This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
OWASP Attack Surface Detector Project
|
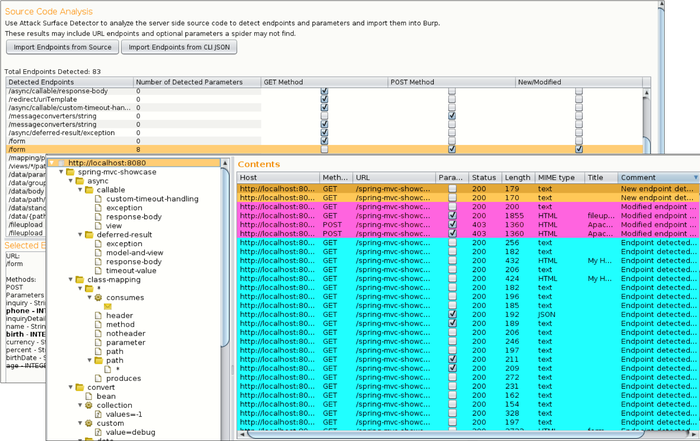
IntroductionDuring web application penetration testing, it is important to enumerate your application's attack surface. While Dynamic Application Security Testing (DAST) tools (such as Burp Suite and ZAP) are good at spidering to identify application attack surfaces, they will often fail to identify unlinked endpoints and optional parameters. These endpoints and parameters not found often go untested, which can leave your application open to an attacker. What is the Attack Surface Detector?The Attack Surface Detector tool figures out the endpoints of a web application, the parameters these endpoints accept, and the data type of those parameters. This includes the unlinked endpoints a spider won't find in client-side code, or optional parameters totally unused in client-side code. It also has the capability to calculate the changes in attack surface between two versions of an application. Below is a screenshot of the Burp Suite Attack Surface Detector plugin in action: How it WorksThe Attack Surface Detector performs static code analyses to identify web app endpoints by parsing routes and identifying parameters (with supported languages and frameworks). This data is made available in Burp Suite and OWASP ZAP to help improve testing coverage. Supported Frameworks
Getting InvolvedContributions to the Attack Surface Detector project are encouraged and welcome. Additions of new features and enhancements can be provided through GitHub. We are eager to get user feedback, so please reach out to us or fill out this ASD survey. LicensingThe Attack Surface Detector plugin is free to use. It is licensed under the link Mozilla Public License 2.0. AcknowledgementsThe Attack Surface Detection project is led by Secure Decision and was developed in collaboration with Denim Group under a research grant sponsored by Department of Homeland Security (DHS) Science and Technology Directorate, Cyber Security Division (DHS S&T/CSD), BAA via contract numbers HHSP233201600058C. |
Project Resources
ASD Plugin for OWASP ZAP:ASD Plugin for PortSwigger Burp:ASD Command-Line Tool:Contact UsProject Leader: Ken Prole Email: [email protected] Related Projects
Classifications
| |||||||||||||