This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP Xenotix XSS Exploit Framework"
Ajin Abraham (talk | contribs) m (added xss protection cheat sheet for developers) |
Ajin Abraham (talk | contribs) (V6 Release Changes) |
||
| Line 6: | Line 6: | ||
| valign="top" style="border-right: 1px dotted gray;padding-right:20px;" | | | valign="top" style="border-right: 1px dotted gray;padding-right:20px;" | | ||
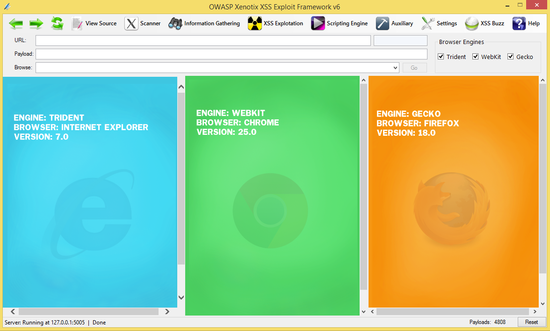
| − | ==OWASP Xenotix XSS Exploit Framework | + | ==OWASP Xenotix XSS Exploit Framework 6== |
| − | [[Image: | + | [[Image:Xen6.png|left|550px]] |
| − | '''OWASP Xenotix XSS Exploit Framework''' is an advanced Cross Site Scripting (XSS) vulnerability detection and exploitation framework. | + | '''OWASP Xenotix XSS Exploit Framework''' is an advanced Cross Site Scripting (XSS) vulnerability detection and exploitation framework. Xenotix provides Zero False Positive XSS Detection by performing the Scan within the browser engines where in real world, payloads get reflected. Xenotix Scanner Module is incorporated with 3 intelligent fuzzers to reduce the scan time and produce better results. If you really don't like the tool logic, then leverage the power of Xenotix API to make the tool work like you wanted it to be. |
| + | It is claimed to have the world’s 2nd largest XSS Payloads of about 4800+ distinctive XSS Payloads. It is incorporated with a feature rich Information Gathering module for target Reconnaissance. The Exploit Framework includes real world offensive XSS exploitation modules for Penetration Testing and Proof of Concept creation. | ||
| Line 49: | Line 50: | ||
== QUICK DOWNLOAD == | == QUICK DOWNLOAD == | ||
| − | [[Image: | + | [[Image:Dwd.png |200px| link=http://opensecurity.in/downloads/OWASP_Xenotix_XSS_Exploit_Framework_V6.rar]] |
== NEWS AND EVENTS == | == NEWS AND EVENTS == | ||
| + | * [14 Sept 2014] Xenotix XSS Exploit Framework V6 is Released | ||
* [14 Feb 2014] Xenotix XSS Exploit Framework V5 is Released | * [14 Feb 2014] Xenotix XSS Exploit Framework V5 is Released | ||
* [16 Dec 2013] [http://www.toolswatch.org/2013/12/2013-top-security-tools-as-voted-by-toolswatch-org-readers/ Top 5th Security tool of 2013, voted by ToolsWatch Readers] | * [16 Dec 2013] [http://www.toolswatch.org/2013/12/2013-top-security-tools-as-voted-by-toolswatch-org-readers/ Top 5th Security tool of 2013, voted by ToolsWatch Readers] | ||
| Line 92: | Line 94: | ||
*GET Request Manual Mode | *GET Request Manual Mode | ||
*GET Request Auto Mode | *GET Request Auto Mode | ||
| + | *Multiple Parameter Scanner | ||
| + | *GET Request Fuzzer | ||
| + | *POST Request Fuzzer | ||
| + | *Advanced Request Fuzzer | ||
| + | *OAuth 1.0a Request Scanner | ||
*DOM Scanner | *DOM Scanner | ||
| − | |||
| − | |||
| − | |||
| − | |||
*Hidden Parameter Detector | *Hidden Parameter Detector | ||
| Line 103: | Line 106: | ||
*WAF Fingerprinting | *WAF Fingerprinting | ||
*Victim Fingerprinting | *Victim Fingerprinting | ||
| − | * | + | **IP to Location |
| − | * | + | **IP to GeoLocation |
| − | * | + | *Network |
| − | *Ping Scan | + | **Network IP (WebRTC) |
| − | *Port Scan | + | **Ping Scan |
| − | *Internal Network Scan | + | **Port Scan |
| + | **Internal Network Scan | ||
| + | *Browser | ||
| + | **Fingerprinting | ||
| + | **Features Detector | ||
'''EXPLOITATION MODULES''' | '''EXPLOITATION MODULES''' | ||
| Line 114: | Line 121: | ||
*Send Message | *Send Message | ||
*Cookie Thief | *Cookie Thief | ||
| − | |||
| − | |||
*Keylogger | *Keylogger | ||
*HTML5 DDoSer | *HTML5 DDoSer | ||
*Load File | *Load File | ||
*Grab Page Screenshot | *Grab Page Screenshot | ||
| − | |||
| − | |||
*JavaScript Shell | *JavaScript Shell | ||
