This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
GSoC2013 Ideas/OWASP ZAP CMS SCANNER
Introduction
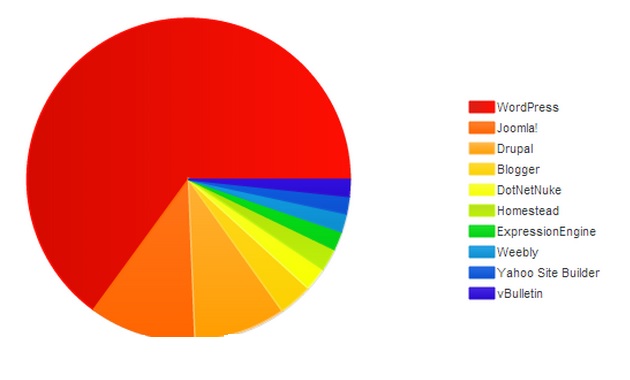
Latest Stats Show that the usage of CMS has grown in the last 5 years Just WordPress and Joomla occupy more than 6% of the top 1 million site The Usage Has Grown in Both Corporate and Personal sites And with the Chaotic Development of plugins and Components in those CMSs The risk of vulnerabilities and flows increase more and more
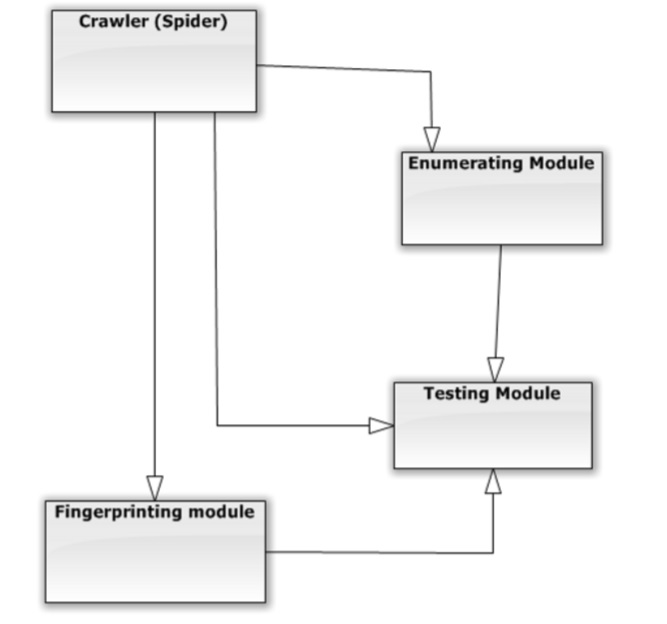
OWASP ZAP CMS SCANNER is a Scanner with More specified search methods
Functionalities
- Enumerating Plugins and Components and Themes in the CMS (Passive and Aggressive Search methods)
- Enumerating from page content
- Enumerating from lists (or database)
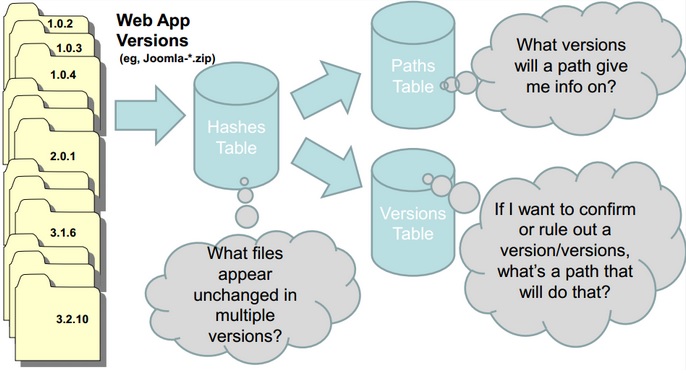
- Version Fingerprinting (with multiple methods)
- Labor intensive to add signatures
- Manually locate version in files or build regexes for headers
- Built-in options to remove identifiers (eg, meta generator)
- Very Generic
- Enumerating Vulnerable plugins , themes and Components
- Enumerating from a well-known list
- Enumerating from web search
- Enumerating using the ZAP api
- Enumerating Security measures (firewalls, security plugins ...)
Matches
Matches are made with:
- Text strings (case sensitive)
- Regular expressions
- Google Hack Database queries (limited set of keywords)
- MD5 hashes
- URL recognition
- HTML tag patterns
- Custom java code for passive and aggressive operations
features
- Control the trade off between speed/stealth and reliability
- Plugins include example URLs
- Performance tuning. Control how many websites to scan concurrently
- Result certainty awareness
- Fast
- Low resource usage
- Accurate (Low FP/FN)
- Resistant to hardening/banner removal
- Super easy to support new versions/apps