This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Testing: Introduction and objectives"
Mmacdonell (talk | contribs) m |
m |
||
| Line 2: | Line 2: | ||
{{Template:OWASP Testing Guide v2}} | {{Template:OWASP Testing Guide v2}} | ||
| − | This Chapter describes the OWASP Web Application Penetration testing methodology and explains how to test each | + | This Chapter describes the OWASP Web Application Penetration testing methodology and explains how to test each vulnerability. |
| − | '''What is | + | '''What is Web Application Penetration Testing?'''<br> |
A penetration test is a method of evaluating the security of a computer system or network by simulating an attack. A Web Application Penetration Test focuses only on evaluating the security of a web application.<br> | A penetration test is a method of evaluating the security of a computer system or network by simulating an attack. A Web Application Penetration Test focuses only on evaluating the security of a web application.<br> | ||
The process involves an active analysis of the application for any weaknesses, technical flaws or vulnerabilities. Any security issues that are found will be presented to the system owner together with an assessment of their impact and often with a proposal for mitigation or a technical solution. | The process involves an active analysis of the application for any weaknesses, technical flaws or vulnerabilities. Any security issues that are found will be presented to the system owner together with an assessment of their impact and often with a proposal for mitigation or a technical solution. | ||
| Line 10: | Line 10: | ||
'''What is a vulnerability?'''<br> | '''What is a vulnerability?'''<br> | ||
| − | Given an application owns a set of assets (resources of value such as the data in a database or on the file system), a vulnerability is a weakness | + | Given that an application owns a set of assets (resources of value such as the data in a database or on the file system), a vulnerability is a weakness in an asset that makes a threat possible. |
| − | So a threat is a potential occurrence that may harm an asset by exploiting a | + | So a threat is a potential occurrence that may harm an asset by exploiting a vulnerability. |
A test is an action that tends to show a vulnerability in the application. | A test is an action that tends to show a vulnerability in the application. | ||
| Line 18: | Line 18: | ||
The OWASP approach is Open and Collaborative: | The OWASP approach is Open and Collaborative: | ||
* Open: every security expert can participate with his experience in the project. Everything is free. | * Open: every security expert can participate with his experience in the project. Everything is free. | ||
| − | * Collaborative: we usually perform brainstorming before the articles are written | + | * Collaborative: we usually perform brainstorming before the articles are written so we can share our ideas and develop a collective vision of the project. That means rough consensus, wider audience and participation.<br> |
This approach tends to create a defined Testing Methodology that will be: | This approach tends to create a defined Testing Methodology that will be: | ||
