This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Video Game Security Framework"
m |
(2020- Added New VGSF Framework) |
||
| (13 intermediate revisions by 2 users not shown) | |||
| Line 19: | Line 19: | ||
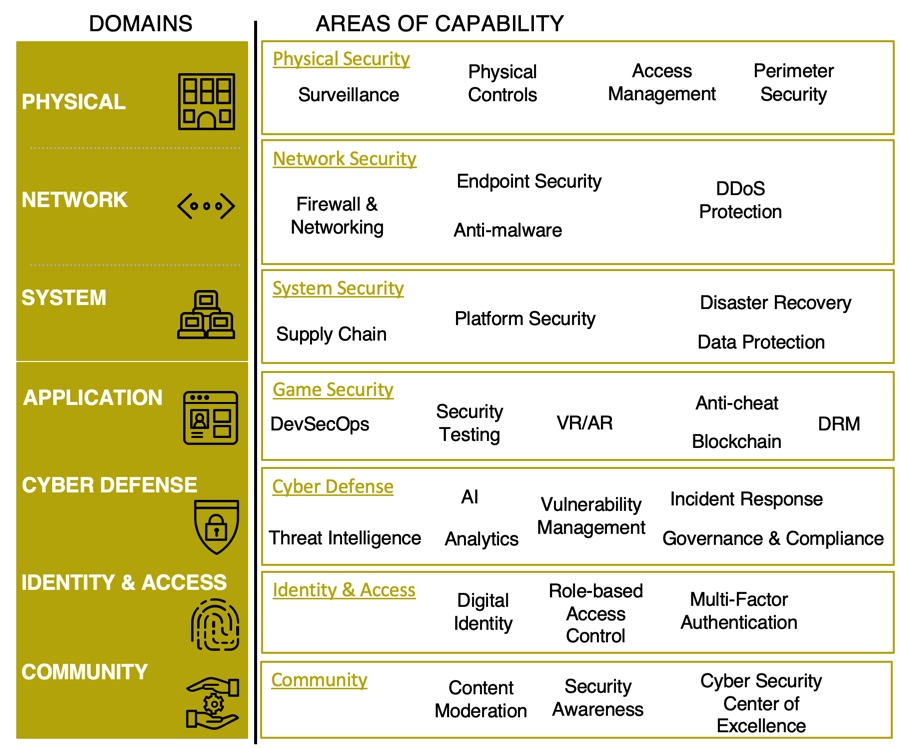
With the fast growth of the video game industry (174 billion by 2021 - Newzoo Global Game Forecast) in recent years, it is critical that organizations operating in this space have a strong security posture. Cyber-attacks aimed at various components of a business can affect the interoperability, user protected info, end-game product, and overall business model. As more businesses and clients operate in the cyber space its important to leverage security as a way to create sustainable trust, lead competitively, and operate more agile with different types of data. | With the fast growth of the video game industry (174 billion by 2021 - Newzoo Global Game Forecast) in recent years, it is critical that organizations operating in this space have a strong security posture. Cyber-attacks aimed at various components of a business can affect the interoperability, user protected info, end-game product, and overall business model. As more businesses and clients operate in the cyber space its important to leverage security as a way to create sustainable trust, lead competitively, and operate more agile with different types of data. | ||
| − | ''The framework is comprised of five discipline areas that could produce many best practice methodologies:''[[File:VGSF | + | ''The framework is comprised of five discipline areas that could produce many best practice methodologies:'' |
| + | [[File:VGSF FRAMEWORK IMAGE.jpg|frame|center|VGSF]] | ||
| Line 64: | Line 65: | ||
== Contributors == | == Contributors == | ||
| − | * | + | * Dmytro Korzhevin |
== Related Projects == | == Related Projects == | ||
| Line 325: | Line 326: | ||
'''Governance & Compliance Process''' | '''Governance & Compliance Process''' | ||
<br /> | <br /> | ||
| − | :1. Regulation | + | :1. Regulation |
| − | :2. Audit | + | :2. Audit |
| − | :3. Monitor | + | :3. Monitor |
| − | :4. Control | + | :4. Control |
<br /> | <br /> | ||
| − | '''1. Regulation | + | '''1. Regulation''' |
<br /> | <br /> | ||
| − | There are many regulations that attribute to organizational compliance and understanding policies that | + | There are many regulations that attribute to organizational compliance and understanding policies that align to the business model and future security strategy is the first step. |
<br /> | <br /> | ||
| Line 363: | Line 364: | ||
::d) Google | ::d) Google | ||
::e) Amazon | ::e) Amazon | ||
| − | ::f) | + | ::f) Apple |
::g) Steam | ::g) Steam | ||
| Line 371: | Line 372: | ||
<br /> | <br /> | ||
| − | 2. '''Audit | + | 2. '''Audit''' |
<br /> | <br /> | ||
| − | The best way to ensure an organization is maintaining the | + | The best way to ensure an organization is maintaining the proper level of compliance is to audit. |
Auditing involves performing routine internal checks to ensure policies are being followed by all. | Auditing involves performing routine internal checks to ensure policies are being followed by all. | ||
| Line 415: | Line 416: | ||
<br /> | <br /> | ||
| − | Monitoring involves watching an existing | + | Monitoring involves watching an existing business environment for changes related to the overall compliance status. The goal is to detect anomalies and watch organizational trends from a compliance point of view. This valuable information will aid in quickly remedying non-compliance and developing new strategies by pinpointing areas of improvements. |
<br /> | <br /> | ||
