This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP ZSC Tool Project"
Ali Razmjoo (talk | contribs) (→Main) |
Ali Razmjoo (talk | contribs) (→Developssssers) |
||
| Line 103: | Line 103: | ||
|} | |} | ||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
=FAQs= | =FAQs= | ||
Revision as of 14:28, 5 August 2015
Main
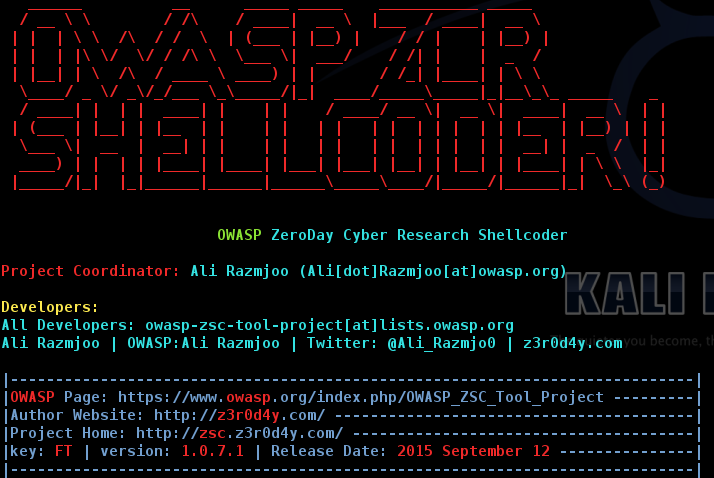
OWASP ZSC Tool ProjectWhat is OWASP ZSC ?OWASP ZSC is an open source software in python language which lets you generate customized shellcodes for listed operation systems. This software could be run on Linux under python 2.7.x.
DescriptionUsage of shellcodesShellcodesare small codes in assembly which could be use as the payload in software exploiting. Other usages are in malwares, bypassing antiviruses, obfuscated codes and etc. Why use OWASP ZSC ?According to other shellcode generators same as metasploit tools and etc, OWASP ZSC using new encodes and methods which antiviruses won't detect. OWASP ZSC encoderes are able to generate shellcodes with random encodes and that's lets you to get thousands new dynamic shellcodes with same job in just a second,that means you will not get a same code if you use random encodes with same commands, And that make OWASP ZSC one of the bests! otherwise it's gonna generate shellcodes for many operation systems in next versions. LicensingGNU GENERAL PUBLIC LICENSE , Version 3, 29 June 2007Copyright (C) 2007 Free Software Foundation, Inc. http://fsf.org/ Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed. Click to see the full license
The OWASP Security Principles are licensed under the http://creativecommons.org/licenses/by-sa/3.0/ Creative Commons Attribution-ShareAlike 3.0 license], so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one. |
Project LeaderLinksShellcode GeneratingWith using OWASP ZSC you would be able to generate any customized Shellcode in your mind including encodes,and Disassembly code in few seconds. Be an OWASP ZSC developerLast Tricks in Home
|
Quick DownloadThe home of the OWASP Security Principles is on GitHub. You are encourged to fork, edit and push your changes back to the project through git or edit the project directly on github. However, if you like you may also download the master repository from the following links: News and Events
DocsClassifications
| |||||||
FAQs
To see full guides please visit our wiki page.
Help Menu
Switches: -h, --h, -help, --help => to see this help guide -os => choose your os to create shellcode -oslist => list os for switch -os -o => output filename -job => what shellcode gonna do for you ? -joblist => list of -job switch -encode => generate shellcode with encode -types => types of encode for -encode switch -wizard => wizard mod -update => check for update -about => about software and developers.
Requirement / Installation
Installation Go to download page, and download last version in github. Extract and run installer.py, then you are able to run software with OWASP ZSC command or you can directly execute zsc.py without installing it.or you can follow these commands to install the last version:
wget https://github.com/Ali-Razmjoo/OWASP-ZSC/archive/master.zip -O owasp-zsc.zip && unzip owasp-zsc.zip && rm -rf owasp-zsc.zip && mv OWASP-ZSC-master owasp-zsc && cd owasp-zsc && python installer.py
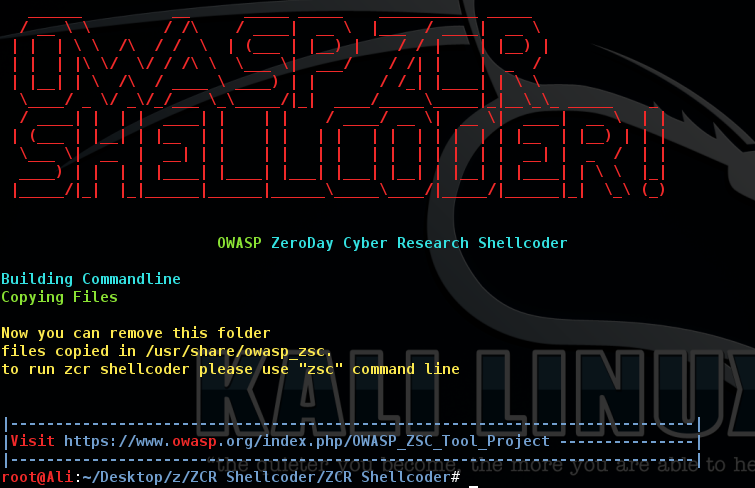
Note: Software could be uninstall with executing uninstaller.py
Note: Software installation directory is "/usr/share/owasp-zsc"
Developers
Be an OWASP ZSC developer
To join us for developing ZCR Shellcoder, Make your OWASP Account at first and you may need to know Assembly, Shellcoding, Python. Then check up this Table and build a shellcode generator with python which we didn’t made it yet, then send it to us and after checking and testing your code, You will became a OWASP ZSC developer and your code will add to software in next versions.
Also please visit Developer Pages.