This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Attack Surface Detector Project"
m |
m (Logo update) |
||
| (10 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
| + | <div style="width:100%;height:120px;border:0,margin:0;overflow: hidden;">[[File:ASD-banner.png|link=]]</div> | ||
<div style="width:100%;height:160px;border:0,margin:0;overflow: hidden;">[[File:OWASP_Project_Header.jpg|link=]]</div> | <div style="width:100%;height:160px;border:0,margin:0;overflow: hidden;">[[File:OWASP_Project_Header.jpg|link=]]</div> | ||
| Line 4: | Line 5: | ||
| style="border-right: 1px dotted gray;padding-right:25px;" valign="top" | | | style="border-right: 1px dotted gray;padding-right:25px;" valign="top" | | ||
<span style="color:#ff0000"></span> | <span style="color:#ff0000"></span> | ||
| − | |||
==Introduction== | ==Introduction== | ||
<span style="color:#000000"> | <span style="color:#000000"> | ||
| − | During web application penetration testing, it is important to enumerate your application's attack surface. While Dynamic Application Security Testing (DAST) tools (such as [https://www.owasp.org/index.php/OWASP_Zed_Attack_Proxy_Project OWASP ZAP] and [https://portswigger.net/ PortSwigger Burp Suite]) are good at spidering to identify application attack surfaces, they will often fail to identify unlinked endpoints | + | During web application penetration testing, it is important to enumerate your application's attack surface. While Dynamic Application Security Testing (DAST) tools (such as [https://www.owasp.org/index.php/OWASP_Zed_Attack_Proxy_Project OWASP ZAP] and [https://portswigger.net/ PortSwigger Burp Suite]) are good at spidering to identify application attack surfaces, they will often fail to identify unlinked endpoints, optional parameters, and parameter datatypes and name. These endpoints and parameters not found often go untested, which can leave your application open to an attacker. |
</span> | </span> | ||
==What is the Attack Surface Detector?== | ==What is the Attack Surface Detector?== | ||
| − | The Attack Surface Detector tool | + | The Attack Surface Detector tool uncovers the endpoints of a web application, the parameters these endpoints accept, and the data type of those parameters. This includes the unlinked endpoints a spider won't find in client-side code, or optional parameters totally unused in client-side code. It also has the capability to calculate the changes in attack surface between two versions of an application.<br> |
| − | The Attack Surface Detector is available as a plugin to both ZAP and Burp Suite, and a Command Line Interface (CLI) tool is also available. The CLI tool exports the attack surface as a JSON output, which can then be used by the ZAP and Burp Suite plugin. This is helpful for cases where the source code is not provided to the penetration tester directly. The CLI tool can also be used for other custom integration where you want to discover an application attack surface or changes in the attack surface.<br> | + | |
| + | The Attack Surface Detector is available as a plugin to both ZAP and Burp Suite, and a Command Line Interface (CLI) tool is also available. The CLI tool exports the attack surface as a JSON output, which can then be used by the ZAP and Burp Suite plugin. This is helpful for cases where the source code is not provided to the penetration tester directly. The CLI tool can also be used for other custom integration where you want to discover an application attack surface or changes in the attack surface.<br> | ||
| + | |||
For a quick overview of the Attack Surface Detection tool, see this YouTube video: | For a quick overview of the Attack Surface Detection tool, see this YouTube video: | ||
| Line 22: | Line 24: | ||
==How it Works== | ==How it Works== | ||
<span style="color:#000000"> | <span style="color:#000000"> | ||
| − | The Attack Surface Detector performs static code analyses to identify web | + | The Attack Surface Detector performs static code analyses to identify web application endpoints by parsing routes and identifying parameters (with supported languages and frameworks). This data is made available in ZAP and Burp Suite to help improve testing coverage. |
