This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP API Security Project"
(Tag: Visual edit) |
PauloASilva (talk | contribs) (→Contributors) |
||
| (6 intermediate revisions by the same user not shown) | |||
| Line 13: | Line 13: | ||
API Security focuses on strategies and solutions to understand and mitigate the unique vulnerabilities and security risks of Application Programming Interfaces (APIs). | API Security focuses on strategies and solutions to understand and mitigate the unique vulnerabilities and security risks of Application Programming Interfaces (APIs). | ||
| − | ==API Security Top 10 | + | ==API Security Top 10 is Here!== |
| − | + | Here is a sneak peek of the 2019 version: | |
| − | Here is a sneak peek: | ||
{| class="wikitable" | {| class="wikitable" | ||
|- | |- | ||
| − | | API1 || Broken Object Level Authorization || APIs tend to expose endpoints that handle object identifiers, creating a wide attack surface Level Access Control issue. Object | + | | API1 || Broken Object Level Authorization || APIs tend to expose endpoints that handle object identifiers, creating a wide attack surface Level Access Control issue. Object level authorization checks should be considered in every function that accesses a data source using an input from the user. |
|- | |- | ||
| − | | API2 || Broken Authentication || Authentication mechanisms are often implemented incorrectly, allowing attackers to compromise authentication tokens or to exploit implementation flaws to assume other user's identities temporarily or permanently. Compromising system's ability to identify the client/user, compromises API security overall. | + | | API2 || Broken User Authentication || Authentication mechanisms are often implemented incorrectly, allowing attackers to compromise authentication tokens or to exploit implementation flaws to assume other user's identities temporarily or permanently. Compromising system's ability to identify the client/user, compromises API security overall. |
|- | |- | ||
| API3 || Excessive Data Exposure || Looking forward to generic implementations, developers tend to expose all object properties without considering their individual sensitivity, relying on clients to perform the data filtering before displaying it to the user. | | API3 || Excessive Data Exposure || Looking forward to generic implementations, developers tend to expose all object properties without considering their individual sensitivity, relying on clients to perform the data filtering before displaying it to the user. | ||
| Line 32: | Line 31: | ||
| API6 || Mass Assignment || Binding client provided data (e.g., JSON) to data models, without proper properties filtering based on a whitelist, usually lead to Mass Assignment. Either guessing objects properties, exploring other API endpoints, reading the documentation, or providing additional object properties in request payloads, allows attackers to modify object properties they are not supposed to. | | API6 || Mass Assignment || Binding client provided data (e.g., JSON) to data models, without proper properties filtering based on a whitelist, usually lead to Mass Assignment. Either guessing objects properties, exploring other API endpoints, reading the documentation, or providing additional object properties in request payloads, allows attackers to modify object properties they are not supposed to. | ||
|- | |- | ||
| − | | API7 || Security Misconfiguration || Security misconfiguration is commonly a result of | + | | API7 || Security Misconfiguration || Security misconfiguration is commonly a result of unsecure default configurations, incomplete or ad-hoc configurations, open cloud storage, misconfigured HTTP headers, unnecessary HTTP methods, permissive Cross-Origin resource sharing (CORS), and verbose error messages containing sensitive information. |
|- | |- | ||
| − | | API8 || Injection || Injection flaws, such as SQL, NoSQL, Command Injection, etc. occur when untrusted data is sent to an interpreter as part of a command or query. The attacker's malicious data can trick the interpreter into executing unintended commands or accessing data without proper authorization. | + | | API8 || Injection || Injection flaws, such as SQL, NoSQL, Command Injection, etc., occur when untrusted data is sent to an interpreter as part of a command or query. The attacker's malicious data can trick the interpreter into executing unintended commands or accessing data without proper authorization. |
