This site is the archived OWASP Foundation Wiki and is no longer accepting Account Requests.
To view the new OWASP Foundation website, please visit https://owasp.org
Difference between revisions of "Category:OWASP WebScarab Project"
m |
|||
| (25 intermediate revisions by 10 users not shown) | |||
| Line 1: | Line 1: | ||
| + | {{taggedDocument | ||
| + | | type=historical | ||
| + | | link=OWASP Zed Attack Proxy Project | ||
| + | }} | ||
| + | {| | ||
| + | |- | ||
| + | ! width="700" align="center" | <br> | ||
| + | ! width="500" align="center" | <br> | ||
| + | |- | ||
| + | | align="right" | [[Image:OWASP Inactive Banner.jpg|800px| link=https://www.owasp.org/index.php/OWASP_Project_Stages#tab=Inactive_Projects]] | ||
| + | | align="right" | | ||
| + | |||
| + | |} | ||
{{OWASP Book|1416452}} | {{OWASP Book|1416452}} | ||
| − | + | {{OWASP Breakers}} | |
| − | + | = Main = | |
'''Welcome to the WebScarab Project''' | '''Welcome to the WebScarab Project''' | ||
| Line 22: | Line 35: | ||
==Download== | ==Download== | ||
| − | + | The canonical source repository for WebScarab is at [https://github.com/OWASP/OWASP-WebScarab GitHub]. A zip archive of the tip of tree can be downloaded [https://github.com/OWASP/OWASP-WebScarab/archive/master.zip here]. | |
| − | |||
| − | |||
| − | + | Historical Versions: | |
| − | + | Alternatively, you can download older builds of WebScarab from the [http://sourceforge.net/project/showfiles.php?group_id=64424&package_id=61823 OWASP Source Code Center at Sourceforge]. Then install them likewise: | |
| + | * Linux: <tt>java -jar ./webscarab-selfcontained-[numbers].jar</tt> | ||
| + | * Windows: double-click the installer jar file [http://www.acsac.org/2007/downloads/t5-webscarab-instructions.pdf (complete installation instructions)]) | ||
==Features== | ==Features== | ||
| Line 50: | Line 63: | ||
* Manual request - Allows editing and replay of previous requests, or creation of entirely new requests. | * Manual request - Allows editing and replay of previous requests, or creation of entirely new requests. | ||
| − | * SessionID analysis - collects and | + | * SessionID analysis - collects and analyzes a number of cookies to visually determine the degree of randomness and unpredictability. Note that this analysis is rather trivial, and does not do any serious checks, such as FIPS, etc. |
| − | * Scripted - operators can use BeanShell to write a script to create requests and fetch them from the server. The script can then perform some analysis on the responses, with all the power of the WebScarab Request and Response object model to simplify things. | + | * Scripted - operators can use BeanShell (or any other BSF supported language found on the classpath) to write a script to create requests and fetch them from the server. The script can then perform some analysis on the responses, with all the power of the WebScarab Request and Response object model to simplify things. |
* Parameter fuzzer - performs automated substitution of parameter values that are likely to expose incomplete parameter validation, leading to vulnerabilities like Cross Site Scripting (XSS) and SQL Injection. | * Parameter fuzzer - performs automated substitution of parameter values that are likely to expose incomplete parameter validation, leading to vulnerabilities like Cross Site Scripting (XSS) and SQL Injection. | ||
| Line 60: | Line 73: | ||
* Compare - calculates the edit distance between the response bodies of the conversations observed, and a selected baseline conversation. The edit distance is "the number of edits required to transform one document into another". For performance reasons, edits are calculated using word tokens, rather than byte by byte. | * Compare - calculates the edit distance between the response bodies of the conversations observed, and a selected baseline conversation. The edit distance is "the number of edits required to transform one document into another". For performance reasons, edits are calculated using word tokens, rather than byte by byte. | ||
| − | * SOAP - There is a plugin that parses WSDL, and presents the various functions and the required parameters, allowing them to be edited before being sent to the server. | + | * SOAP - There is a plugin that parses WSDL, and presents the various functions and the required parameters, allowing them to be edited before being sent to the server. '''NOTE''': This plugin is deprecated, and may be removed in the future. [http://www.soapui.org SOAPUI] is streets beyond anything that Webscarab can do, or will ever do, and is also a free tool. |
