This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP ZSC Tool Project"
(→Contributors & Main Developers) |
|||
| (70 intermediate revisions by 3 users not shown) | |||
| Line 20: | Line 20: | ||
<span title="Seed on Newsvine">[[File:social-newsvine.png|16px|Seed on Newsvine|link=http://www.newsvine.com/_wine/save?popoff=1&u={{fullurle:{{FULLPAGENAME}}}}]]</span> | <span title="Seed on Newsvine">[[File:social-newsvine.png|16px|Seed on Newsvine|link=http://www.newsvine.com/_wine/save?popoff=1&u={{fullurle:{{FULLPAGENAME}}}}]]</span> | ||
</div> | </div> | ||
| − | |||
| − | '''OWASP ZSC''' | + | '''Donate to OWASP ZSC''' {{#widget:PayPal Donation |target=_blank |budget=OWASP ZSC }} |
| + | ====What is OWASP ZSC ?==== | ||
http://zsc.z3r0d4y.com/images/Snapshot_2015-07-26_191951-half.png | http://zsc.z3r0d4y.com/images/Snapshot_2015-07-26_191951-half.png | ||
| − | + | '''OWASP ZSC''' is an open source software in Python language which lets you '''generate customized shellcodes''' and '''convert scripts to an obfuscated script'''. This software can be run on Windows/Linux/OSX under Python. | |
| + | |||
| + | [[File:Zsc1.png|200px]] | ||
==Description== | ==Description== | ||
====Usage of shellcodes==== | ====Usage of shellcodes==== | ||
| − | Shellcodes are small codes in | + | Shellcodes are small codes in Assembly language which could be used as the payload in software exploitation. Other usages are in malwares, bypassing antiviruses, obfuscated codes and etc. |
| + | |||
| + | ====DISCLAIMER==== | ||
| + | This tool is related to IT, Hacking, Programming and Computer|Network|Software Security. The word “Hack”, "Pen testing",“Hacking” that is used on these project pages shall be regarded as “Ethical Hack” or “Ethical Hacking” respectively. This is not a tool that provides any illegal information.We do not promote hacking or software cracking. All the information provided on these pages is for educational purposes only. | ||
| + | |||
| + | The authors of this tool are not responsible for any misuse of the information.You shall not misuse the information to gain unauthorized access and/or write malicious programs.This information shall only be used to expand knowledge and not for causing malicious or damaging attacks.You may try all of these techniques on your own computer at your own risk.Performing any hack attempts/tests without written permission from the owner of the computer system is illegal. | ||
| + | |||
| + | IN NO EVENT SHALL THE CREATORS, OWNER, OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. | ||
====Usage of Obfuscate Codes==== | ====Usage of Obfuscate Codes==== | ||
| − | Can be | + | Can be used for bypassing antiviruses, code protections, same stuff etc … |
====Why use OWASP ZSC ?==== | ====Why use OWASP ZSC ?==== | ||
| − | According to other shellcode generators same as | + | Another good reason for obfuscating files or generating shellcode with ZSC is that it can be used during your pen-testing. Malicious hackers use these techniques to bypass anti-virus and load malicious files in systems they have hacked using customized shellcode generators. |
| − | OWASP ZSC | + | Anti-virus work with signatures in order to identify harmful files. When using very well known encoders such as msfvenom, files generated by this program might be already flagged by Anti-virus programs. |
| + | |||
| + | Our purpose is not to provide a way to bypass anti-virus with malicious intentions, instead, we want to provide pen-testers a way to challenge the security provided by Anti-virus programs and Intrusion Detection systems during a pen test.In this way, they can verify the security just as a black-hat will do. | ||
| + | |||
| + | According to other shellcode generators same as Metasploit tools and etc, OWASP ZSC using new encodes and methods which antiviruses won't detect. | ||
| + | OWASP ZSC encoders are able to generate shell codes with random encodes and that allows you to generate thousands of new dynamic shellcodes with the same job in just a second, that means, you will not get the same code if you use random encodes with same commands, And that make OWASP ZSC one of the best! | ||
