This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
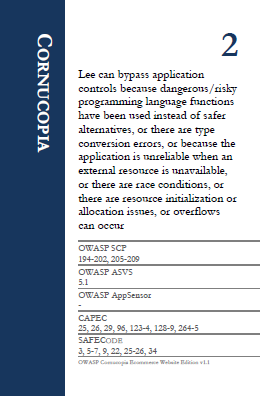
Cornucopia - Ecommerce Website - C 2
From OWASP
Suit: Cornucopia
Card/Value: 2
Description:
Lee can bypass application controls because dangerous/risky programming language functions have been used instead of safer alternatives, or there are type conversion errors, or because the application is unreliable when an external resource is unavailable, or there are race conditions, or there are resource initialization or allocation issues, or overflows can occur.
Technical Note:
This card is framework/language-specific. Examples include:
- Beware of un-trusted data.
- Check buffer sizes.
- Do not rely on garbage collection.
- Use non-executable stacks when available.
- Avoid the use of known vulnerable functions.
- Properly free allocated memory.
- Use checksums or hashes to verify the integrity of interpreted code, libraries, executables, and configuration files.
- Utilize locking to prevent multiple simultaneous requests.
- Use a synchronization mechanism to prevent race conditions.
- Protect shared variables and resources from inappropriate concurrent access.
- Explicitly initialize all your variables and other data store.
- In cases where the application must run with elevated privileges, raise privileges as late as possible, and drop them as soon as possible.
- Make no assumptions about availability of other resources, and handle exceptions.
References:
| OWASP SCP | OWASP ASVS | OWASP AppSensor | CAPEC | SAFECODE |
|---|---|---|---|---|
| 194 | 5.1 | - | 25 | 3 |
| 195 | 26 | 5 | ||
| 196 | 29 | 6 | ||
| 197 | 96 | 7 | ||
| 198 | 123 | 9 | ||
| 199 | 124 | 22 | ||
| 200 | 128 | 25 | ||
| 201 | 129 | 26 | ||
| 202 | 264 | 34 | ||
| 205 | 265 | |||
| 206 | ||||
| 207 | ||||
| 208 | ||||
| 209 |