This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "OWASP AppSec Asia 2008 - Taiwan"
From OWASP
Wayne huang (talk | contribs) |
(→OWASP AppSec Asia 2008, Conference Schedule (Oct 27th - Oct 28th)) |
||
| Line 32: | Line 32: | ||
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''<br><br>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''<br><br>''' | ||
|- | |- | ||
| − | | align="center" style="width:20%; background:#4F81BD; color:white" | '''10:00- | + | | align="center" style="width:20%; background:#4F81BD; color:white" | '''10:00-10:50''' || style="width:30%; background:#A7BFDE" align="center" | ''' [[What's Next? Strategies for Web Application Security]]<br>''' |
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''<BR>[[YM Chen, Director, Foundstone, A Division of McAfee]]<br><BR>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''<BR>[[YM Chen, Director, Foundstone, A Division of McAfee]]<br><BR>''' | ||
|- | |- | ||
| − | | align="center" style="width:20%; background:#4F81BD; color:white" | '''11: | + | | align="center" style="width:20%; background:#4F81BD; color:white" | '''11:00-11:50''' || style="width:30%; background:#A7BFDE" align="center" | '''[[Web-based Malware obfuscation: the kung-fu and the detection]]''' |
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''<BR>[[Wayne Huang, OWASP Taiwan Chapter]]<br><BR>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''<BR>[[Wayne Huang, OWASP Taiwan Chapter]]<br><BR>''' | ||
|- | |- | ||
{| style="width:80%" border="0" align="center" | {| style="width:80%" border="0" align="center" | ||
| − | ! colspan="2" align="center" style="background:#4058A0; color:white" | | + | ! colspan="2" align="center" style="background:#4058A0; color:white" | 11:50 - 12:40 Lunch |
|- | |- | ||
{| style="width:80%" border="0" align="center" | {| style="width:80%" border="0" align="center" | ||
| Line 49: | Line 49: | ||
|- | |- | ||
| − | | align="center" style="width:20%; background:#4F81BD; color:white" | ''' | + | | align="center" style="width:20%; background:#4F81BD; color:white" | '''12:40 - 13:30''' || style="width:30%; background:#A7BFDE" align="center" | '''[[Why Webmail systems are hard to secure--using real case studies]]<BR><br>''' |
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Charmi Lin, Taiwan Information & Communication Security Technology Center]]<br>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Charmi Lin, Taiwan Information & Communication Security Technology Center]]<br>''' | ||
|- | |- | ||
| − | | align="center" style="width:20%; background:#4F81BD; color:white" | '''13: | + | | align="center" style="width:20%; background:#4F81BD; color:white" | '''13:40 - 14:30''' || style="width:30%; background:#A7BFDE" align="center" | '''Web Application Proactive and Passive Defense Best Practices<BR><br>''' |
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Frank Fan, OWASP China]]<br>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Frank Fan, OWASP China]]<br>''' | ||
|- | |- | ||
|- | |- | ||
{| style="width:80%" border="0" align="center" | {| style="width:80%" border="0" align="center" | ||
| − | ! colspan="2" align="center" style="background:#4058A0; color:white" | 14: | + | ! colspan="2" align="center" style="background:#4058A0; color:white" | 14:30 - 14:50 Coffee Break |
|- | |- | ||
{| style="width:80%" border="0" align="center" | {| style="width:80%" border="0" align="center" | ||
| Line 67: | Line 67: | ||
|- | |- | ||
| − | | align="center" style="width:20%; background:#4F81BD; color:white" | ''' | + | | align="center" style="width:20%; background:#4F81BD; color:white" | '''14:50 - 15:40''' || style="width:30%; background:#A7BFDE" align="center" | '''[[How bad can Web vulnerabilities be—case study on a 50 million personal records breach]]<BR><br>''' |
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[PK (Taiwan Criminal Investigation Bureau)]]<br>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[PK (Taiwan Criminal Investigation Bureau)]]<br>''' | ||
|- | |- | ||
| Line 73: | Line 73: | ||
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Fyodor Yarochkin (Guard-Info)]]<br>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Fyodor Yarochkin (Guard-Info)]]<br>''' | ||
|- | |- | ||
| − | | align="center" style="width:20%; background:#4F81BD; color:white" | '''16:50 - 17: | + | | align="center" style="width:20%; background:#4F81BD; color:white" | '''16:50 - 17:30''' || style="width:30%; background:#A7BFDE" align="center" | '''[[Proxy Caches and Web Application Security--using the recent Google Docs 0-day as an example]]<BR><br>''' |
| style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Tim Bass, OWASP Thailand]]<br>''' | | style="width:40%; background:#EEF0F7; color:#4A4AFF" align="center" | '''[[Tim Bass, OWASP Thailand]]<br>''' | ||
|- | |- | ||
Revision as of 12:23, 20 October 2008
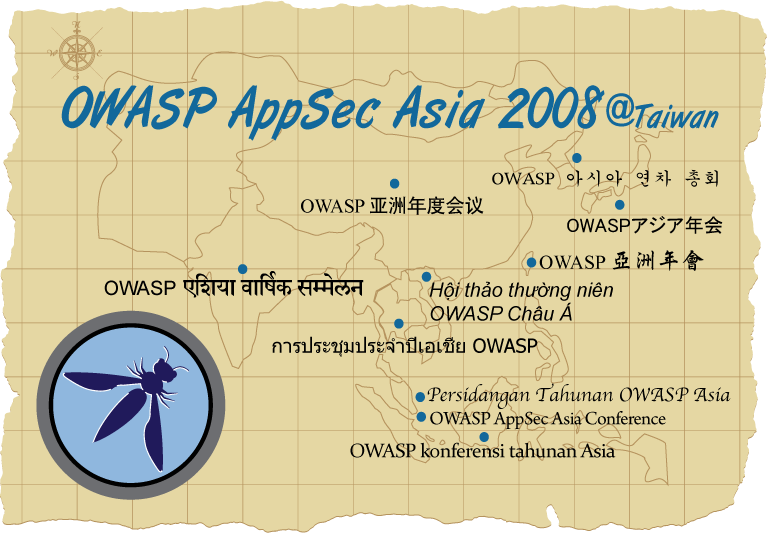
Welcome to OWASP AppSec Asia 2008! We'd like to thank China, Delhi, Hong Kong, Korea, Mumbai, Singapore, Taiwan, Thailand, and Vietnam Chapters for helping out with the conference and for attending the conference. We are working with other chapters across Asia to see if we can invite more chapters. If you represent an Asia chapter and are interested in participating, please email us.
Two professional translators will be at the conference to conduct simultaneous oral translation between English and Mandarin. Wireless earphones will be provided.