*Reverse HTTP WebShell | *Reverse HTTP WebShell | ||
| − | |||
*Metasploit Browser Exploit | *Metasploit Browser Exploit | ||
| − | *Firefox Reverse Shell Addon (Persistent) | + | *Social Engineering |
| − | * | + | **Phisher |
| − | * | + | **Tabnabbing |
| − | * | + | **Live WebCam Screenshot |
| − | * | + | **Download Spoofer |
| − | * | + | **Geolocation HTML5 API |
| + | **Java Applet Drive-By (Windows) | ||
| + | **Java Applet Drive-By Reverse Shell (Windows) | ||
| + | **HTA Network Configuration (Windows, IE) | ||
| + | **HTA Drive-By (Windows, IE) | ||
| + | **HTA Drive-By Reverse Shell (Windows, IE) | ||
| + | *Firefox Addons | ||
| + | **Reverse TCP Shell Addon (Windows, Persistent) | ||
| + | **Reverse TCP Shell Addon (Linux, Persistent) | ||
| + | **Session Stealer Addon (Persistent) | ||
| + | **Keylogger Addon (Persistent) | ||
| + | **DDoSer Addon (Persistent) | ||
| + | **Linux Credential File Stealer Addon (Persistent) | ||
| + | **Drop and Execute Addon (Persistent) | ||
| − | ''' | + | '''AUXILIARY MODULES''' |
*WebKit Developer Tools | *WebKit Developer Tools | ||
| − | * | + | *Encoder/Decoder |
| − | *JavaScript | + | *JavaScript Encoders |
| + | **JSFuck 6 Char Encoder | ||
| + | **jjencode Encoder | ||
| + | **aaencode Encoder | ||
| + | *JavaScript Beautifier | ||
*Hash Calculator | *Hash Calculator | ||
*Hash Detector | *Hash Detector | ||
| + | *View Injected JavaScript | ||
| + | *View XSS Payloads | ||
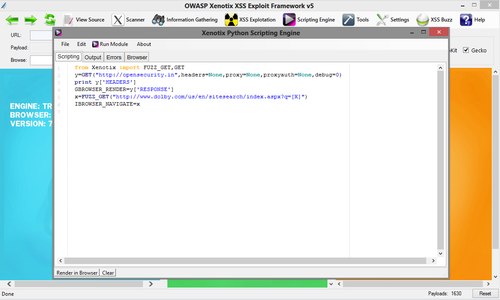
'''XENOTIX SCRIPTING ENGINE''' | '''XENOTIX SCRIPTING ENGINE''' | ||
| Line 185: | Line 206: | ||
====Latest Release==== | ====Latest Release==== | ||
| − | [[Image: | + | [[Image:Dwd.png | 200px | link=http://opensecurity.in/downloads/OWASP_Xenotix_XSS_Exploit_Framework_V6.rar]] |
| + | MD5: 69b96d2a66f7dffeaa8a7c7926278042 | ||
| + | * Download V5 http://opensecurity.in/downloads/OWASP_Xenotix_XSS_Exploit_Framework_V6.rar | ||
MD5: bdfce2d4af4012ecc20b86bed876a54a | MD5: bdfce2d4af4012ecc20b86bed876a54a | ||
| + | |||
====Requirements==== | ====Requirements==== | ||
* Microsoft .NET Framework 4.0 http://www.microsoft.com/en-in/download/details.aspx?id=17718 | * Microsoft .NET Framework 4.0 http://www.microsoft.com/en-in/download/details.aspx?id=17718 | ||
| Line 231: | Line 255: | ||
<div style="font-size:120%;border:none;margin: 0;color:#000"> | <div style="font-size:120%;border:none;margin: 0;color:#000"> | ||
| + | ==V6 Changes== | ||
| + | |||
| + | * Intelli Fuzzer | ||
| + | * Context Based Fuzzer | ||
| + | * Blind Fuzzer | ||
| + | * HTA Network Configuration | ||
| + | * HTA Drive-By | ||
| + | * HTA Drive-By Reverse Shell | ||
| + | * JSFuck 6 Char Encoder | ||
| + | * jjencode Encoder | ||
| + | * aaencode Encoder | ||
| + | * IP to Location | ||
| + | * IP to GeoLocation | ||
| + | * IP Hinting | ||
| + | * Download Spoofer | ||
| + | * HTML5 Geolocation API | ||
| + | * Reverse TCP Shell Addon (Linux) | ||
| + | * OAuth 1.0a Request Scanner | ||
| + | * 4800+ Payloads | ||
| + | * SSL Error Fixed | ||
| + | |||
==V5 Changes== | ==V5 Changes== | ||
* Xenotix Scripting Engine | * Xenotix Scripting Engine | ||
| Line 297: | Line 342: | ||
</div> | </div> | ||
| − | |||
| − | |||
| − | |||
__NOTOC__ <headertabs /> | __NOTOC__ <headertabs /> | ||
[[Category:OWASP Project]] [[Category:OWASP_Breakers]] [[Category:OWASP_Defenders]] | [[Category:OWASP Project]] [[Category:OWASP_Breakers]] [[Category:OWASP_Defenders]] | ||
[[Category:OWASP_Project|Xenotix XSS Exploit Framework Project]] [[Category:OWASP_Tool]] [[Category:OWASP_Release_Quality_Tool|OWASP Release Quality Tool]] [[Category:OWASP_Download]] | [[Category:OWASP_Project|Xenotix XSS Exploit Framework Project]] [[Category:OWASP_Tool]] [[Category:OWASP_Release_Quality_Tool|OWASP Release Quality Tool]] [[Category:OWASP_Download]] | ||