| Line 433: | Line 434: | ||
::b) Is the Incident Response plan being implemented and tracked at each stage | ::b) Is the Incident Response plan being implemented and tracked at each stage | ||
| + | <nowiki>**</nowiki>''Overall if anything goes wrong, will you be able to pinpoint where non-compliance is.'' | ||
| − | + | '''''How ''''' do we want to view information on what is being monitored? | |
| − | ''''' | ||
:1) Reports | :1) Reports | ||
:2) Dashboards/Charts | :2) Dashboards/Charts | ||
| Line 457: | Line 458: | ||
<br /> | <br /> | ||
| − | During this phase an org must implement controls in place to | + | During this phase an org must implement controls in place to structure compliance in daily operations. The goal should not only be to set up a compliance framework but to use as much automation as possible. This will in turn reduce overhead and will make compliance easier to manage and modify in the future. |
<br /> | <br /> | ||
| Line 466: | Line 467: | ||
:1) People | :1) People | ||
| + | |||
| + | :a) Work Requirements | ||
:2) Process | :2) Process | ||
| + | |||
| + | :a) Change management | ||
:3) Technology | :3) Technology | ||
| + | :a) Identity Access Management (IAM) Software | ||
<br /> | <br /> | ||
'''''What''''' can be done to automate future compliance controls? | '''''What''''' can be done to automate future compliance controls? | ||
| Line 492: | Line 498: | ||
== Related Projects == | == Related Projects == | ||
| − | * [[OWASP_Mobile_Security_Project | + | * [https://www.owasp.org/index.php/OWASP_Game_Security_Framework_Project The OWASP Game Security Framework Project] |
| − | * [ | + | * [https://www.owasp.org/index.php/OWASP_Mobile_Security_Project The OWASP Mobile Top 10 Project] |
| + | * [https://www.owasp.org/index.php/Category:OWASP_Top_Ten_Project The OWASP Web Top 10 Project] | ||
== Collaboration == | == Collaboration == | ||
| Line 524: | Line 531: | ||
== Prevention == | == Prevention == | ||
| + | In the prevention phase begins the implementation of a security solution. | ||
| + | This phase can have many sub tasks/levels depending on what you are implementing. | ||
| + | |||
| + | |||
| + | |||
| + | <br /> | ||
| + | '''Prevention Process''' | ||
| + | <br /> | ||
| + | |||
| + | :1. Plan | ||
| + | |||
| + | :2. Analyze | ||
| + | |||
| + | :3. Design | ||
| + | |||
| + | :4. Build | ||
| + | |||
| + | :5. Deploy | ||
| + | |||
| + | <br /> | ||
| + | |||
| + | '''1. Plan''' | ||
| + | |||
| + | <br /> | ||
| + | Some of the planning work could have been done in the strategy phase. | ||
| + | |||
| + | <br /> | ||
| + | '''''Example Questions to ask:''''' | ||
| + | <br /> | ||
| + | |||
| + | '''''What''''' do we need a security solution for? | ||
| + | <br /> | ||
| + | |||
| + | :1) Application | ||
| + | ::a) General Data Protection Regulation (GDPR) | ||
| + | ::b) Payment Card Industry Data Security Standard (PCI) | ||
| + | ::c) The National Institute for Standards and Technology (NIST) | ||
| + | |||
| + | :2) Data Protection | ||
| + | ::a) General Data Protection Regulation (GDPR) | ||
| + | ::b) Payment Card Industry Data Security Standard (PCI) | ||
| + | ::c) The National Institute for Standards and Technology (NIST) | ||
| + | |||
| + | :3) IT infrastructure | ||
| + | ::a) General Data Protection Regulation (GDPR) | ||
| + | ::b) Payment Card Industry Data Security Standard (PCI) | ||
| + | ::c) The National Institute for Standards and Technology (NIST) | ||
| + | |||
| + | :4) Identity & Access Management | ||
| + | ::a) General Data Protection Regulation (GDPR) | ||
| + | ::b) Payment Card Industry Data Security Standard (PCI) | ||