During the Google Summer of Code we are working on to generate Windows Shellcode and new obfuscation methods. | During the Google Summer of Code we are working on to generate Windows Shellcode and new obfuscation methods. | ||
| − | We are working on the next version that will allow you to generate OSX . | + | We are working on the next version that will allow you to generate OSX. |
==Licensing== | ==Licensing== | ||
| Line 61: | Line 75: | ||
== Project Leaders == | == Project Leaders == | ||
| − | |||
* [https://www.owasp.org/index.php/User:Ali_Razmjoo Ali Razmjoo] | * [https://www.owasp.org/index.php/User:Ali_Razmjoo Ali Razmjoo] | ||
| Line 76: | Line 89: | ||
== Links == | == Links == | ||
| + | * [http://api.z3r0d4y.com/ API] | ||
* [https://github.com/Ali-Razmjoo/OWASP-ZSC Project on Github] | * [https://github.com/Ali-Razmjoo/OWASP-ZSC Project on Github] | ||
* [https://groups.google.com/d/forum/owasp-zsc Mailing List] | * [https://groups.google.com/d/forum/owasp-zsc Mailing List] | ||
| Line 86: | Line 100: | ||
== Shellcode Generating == | == Shellcode Generating == | ||
| − | With using '''OWASP ZSC''' you would be able to generate any customized '''Shellcode''' in your mind including encodes | + | With using '''OWASP ZSC''' you would be able to generate any customized '''Shellcode''' in your mind including encodes and Disassembly code in few seconds. |
== Be an OWASP ZSC developer == | == Be an OWASP ZSC developer == | ||
| Line 96: | Line 110: | ||
* [http://zsc.z3r0d4y.com/blog/2015/07/27/video-how-to-install-and-generate-shellcode-using-zsc/ Video: Install&Generate Shellcode] | * [http://zsc.z3r0d4y.com/blog/2015/07/27/video-how-to-install-and-generate-shellcode-using-zsc/ Video: Install&Generate Shellcode] | ||
| + | ==Related links== | ||
| + | *[https://www.youtube.com/watch?v=nkx0HQhYdmY| Appsec Presentation 2013 Beef and Custome shellcodes] | ||
| + | *[https://www.owasp.org/index.php/File:Introduction_to_shellcode_development.pdf| Introduction to Shellcode Development] | ||
<!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | <!-- DO NOT ALTER OR REMOVE THE TEXT ON NEXT LINE --> | ||
| Line 101: | Line 118: | ||
== Quick Download == | == Quick Download == | ||
| − | [https://github.com/ | + | |
| + | [https://github.com/zscproject/OWASP-ZSC Github Page.] | ||
[http://zsc.z3r0d4y.com/download/ Download Page.] | [http://zsc.z3r0d4y.com/download/ Download Page.] | ||
| − | * [https://github.com/ | + | * [https://github.com/zscproject/OWASP-ZSC/zipball/master .zip file.] |
| − | * [https://github.com/ | + | * [https://github.com/zscproject/OWASP-ZSC/tarball/master .tgz file.] |
== News and Events == | == News and Events == | ||
| − | * OWASP ZSC has been selected for Defcon Demo Lab 2016 | + | * [https://www.owasp.org/index.php/Iran#tab=Past_Events OWASP Nettacker Presented By Ali Razmjoo in OWASP Iran Chapter Meeting July 2018] |
| − | * OWASP ZSC applied and was selected to participate in the Google Summer of Code | + | * [https://www.owasp.org/index.php/OWASP_Code_Sprint_2017#OWASP_ZSC OWASP ZSC in OWASP Code Sprint 2017] |
| − | * | + | * [http://www.toolswatch.org/2017/02/2016-top-security-tools-as-voted-by-toolswatch-org-readers/ OWASP ZSC Selected as Top 10 Security tools in 2016 By ToolsWatch] |
| + | * [https://groups.google.com/forum/#!topic/owasp-zsc/t12M2fxn78k OWASP ZSC Presented in OFFSECONF 2016] | ||
| + | * [https://www.blackhat.com/eu-16/arsenal.html#brian-beaudry Been Selected for Blackhat EU Arsenal 2016] | ||
| + | * [https://www.defcon.org/html/defcon-24/dc-24-demolabs.html#Curiel OWASP ZSC has been selected for Defcon Demo Lab 2016] | ||
| + | * [https://summerofcode.withgoogle.com/archive/2016/projects/5969824152813568/ OWASP ZSC applied and was selected to participate in the Google Summer of Code 2016] | ||
| + | * [https://www.linkedin.com/pulse/lessons-from-cyber-underworld-how-understand-software-ali-razmjoo Press Release 12th February 2015 ] | ||