* Consistent | * Consistent | ||
| Line 26: | Line 26: | ||
* Document all | * Document all | ||
* Test all | * Test all | ||
| − | We think | + | We think it is important to use a method to test all the know vulnerabilities and document all the the pen test activities.<br> |
| + | |||
'''What is the OWASP testing methodology?'''<br> | '''What is the OWASP testing methodology?'''<br> | ||
Penetration testing will never be an exact science where a complete list of all possible issues that should be tested can be defined. Indeed, penetration testing is only an appropriate technique for testing the security of web applications under certain circumstances. | Penetration testing will never be an exact science where a complete list of all possible issues that should be tested can be defined. Indeed, penetration testing is only an appropriate technique for testing the security of web applications under certain circumstances. | ||
The goal is to collect all the possible testing techniques, explain them and keep the guide updated.<br> | The goal is to collect all the possible testing techniques, explain them and keep the guide updated.<br> | ||
| − | The OWASP Web Application Penetration Testing is based on black box approach. The tester | + | The OWASP Web Application Penetration Testing method is based on the black box approach. The tester knows nothing or very little information about the application to be tested. |
| − | The testing model | + | The testing model consists of: |
* Tester: Who performs the testing activities | * Tester: Who performs the testing activities | ||
* Tools and methodology: The core of this Testing Guide project | * Tools and methodology: The core of this Testing Guide project | ||
* Application: The black box to test | * Application: The black box to test | ||
The test is divided in 2 phases: | The test is divided in 2 phases: | ||
| − | * Passive mode: in the passive mode the tester tries to understand the application's logic, plays with the application; a tool can be used for information gathering | + | * Passive mode: in the passive mode the tester tries to understand the application's logic, plays with the application; a tool can be used for information gathering such as an HTTP proxy to observe all the HTTP requests and responses. At the end of this phase the tester should understand all the access points (gates) of the application (e.g. Header HTTP, parameters, cookies). For example the tester could find the following: |
<pre> | <pre> | ||
https://www.example.com/login/Autentic_Form.html | https://www.example.com/login/Autentic_Form.html | ||
| Line 61: | Line 62: | ||
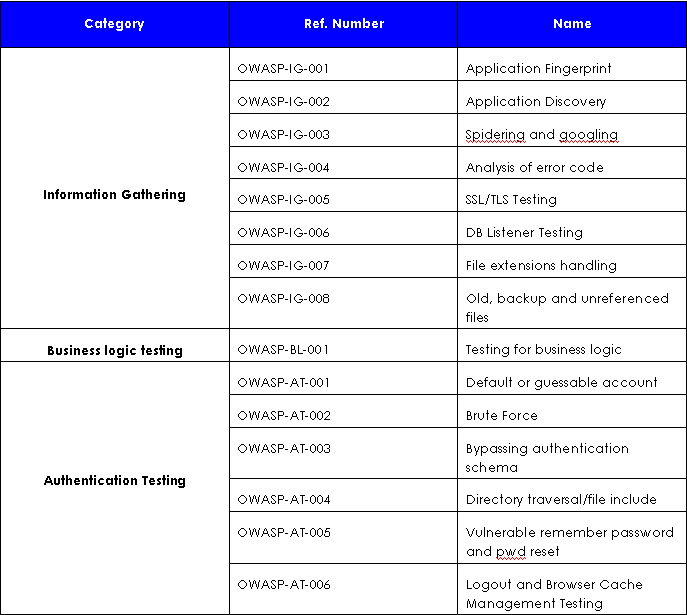
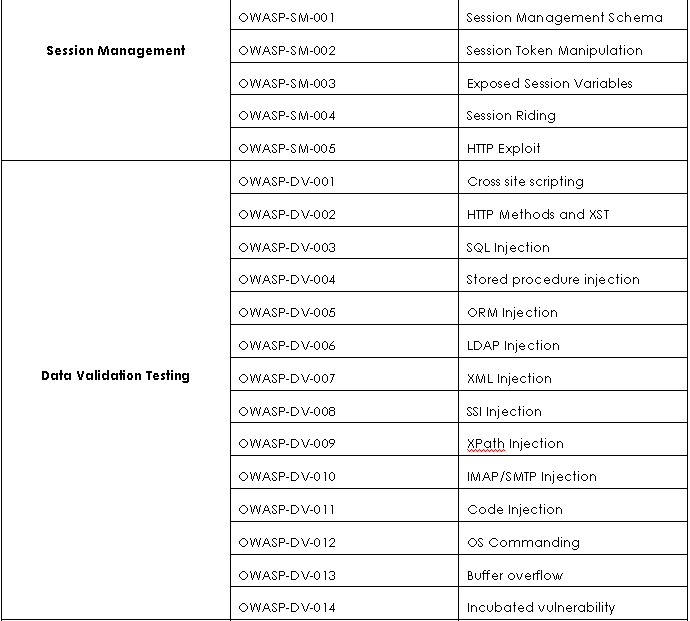
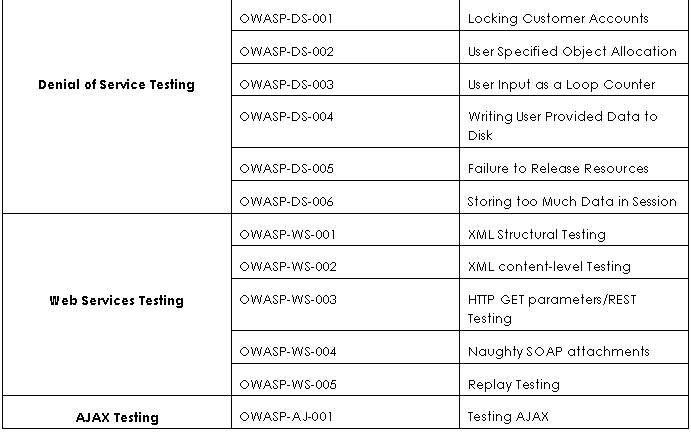
| − | Here is the list of | + | Here is the list of tests that we will explain in the next paragraphs: |
<center>[[Image:Table1.PNG]]</center> | <center>[[Image:Table1.PNG]]</center> | ||
Revision as of 16:22, 12 January 2007
[Up]
OWASP Testing Guide v2 Table of Contents
This Chapter describes the OWASP Web Application Penetration testing methodology and explains how to test each vulnerability.