| + | ::c) The National Institute for Standards and Technology (NIST) | ||
| + | |||
| + | <br /> | ||
| + | '''''What''''' do we need a security solution for? | ||
| + | <br /> | ||
| + | :1) Software Application | ||
| + | |||
| + | ::a) General Data Protection Regulation (GDPR) | ||
| + | ::b) Payment Card Industry Data Security Standard (PCI) | ||
| + | ::c) The National Institute for Standards and Technology (NIST) | ||
| + | |||
| + | :2) Data Protection | ||
| + | |||
| + | ::a) Open Web Application Security Project (OWASP) | ||
| + | ::b) Payment Card Industry Data Security Standard (PCI) | ||
| + | ::c) The National Institute for Standards and Technology (NIST) | ||
| + | |||
| + | :3) IT Infrastructure | ||
| + | |||
| + | ::a) Microsoft | ||
| + | ::b) Sony | ||
| + | |||
| + | |||
| + | |||
| + | :4) Identify & Access Management | ||
| + | <br /> | ||
| + | '''''Does''''' it align with our overall security & business strategy? | ||
| + | |||
| + | <br /> | ||
| + | '''''Does''''' it fit in our current architecture? | ||
| + | <br /> | ||
| + | '''''What''''' would the impact on this solution be? | ||
| + | <br /> | ||
| + | |||
| + | '''2. Analyze''' | ||
| + | <br /> | ||
| + | |||
| + | '''''What''''' capabilities do we need to assess? | ||
| + | :1) Application | ||
| + | :2) Architecture | ||
| + | :3) Processes & Flows | ||
| + | <br /> | ||
| + | |||
| + | '''''What''''' functions exist in the current security solutions vs future? | ||
| + | <br /> | ||
| + | |||
| + | '''3. Design''' | ||
| + | <br /> | ||
| + | '''''How''''' exactly do we want this solution to function? | ||
| + | :1) Configuration | ||
| + | |||
| + | '''4. Build''' | ||
| + | :1) Assigning work tasks and doing them | ||
| + | <br /> | ||
| − | |||
| − | + | '''5. Test''' | |
| − | + | :1) What is our testing strategy? | |
| − | + | ||
| − | + | :2) How do we shift when bugs are found? | |
| − | + | ||
| − | + | <br /> | |
| − | + | ||
| − | + | '''6. Deploy''' | |
| − | + | :1) What is our "go-live" strategy for moving the solution from development to production? | |
| − | + | ||
| − | + | <br /> | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
{{Social Media Links}} | {{Social Media Links}} | ||
| Line 565: | Line 664: | ||
== Related Projects == | == Related Projects == | ||
| − | * [[OWASP_Mobile_Security_Project | + | * [https://www.owasp.org/index.php/OWASP_Game_Security_Framework_Project The OWASP Game Security Framework Project] |
| − | * [ | + | * [https://www.owasp.org/index.php/OWASP_Mobile_Security_Project The OWASP Mobile Top 10 Project] |
| + | * [https://www.owasp.org/index.php/Category:OWASP_Top_Ten_Project The OWASP Web Top 10 Project] | ||
== Collaboration == | == Collaboration == | ||
| − | [https:// | + | [https://discord.gg/kS7UBc6 Join the discord channel!] |
== Resources == | == Resources == | ||
| Line 588: | Line 688: | ||
== Management == | == Management == | ||
| − | + | Management refers to the management of access and identity within your organization. | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
{{Social Media Links}} | {{Social Media Links}} | ||
| Line 651: | Line 727: | ||
== Service Delivery/ Support == | == Service Delivery/ Support == | ||
| − | + | Service Delivery & Support refers to how an organization should approach managing any security services that have been implemented going forward. | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
{{Social Media Links}} | {{Social Media Links}} | ||
| Line 719: | Line 766: | ||
== Resources == | == Resources == | ||
