This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Top 10-2017 Application Security Risks"
m (underlined all links, redefined links to OWASP as internal links) |
(Editorial changes e.g. table, line feeds, added a link) |
||
| (2 intermediate revisions by the same user not shown) | |||
| Line 1: | Line 1: | ||
{{Top_10_2013:TopTemplate | {{Top_10_2013:TopTemplate | ||
| − | | | + | |useprev=2017PrevLink |
| − | | | + | |prev={{Top_10:LanguageFile|text=releaseNotes|year=2017|language=en}} |
| − | | | + | |usenext=2017NextLink |
| − | | | + | |next={{Top_10:LanguageFile|text=top10|year=2017|language=en}} |
|year=2017 | |year=2017 | ||
|language=en | |language=en | ||
}} | }} | ||
| − | + | <!--- Risk - Application Security Risks ---> | |
| − | {{Top_10:SubsectionTableBeginTemplate|type=main}}{{Top_10_2010:SubsectionAdvancedTemplate|type={{Top_10_2010:StyleTemplate}}|subsection=freetext|position=firstWhole|title= | + | {{Top_10:SubsectionTableBeginTemplate|type=main}}{{Top_10_2010:SubsectionAdvancedTemplate|type={{Top_10_2010:StyleTemplate}}|subsection=freetext|position=firstWhole|title='What Are Application Security Risks?|year=2017|language=en}} |
| − | Attackers can potentially use many different paths through your application to do harm to your business or organization. Each of | + | Attackers can potentially use many different paths through your application to do harm to your business or organization. Each of these paths represents a risk that may, or may not, be serious enough to warrant attention. |
| − | these paths represents a risk that may, or may not, be serious enough to warrant attention. | ||
[[File:Risks-2017.png|frameless|650px|center]] | [[File:Risks-2017.png|frameless|650px|center]] | ||
| − | Sometimes | + | Sometimes these paths are trivial to find and exploit, and sometimes they are extremely difficult. Similarly, the harm that is caused may be of no consequence, or it may put you out of business. To determine the risk to your organization, you can evaluate the likelihood associated with each threat agent, attack vector, and security weakness and combine it with an estimate of the technical and business impact to your organization. Together, these factors determine your overall risk. |
| − | caused may be of no consequence, or it may put you out of business. To determine the risk to your organization, you can | ||
| − | evaluate the likelihood associated with each threat agent, attack vector, and security weakness and combine it with an estimate | ||
| − | of the technical and business impact to your organization. Together, these factors determine your overall risk. | ||
| − | {{Top_10_2010:SubsectionAdvancedTemplate|type={{Top_10_2010:StyleTemplate}}|subsection=freetext|position=left|title= | + | {{Top_10_2010:SubsectionAdvancedTemplate|type={{Top_10_2010:StyleTemplate}}|subsection=freetext|position=left|title=What's <u>My</u> Risk|year=2017|language=en}} |
| − | The <u>[[ | + | The <u>[[Top10|OWASP Top 10]]</u> focuses on identifying the most serious web application security risks for a broad array of organizations. For each of these risks, we provide generic information about likelihood and technical impact using the following simple ratings scheme, which is based on the <u>[[OWASP_Risk_Rating_Methodology|OWASP Risk Rating Methodology]]</u>. |
<center><table style="align:center; border-collapse: collapse; text-align:center; | <center><table style="align:center; border-collapse: collapse; text-align:center; | ||
| Line 27: | Line 23: | ||
<tr style="background-color: {{Top 10:BorderColor|year=2017}}; height: 2em; font-size: 90%; color: #FFFFFF; text-shadow: 2px 2px 8px #444444; "> | <tr style="background-color: {{Top 10:BorderColor|year=2017}}; height: 2em; font-size: 90%; color: #FFFFFF; text-shadow: 2px 2px 8px #444444; "> | ||