|- | |- | ||
| API9 || Improper Assets Management || APIs tend to expose more endpoints than traditional web applications, making proper and updated documentation highly important. Proper hosts and deployed API versions inventory also play an important role to mitigate issues such as deprecated API versions and exposed debug endpoints. | | API9 || Improper Assets Management || APIs tend to expose more endpoints than traditional web applications, making proper and updated documentation highly important. Proper hosts and deployed API versions inventory also play an important role to mitigate issues such as deprecated API versions and exposed debug endpoints. | ||
| Line 63: | Line 62: | ||
[https://github.com/OWASP/API-Security GitHub] | [https://github.com/OWASP/API-Security GitHub] | ||
| − | [https://github.com/OWASP/API-Security/raw/master/2019/en/dist/owasp-api-security-top-10.pdf | + | [https://github.com/OWASP/API-Security/raw/master/2019/en/dist/owasp-api-security-top-10.pdf API Security Top 10 2019 (PDF)] |
| − | + | == News == | |
| − | == | + | === Dec 26, 2019 === |
| + | |||
| + | OWASP API Security Top 10 2019 stable version release. | ||
=== Sep 30, 2019 === | === Sep 30, 2019 === | ||
| Line 119: | Line 120: | ||
==Contributors== | ==Contributors== | ||
| − | + | 007divyachawla, Abid Khan, Adam Fisher, anotherik, bkimminich, caseysoftware, Chris Westphal, dsopas, DSotnikov, emilva, ErezYalon, flascelles, Guillaume Benats, IgorSasovets, Inonshk, JonnySchnittger, jmanico, jmdx, Keith Casey, kozmic, LauraRosePorter, Matthieu Estrade, nathanawmk, PauloASilva, pentagramz, philippederyck, pleothaud, r00ter, Raj kumar, Sagar Popat, Stephen Gates, thomaskonrad, xycloops123 | |
| − | |||
= Join = | = Join = | ||
Latest revision as of 10:39, 6 January 2020
What is API Security?A foundational element of innovation in today’s app-driven world is the API. From banks, retail and transportation to IoT, autonomous vehicles and smart cities, APIs are a critical part of modern mobile, SaaS and web applications and can be found in customer-facing, partner-facing and internal applications. By nature, APIs expose application logic and sensitive data such as Personally Identifiable Information (PII) and because of this have increasingly become a target for attackers. Without secure APIs, rapid innovation would be impossible. API Security focuses on strategies and solutions to understand and mitigate the unique vulnerabilities and security risks of Application Programming Interfaces (APIs). API Security Top 10 is Here!Here is a sneak peek of the 2019 version:
LicensingThe OWASP API Security Project documents are free to use! The OWASP API Security Project is licensed under the http://creativecommons.org/licenses/by-sa/3.0/ Creative Commons Attribution-ShareAlike 3.0 license], so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one. |
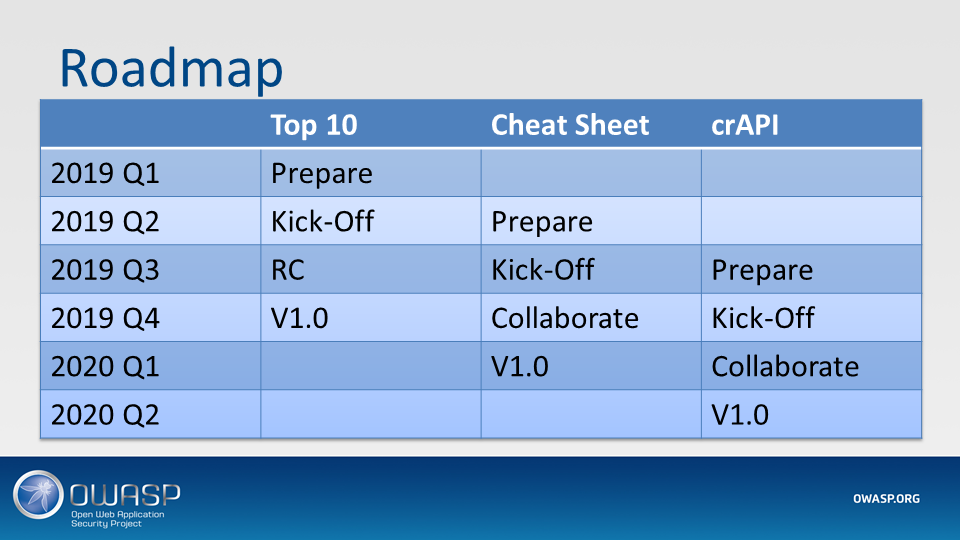
Project LeadersMain Collaborator Quick LinksAPI Security Top 10 2019 (PDF) NewsDec 26, 2019OWASP API Security Top 10 2019 stable version release. Sep 30, 2019The RC of API Security Top-10 List was published during OWASP Global AppSec Amsterdam File:API Security Top 10 RC - Global AppSec AMS.pdf Sep 13, 2019The RC of API Security Top-10 List was published during OWASP Global AppSec DC File:API Security Top 10 RC.pdf May 30, 2019The API Security Project was Kicked-Off during OWASP Global AppSec Tel Aviv File:OWASP APIs Security Project Kick Off.pdf Classifications
| ||||||||||||||||||||||||||||||||||||||
Founders
- Erez Yalon
- Inon Shkedy
Sponsors
Main Maintainer
- Paulo Silva
Contributors
007divyachawla, Abid Khan, Adam Fisher, anotherik, bkimminich, caseysoftware, Chris Westphal, dsopas, DSotnikov, emilva, ErezYalon, flascelles, Guillaume Benats, IgorSasovets, Inonshk, JonnySchnittger, jmanico, jmdx, Keith Casey, kozmic, LauraRosePorter, Matthieu Estrade, nathanawmk, PauloASilva, pentagramz, philippederyck, pleothaud, r00ter, Raj kumar, Sagar Popat, Stephen Gates, thomaskonrad, xycloops123
Google Group
Join the discussion on the OWASP API Security Project Google group.
This is the best place to introduce yourself, ask questions, suggest and discuss any topic that is relevant to the project.
GitHub
The project is maintained in the OWASP API Security Project repo.
The latest changes are under the develop branch.
Feel free to open or solve an issue.
Ready to contribute directly into the repo? Great! Just make you you read the How to Contribute guide.