* [http://zsc.z3r0d4y.com/ OWASP ZSC Version 1.0.9.1 Released!] | * [http://zsc.z3r0d4y.com/ OWASP ZSC Version 1.0.9.1 Released!] | ||
| + | * [https://github.com/longld/peda OWASP ZSC in GDB-PEDA] | ||
== Docs == | == Docs == | ||
* [https://github.com/Ali-Razmjoo/OWASP-ZSC/tree/master/doc Developers and Users Documents]. | * [https://github.com/Ali-Razmjoo/OWASP-ZSC/tree/master/doc Developers and Users Documents]. | ||
| + | * [http://zsc.z3r0d4y.com/ OWASP ZSC Home] | ||
==Classifications== | ==Classifications== | ||
| Line 122: | Line 147: | ||
|- | |- | ||
| align="center" valign="top" width="50%" rowspan="2"| [[File:New projects.png|100px|link=https://www.owasp.org/index.php/OWASP_Project_Stages#tab=Incubator_Projects]] | | align="center" valign="top" width="50%" rowspan="2"| [[File:New projects.png|100px|link=https://www.owasp.org/index.php/OWASP_Project_Stages#tab=Incubator_Projects]] | ||
| − | | align="center" valign="top" width="50%"| [[File:Owasp- | + | | align="center" valign="top" width="50%"| [[File:Owasp-breakers-small.png|link=]] |
|- | |- | ||
| − | | | + | | |
|- | |- | ||
| − | | | + | | |
|- | |- | ||
| − | | colspan="2" align="center" | [[File: | + | | colspan="2" align="center" | [[File:Project_Type_Files_TOOL.jpg|link=]] |
|} | |} | ||
| Line 156: | Line 181: | ||
| − | OWASP ZSC is an open source software in | + | OWASP ZSC is an open source software in Python language which lets you generate customized shellcodes and convert scripts to an obfuscated script. This software can be run on Windows/Linux/OSX under python. |
| Line 162: | Line 187: | ||
| − | Shellcodes are small codes in | + | Shellcodes are small codes in Assembly Languagewhich could be used as the payload in software exploiting. Other usages are in malwares, bypassing anti viruses, obfuscated codes and etc. |
| Line 168: | Line 193: | ||
| − | Can be | + | Can be used for bypassing antiviruses, code protections, same stuff etc … |
| Line 174: | Line 199: | ||
| − | According to other shellcode generators such as | + | According to other shellcode generators such as Metasploit tools and etc, OWASP ZSC using new encodes and methods which antiviruses won't detect. OWASP ZSC encoders are able to generate shell codes with random encodes that allows you to generate thousands of new dynamic shell codes with the same job in just a second, it means you will not get the same code if you use random encodes with the same commands, and that makes OWASP ZSC one of the best! |
OWASP ZSC can generate shellcode for Linux and Windows _x86 | OWASP ZSC can generate shellcode for Linux and Windows _x86 | ||
| − | Upcoming features will allow | + | Upcoming features will allow generating shellcodes for OSX |
And new encodes for the code obfuscation. | And new encodes for the code obfuscation. | ||
| Line 186: | Line 211: | ||
======Generating Shellcode====== | ======Generating Shellcode====== | ||
| − | Via `zsc` command , you are able to enter the software [or run python zsc.py if you don’t want install it], Then you can have list of menu with entering `help`. You can have your choices with pressing `tab` key on each step. To generate shellcode , you have to type `shellcode` and then press enter, after that, you can see what’s available in `shellcode` section. There is `generate` , `search` and `download` choices in here which use for `generate shellcodes` , `search` and `download` shellcode from shellstorm. To generate a shellcode, type `generate` and press enter, after that with a `tab` key, you can have list of operation systems available in there. With pressing `tab` key again, functions will be shown for you in this step [ such as `exec` ,`systm`,`write` and `etc`]. choose your function by writing the name `example: exec` and press inter. In the next section you have to fill the argv of function which exec() function have one `example: exec("/bin/bash")`, all you need in this section is pressing a `tab` and then `enter` key, software will automatically ask you for function argv. Fill them and next section software will ask you for shellcode type which can be `none` or choose one of listed encoding types. After entering