This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Mobile Top 10 2012-M2"
Jason Haddix (talk | contribs) |
Jason Haddix (talk | contribs) |
||
| (4 intermediate revisions by the same user not shown) | |||
| Line 25: | Line 25: | ||
* Weakness due to cross-platform development and compilation | * Weakness due to cross-platform development and compilation | ||
{{Mobile_Top_10_2012:SubsectionAdvancedTemplate|type={{Mobile_Top_10_2012:StyleTemplate}}|number=2|risk=2}} | {{Mobile_Top_10_2012:SubsectionAdvancedTemplate|type={{Mobile_Top_10_2012:StyleTemplate}}|number=2|risk=2}} | ||
| − | Secure coding and configuration practices must be used on server-side of the mobile application. For specific vulnerability information refer to the OWASP Web Top Ten or Cloud | + | Secure coding and configuration practices must be used on server-side of the mobile application. For specific vulnerability information refer to the OWASP Web Top Ten or Cloud Top Ten projects. We will try and link references to those projects and other OWASP projects that provide more robust descriptions. |
{{Mobile_Top_10_2012:SubsectionAdvancedTemplate|type={{Mobile_Top_10_2012:StyleTemplate}}|number=3|risk=2}} | {{Mobile_Top_10_2012:SubsectionAdvancedTemplate|type={{Mobile_Top_10_2012:StyleTemplate}}|number=3|risk=2}} | ||
| − | |||
If you look below, you can see that there is a ton of surface area to cover when thinking about M2: | If you look below, you can see that there is a ton of surface area to cover when thinking about M2: | ||
| Line 35: | Line 34: | ||
[[File:CloudTT_thum.png|border|350px]][[File:WebTT_thumb.png|border|350px]] | [[File:CloudTT_thum.png|border|350px]][[File:WebTT_thumb.png|border|350px]] | ||
| + | === The Worst Offenders === | ||
| − | While we cannot go over all of these, what we can do is list vulnerability types that we see most often within | + | While we cannot go over all of these, what we can do is list vulnerability types that we see most often within mobile applications: |
| − | ;Poor | + | ;Poor Web Services Hardening |
: Logic flaws | : Logic flaws | ||
| + | :: [https://www.owasp.org/index.php/Testing_for_business_logic_(OWASP-BL-001) Testing for business logic flaws] | ||
| + | :: [https://www.owasp.org/index.php/Business_Logic_Security_Cheat_Sheet Business Logic Security Cheat Sheet] | ||
: Weak Authentication | : Weak Authentication | ||
| + | :: [https://www.owasp.org/index.php/Top_10_2013-A2-Broken_Authentication_and_Session_Management OWASP Top Ten Broken Authentication Section] | ||
| + | :: [https://www.owasp.org/index.php/Authentication_Cheat_Sheet Authentication Cheat Sheet] | ||
| + | :: [https://www.owasp.org/index.php/Guide_to_Authentication Developers Guide for Authentication] | ||
| + | :: [https://www.owasp.org/index.php/Testing_for_authentication Testing for Authentication] | ||
: Weak or no session management | : Weak or no session management | ||
: Session fixation | : Session fixation | ||
Latest revision as of 21:09, 22 January 2014
| Threat Agents | Attack Vectors | Security Weakness | Technical Impacts | Business Impacts | |
|---|---|---|---|---|---|
| Application Specific | Exploitability EASY |
Prevalence COMMON |
Detectability EASY |
Impact SEVERE |
Application / Business Specific |
| Threat Description | Attack Vector Description | Security Weakness Description | Technical Impacts | Business Impacts | |
The M2 category is one that is always in heavy debate. It encompasses almost everything that a mobile application can do badly that does not take place on the phone. Which is exactly the argument… should it be listed at all? Don’t we have Top Ten lists for Web Applications? Don’t we have one for cloud too?
In fact, we do. If we could be altogether sure that everyone who wanted information on mobile security also stopped by those projects… it would be a perfect world. Unfortunately, after two rounds of data collection from some of the world’s top assessment teams, we find that server side issues are so prevalent in mobile applications that we cannot ignore them in the Risk listing. M2 is only .52% lower in prevalence than M1 (Insecure Data Storage) and almost always trumps M1 findings in terms of overall risk. While not statistically validated we feel that several factors lead to bad mobile application server code (and on a larger scale mobile insecurity in general):
- Rush to market
- Lack of security knowledge because of the new-ness of the languages
- Easy access to frameworks that don’t prioritize security
- Higher than average outsourced development
- Lower security budgets for mobile applications
- Assumption that the mobile OS takes full responsibility for security
- Weakness due to cross-platform development and compilation
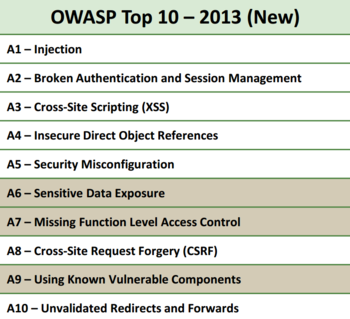
Secure coding and configuration practices must be used on server-side of the mobile application. For specific vulnerability information refer to the OWASP Web Top Ten or Cloud Top Ten projects. We will try and link references to those projects and other OWASP projects that provide more robust descriptions.
If you look below, you can see that there is a ton of surface area to cover when thinking about M2:
The Worst Offenders
While we cannot go over all of these, what we can do is list vulnerability types that we see most often within mobile applications:
- Poor Web Services Hardening
- Logic flaws
- Weak Authentication
- Weak or no session management
- Session fixation
- Sensitive data transmitted using GET method
- Insecure web server configurations
- Default content
- Administrative interfaces
- Injection (SQL, XSS, Command) on both web services and mobile-enabled websites
- Authentication flaws
- Session Management flaws
- Access control vulnerabilities
- Local and Remote File Includes
References