| + | </span> | ||
==Supported Languages and Frameworks== | ==Supported Languages and Frameworks== | ||
| Line 41: | Line 44: | ||
</span> | </span> | ||
| + | |||
| + | ==Roadmap== | ||
| + | We continue to improve the attack surface detection accuracy for existing supported languages and frameworks, and we are looking to add additional language support, particularly for PHP and Python. If there are any PHP or Python developers that are looking to contribute, [mailto:[email protected] please let us know].<br> | ||
| + | |||
| + | We are also looking to extend ASD for use in automated headless usage of ZAP and Burp and move the ASD ZAP plugin out of alpha classification, which requires [https://github.com/zaproxy/zap-extensions/wiki/AddOnsBeta internationalization]. If anyone can help, we would love your contributions.<br> | ||
| + | |||
| + | Finally, we are really interested in what the community thinks will help improve ASD and we will adjust our roadmap based on that feedback. | ||
==Getting Involved== | ==Getting Involved== | ||
| − | |||
Contributions to the Attack Surface Detector project are encouraged and welcome. Additions of new features and enhancements can be provided through [https://github.com/secdec/ GitHub]. We are eager to get user feedback, so please [mailto:[email protected] reach out to us] or fill out this [https://www.surveymonkey.com/r/D2N87GB ASD survey]. | Contributions to the Attack Surface Detector project are encouraged and welcome. Additions of new features and enhancements can be provided through [https://github.com/secdec/ GitHub]. We are eager to get user feedback, so please [mailto:[email protected] reach out to us] or fill out this [https://www.surveymonkey.com/r/D2N87GB ASD survey]. | ||
| Line 53: | Line 62: | ||
==Acknowledgements== | ==Acknowledgements== | ||
<span style="color:#000000"> | <span style="color:#000000"> | ||
| − | The Attack Surface Detection project is led by [https://securedecisions.com/ Secure Decisions] and was developed in collaboration with [https://www.denimgroup.com/ Denim Group] under a research grant sponsored by Department of Homeland Security (DHS) Science and Technology Directorate, Cyber Security Division (DHS S&T/CSD), BAA via contract number HHSP233201600058C. | + | The Attack Surface Detection project is led by [https://securedecisions.com/ Secure Decisions] and was developed in collaboration with [https://www.denimgroup.com/ Denim Group] under a research grant sponsored by the Department of Homeland Security (DHS) Science and Technology Directorate, Cyber Security Division (DHS S&T/CSD), BAA via contract number HHSP233201600058C. |
</span> | </span> | ||
| Line 60: | Line 69: | ||
== Project Resources == | == Project Resources == | ||
<span style="color:#ff0000"></span> | <span style="color:#ff0000"></span> | ||
| + | |||
| + | The Attack Surface Detector is available in the ZAP Marketplace and PortSwigger BApp Store, and can be installed directly from within those tools. | ||
| + | |||
====ASD Plugin for OWASP ZAP:==== | ====ASD Plugin for OWASP ZAP:==== | ||
[https://github.com/secdec/attack-surface-detector-zap/releases Download ZAP Plugin] | [https://github.com/secdec/attack-surface-detector-zap/releases Download ZAP Plugin] | ||
| Line 86: | Line 98: | ||
[https://github.com/secdec/attack-surface-detector-cli GitHub Source Code] | [https://github.com/secdec/attack-surface-detector-cli GitHub Source Code] | ||
| + | |||
| + | == News and Events == | ||
| + | * <span style="background: #66CCFF; font-size:85%;padding:2px;">24 Aug 2018</span> [https://github.com/secdec/attack-surface-detector-zap/releases Version 1.1.2 of the ASD ZAP plugin is out!] | ||
| + | * <span style="background: #66CCFF; font-size:85%;padding:2px;">23 Aug 2018</span> [https://github.com/secdec/attack-surface-detector-burp/releases Version 1.1.2 of the ASD Burp Suite plugin is out!] | ||