that, your shellcode is ready! | + | Via `zsc` command, you are able to enter the software [or run python zsc.py if you don’t want to install it], Then you can have a list of menu with entering `help`. You can have your choices with pressing `tab` key on each step. To generate shellcode, you have to type `shellcode` and then press enter, after that, you can see what’s available in `shellcode` section. There is `generate` , `search` and `download` choices in here which use for `generate shellcodes`, `search` and `download` shellcode from shellstorm. To generate a shellcode, type `generate` and press enter, after that with a `tab` key, you can have list of operation systems available in there. With pressing `tab` key again, functions will be shown for you in this step [ such as `exec` ,`systm`,`write` and `etc`]. choose your function by writing the name `example: exec` and press inter. In the next section you have to fill the argv of function which exec() function have one `example: exec("/bin/bash")`, all you need in this section is pressing a `tab` and then `enter` key, software will automatically ask you for function argv. Fill them and next section software will ask you for shellcode type which can be `none` or choose one of listed encoding types. After entering that, your shellcode is ready! |
There is one more way to have a shellcode from software, which is using shellstorm API. Following the `shellcode`, and then `search` commands to search for a shellcode. After that shellcodes will be listed for you with title name , ID and etc. you can download them with following `shellcode` and then `download` command to download them with the ID which shown to you in the past section! For canceling each section, you can use `restart` command to restart the software and start new task! | There is one more way to have a shellcode from software, which is using shellstorm API. Following the `shellcode`, and then `search` commands to search for a shellcode. After that shellcodes will be listed for you with title name , ID and etc. you can download them with following `shellcode` and then `download` command to download them with the ID which shown to you in the past section! For canceling each section, you can use `restart` command to restart the software and start new task! | ||
| Line 241: | Line 266: | ||
==Roadmap== | ==Roadmap== | ||
| − | As of <strong>August, | + | As of <strong>August, 2016, the highest priorities for the next one year</strong> are: |
<strong> | <strong> | ||
* Develop future [http://zsc.z3r0d4y.com/table.html features] list , Add Operation Systems and new encode types | * Develop future [http://zsc.z3r0d4y.com/table.html features] list , Add Operation Systems and new encode types | ||
| Line 261: | Line 286: | ||
=Minimum Viable Product= | =Minimum Viable Product= | ||
| + | |||
<div class="plainlinks"> | <div class="plainlinks"> | ||
'''Share this:''' | '''Share this:''' | ||
| Line 276: | Line 302: | ||
Highest usage of OWASP ZSC Tool could be when users are able to use all [http://zsc.z3r0d4y.com/table.html features] with best User Interface and <strong>API</strong> performance. | Highest usage of OWASP ZSC Tool could be when users are able to use all [http://zsc.z3r0d4y.com/table.html features] with best User Interface and <strong>API</strong> performance. | ||
| + | https://www.owasp.org/images/3/33/Zsc.png | ||
= Developers = | = Developers = | ||
| Line 292: | Line 319: | ||
==Developers== | ==Developers== | ||
| + | Architect & Creator: Ali Razmjoo | ||
| + | * Pratik Patel (Google Summer of Code student 2016) | ||
| + | * Akash Trehan (CodeMaxx) | ||
| + | * Paras Chetal (Google Summer of Code candidate 2016) | ||
| + | * Hamid Samani (HAMIDx9) | ||
| − | + | ==Testers == | |
| − | * | + | *Johanna Curiel |
| − | * | + | *Brian Beaudry |
| − | |||
| − | |||
===Be an OWASP ZSC developer=== | ===Be an OWASP ZSC developer=== | ||
| Line 321: | Line 351: | ||
__NOTOC__ <headertabs /> | __NOTOC__ <headertabs /> | ||
| − | [[Category:OWASP Project]] [[Category: | + | [[Category:OWASP Project]] [[Category:OWASP_Breakers]] [[Category:OWASP_Code]] [[Category:OWASP_Tool]] [[Category:OWASP_Download]] [[Category:Shellcode]] |
