This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Projects/OWASP Mobile Security Project - Top Ten Mobile Risks"
m (minor wiki cleanup) |
Chad Butler (talk | contribs) |
||
| Line 33: | Line 33: | ||
== Call to Action for 2015 == | == Call to Action for 2015 == | ||
We are currently looking for vendors, consultants, or other industry experts within the appsec community that are willing to participate in the OWASP Mobile Top Ten 2015. Participation could include any of the following: gathering data, promoting awareness, etc. | We are currently looking for vendors, consultants, or other industry experts within the appsec community that are willing to participate in the OWASP Mobile Top Ten 2015. Participation could include any of the following: gathering data, promoting awareness, etc. | ||
| + | |||
| + | === Project Survey === | ||
| + | Please help us shape the roadmap for this important project by participating in this survey: | ||
| + | [http://preview.tinyurl.com/m2cyyrp Survey Link] | ||
| + | |||
| + | === AppSec USA 2014 Opportunities === | ||
| + | We have also scheduled a project summit at AppSec USA 2014 for Friday, September 19th at 1:00 PM. More information to follow. | ||
== Top 10 Mobile Risks - Final List 2014 == | == Top 10 Mobile Risks - Final List 2014 == | ||
Revision as of 21:37, 13 September 2014
About this list
In 2013, we polled the industry for new vulnerability statistics in the field of mobile applications. What you see here is a result of that data and a representation of the mobile application threat landscape.
Our goals for the 2014 list included the following:
- Updates to the wiki content; including cross-linking to testing guides, more visual exercises, etc;
- Generation of more data; and
- A PDF release.
This list has been finalized after a 90-day feedback period from the community. Based on feedback, we intend on releasing a Mobile Top Ten 2015 list following a similar approach of collecting data, grouping the data in logical and consistent ways.
Feel free to visit the mailing list as well!
Call to Action for 2015
We are currently looking for vendors, consultants, or other industry experts within the appsec community that are willing to participate in the OWASP Mobile Top Ten 2015. Participation could include any of the following: gathering data, promoting awareness, etc.
Project Survey
Please help us shape the roadmap for this important project by participating in this survey: Survey Link
AppSec USA 2014 Opportunities
We have also scheduled a project summit at AppSec USA 2014 for Friday, September 19th at 1:00 PM. More information to follow.
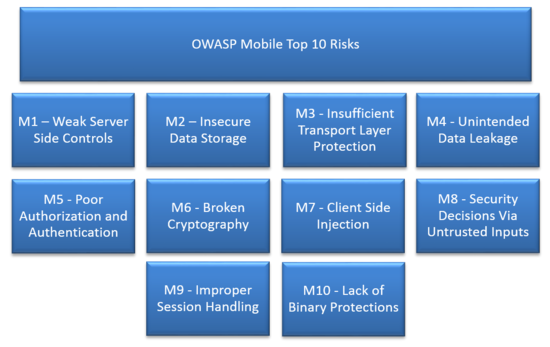
Top 10 Mobile Risks - Final List 2014
- M1: Weak Server Side Controls
- M2: Insecure Data Storage
- M3: Insufficient Transport Layer Protection
- M4: Unintended Data Leakage
- M5: Poor Authorization and Authentication
- M6: Broken Cryptography
- M7: Client Side Injection
- M8: Security Decisions Via Untrusted Inputs
- M9: Improper Session Handling
- M10: Lack of Binary Protections
Project Leads, Credit, and Contributions
Project Methodology
- We adhered loosely to the OWASP Web Top Ten Project methodology.
Archive
- The list below is the OLD release candidate v1.0 of the OWASP Top 10 Mobile Risks. This list was initially released on September 23, 2011 at Appsec USA.
- The original presentation can be found here: SLIDES
- The corresponding video can be found here: VIDEO
- 2011-12 Mobile Top Ten for archive purposes
- The original presentation can be found here: SLIDES