What is Web Application Penetration Testing?
A penetration test is a method of evaluating the security of a computer system or network by simulating an attack. A Web Application Penetration Test focuses only on evaluating the security of a web application.
The process involves an active analysis of the application for any weaknesses, technical flaws or vulnerabilities. Any security issues that are found will be presented to the system owner together with an assessment of their impact and often with a proposal for mitigation or a technical solution.
What is a vulnerability?
Given that an application owns a set of assets (resources of value such as the data in a database or on the file system), a vulnerability is a weakness in an asset that makes a threat possible. So a threat is a potential occurrence that may harm an asset by exploiting a vulnerability. A test is an action that tends to show a vulnerability in the application.
Our approach in writing this guide
The OWASP approach is Open and Collaborative:
- Open: every security expert can participate with his experience in the project. Everything is free.
- Collaborative: we usually perform brainstorming before the articles are written so we can share our ideas and develop a collective vision of the project. That means rough consensus, wider audience and participation.
This approach tends to create a defined Testing Methodology that will be:
- Consistent
- Reproducible
- Under quality control
The problems that we want to be addressed are:
- Document all
- Test all
We think it is important to use a method to test all the know vulnerabilities and document all the the pen test activities.
What is the OWASP testing methodology?
Penetration testing will never be an exact science where a complete list of all possible issues that should be tested can be defined. Indeed, penetration testing is only an appropriate technique for testing the security of web applications under certain circumstances.
The goal is to collect all the possible testing techniques, explain them and keep the guide updated.
The OWASP Web Application Penetration Testing method is based on the black box approach. The tester knows nothing or very little information about the application to be tested.
The testing model consists of:
- Tester: Who performs the testing activities
- Tools and methodology: The core of this Testing Guide project
- Application: The black box to test
The test is divided in 2 phases:
- Passive mode: in the passive mode the tester tries to understand the application's logic, plays with the application; a tool can be used for information gathering such as an HTTP proxy to observe all the HTTP requests and responses. At the end of this phase the tester should understand all the access points (gates) of the application (e.g. Header HTTP, parameters, cookies). For example the tester could find the following:
https://www.example.com/login/Autentic_Form.html
This indicates an authentication form in which the application requests a username and a password.
The following parameters represent two access points (gates) to the application:
http://www.example.com/Appx.jsp?a=1&b=1
In this case, the application shows two gates (parameters a and b).
All the gates found in this phase represent a point of testing. A spreadsheet with the directory tree of the application and all the access points would be useful for the second phase.
- Active mode: in this phase the tester begins to test using the methodology described in the follow paragraphs.
We have split the set of tests in 8 sub-categories:
- Information Gathering
- Business Logic Testing
- Authentication Testing
- Session Management Testing
- Data Validation Testing
- Denial of Service Testing
- Web Services Testing
- AJAX Testing
Here is the list of tests that we will explain in the next paragraphs:
OWASP Testing Guide v2
Here is the OWASP Testing Guide v2 Table of Contents