* Extensions - automates checks for files that were mistakenly left in web server's root directory (e.g. .bak, ~, etc). Checks are performed for both, files and directories (e.g. /app/login.jsp will be checked for /app/login.jsp.bak, /app/login.jsp~, /app.zip, /app.tar.gz, etc). Extensions for files and directories can be edited by user. | * Extensions - automates checks for files that were mistakenly left in web server's root directory (e.g. .bak, ~, etc). Checks are performed for both, files and directories (e.g. /app/login.jsp will be checked for /app/login.jsp.bak, /app/login.jsp~, /app.zip, /app.tar.gz, etc). Extensions for files and directories can be edited by user. | ||
* XSS/CRLF - passive analysis plugin that searches for user-controlled data in HTTP response headers and body to identify potential CRLF injection (HTTP response splitting) and reflected cross-site scripting (XSS) vulnerabilities. | * XSS/CRLF - passive analysis plugin that searches for user-controlled data in HTTP response headers and body to identify potential CRLF injection (HTTP response splitting) and reflected cross-site scripting (XSS) vulnerabilities. | ||
| + | |||
| + | ==Training Material== | ||
| + | |||
| + | Aung Khant (YGN Ethical Hacker Group, Myanmar) has created a series of WebScarab movies which can be found [http://yehg.net/lab/pr0js/training/webscarab.php here]. | ||
| + | |||
| + | There are slides of the presentation "Uncovering Webscarab's Hidden Treasures", given at the OWASP EU Summit 2008, available [https://www.owasp.org/images/8/88/OWASP_EU_Summit_2008_WebScarab_treasures.ppt here]. | ||
==Future development== | ==Future development== | ||
| Line 70: | Line 89: | ||
Features will probably include: | Features will probably include: | ||
| − | * | + | * Combining the Search and Compare plugins, so that you can compare only specific responses |
| − | * | + | * Improving the fuzzer, adding ability to follow redirects, or to specify the number of threads to use. Also, adding the ability to define what is (or isn't) interesting in the fuzz results, and save only interesting conversations to the summary. |
==Extensibility== | ==Extensibility== | ||
| Line 80: | Line 99: | ||
==Project Contributors== | ==Project Contributors== | ||
| − | The WebScarab project is run by Rogan Dawes | + | The WebScarab project is run by Rogan Dawes. He can be contacted at rogan AT dawes.za.net |
| + | |||
| + | = Project About = | ||
| + | |||
| + | {{:Projects/OWASP WebScarab Project | Project About}} | ||
| + | |||
| + | |||
| + | __NOTOC__ <headertabs /> | ||
| − | [[Category: | + | [[Category:OWASP_Project|WebScarab Project]] [[Category:OWASP_Tool]] [[Category:OWASP_Download]] [[Category:OWASP Release Quality Tool]] |
| − | [[Category: | ||
| − | [[Category:OWASP | ||
Latest revision as of 03:16, 15 August 2014
This page contains content that is outdated and is no longer being maintained. It is provided as a courtesy for individuals who are still using these technologies. This page may contain URLs that were once valid but may now link to sites or pages that no longer exist.
Please use the newer Edition(s) like OWASP Zed Attack Proxy Project
| |
|
|---|---|

|
| |
This project has produced a book that can be downloaded or purchased. Feel free to browse the full catalog of available OWASP books. |
| This project is part of the OWASP Breakers community. Feel free to browse other projects within the Defenders, Builders, and Breakers communities. |
Welcome to the WebScarab Project
WebScarab is a framework for analysing applications that communicate using the HTTP and HTTPS protocols. It is written in Java, and is thus portable to many platforms. WebScarab has several modes of operation, implemented by a number of plugins. In its most common usage, WebScarab operates as an intercepting proxy, allowing the operator to review and modify requests created by the browser before they are sent to the server, and to review and modify responses returned from the server before they are received by the browser. WebScarab is able to intercept both HTTP and HTTPS communication. The operator can also review the conversations (requests and responses) that have passed through WebScarab.
You may also be interested in testing the Next Generation of WebScarab.
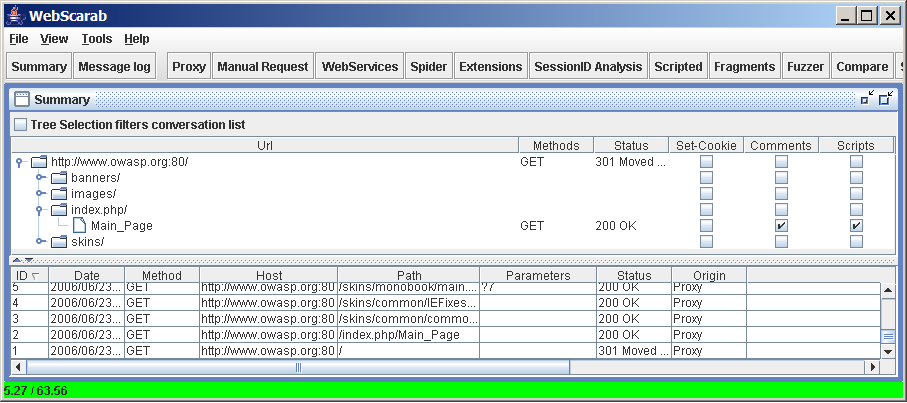
Screenshots
Here's the main window of WebScarab. Check the WebScarab Getting Started guide for more screenshots of WebScarab in action.
Overview
There is no shiny red button on WebScarab, it is a tool primarily designed to be used by people who can write code themselves, or at least have a pretty good understanding of the HTTP protocol. If that sounds like you, welcome! Download WebScarab, sign up for the mailing list on the OWASP subscription page, and enjoy! You can read a brief tutorial to explain the basic workings.
