers use SCAT</b></h1> | ||
| Line 232: | Line 181: | ||
<br> | <br> | ||
| − | <h1> | + | <h1>Project information</h1> |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
==Licensing== | ==Licensing== | ||
This program is free software: you can redistribute it and/or modify it under the terms of the [http://www.gnu.org/licenses/agpl-3.0.html link GNU Affero General Public License 3.0] as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version. | This program is free software: you can redistribute it and/or modify it under the terms of the [http://www.gnu.org/licenses/agpl-3.0.html link GNU Affero General Public License 3.0] as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version. | ||
| + | |||
| + | == Interested in contributing== | ||
| + | [https://www.linkedin.com/in/michael-bergman-99826212a/ Please send a connect request with subject SCAT] | ||
== Project Resources == | == Project Resources == | ||
| Line 318: | Line 196: | ||
== Project Leader == | == Project Leader == | ||
| − | [ | + | [https://www.linkedin.com/in/michael-bergman-99826212a/ Michael Bergman LinkedIn] |
==Classifications== | ==Classifications== | ||
Latest revision as of 18:33, 14 October 2019
What is the Secure code assurance tool (SCAT)
For more information on the why behind the SCAT, read my linkedIn Article here What is the SCAT
Process integrity and point in time tools: How they work in the SDLCWithout further complicating development environment
See below how the Secure code assurance tool integrates security into software development phases Sprint planning phaseObjective: Ensures security requirements are understood
Development phaseObjective: Ensure correct implementation of security requirements
Secure code review phaseObjective: Ensure correct implementation of security requirements
Testing phaseObjective: Ensure valid security testing
Approval phaseObjective: Streamline the approval and audit process
Risk managementObjective: Enable risk managers to prioritise, plan and monitor mitigation efforts
When developing secure software we need to consider both standard secure code and client specific architectural requirements Standard secure code requirements
Client specific architectural requirements
LicensingThis program is free software: you can redistribute it and/or modify it under the terms of the link GNU Affero General Public License 3.0 as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version. Interested in contributingPlease send a connect request with subject SCAT Project Resources[Installation Package] [Source Code] Project LeaderClassifications
| ||||||