<th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text=threatAgents|language=en}}</th> | <th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text=threatAgents|language=en}}</th> | ||
| − | <th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text= | + | <th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text=exploitability|language=en}}</th> |
<th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text=weakness|language=en}} {{Top_10:LanguageFile|text=prevalence|language=en}}</th> | <th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text=weakness|language=en}} {{Top_10:LanguageFile|text=prevalence|language=en}}</th> | ||
<th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text=weakness|language=en}} {{Top_10:LanguageFile|text=detectability|language=en}}</th> | <th style="width: 16.5%; border: 3px solid #444444;">{{Top_10:LanguageFile|text=weakness|language=en}} {{Top_10:LanguageFile|text=detectability|language=en}}</th> | ||
| Line 34: | Line 30: | ||
</tr> | </tr> | ||
| − | <tr><td style="font-weight: bold; font-size:100%; border: 3px solid #444444;" rowspan="3">{{Top_10:LanguageFile|text=appSpecific|language=en}}</td> | + | <tr><td style="font-weight: bold; font-size:100%; border: 3px solid #444444;" rowspan="3">{{Top_10:LanguageFile|text=appSpecific|language=en}}</td> |
| − | + | {{Top_10-2017:SummaryTableTemplate|type=valueOnly|exploitability=3|prevalence=3|detectability=3|impact=3|language=en|year=2017|style=border: 3px solid #444444; font-size: 90% !important;}} | |
<td style="font-weight: bold; font-size: 100%; border: 3px solid #444444; " rowspan="3">{{Top_10:LanguageFile|text=appBusinessSpecific|language=en}}</td></tr> | <td style="font-weight: bold; font-size: 100%; border: 3px solid #444444; " rowspan="3">{{Top_10:LanguageFile|text=appBusinessSpecific|language=en}}</td></tr> | ||
<tr> | <tr> | ||
| − | {{Top_10:SummaryTableTemplate|type=valueOnly|exploitability=2|prevalence=2|detectability=2|impact=2|language=en|year=2017|style=border: 3px solid #444444; font-size: 90% !important;}}</tr> | + | {{Top_10-2017:SummaryTableTemplate|type=valueOnly|exploitability=2|prevalence=2|detectability=2|impact=2|language=en|year=2017|style=border: 3px solid #444444; font-size: 90% !important;}}</tr> |
<tr> | <tr> | ||
| − | {{Top_10:SummaryTableTemplate|type=valueOnly|exploitability= | + | {{Top_10-2017:SummaryTableTemplate|type=valueOnly|exploitability=1|prevalence=1|detectability=1|impact=1|language=en|year=2017|style=border: 3px solid #444444; font-size: 90% !important;}}</tr> |
</table></center> | </table></center> | ||
| − | + | In this edition, we have updated the risk rating system to assist in calculating the likelihood and impact of any given risk. For more details, please see <b><u>[[Top 10-2017 Note About Risks|Note About Risks]]</u></b>. | |
| − | + | Each organization is unique, and so are the threat actors for that organization, their goals, and the impact of any breach. If a public interest organization uses a content management system (CMS) for public information and a health system uses that same exact CMS for sensitive health records, the threat actors and business impacts can be very different for the same software. It is critical to understand the risk to your organization based on applicable threat agents and business impacts. | |
| − | + | Where possible, the names of the risks in the Top 10 are aligned with <u>[https://cwe.mitre.org/ Common Weakness Enumeration]</u> (CWE) weaknesses to promote generally accepted naming conventions and to reduce confusion. | |
| − | {{Top_10_2010:SubSubsectionOWASPReferencesTemplate}} | + | {{Top_10_2010:SubsectionAdvancedTemplate|type={{Top_10_2010:StyleTemplate}}|subsection=freetext|position=right|title=References|year=2017|language=en}} |
