This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Command Injection Defense Cheat Sheet-Draft
Description
Command injection (or OS Command Injection) is a type of injection where the software, that constructs a system command using externally-influenced input, does not correctly neutralizes the input from special elements that can modify the initially intended command.
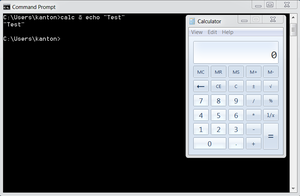
For example, if the supplied value is:
calc
when typed in a Windows command prompt, the application “Calculator” is displayed. However, if the supplied value has been tempered with, and now it is:
calc & echo “test”
this changes the meaning of the initial intended value: now, both the “Calculator” application and the value “test” are displayed.
The problem is exacerbated if the compromised process does not follow the principle of least privilege principle and attacker-controlled commands end up running with special system privileges that increases the amount of damage.
Primary Defenses
Defense Option 1: Avoid calling OS commands directly
The primary defense is to avoid calling OS commands directly. Built-in library functions are a very good alternative to OS Commands, and they cannot be manipulated to perform tasks other than those it is intended to do. For example use “mkdir()” instead of system(“mkdir /dir_name”). If there are availble libraries or APIs for the language you used, this is the preferred method.
Defense option 2: Parametrization in conjunction with Input Validation
If it is considered unavoidable the call to a system command incorporated with user-supplied, the following two layers of defense should be used within software in order to prevent attacks
- Parametrization - If available, use structured mechanisms that automatically enforce the separation between data and command. These mechanisms can help to provide the relevant quoting, encoding.
- Input validation - the values for commands and the relevant arguments should be both validated. There are different degrees of validation for the actual command and its arguments:
- When it comes to the commands used, these must be validated against a whitelist of allowed commands.
- In regards to the arguments used for these commands, they should be validated using the following options:
- Positive or “whitelist” input validation - where are the arguments allowed explicitly defined
- White list Regular Expression - where is explicitly defined a whitelist of good characters allowed and the maximum length of the string. Ensure that metacharacters like & | ; $ > < ` \ ! and white-spaces are not part of the Regular Expression. For example, the following regular expression only allows lowercase letters and numbers, and does not contain metacharacters. The length is also being limited to 3-10 characters:
^[a-z0-9]{3,10}$
Additional Defenses
Least privilege
On top of primary defences, parameterizations and input validation, we also recommend adopting all of these additional defenses in order to provide defense in depth. These additional defenses are:
- Applications should run using the lowest privileges that are required to accomplish the necessary tasks .
- If possible, create isolated accounts with limited privileges that are only used for a single task.
Code examples
C/C++
Use function from exec() family ( execl(), execve(), etc) , instead of system()
The exec family of functions does not use a full shell interpreter, so it is not vulnerable to command-injection attacks.
Java
In Java, use ProcessBuilder and the command must be separated from its arguments.
Incorrect Usage
ProcessBuilder b = new ProcessBuilder("C:\DoStuff.exe -arg1 -arg2");
In this example, the command together with the arguments are passed as a one string, making easy to manipulate that expression and inject malicious strings.
Correct Usage
Here is an example that starts a process with a modified working directory. The command, and each of the arguments are passed separately, This make it easy to validated each term and reduces the risk to insert malicious strings.
ProcessBuilder pb = new ProcessBuilder("TrustedCmd", "TrustedArg1", "TrustedArg2");
Map<String, String> env = pb.environment();
pb.directory(new File("TrustedDir"));
Process p = pb.start();
PHP
In PHP use escapeshellarg() or escapeshellcmd() rather than exec() / system() / passthru()
Related articles
Description of Command Injection Vulnerability
How to Avoid Vulnerabilities
- C Coding: Do not call system()
How to Review Code
- OWASP - Reviewing Code for OS Injection
How to Test
- OWASP Testing Guide article on Testing for Command Injection
External References