Latest revision as of 02:55, 16 January 2020
- Main
- FAQs
- Requirement / Installation
- Road Map and Getting Involved
- Minimum Viable Product
- Developers
- Project About
OWASP ZSC Tool ProjectDonate to OWASP ZSC What is OWASP ZSC ?
OWASP ZSC is an open source software in Python language which lets you generate customized shellcodes and convert scripts to an obfuscated script. This software can be run on Windows/Linux/OSX under Python. DescriptionUsage of shellcodesShellcodes are small codes in Assembly language which could be used as the payload in software exploitation. Other usages are in malwares, bypassing antiviruses, obfuscated codes and etc. DISCLAIMERThis tool is related to IT, Hacking, Programming and Computer|Network|Software Security. The word “Hack”, "Pen testing",“Hacking” that is used on these project pages shall be regarded as “Ethical Hack” or “Ethical Hacking” respectively. This is not a tool that provides any illegal information.We do not promote hacking or software cracking. All the information provided on these pages is for educational purposes only. The authors of this tool are not responsible for any misuse of the information.You shall not misuse the information to gain unauthorized access and/or write malicious programs.This information shall only be used to expand knowledge and not for causing malicious or damaging attacks.You may try all of these techniques on your own computer at your own risk.Performing any hack attempts/tests without written permission from the owner of the computer system is illegal. IN NO EVENT SHALL THE CREATORS, OWNER, OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. Usage of Obfuscate CodesCan be used for bypassing antiviruses, code protections, same stuff etc … Why use OWASP ZSC ?Another good reason for obfuscating files or generating shellcode with ZSC is that it can be used during your pen-testing. Malicious hackers use these techniques to bypass anti-virus and load malicious files in systems they have hacked using customized shellcode generators. Anti-virus work with signatures in order to identify harmful files. When using very well known encoders such as msfvenom, files generated by this program might be already flagged by Anti-virus programs. Our purpose is not to provide a way to bypass anti-virus with malicious intentions, instead, we want to provide pen-testers a way to challenge the security provided by Anti-virus programs and Intrusion Detection systems during a pen test.In this way, they can verify the security just as a black-hat will do. According to other shellcode generators same as Metasploit tools and etc, OWASP ZSC using new encodes and methods which antiviruses won't detect. OWASP ZSC encoders are able to generate shell codes with random encodes and that allows you to generate thousands of new dynamic shellcodes with the same job in just a second, that means, you will not get the same code if you use random encodes with same commands, And that make OWASP ZSC one of the best! During the Google Summer of Code we are working on to generate Windows Shellcode and new obfuscation methods. We are working on the next version that will allow you to generate OSX. LicensingGNU GENERAL PUBLIC LICENSE , Version 3, 29 June 2007Copyright (C) 2007 Free Software Foundation, Inc. http://fsf.org/ Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed. Click to see the full license
The OWASP Security Principles are licensed under the http://creativecommons.org/licenses/by-sa/3.0/ Creative Commons Attribution-ShareAlike 3.0 license], so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one. |
Project LeadersContributors & Main Developers
Links
Shellcode GeneratingWith using OWASP ZSC you would be able to generate any customized Shellcode in your mind including encodes and Disassembly code in few seconds. Be an OWASP ZSC developerLast Tricks in HomeRelated links |
Quick DownloadNews and Events
DocsClassifications
| ||||||
To see full guides please visit our wiki page.
