This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Mth3l3m3nt Framework Project"
Munir Njiru (talk | contribs) (→Contributors) |
Munir Njiru (talk | contribs) (→Videos) |
||
| (3 intermediate revisions by the same user not shown) | |||
| Line 60: | Line 60: | ||
==Videos== | ==Videos== | ||
| − | + | View the videos tab for an up to date list of videos. | |
| − | + | ||
| − | |||
==Documentation== | ==Documentation== | ||
* [https://github.com/alienwithin/OWASP-mth3l3m3nt-framework/wiki User Guide] | * [https://github.com/alienwithin/OWASP-mth3l3m3nt-framework/wiki User Guide] | ||
| Line 136: | Line 135: | ||
*[https://github.com/alienwithin/OWASP-mth3l3m3nt-framework/wiki/Developing-LFI-Plugins-(Exploits) Developing LFI Exploit Plugins] | *[https://github.com/alienwithin/OWASP-mth3l3m3nt-framework/wiki/Developing-LFI-Plugins-(Exploits) Developing LFI Exploit Plugins] | ||
*[https://github.com/alienwithin/OWASP-mth3l3m3nt-framework/wiki/Using-The-Cookie-Theft-Module Using the Cookie Theft Module] | *[https://github.com/alienwithin/OWASP-mth3l3m3nt-framework/wiki/Using-The-Cookie-Theft-Module Using the Cookie Theft Module] | ||
| + | |||
| + | = Videos = | ||
| + | * [https://www.youtube.com/watch?v=ETnAmV3dxRE OWASP Mth3l3m3nt Framework vs bWAPP (Stored XSS Case)] | ||
| + | * [https://www.youtube.com/watch?v=ZFWOKg9c_vA OWASP Mth3l3m3nt Framework in Africahackon 2015 CTF] | ||
| + | * [https://www.youtube.com/watch?v=QjBbrNtCx3A OWASP Mth3l3m3nt Framework Windows Installation] | ||
| + | * [https://www.youtube.com/watch?v=_Nw05Q3fc2A OWASP Mth3l3m3nt Framework Linux Installation] | ||
= Acknowledgements = | = Acknowledgements = | ||
Latest revision as of 12:30, 8 April 2016
|
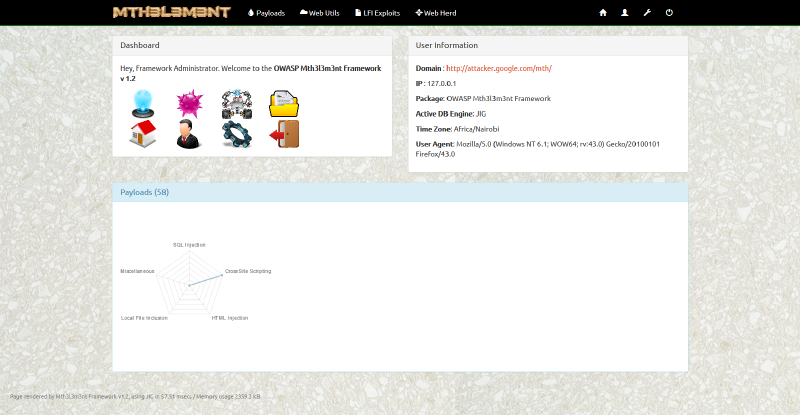
Mth3l3m3nt Framework ProjectOWASP Mth3l3m3nt Framework is a penetration testing aiding tool and exploitation framework. Mth3l3m3nt provides the ability to create or do custom LFI and RFI exploits fast with little or no effort at all. It also enables you to store all your quick wins based on its ability to manage HTTP bots, say no to runaway web shells and yes to centrally managed herds in large penetration testing engagements. DescriptionThe purpose of this project is to provide a platform to enable more flexible testing especially in aspects regarding to web security and the OWASP top 10 threats to web applications. This will enable free and opensource collaboration, being a web based tool, it is intended to make offensive security on the web easier and more efficient as it leverages on existing technologies with few dependencies. It is built on purely opensource components. It is intended to build up to a fully fledged web penetration testing framework with extensibility for zero day exploits in minutes to users. Currently the features it offers:
Please contribute to this project. LicensingThe OWASP Mth3l3m3nt Framework is free to use. Additionally, I also encourage you to contribute back to the project. I have no monopoly on this knowledge; however, we all have pieces of this knowledge from our experience. Let's begin by putting our individual pieces together to make something great. Great things happen when people work together. The OWASP Mth3l3m3nt Framework is licensed under the GNU AGPL v3 License, so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one. |
What is the OWASP Mth3l3m3nt Framework ProjectIt's a tool to exploit the web using the web when simply put. Imagine testing applications on the go, checking for vulnerabilities and analysing assets with no need for complex environments, just your simple web server and a database server, yes it can run on your tab too. tested with Palapa webserver on android running on Lighttpd and MySQL and it works well there also. This project aims to be that tool on the go and with time it will achieve its full potential. Project LeaderProject WebsiteRelated Projects
OpenhubVideosView the videos tab for an up to date list of videos. DocumentationIssue Tracker |
Quick DownloadThe home of the OWASP Mth3l3m3nt Framework is on GitHub. You are encouraged to fork, edit and push your changes back to the project through git or edit the project directly on github. However, if you like you may also download the master repository from the following links: Mailing ListUpdates
Classifications
| |||||||
How can I participate in your project?