Revision as of 15:21, 14 September 2014
- Main
- Features
- Conference Talks
- Screenshots
- Downloads
- Documentation
- Roadmap
- XSS Protection Cheat Sheet
- Get Involved
OWASP Xenotix XSS Exploit Framework 6OWASP Xenotix XSS Exploit Framework is an advanced Cross Site Scripting (XSS) vulnerability detection and exploitation framework. Xenotix provides Zero False Positive XSS Detection by performing the Scan within the browser engines where in real world, payloads get reflected. Xenotix Scanner Module is incorporated with 3 intelligent fuzzers to reduce the scan time and produce better results. If you really don't like the tool logic, then leverage the power of Xenotix API to make the tool work like you wanted it to be. It is claimed to have the world’s 2nd largest XSS Payloads of about 4800+ distinctive XSS Payloads. It is incorporated with a feature rich Information Gathering module for target Reconnaissance. The Exploit Framework includes real world offensive XSS exploitation modules for Penetration Testing and Proof of Concept creation.
LICENSINGOWASP Xenotix XSS Exploit Framework is free to use. It is licensed under the http://creativecommons.org/licenses/by-sa/3.0/ Creative Commons Attribution-ShareAlike 3.0 license], so you can copy, distribute and transmit the work, and you can adapt it, and use it commercially, but all provided that you attribute the work and if you alter, transform, or build upon this work, you may distribute the resulting work only under the same or similar license to this one.
|
PRESENTATIONSDEFCON DCG Banglore 2013
BlackHat Europe Arsenal 2013
Nulcon Goa 2013
ClubHack 2012
PROJECT LEADERAjin Abraham | @ajinabraham
AWARDS
|
QUICK DOWNLOADNEWS AND EVENTS
RELATED PROJECTS
OhlohCLASSIFICATIONS
| |||||||
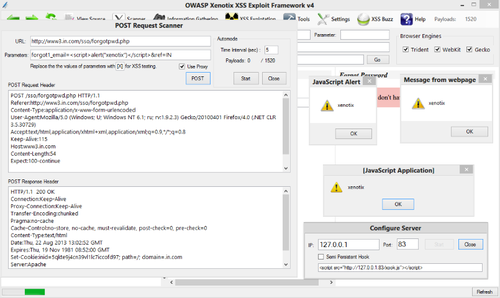
SCANNER MODULES
- GET Request Manual Mode
- GET Request Auto Mode
- Multiple Parameter Scanner
- GET Request Fuzzer
- POST Request Fuzzer
- Advanced Request Fuzzer
- OAuth 1.0a Request Scanner
- DOM Scanner
- Hidden Parameter Detector
INFORMATION GATHERING MODULES
- WAF Fingerprinting
- Victim Fingerprinting
- IP to Location
- IP to GeoLocation
- Network
- Network IP (WebRTC)
- Ping Scan
- Port Scan
- Internal Network Scan
- Browser
- Fingerprinting
- Features Detector
EXPLOITATION MODULES
- Send Message
- Cookie Thief
- Keylogger
- HTML5 DDoSer
- Load File
- Grab Page Screenshot
- JavaScript Shell
- Reverse HTTP WebShell
- Metasploit Browser Exploit
- Social Engineering
- Phisher
- Tabnabbing
- Live WebCam Screenshot
- Download Spoofer
- Geolocation HTML5 API
- Java Applet Drive-By (Windows)
- Java Applet Drive-By Reverse Shell (Windows)
- HTA Network Configuration (Windows, IE)
- HTA Drive-By (Windows, IE)
- HTA Drive-By Reverse Shell (Windows, IE)
- Firefox Addons
- Reverse TCP Shell Addon (Windows, Persistent)
- Reverse TCP Shell Addon (Linux, Persistent)
- Session Stealer Addon (Persistent)
- Keylogger Addon (Persistent)
- DDoSer Addon (Persistent)
- Linux Credential File Stealer Addon (Persistent)
- Drop and Execute Addon (Persistent)
AUXILIARY MODULES
- WebKit Developer Tools
- Encoder/Decoder
- JavaScript Encoders
- JSFuck 6 Char Encoder
- jjencode Encoder
- aaencode Encoder
- JavaScript Beautifier
- Hash Calculator
- Hash Detector
- View Injected JavaScript
- View XSS Payloads
XENOTIX SCRIPTING ENGINE
- Xenotix API
- IronPython Scripting Support
- Trident and Gecko Web Engine Support
NULLCON GOA 2013
CLUBHACK 2012
IMPORTANT
Antivirus Solutions may detect it as a threat. However it is due to the features in the exploitation framework.