Help Menu
PLEASE CLICK HERE TO SEE FULL DEVELOPERS AND USERS DOCUMENTS
OWASP ZSC Project
OWASP ZSC is an open source software in Python language which lets you generate customized shellcodes and convert scripts to an obfuscated script. This software can be run on Windows/Linux/OSX under python.
Usage of shellcodes
Shellcodes are small codes in Assembly Languagewhich could be used as the payload in software exploiting. Other usages are in malwares, bypassing anti viruses, obfuscated codes and etc.
Usage of Obfuscate Codes
Can be used for bypassing antiviruses, code protections, same stuff etc …
Why use OWASP ZSC ?
According to other shellcode generators such as Metasploit tools and etc, OWASP ZSC using new encodes and methods which antiviruses won't detect. OWASP ZSC encoders are able to generate shell codes with random encodes that allows you to generate thousands of new dynamic shell codes with the same job in just a second, it means you will not get the same code if you use random encodes with the same commands, and that makes OWASP ZSC one of the best! OWASP ZSC can generate shellcode for Linux and Windows _x86 Upcoming features will allow generating shellcodes for OSX And new encodes for the code obfuscation.
User Guides
To run OWASP ZSC, You need to install python `2.x|3.x` on your operation system `Windows|Linux|OSX`, Then it could be run directly with executing `zsc.py` or run the software after you installed it! To see the user manuals, Please follow the next steps!
Generating Shellcode
Via `zsc` command, you are able to enter the software [or run python zsc.py if you don’t want to install it], Then you can have a list of menu with entering `help`. You can have your choices with pressing `tab` key on each step. To generate shellcode, you have to type `shellcode` and then press enter, after that, you can see what’s available in `shellcode` section. There is `generate` , `search` and `download` choices in here which use for `generate shellcodes`, `search` and `download` shellcode from shellstorm. To generate a shellcode, type `generate` and press enter, after that with a `tab` key, you can have list of operation systems available in there. With pressing `tab` key again, functions will be shown for you in this step [ such as `exec` ,`systm`,`write` and `etc`]. choose your function by writing the name `example: exec` and press inter. In the next section you have to fill the argv of function which exec() function have one `example: exec("/bin/bash")`, all you need in this section is pressing a `tab` and then `enter` key, software will automatically ask you for function argv. Fill them and next section software will ask you for shellcode type which can be `none` or choose one of listed encoding types. After entering that, your shellcode is ready! There is one more way to have a shellcode from software, which is using shellstorm API. Following the `shellcode`, and then `search` commands to search for a shellcode. After that shellcodes will be listed for you with title name , ID and etc. you can download them with following `shellcode` and then `download` command to download them with the ID which shown to you in the past section! For canceling each section, you can use `restart` command to restart the software and start new task!
Generating Obfuscate Code
With the following `obfuscate` command, you can begin the step for obfuscating a code. With a `tab` key , you can see the list of languages along with the obfuscating module ready. After choosing the language software will ask you for a filename which is a filename of file you want to obfuscate that! Next step software will ask you for encode type. With a `tab` key list the encode modules and choose your encode name. your file rewrited and converted to a obfuscate with encode type you chosen. And do not worry about your original code, it’s saved in file as a comment!