This page will list additional resources related to game security that may provide more detailed context. | This page will list additional resources related to game security that may provide more detailed context. | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
{{Social Media Links}} | {{Social Media Links}} | ||
| Line 769: | Line 790: | ||
== Resources == | == Resources == | ||
| + | * [https://www.techn0rome0.com/home/2019/4/17/video-game-security-overview Video Game Security Overview] | ||
* [https://www.owasp.org/index.php/Top_IoT_Vulnerabilities Top 10 IoT Vulnerabilities from 2014] | * [https://www.owasp.org/index.php/Top_IoT_Vulnerabilities Top 10 IoT Vulnerabilities from 2014] | ||
| + | * [https://www.researchgate.net/publication/51952605_IT_Security_Issues_Within_the_Video_Game_Industry IT Security Issues Within Video Game Industry] | ||
== News and Events == | == News and Events == | ||
| Line 885: | Line 908: | ||
{{Social Media Links}} | {{Social Media Links}} | ||
| + | {{Tools categories}} | ||
| + | |||
| + | Work in progress - set of tools will be put here aside with proposed classification. | ||
=Project About= | =Project About= | ||
Latest revision as of 23:14, 2 January 2020
- About the Project
- Business Strategy & Risk
- Governance & Compliance
- Prevention
- Management
- Service Delivery/ Support
- Resources
- Trending
- Community
- Testing Tools
- Project About
OWASP Video Game Security Framework (VGSF)OWASP Video Game Security Framework (VGSF) defines an approach to discovering solutions for strategy, development, operations, and management surrounding security for video game industry business models
Most organizations that operate in the digital landscape approach security as a last afterthought when compared to the overall business strategy and operations. In the recent years it has become more apparent the consequences of such behavior with increasingly amounts of data breaches happening. The cost associated with an organization’s loss of intellectual property and other digital assets has reached the millions.
The framework is comprised of five discipline areas that could produce many best practice methodologies:
This will be one of the largest sections as it is comprised of many different aspects of overall cyber security
LicensingThe OWASP Video Game Security Framework is free to use. It is licensed under the http://creativecommons.org/licenses/by-sa/3.0/ Creative Commons Attribution-ShareAlike 3.0 license], so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one.
|
What is the OWASP Video Game Security Framework?The goal of the OWASP Video Game Security Framework is to provide an adaptable blueprint to guide the development and deployment of cyber resiliency within a video game enterprise operation. The target audience for the project includes:
Project Leaders
Contributors
Related Projects |
CollaborationJoin the discord channel: [1] Quick DownloadCOMING SOON News and Events
Classifications
| |||||||
Business Strategy & Risk
|
What is the Business Strategy & Risk Section?This section provides an overview of the various places an attacker can target to harm a given game infrastructure. Sub-project Leader
Related Projects
CollaborationJoin the discord channel: [2] Quick Download
News and Events
|
Governance & ComplianceThe purpose of the Governance & Compliance phase in the framework is to layout a guiding path to establishing and maintaining a G&C operating model. With the current trends in gaming raising the risk to the public's privacy, having a proper G&C model will keep the business continuity high therefore lowering the risks related to non-compliance.
2. Audit
Auditing involves performing routine internal checks to ensure policies are being followed by all.
