This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Cyber Defense Matrix"
(→Presentation) (Tag: Visual edit) |
m (→Project Leader: Removed defunct mailing lists. Replaced links to point to LinkedIn page that people can follow instead for updates.) (Tag: Visual edit) |
||
| (19 intermediate revisions by 3 users not shown) | |||
| Line 1: | Line 1: | ||
| − | =Main= | + | = Main = |
| + | {{#widget:PayPal Donation | ||
| + | |target=_blank | ||
| + | |budget=OWASP_Cyber_Defense_Matrix | ||
| + | }} | ||
| + | |||
<!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | <!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | ||
<div style="width:100%;height:160px;border:0,margin:0;overflow: hidden;">[[File:OWASP_Project_Header.jpg|link=]]</div> | <div style="width:100%;height:160px;border:0,margin:0;overflow: hidden;">[[File:OWASP_Project_Header.jpg|link=]]</div> | ||
| − | |||
<!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | <!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | ||
{| style="padding: 0;margin:0;margin-top:10px;text-align:left;" |- | {| style="padding: 0;margin:0;margin-top:10px;text-align:left;" |- | ||
| valign="top" style="border-right: 1px dotted gray;padding-right:25px;" | | | valign="top" style="border-right: 1px dotted gray;padding-right:25px;" | | ||
| − | == | + | ==Introduction to the Cyber Defense Matrix== |
| − | + | Imagine going into a grocery store to shop for Thanksgiving dinner, but instead of seeing nice, orderly aisles, you see a massive pile of food in the middle of the grocery store. Finding the ingredients that you need to make dinner is going to be extremely hard because there’s no organizational system helping you understand where things are. The disorganization makes it very difficult to find what you need and compare competing products. | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | + | The cybersecurity vendor marketplace is like this disorganized grocery store. A proof of this assertion can be seen by looking at the vendor hall at any major security conference. The cacophony of sounds from vendors hawking their wares, the confusing language of the vendor’s marketecture, and the lack of any semblance of organization (aside from biggest to smallest) does not help buyers understand what they need or where to find it. | |
| − | |||
| − | |||
| − | + | Because the cybersecurity community does not use consistent terminology to describe what we need, there is much confusion about what many vendor products actually do. Instead of a clear articulation of a product's capabilities, we are bombarded with overused, trendy jargon that usually leaves us wondering if the product can really solve any of our woes. Some organizations even organize themselves according to the jargon. We need to stop letting marketing pitches dictate our terminology and not lose sight of the more bland descriptors that actually tell us what something does. | |
| − | + | The Cyber Defense Matrix helps us understand what we need organized through a logical construct so that when we go into the security vendor marketplace, we can quickly discern what products solve what problems and be informed on what is the core function of a given product. In addition, the Cyber Defense Matrix provides a mechanism to ensure that we have capabilities across the entire spectrum of options to help secure our environments. | |
| − | + | Although the Cyber Defense Matrix was initially created to help organize security technologies, many other use cases have been discovered to help build, manage, and operate a security program. This project intends to capture these use cases and their implementations to help security practitioners mature their security programs. | |
| − | == | + | ==Structure of the Cyber Defense Matrix== |
| − | + | The basic construct of the Cyber Defense Matrix starts with two dimensions. The first dimension captures the five operational functions of the NIST Cybersecurity Framework: | |
| + | {| class="wikitable" | ||
| + | !IDENTIFY | ||
| + | !PROTECT | ||
| + | !DETECT | ||
| + | !RESPOND | ||
| + | !RECOVER | ||
| + | |} | ||
| + | The second dimension captures five assets classes that we try to secure: | ||
| + | {| class="wikitable" | ||
| + | !DEVICES | ||
| + | |- | ||
| + | !APPLICATIONS | ||
| + | |- | ||
| + | !NETWORKS | ||
| + | |- | ||
| + | !DATA | ||
| + | |- | ||
| + | !USERS | ||
| + | |} | ||
| + | When these two dimensions are put into a grid, we arrive at with a five-by-five matrix that we call the “Cyber Defense Matrix.” | ||
| + | <div style="width:100%;border:0,margin:0;">[[File:Cyber Defense Matrix.png|center]]</div> | ||