| + | * <span style="background: #66CCFF; font-size:85%;padding:2px;">20 Jul 2018</span> [https://github.com/secdec/attack-surface-detector-cli/releases Version 1.2.16 of the ASD CLI is out!] | ||
== Contact Us == | == Contact Us == | ||
Latest revision as of 14:31, 8 October 2018
|
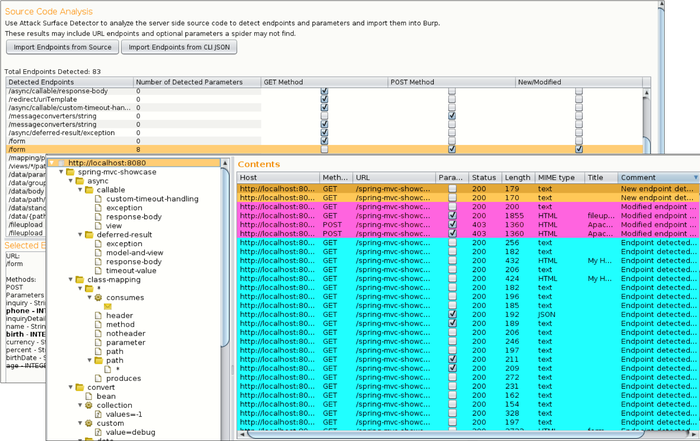
IntroductionDuring web application penetration testing, it is important to enumerate your application's attack surface. While Dynamic Application Security Testing (DAST) tools (such as OWASP ZAP and PortSwigger Burp Suite) are good at spidering to identify application attack surfaces, they will often fail to identify unlinked endpoints, optional parameters, and parameter datatypes and name. These endpoints and parameters not found often go untested, which can leave your application open to an attacker. What is the Attack Surface Detector?The Attack Surface Detector tool uncovers the endpoints of a web application, the parameters these endpoints accept, and the data type of those parameters. This includes the unlinked endpoints a spider won't find in client-side code, or optional parameters totally unused in client-side code. It also has the capability to calculate the changes in attack surface between two versions of an application. The Attack Surface Detector is available as a plugin to both ZAP and Burp Suite, and a Command Line Interface (CLI) tool is also available. The CLI tool exports the attack surface as a JSON output, which can then be used by the ZAP and Burp Suite plugin. This is helpful for cases where the source code is not provided to the penetration tester directly. The CLI tool can also be used for other custom integration where you want to discover an application attack surface or changes in the attack surface. For a quick overview of the Attack Surface Detection tool, see this YouTube video: Below is a screenshot of the Burp Suite Attack Surface Detector plugin where you can see a list of endpoints, endpoint details, and their corresponding requests: How it WorksThe Attack Surface Detector performs static code analyses to identify web application endpoints by parsing routes and identifying parameters (with supported languages and frameworks). This data is made available in ZAP and Burp Suite to help improve testing coverage. Supported Languages and Frameworks
RoadmapWe continue to improve the attack surface detection accuracy for existing supported languages and frameworks, and we are looking to add additional language support, particularly for PHP and Python. If there are any PHP or Python developers that are looking to contribute, please let us know. We are also looking to extend ASD for use in automated headless usage of ZAP and Burp and move the ASD ZAP plugin out of alpha classification, which requires internationalization. If anyone can help, we would love your contributions. Finally, we are really interested in what the community thinks will help improve ASD and we will adjust our roadmap based on that feedback. Getting InvolvedContributions to the Attack Surface Detector project are encouraged and welcome. Additions of new features and enhancements can be provided through GitHub. We are eager to get user feedback, so please reach out to us or fill out this ASD survey. LicensingThe Attack Surface Detector plugin is free to use. It is licensed under the link Mozilla Public License 2.0. AcknowledgementsThe Attack Surface Detection project is led by Secure Decisions and was developed in collaboration with Denim Group under a research grant sponsored by the Department of Homeland Security (DHS) Science and Technology Directorate, Cyber Security Division (DHS S&T/CSD), BAA via contract number HHSP233201600058C. |
Project Resources
The Attack Surface Detector is available in the ZAP Marketplace and PortSwigger BApp Store, and can be installed directly from within those tools. ASD Plugin for OWASP ZAP:ASD Plugin for PortSwigger Burp:ASD Command-Line Tool:News and Events
Contact UsProject Leader: Ken Prole Email: [email protected] Related Projects
Classifications
| |||||||||||||