This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Cornucopia - Ecommerce Website - VE 3
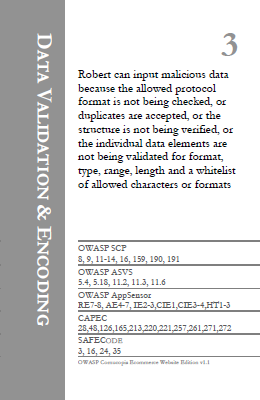
Suit: Data Validation and Encoding
Card/Value: 3
Description:
Robert can input malicious data because the allowed protocol format is not being checked, or duplicates are accepted, or the structure is not being verified, or the individual data elements are not being validated for format, type, range, length and a whitelist of allowed characters or formats.
Technical Note:
A lack of input validation is often the root cause of many security issues. Since the validation needs to be context specific, generic sanitisation routines will not suffice and the developer needs to understand how data are formatted/composed, why the data is being sent, what it is used for and the meaning of the values. This input validation should ensure that
- Only the permitted inputs (field/parameter names) are supplied.
- All the mandatory inputs are supplied.
- The values associated with the field/parameter name are of the expected format, type, range, length, etc.
NB: This card relates to generic input validation. See VE 4 for the similar additional context-specific checks.
References:
| OWASP SCP | OWASP ASVS | OWASP AppSensor | CAPEC | SAFECODE |
|---|---|---|---|---|
| 8 | 5.4 | RE7 | 28 | 3 |
| 9 | 5.18 | RE8 | 48 | 16 |
| 11 | 11.2 | AE4 | 126 | 24 |
| 12 | 11.3 | AE7 | 165 | 35 |
| 13 | 11.6 | IE2 | 213 | |
| 14 | IE3 | 220 | ||
| 16 | CIE1 | 221 | ||
| 159 | CIE3 | 257 | ||
| 190 | CIE4 | 261 | ||
| 191 | HT1 | 271 | ||
| HT2 | 272 | |||
| HT3 |