| − | + | There is one more important piece of this matrix. At bottom of the grid, we show a continuum that characterizes the degree of dependency on technology, people, and process as we progress through the five operational functions of the NIST Cybersecurity Framework. TECHNOLOGY plays a much greater role in IDENTIFY and PROTECT. As we move to DETECT, RESPOND, and RECOVER, our dependency on TECHNOLOGY diminishes and our dependency on PEOPLE grows. Throughout all five operational functions, there's a consistent level of dependency on PROCESS. This continuum helps us understand where we might have imbalances in our reliance on PEOPLE, PROCESS, and TECHNOLOGY when trying to tackle our cybersecurity challenges. | |
| − | + | We believe that this matrix is a realistic model describes a broad range of cybersecurity practices. In this website, you will find several insights on the Cyber Defense Matrix and examples of how to leverage it to address the challenges that we face in cybersecurity. | |
| − | + | If you discover a new use of the Cyber Defense Matrix, we would love to hear about it. Likewise, if you find a problem with the matrix in that it doesn't seem to properly describe something that we do in cybersecurity, please point that out, and we'll either adjust the matrix or clarify how that perceived discrepancy can be addressed or explained through the matrix. | |
| − | |||
| − | |||
<!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | <!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | ||
| valign="top" style="padding-left:25px;width:200px;border-right: 1px dotted gray;padding-right:25px;" | | | valign="top" style="padding-left:25px;width:200px;border-right: 1px dotted gray;padding-right:25px;" | | ||
| − | == | + | == Presentations and Other Media == |
| − | + | [https://bit.ly/cyberdefensematrix Cyber Defense Matrix Presentation at RSA Conference 2016] | |
| − | + | [https://bit.ly/cyberdefensematrixreloaded Cyber Defense Matrix Reloaded Presentation at RSA Conference 2019] | |
| − | == | + | == Project Leader == |
| − | + | * [https://twitter.com/sounilyu Sounil Yu (@sounilyu)] | |
| − | |||
| − | + | == FAQs == | |
| − | * | + | * TBD |
| + | == Things To Do == | ||
| + | * Document structure of the Cyber Defense Matrix | ||
| + | * Map vendors to the Cyber Defense Matrix | ||
| + | * Map NIST NICE NCWF skillsets to the Cyber Defense Matrix | ||
| + | * Define attributes that can support measurement of efficacy of capability | ||
| + | * Define Design Patterns and Business Constraints aligned against the Cyber Defense Matrix | ||
| + | * Capture anecdotal and empirical measurements of capability degradation rates | ||
| + | * Incorporate and document new use cases as they are discovered | ||
== Related Projects == | == Related Projects == | ||
| + | * TBD | ||
| − | + | == Licensing == | |
| − | + | The Cyber Defense Matrix, originally created by Sounil Yu, is licensed under the http://creativecommons.org/licenses/by-sa/4.0/ Creative Commons Attribution-ShareAlike 4.0 license, so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one. | |
| − | == | ||
| − | |||
| − | |||
<!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | <!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | ||
| valign="top" style="padding-left:25px;width:200px;" | | | valign="top" style="padding-left:25px;width:200px;" | | ||
| − | == | + | == MAILING LIST == |
| − | * | + | * [https://www.linkedin.com/company/cyber-defense-matrix/ CLICK TO JOIN] |
== News and Events == | == News and Events == | ||
| − | * [01 May 2017] Project | + | * [01 May 2017] Project created |
| − | + | * [20 April 2019] Added links to 2019 briefing at RSA | |
| − | |||
| − | |||
| − | |||
==Classifications== | ==Classifications== | ||
| Line 92: | Line 111: | ||
|} | |} | ||
| − | =FAQs | + | = FAQs = |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | + | == How can I participate in your project? == | |
| − | + | Everyone is invited to collaborate on this project. Contact the Project Leaders. The project needs different skills and expertise and different times during its development. Currently, we are looking for help in the following areas: | |
| − | |||
| − | |||
| − | |||
| − | + | * Documenting new use cases | |
| + | * Creating a system to capture everything that is mapped to the Cyber Defense Matrix. This includes: | ||
| + | ** Mapping of vendors | ||
| + | ** Mapping of NIST NICE NCWF skillsets | ||
| + | ** Mapping of measurements and metrics | ||
| + | = Events and Opportunities to Get Involved = | ||
<!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | <!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | ||
Latest revision as of 02:48, 11 October 2019
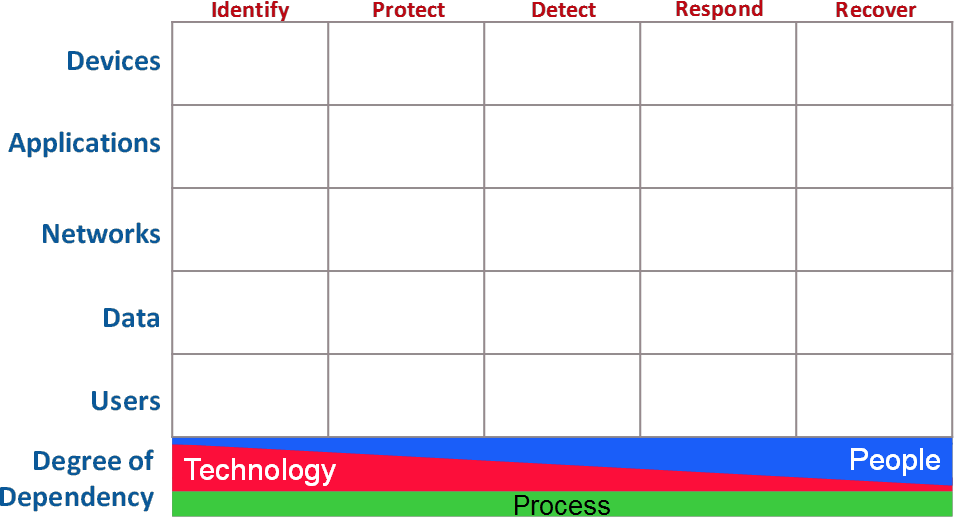
