This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Top 10 2013-Risk"
| Line 6: | Line 6: | ||
}} | }} | ||
| + | {{Top_10_2010:SubsectionAdvancedTemplate|type={{Top_10_2010:StyleTemplate}}|title=What Are Application Security Risks?|number=whole|width=100%|year=2013}} | ||
| + | </td></tr></table> | ||
| + | Attackers can potentially use many different paths through your application to do harm to your business or organization. Each of these paths represents a risk that may, or may not, be serious enough to warrant attention. | ||
| + | <br/> | ||
[[File:Top_10_2013-appsec-risks.png|750px|center]] | [[File:Top_10_2013-appsec-risks.png|750px|center]] | ||
| − | + | Sometimes, these paths are trivial to find and exploit and sometimes they are extremely difficult. Similarly, the harm that is caused may range from nothing, all the way through putting you out of business. To determine the risk to your organization, you can evaluate the likelihood associated with each threat agent, attack vector, and security weakness and combine it with an estimate of the technical and business impact to your organization. Together, these factors determine the overall risk. | |
| − | + | ||
| − | |||
{{Top_10_2013:BottomAdvancedTemplate | {{Top_10_2013:BottomAdvancedTemplate | ||
Revision as of 00:52, 22 February 2013
NOTE: THIS IS NOT THE LATEST VERSION. Please visit the OWASP Top 10 project page to find the latest edition.
| [[Top 10 {{{year}}}-RN|← RN]] | [[Top_10_{{{year}}}-Top 10|{{{year}}} Top 10 List]] |
[[Top 10 {{{year}}}-T10|T10 →]] |
|
What Are Application Security Risks?
|
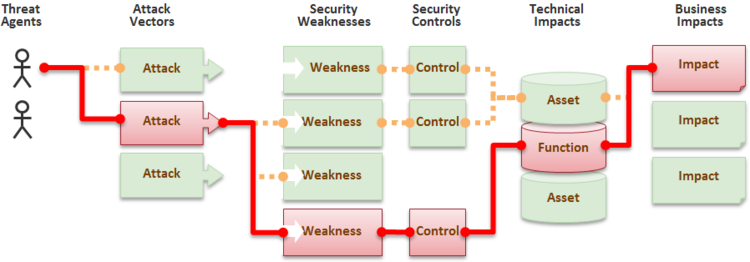
Attackers can potentially use many different paths through your application to do harm to your business or organization. Each of these paths represents a risk that may, or may not, be serious enough to warrant attention.
Sometimes, these paths are trivial to find and exploit and sometimes they are extremely difficult. Similarly, the harm that is caused may range from nothing, all the way through putting you out of business. To determine the risk to your organization, you can evaluate the likelihood associated with each threat agent, attack vector, and security weakness and combine it with an estimate of the technical and business impact to your organization. Together, these factors determine the overall risk.
</td></tr></table>
| [[Top 10 {{{year}}}-RN|← RN]] | [[Top_10_{{{year}}}-Top 10|{{{year}}} Top 10 List]] |
[[Top 10 {{{year}}}-T10|T10 →]] |