| + | {{Top_10_2010:SubSubsectionOWASPReferencesTemplate|year=2017|language=en}} | ||
* <u>[[OWASP_Risk_Rating_Methodology|OWASP Risk Rating Methodology]]</u> | * <u>[[OWASP_Risk_Rating_Methodology|OWASP Risk Rating Methodology]]</u> | ||
* <u>[[Threat_Risk_Modeling|Article on Threat/Risk Modeling]]</u> | * <u>[[Threat_Risk_Modeling|Article on Threat/Risk Modeling]]</u> | ||
| − | {{Top_10_2010:SubSubsectionExternalReferencesTemplate|language=en}} | + | {{Top_10_2010:SubSubsectionExternalReferencesTemplate|year=2017|language=en}} |
| − | * <u>[ | + | * <u>[https://www.iso.org/iso-31000-risk-management.html ISO 31000: Risk Management Std]</u> |
| − | * <u>[ | + | * <u>[https://www.iso.org/isoiec-27001-information-security.html ISO 27001: ISMS]</u> |
| + | * <u>[https://www.nist.gov/cyberframework NIST Cyber Framework (US)]</u> | ||
| + | * <u>[https://www.asd.gov.au/infosec/mitigationstrategies.htm ASD Strategic Mitigations (AU)]</u> | ||
| + | * <u>[https://nvd.nist.gov/vuln-metrics/cvss/v3-calculator NIST CVSS 3.0]</u> | ||
| + | * <u>[https://www.microsoft.com/en-us/download/details.aspx?id=49168 Microsoft Threat Modelling Tool]</u> | ||
{{Top_10_2013:BottomAdvancedTemplate | {{Top_10_2013:BottomAdvancedTemplate | ||
|type=box | |type=box | ||
| − | |usenext= | + | |useprev=2017PrevLink |
| + | |prev={{Top_10:LanguageFile|text=releaseNotes|year=2017|language=en}} | ||
| + | |usenext=2017NextLink | ||
|next={{Top_10:LanguageFile|text=top10|year=2017|language=en}} | |next={{Top_10:LanguageFile|text=top10|year=2017|language=en}} | ||
| − | |||
| − | |||
|year=2017 | |year=2017 | ||
|language=en | |language=en | ||
}} | }} | ||
| + | |||
| + | <!-- [[Category:OWASP Top Ten Project]] --> | ||
Latest revision as of 12:52, 22 December 2017
|
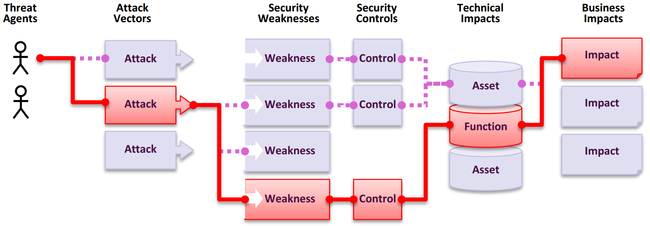
'What Are Application Security Risks?
Attackers can potentially use many different paths through your application to do harm to your business or organization. Each of these paths represents a risk that may, or may not, be serious enough to warrant attention. Sometimes these paths are trivial to find and exploit, and sometimes they are extremely difficult. Similarly, the harm that is caused may be of no consequence, or it may put you out of business. To determine the risk to your organization, you can evaluate the likelihood associated with each threat agent, attack vector, and security weakness and combine it with an estimate of the technical and business impact to your organization. Together, these factors determine your overall risk. | |||||||||||||||||||||
|
What's My Risk
The OWASP Top 10 focuses on identifying the most serious web application security risks for a broad array of organizations. For each of these risks, we provide generic information about likelihood and technical impact using the following simple ratings scheme, which is based on the OWASP Risk Rating Methodology.
In this edition, we have updated the risk rating system to assist in calculating the likelihood and impact of any given risk. For more details, please see Note About Risks. Each organization is unique, and so are the threat actors for that organization, their goals, and the impact of any breach. If a public interest organization uses a content management system (CMS) for public information and a health system uses that same exact CMS for sensitive health records, the threat actors and business impacts can be very different for the same software. It is critical to understand the risk to your organization based on applicable threat agents and business impacts. Where possible, the names of the risks in the Top 10 are aligned with Common Weakness Enumeration (CWE) weaknesses to promote generally accepted naming conventions and to reduce confusion. |
References
OWASP External | ||||||||||||||||||||