Latest Release
 MD5: 69b96d2a66f7dffeaa8a7c7926278042
MD5: 69b96d2a66f7dffeaa8a7c7926278042
MD5: bdfce2d4af4012ecc20b86bed876a54a
Requirements
- Microsoft .NET Framework 4.0 http://www.microsoft.com/en-in/download/details.aspx?id=17718
- IronPython 2.7.3 http://ironpython.codeplex.com/downloads/get/423690
Older Versions
- Version 4.5 http://opensecurity.in/downloads/Xenotix_XSS_Exploit_Framework_v4.5.rar
- Version 4 https://www.dropbox.com/s/ookdse6pyszh736/Xenotix%20XSS%20Exploit%20Framework%20V4.rar
- Version 3 https://www.owasp.org/index.php/File:OWASP_Xenotix_XSS_Exploit_Framework_v3_2013.zip
- Version 2 https://www.owasp.org/index.php/File:Xenotix_XSS_Exploit_Framework_2013_v2.zip
- Version 1 https://www.owasp.org/index.php/File:Xenotix_XSS_Exploitation_Framework.zip
Source
Version 5 Videos
Version 4.5 Videos
Version 4 Videos
Version 3 Videos
V6 Changes
- Intelli Fuzzer
- Context Based Fuzzer
- Blind Fuzzer
- HTA Network Configuration
- HTA Drive-By
- HTA Drive-By Reverse Shell
- JSFuck 6 Char Encoder
- jjencode Encoder
- aaencode Encoder
- IP to Location
- IP to GeoLocation
- IP Hinting
- Download Spoofer
- HTML5 Geolocation API
- Reverse TCP Shell Addon (Linux)
- OAuth 1.0a Request Scanner
- 4800+ Payloads
- SSL Error Fixed
V5 Changes
- Xenotix Scripting Engine
- Xenotix API
- V4.5 Bug Fixes
- GET Network IP (Information Gathering)
- QR Code Generator for Xenotix xook
- HTML5 WebCam Screenshot(Exploitation Module)
- HTML5 Get Page Screenshot (Exploitation Module)
- Find Feature in View Source.
- Improved Payload Count to 1630
- Name Changes
V4.5 Changes
- JavaScript Beautifier
- Pause and Resume support for Scan
- Jump to Payload
- Cookie Support for POST Request
- Cookie Support and Custom Headers for Header Scanner
- Added TRACE method Support
- Improved Interface
- Better Proxy Support
- WAF Fingerprinting
- Load Files <exploitation module>
- Hash Calculator
- Hash Detector
The Ultimate XSS Protection Cheat Sheet for Developers is a compilation of information available on XSS Protection from various organization, researchers, websites, and from our own experience. This document follows a simple language and justifying explanations that helps a developer to implement the correct XSS defense and to build a secure web application that prevents XSS vulnerability and Post XSS attacks. It will also discuss about the existing methods or functions provided by various programming languages to mitigate XSS vulnerability. This document will be updated regularly in order to include updated and correct in information in the domain of XSS Protection.
VIEW: THE ULTIMATE XSS PROTECTION CHEAT SHEET FOR DEVELOPERS
Involvement in the development of Xenotix is highly encouraged!
Here are some of the ways you can help:
Support Us
- Facebook Page: Xenotix on Facebook
- Official Page: [Xenotix @ OpenSecurity]
Feedback & Queries
- Do you have any issues with it?
- Do you find any design flows or errors?
- Do you need help in using it?
- Do you have something to tell about it?
Then please use this form: https://docs.google.com/forms/d/1RpUhQvuHGvPTl7Gi-EXzecidGvJwKpsRaY9-MeXm1ro/viewform
Development
Are you a developer? Do you have some cool ideas to contribute? Get in touch via ajin [DOT] abraham [AT] owasp.org If you actively contribute to Xenotix then you will be invited to join the project.