**Its important to be able to perform an audit on call for unpredictable external shifts in compliance requirements
**Overall if anything goes wrong, will you be able to pinpoint where non-compliance is. How do we want to view information on what is being monitored?
|
What is the Governance & Compliance (G&C) Section?This section provides an overview of the various places an attacker can target to harm a given game infrastructure. Sub-project Leader
Related Projects
CollaborationResources
News and Events
|
PreventionIn the prevention phase begins the implementation of a security solution. This phase can have many sub tasks/levels depending on what you are implementing.
1. Plan
What do we need a security solution for?
2. Analyze
What capabilities do we need to assess?
What functions exist in the current security solutions vs future?
3. Design
4. Build
6. Deploy
|
The Exploits ProjectThe Exploits provides information on what types of tools and techniques an attacker might use to accomplish his/her goal. Sub-project Leader
Related Projects
CollaborationResourcesNews and Events
|
ManagementManagement refers to the management of access and identity within your organization.
|
What is the Attacker Goals ProjectThe Attacker Goals Project provides information on what types of outcomes attackers might try to achieve within or outside of the game they're attacking. Sub-project Leader
Related ProjectsCollaborationResourcesNews and Events
|
Service Delivery/ SupportService Delivery & Support refers to how an organization should approach managing any security services that have been implemented going forward.
|
What is the Negative Outcomes Project?The Negative Outcomes Project provides information on what types of situations could manifest within the game if bugs or exploits are not successfully addressed. Project Leader
Related ProjectsCollaborationResourcesNews and Events
|
ResourcesThis page will list additional resources related to game security that may provide more detailed context.
|
What is the Game Security Vulnerabilities Project?The Security Vulnerabilities Project provides information on what types of vulnerabilities exist within games, and which attack surfaces they fall under. Project Leaders
Related ProjectsCollaborationJoin the discord channel: [3]
Resources
News and Events
|
Video Game Trends
This section is dedicated to trends in gaming and how it can evaluated from a security perspective
| ID | Vulnerabilty Name | Description | Surface Area | Goal | Techical Impact | Business Impact | Defense | Ref | Game | Genre |
|---|---|---|---|---|---|---|---|---|---|---|
| V1 | Local Resource Modification, Client-side Logic Flaw | In 2015 The Division experienced an exploit that allowed an attacker to switch weapons rapidly, applying weapon buffs in a stacking manner, with no cap. | Game Client | Unfair Player Advantage | Player Anger | Players leave, Lost Revenue | Cryptographic Integrity Checks on Game Client | http://www.gamesradar.com/theres-a-division-damage-stacking-glitch-if-youve-got-fast-fingers/ | 3PS/1PS/MMO | |
| VN1 | "The attacker attacked and edited the LOCAL GAME CLIENT (Attack Surface), which had a LACK OF CLIENT INTEGRITY CONTROLS (Vulnerability), which allowed her to ARTIFICIALLY INCREASE HER ABILITIES (Attacker Goal), ultimately leading to an UNHAPPY PLAYER BASE (Negative Outcome) and DECLINING GAME REVENUE (Negative Outcome) due to cheating, which could have been prevented by CRYPTOGRAPHIC INTEGRITY CHECKS ON GAME CLIENT”
| |||||||||
Working Data Collection Spreadsheet:
https://docs.google.com/spreadsheets/d/1Og08wyHsqtODBDkU_M2zHAvdxc63GSu-OmT8NjCc9Ak/edit#gid=0
The VGSF team has open opportunities for individuals to collaborate and contribute to the project.
- Improving the framework schema, e.g., vulns, attack surfaces, technical impacts, business impacts, defenses, etc.
- Adding content to any of the various sections
- Input from avid gamers on how useful this is to them
- Input from app security experts
- Input from security types working at gaming companies
- Input from game company business types
If you have interest in helping, reach out to us and we'll make you a contributor.
Commonly Used Game Hacking Tools
Work in progress - set of tools will be put here aside with proposed classification.
| PROJECT INFO What does this OWASP project offer you? |
RELEASE(S) INFO What releases are available for this project? | |||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
| |||||||||||||||||||||||||||||||||||