All you have to do is make the Project Leader(s) aware of your available time to contribute to the project. It is also important to let the Leader(s) know how you would like to contribute and pitch in to help the project meet it's goals and milestones. There are many different ways you can contribute to an OWASP Project, but communication with the leads is key.
If I am not a programmer can I participate in your project?
Yes, you can certainly participate in the project if you are not a programmer or technical. The project needs different skills and expertise and different times during its development. Currently the most important aspects though would be along, graphics and UX design as well as researchers etc. Any Ideas are welcome to participate in the project.
Welcome to the OWASP Mth3l3m3nt framework User Guide, Here you will find a few tutorials on how to use and configure the system and make it better.
Table of Contents
- Initial WebServer Configuration
- Installation of OMF on Linux running Apache
- Installation of OMF on Linux running Nginx
- Installation of OMF on Linux running Lighttpd
- Installation of OMF on Windows running Apache
- Using the Payloads Module
- Using the Generic Requests Module
- Using the Shell Generator Module
- Using the Payload Encoder & Decoder Modules
- Using the Client Side Obfuscator Module
- Using the String Tools Module
- Using the LFI Exploit Module
- Using the Web Herd Module (HTTP Bot)
- Developing LFI Exploit Plugins
- Using the Cookie Theft Module
Contributors
The OWASP Mth3l3m3nt Framework project is developed by a worldwide team of volunteers. A live update of project contributors is found here. We can't forget the great support of the Africahackon team as this began to take flight and for testing some of its aspects. A special thanks should be in order for the Pentest-tools team that inspired the Cookie theft module.
The first contributors to the project were:
Currently already available is the source code ready for download and use. Working on sample videos for it and a PDF document on usage.
The project is envisioned to become a fully fledged security tool to test the OWASP top 10. Currently milestones achieved are:
- A web bot commander over HTTP to enable post-exploitation more easily
- A minimal web shell generator to use in commanding vulnerable hosts especially those with File Upload Vulnerabilities and some input injection ones.
- A payload store to keep new and old payloads that you frequently use and lose.
- An LFI/RFI exploiter to perform File inclusion attacks and create new exploits on the same.
- A web request module similar to hurl.it currently supporting GET/HEAD/TRACE/OPTIONS/POST requests and data very useful when in need of fingerprinting based on server headers and response codes.
- A payload encoder and decoder to convert payload strings e.g. Hex with 0x prefix for SQL Injection payloads.
- Client Side Obfuscator
- String Tools
- Whois
It is envisioned to be enabled to test and exploit all the OWASP top 10 vulnerabilities with ease and scalability. For instance currently developing an LFI exploit takes around 6 lines of code in the framework making it quite efficient even for zero day's along the same lines. This principle of ease is intended to be maintained through the project's lifecycle if not made easier.
Involvement in the development and promotion of the OWASP Mth3l3m3nt Framework Project is actively encouraged! You do not have to be a security expert in order to contribute. Some of the ways you can help:
- Helping find references to some new exploits.
- Project administration support.
- Wiki editing support.
- Writing documentation for its use.
- Bringing in fresh design principles from a UX perspective