This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Information exposure through query strings in url
This article is a stub. You can help OWASP by expanding it or discussing it on its Talk page.
This is a Vulnerability. To view all vulnerabilities, please see the Vulnerability Category page.
Last revision (mm/dd/yy): 04/6/2017
Description
Information exposure through query strings in GET request is when sensitive data is passed to parameters in the URL. This allows attackers to obtain sensitive data such as usernames, passwords, tokens (authX), database details, and any other potentially sensitive data. Simply using HTTPS does not resolve this vulnerability.
Risk Factors
TBD
Examples
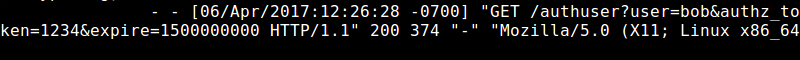
Regardless of using encryption, the following URL will expose information in the locations detailed below: https://vulnerablehost.com/authuser?user=bob&authz_token=1234&expire=1500000000
The parameter values for 'user', 'authz_token', and 'expire' will be exposed in the following locations when using HTTP or HTTPS:
- Referer Header
- Web Logs
- Shared Systems
- Browser History
- Browser Cache
- Shoulder Surfing
- TBD
When not using an encrypted channel, all of the above and the following:
- Man-in-the-Middle
- TBD
Exposure Proof-of-Concept
The following figure displays how an internal attacker can potentially exploit this vulnerability as the request above is captured in the server logs even when requested via an encrypted channel:
Related Attacks
TBD
Related Vulnerabilities
TBD
Related Controls
TBD
Related Technical Impacts
TBD