Please click HERE to read more!
Installation Go to download page, and download last version in github. Extract and run installer.py, then you are able to run software with OWASP ZSC command or you can directly execute zsc.py without installing it.or you can follow these commands to install the last version:
wget https://github.com/Ali-Razmjoo/OWASP-ZSC/archive/master.zip -O owasp-zsc.zip && unzip owasp-zsc.zip && rm -rf owasp-zsc.zip && mv OWASP-ZSC-master owasp-zsc && cd owasp-zsc && python installer.py
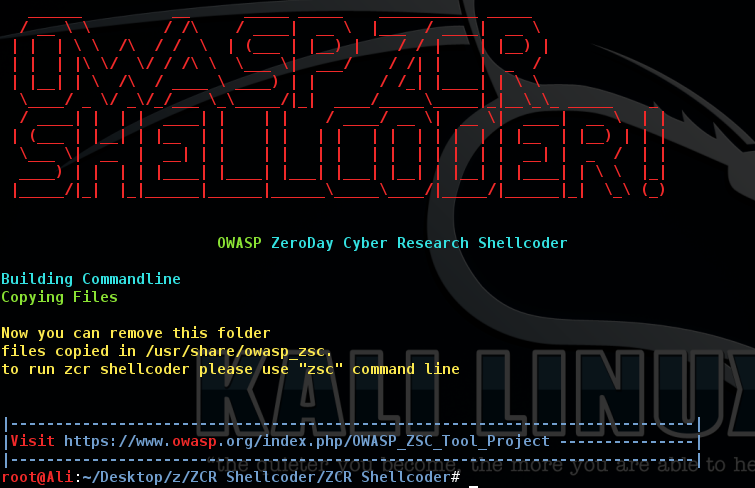
Note: Software could be uninstall with executing uninstaller.py
Note: Software installation directory is "/usr/share/owasp-zsc"
Note: OWASP ZSC Tool could be execute on Linux and Python 2.7.x is required.
Roadmap
As of August, 2016, the highest priorities for the next one year are:
- Develop future features list , Add Operation Systems and new encode types
- Planing for activate features
- Build ZSC API
- Find developers to get better performance, quality, optimizing and best improvement in minimum possible time
- Get other people to review the ZSC Tool Project provide feedback
- Incorporate feedback into changes in the Tool Project and the features
- Keep test, developing and updating with best new methods
- Build and update documents in several languages for developers/users guiding
Subsequent Releases will add
- Internationalization Support
- Additional Unit Tests
- Automated Regression tests
OWASP ZSC could be improving with handling module features. MVP of this project is build and active the first module which could be usable to generate/encode Shellcode which already some of them [modules] activated.
Highest usage of OWASP ZSC Tool could be when users are able to use all features with best User Interface and API performance.

Developers
Architect & Creator: Ali Razmjoo
- Pratik Patel (Google Summer of Code student 2016)
- Akash Trehan (CodeMaxx)
- Paras Chetal (Google Summer of Code candidate 2016)
- Hamid Samani (HAMIDx9)
Testers
- Johanna Curiel
- Brian Beaudry
Be an OWASP ZSC developer
Developers can add new features and if you don’t have an idea but like to develop, you can submit the issue, which software needs to be fix/add/done in HERE.
After fix/add or develop something, please send your pull request and remember that your code must be compatible with python2 and python3. If you have any question you can open an issue or just mail us. do not forget to register on our mailing list.
AND DON'T FORGET TO READ DEVELOPERS DOCUMENTS
Also this GitBook
| PROJECT INFO What does this OWASP project offer you? |
RELEASE(S) INFO What releases are available for this project? | |||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
| |||||||||||||||||||||||||||||||||||||||