This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Cornucopia - Ecommerce Website - CR K"
From OWASP
(Created page with "{{DISPLAYTITLE:<span style="padding:2px 5px 0px 5px;color:white;background:#a395ca;">Cornucopia - Ecommerce Website - CR K</span>}} File:Cornucopia_-_Ecommerce_Website_CR_K....") |
|||
| Line 47: | Line 47: | ||
</tr> | </tr> | ||
</table> | </table> | ||
| − | |||
| − | |||
| − | |||
| − | |||
Latest revision as of 16:29, 21 January 2016
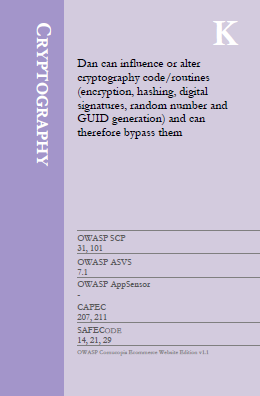
Suit: Cryptography
Card/Value: K
Description:
Dan can influence or alter cryptography code/routines (encryption, hashing, digital signatures, random number and GUID generation) and can therefore bypass them.
Technical Note:
In general, all cryptographic routines should be on the server-side using robust, tested and protected routines.
NB: Unlike other cards in this suit, this CR K relates to an attacker being able to change the executing code. This may be due to inadequate source code control, deployment controls or server protection, but could also be modification of client-side code.
References:
| OWASP SCP | OWASP ASVS | OWASP AppSensor | CAPEC | SAFECODE |
|---|---|---|---|---|
| 31 | 7.1 | - | 207 | 14 |
| 101 | 211 | 21 | ||
| 29 |