This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Testing for WS Replay (OWASP-WS-007)"
m (→Black Box testing and example) |
|||
| Line 1: | Line 1: | ||
| − | + | {{Template:OWASP Testing Guide v3}} | |
| − | {{Template:OWASP Testing Guide | ||
== Brief Summary == | == Brief Summary == | ||
| Line 64: | Line 63: | ||
* Wireshark - http://www.wireshark.org/ (recommended instead of Ethereal - same developers, same codebase) | * Wireshark - http://www.wireshark.org/ (recommended instead of Ethereal - same developers, same codebase) | ||
* TCPReplay - http://tcpreplay.synfin.net/trac/wiki/manual | * TCPReplay - http://tcpreplay.synfin.net/trac/wiki/manual | ||
| − | |||
| − | |||
Revision as of 12:48, 22 August 2008
OWASP Testing Guide v3 Table of Contents
This article is part of the OWASP Testing Guide v3. The entire OWASP Testing Guide v3 can be downloaded here.
OWASP at the moment is working at the OWASP Testing Guide v4: you can browse the Guide here
Brief Summary
This section describes testing replay vulnerabilities of a web service. The threat for a replay attack is that the attacker can assume the identity of a valid user and commit some nefarious act without detection.
Description of the Issue
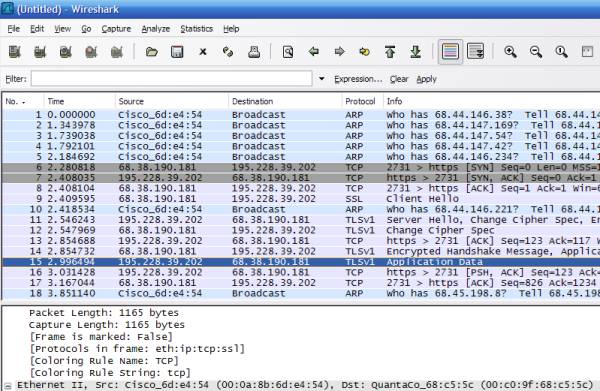
A replay attack is a "man-in-the-middle" type of attack where a message is intercepted and replayed by an attacker to impersonate the original sender. For web services, as with other types of HTTP traffic, a sniffer such as Ethereal or Wireshark can capture traffic posted to a web service and using a tool like WebScarab, a tester can resend a packet to the target server. An attacker can attempt to resend the original message or change the message in order to compromise the host server.
Black Box testing and example
Testing for Replay Attack vulnerabilities:
1. Using Wireshark on a network, sniff traffic and filter for web service traffic. Another alternative is to install WebScarab and use it as a proxy to capture http traffic
2. Using the packets captured by ethereal, use TCPReplay to initiate the replay attack by reposting the packet. It may be necessary to capture many packets over time to determine session id patterns in order to assume a valid session id for the replay attack. It is also possible to manually post captured HTTP traffic, by using WebScarab
Result Expected:
The tester can assume the identity of the attacker.
Gray Box testing and example
Testing for Replay Attack vulnerabilities
1. Does the web service employ some means of preventing the replay attack? Such as pseudo random Session tokens, Nonces with MAC addresses or Timestamping. Here is an example of an attempt to randomize session tokens: (from MSDN Wicked Code - http://msdn.microsoft.com/msdnmag/issues/04/08/WickedCode/default.aspx?loc=&fig=true#fig1).
string id = GetSessionIDMac().Substring (0, 24);
...
private string GetSessionIDMac (string id, string ip,
string agent, string key)
{
StringBuilder builder = new StringBuilder (id, 512);
builder.Append (ip.Substring (0, ip.IndexOf ('.',
ip.IndexOf ('.') + 1)));
builder.Append (agent);
using (HMACSHA1 hmac = new HMACSHA1
(Encoding.UTF8.GetBytes (key))) {
return Convert.ToBase64String (hmac.ComputeHash
(Encoding.UTF8.GetBytes (builder.ToString ())));
}
}
2. Can the site employ SSL - this will prevent unauthorized attempts to replay messages?
References
Whitepapers
- W3C: "Web Services Architecture" - http://www.w3.org/TR/ws-arch/
Tools
- OWASP WebScarab - http://www.owasp.org/index.php/Category:OWASP_WebScarab_Project
- Ethereal - http://www.ethereal.com/
- Wireshark - http://www.wireshark.org/ (recommended instead of Ethereal - same developers, same codebase)
- TCPReplay - http://tcpreplay.synfin.net/trac/wiki/manual