WebScarab is designed to be a tool for anyone who needs to expose the workings of an HTTP(S) based application, whether to allow the developer to debug otherwise difficult problems, or to allow a security specialist to identify vulnerabilities in the way that the application has been designed or implemented.
Download
The canonical source repository for WebScarab is at GitHub. A zip archive of the tip of tree can be downloaded here.
Historical Versions:
Alternatively, you can download older builds of WebScarab from the OWASP Source Code Center at Sourceforge. Then install them likewise:
- Linux: java -jar ./webscarab-selfcontained-[numbers].jar
- Windows: double-click the installer jar file (complete installation instructions))
Features
A framework without any functions is worthless, of course, and so WebScarab provides a number of plugins, mainly aimed at the security functionality for the moment. Those plugins include:
- Fragments - extracts Scripts and HTML comments from HTML pages as they are seen via the proxy, or other plugins
- Proxy - observes traffic between the browser and the web server. The WebScarab proxy is able to observe both HTTP and encrypted HTTPS traffic, by negotiating an SSL connection between WebScarab and the browser instead of simply connecting the browser to the server and allowing an encrypted stream to pass through it. Various proxy plugins have also been developed to allow the operator to control the requests and responses that pass through the proxy.
- Manual intercept - allows the user to modify HTTP and HTTPS requests and responses on the fly, before they reach the server or browser.
- Beanshell - allows for the execution of arbitrarily complex operations on requests and responses. Anything that can be expressed in Java can be executed.
- Reveal hidden fields - sometimes it is easier to modify a hidden field in the page itself, rather than intercepting the request after it has been sent. This plugin simply changes all hidden fields found in HTML pages to text fields, making them visible, and editable.
- Bandwidth simulator - allows the user to emulate a slower network, in order to observe how their website would perform when accessed over, say, a modem.
- Spider - identifies new URLs on the target site, and fetches them on command.
- Manual request - Allows editing and replay of previous requests, or creation of entirely new requests.
- SessionID analysis - collects and analyzes a number of cookies to visually determine the degree of randomness and unpredictability. Note that this analysis is rather trivial, and does not do any serious checks, such as FIPS, etc.
- Scripted - operators can use BeanShell (or any other BSF supported language found on the classpath) to write a script to create requests and fetch them from the server. The script can then perform some analysis on the responses, with all the power of the WebScarab Request and Response object model to simplify things.
- Parameter fuzzer - performs automated substitution of parameter values that are likely to expose incomplete parameter validation, leading to vulnerabilities like Cross Site Scripting (XSS) and SQL Injection.
- Search - allows the user to craft arbitrary BeanShell expressions to identify conversations that should be shown in the list.
- Compare - calculates the edit distance between the response bodies of the conversations observed, and a selected baseline conversation. The edit distance is "the number of edits required to transform one document into another". For performance reasons, edits are calculated using word tokens, rather than byte by byte.
- SOAP - There is a plugin that parses WSDL, and presents the various functions and the required parameters, allowing them to be edited before being sent to the server. NOTE: This plugin is deprecated, and may be removed in the future. SOAPUI is streets beyond anything that Webscarab can do, or will ever do, and is also a free tool.
- Extensions - automates checks for files that were mistakenly left in web server's root directory (e.g. .bak, ~, etc). Checks are performed for both, files and directories (e.g. /app/login.jsp will be checked for /app/login.jsp.bak, /app/login.jsp~, /app.zip, /app.tar.gz, etc). Extensions for files and directories can be edited by user.
- XSS/CRLF - passive analysis plugin that searches for user-controlled data in HTTP response headers and body to identify potential CRLF injection (HTTP response splitting) and reflected cross-site scripting (XSS) vulnerabilities.
Training Material
Aung Khant (YGN Ethical Hacker Group, Myanmar) has created a series of WebScarab movies which can be found here.
There are slides of the presentation "Uncovering Webscarab's Hidden Treasures", given at the OWASP EU Summit 2008, available here.
Future development
Features will probably include:
- Combining the Search and Compare plugins, so that you can compare only specific responses
- Improving the fuzzer, adding ability to follow redirects, or to specify the number of threads to use. Also, adding the ability to define what is (or isn't) interesting in the fuzz results, and save only interesting conversations to the summary.
Extensibility
As a framework, WebScarab is extensible. Each feature above is implemented as a plugin, and can be removed or replaced. New features can be easily implemented as well. The sky is the limit! If you have a great idea for a plugin, please let us know about it on the list.
Project Contributors
The WebScarab project is run by Rogan Dawes. He can be contacted at rogan AT dawes.za.net
| PROJECT INFO What does this OWASP project offer you? |
RELEASE(S) INFO What releases are available for this project? | |||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
| |||||||||||||||||||||||||||||||||||||||||||||
Pages in category "OWASP WebScarab Project"
The following 16 pages are in this category, out of 16 total.