Introduction to the Cyber Defense MatrixImagine going into a grocery store to shop for Thanksgiving dinner, but instead of seeing nice, orderly aisles, you see a massive pile of food in the middle of the grocery store. Finding the ingredients that you need to make dinner is going to be extremely hard because there’s no organizational system helping you understand where things are. The disorganization makes it very difficult to find what you need and compare competing products. The cybersecurity vendor marketplace is like this disorganized grocery store. A proof of this assertion can be seen by looking at the vendor hall at any major security conference. The cacophony of sounds from vendors hawking their wares, the confusing language of the vendor’s marketecture, and the lack of any semblance of organization (aside from biggest to smallest) does not help buyers understand what they need or where to find it. Because the cybersecurity community does not use consistent terminology to describe what we need, there is much confusion about what many vendor products actually do. Instead of a clear articulation of a product's capabilities, we are bombarded with overused, trendy jargon that usually leaves us wondering if the product can really solve any of our woes. Some organizations even organize themselves according to the jargon. We need to stop letting marketing pitches dictate our terminology and not lose sight of the more bland descriptors that actually tell us what something does. The Cyber Defense Matrix helps us understand what we need organized through a logical construct so that when we go into the security vendor marketplace, we can quickly discern what products solve what problems and be informed on what is the core function of a given product. In addition, the Cyber Defense Matrix provides a mechanism to ensure that we have capabilities across the entire spectrum of options to help secure our environments. Although the Cyber Defense Matrix was initially created to help organize security technologies, many other use cases have been discovered to help build, manage, and operate a security program. This project intends to capture these use cases and their implementations to help security practitioners mature their security programs. Structure of the Cyber Defense MatrixThe basic construct of the Cyber Defense Matrix starts with two dimensions. The first dimension captures the five operational functions of the NIST Cybersecurity Framework:
The second dimension captures five assets classes that we try to secure:
When these two dimensions are put into a grid, we arrive at with a five-by-five matrix that we call the “Cyber Defense Matrix.” There is one more important piece of this matrix. At bottom of the grid, we show a continuum that characterizes the degree of dependency on technology, people, and process as we progress through the five operational functions of the NIST Cybersecurity Framework. TECHNOLOGY plays a much greater role in IDENTIFY and PROTECT. As we move to DETECT, RESPOND, and RECOVER, our dependency on TECHNOLOGY diminishes and our dependency on PEOPLE grows. Throughout all five operational functions, there's a consistent level of dependency on PROCESS. This continuum helps us understand where we might have imbalances in our reliance on PEOPLE, PROCESS, and TECHNOLOGY when trying to tackle our cybersecurity challenges. We believe that this matrix is a realistic model describes a broad range of cybersecurity practices. In this website, you will find several insights on the Cyber Defense Matrix and examples of how to leverage it to address the challenges that we face in cybersecurity. If you discover a new use of the Cyber Defense Matrix, we would love to hear about it. Likewise, if you find a problem with the matrix in that it doesn't seem to properly describe something that we do in cybersecurity, please point that out, and we'll either adjust the matrix or clarify how that perceived discrepancy can be addressed or explained through the matrix. |
Presentations and Other MediaCyber Defense Matrix Presentation at RSA Conference 2016 Cyber Defense Matrix Reloaded Presentation at RSA Conference 2019 Project LeaderFAQs
Things To Do
Related Projects
LicensingThe Cyber Defense Matrix, originally created by Sounil Yu, is licensed under the http://creativecommons.org/licenses/by-sa/4.0/ Creative Commons Attribution-ShareAlike 4.0 license, so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one. |
MAILING LISTNews and Events
Classifications
| |||||||||||||||||
How can I participate in your project?
Everyone is invited to collaborate on this project. Contact the Project Leaders. The project needs different skills and expertise and different times during its development. Currently, we are looking for help in the following areas:
- Documenting new use cases
- Creating a system to capture everything that is mapped to the Cyber Defense Matrix. This includes:
- Mapping of vendors
- Mapping of NIST NICE NCWF skillsets
- Mapping of measurements and metrics